Author
Security Researcher: Hemant Raj Bhati Category: Web Application Security Vulnerability Type: Insecure Direct Object Reference (IDOR)
Introduction
Insecure Direct Object Reference (IDOR) is a common access control vulnerability that occurs when an application exposes internal object identifiers such as database IDs without proper authorization checks.
Attackers can manipulate these identifiers to access resources belonging to other users.
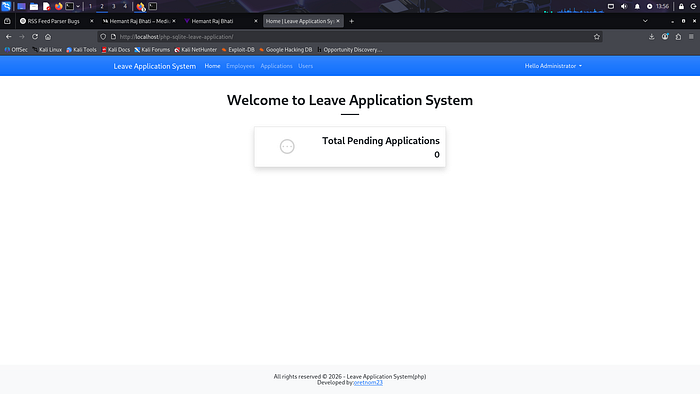
During security testing of the Leave Application System built with PHP and SQLite3, an IDOR vulnerability was discovered in the user management functionality. This issue allows attackers to access and modify other users' information simply by manipulating the user ID parameter in the request.
Affected Application
Application: Leave Application System in PHP and SQLite3 Version: 1.0
Source Code: https://www.sourcecodester.com/php/16403/leave-application-system-php-and-sqlite3-source-code-free-download.html
Vulnerability Type
Insecure Direct Object Reference (IDOR)
IDOR occurs when an application uses user-supplied input to directly access objects such as files, database records, or accounts without verifying whether the user has permission to access that resource.
This results in unauthorized access to sensitive information or functionality.
Vulnerable Endpoint
The vulnerability exists in the following endpoint:
?page=manage_user&id=The application directly uses the id parameter to fetch user data from the database without performing proper authorization checks.
Proof of Concept (PoC)
An attacker can manipulate the id parameter in the URL to access different user accounts.
Example 1
?page=manage_user&id=1The Administrator account becomes visible.
Example 2
?page=manage_user&id=2Another user's account information is displayed.
Example 3
?page=manage_user&id=3A different user profile is loaded.
This confirms that the application does not validate whether the logged-in user is authorized to access the requested account.
Steps to Reproduce
- Login to the application.
- Navigate to the User Management section.
- Open the following URL:
?page=manage_user&id=1- Modify the ID parameter:
?page=manage_user&id=2
?page=manage_user&id=3- Observe that different user profiles can be accessed without any authorization checks.
Impact
This vulnerability may allow attackers to:
- Access sensitive information of other users
- Modify other users' accounts
- Escalate privileges
- Take over administrator accounts
Successful exploitation could lead to a complete compromise of the application.
Screenshot Evidence
Add the following screenshots:

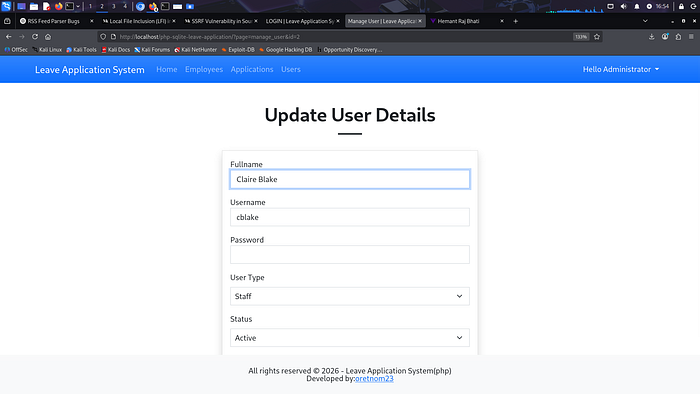

These screenshots demonstrate unauthorized access to multiple user accounts.
Root Cause
The application fails to enforce proper authorization checks when accessing user records.
Instead of validating whether the logged-in user is allowed to access the requested resource, the application directly trusts the user-supplied id parameter.
This results in unauthorized data access across multiple user accounts.
Recommended Fix
Developers should implement proper access control mechanisms to ensure that users can only access resources they are authorized to view.
Recommended mitigations include:
- Implementing authorization checks on every request
- Avoiding direct exposure of database identifiers
- Using session-based access validation
- Verifying user ownership before returning data
Example Secure Logic
if ($_SESSION['user_id'] != $_GET['id']) {
die("Unauthorized access");
}Conclusion
IDOR vulnerabilities occur when applications fail to properly validate access permissions for user-controlled object references.
Developers should enforce strict authorization checks and follow secure coding practices to ensure that users cannot access resources belonging to other users.
Proper access control implementation is essential to prevent unauthorized data access and account manipulation.
