Hello Hackers
I'm Mohamed, also known as Mado , a dedicated Web Application Penetration Tester and bug hunter
NOTE: The Write Up is hunting and The Write up Focus on 2 Bugs ,information disclosure , Open Redirect Get Your Coffee and Lets go If You Liked The Write up Don't Forget 50 Clapped And Thank you
First Bug (Information disclosure) Target Overview #1
My target is a program for documents. You can write anything in the documents and you can invite many people with different roles:
Viewer = Can only see documents and chat
Editor = Can change anything in documents only
Manager = Can change anything in documents and any member with a lower role

My Technique For Exploit :
I made the documents viewer available to everyone (public link). When I visit the link as a user outside the team, the attacker cannot see any information or anything here

But when I open the team chat, I can see all messages from all users in the team. I will write a message, send it, and catch the request to understand how it works

I changed the request method from POST to GET. The server Give me information in response about users in the team, even though I don't have permission to see all team members
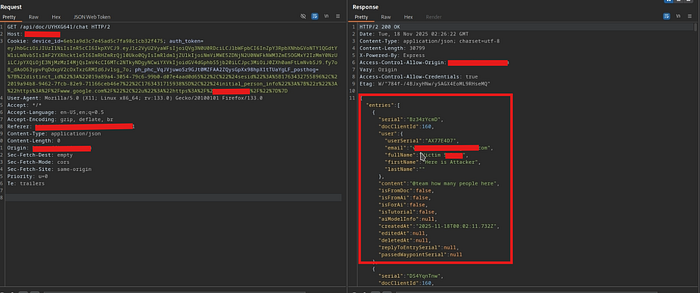
Here, the server give me all the emails, Names of users in the team after changing the request from POST to GET
Second Bug ( URL Bypass = Open Redirect ) Target Overview #2
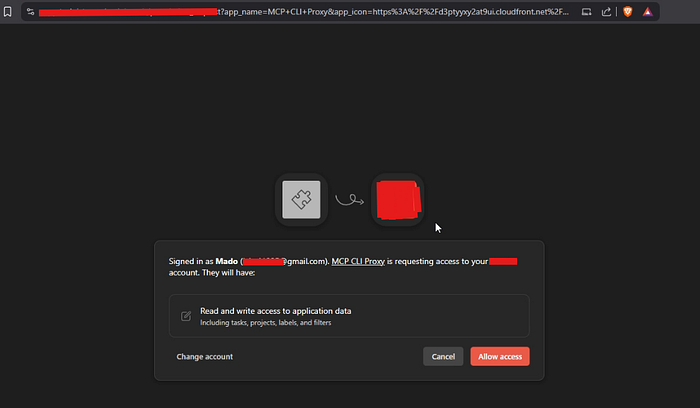
Target for writing your daily tasks, with roles and the ability to invite people with different roles. After recon, I found the MCP server endpoint
I saw The URL :
APP_ICON=HTTPS://BLABLABLA.COM
I changed the URL to evil.com, like:
APP_ICON=HTTPS://EVIL.COM
BUT IT DIDN'T WORK
I tried to bypass:
HTTPS://BLABLABLA.COM@Evil.com => NOT WORK
HTTPS://BLABLABLA.COM?Evil.com => NOT WORK
HTTPS://BLABLABLA.COM/Evil.com => NOT WORK
//evil.com => WORKING
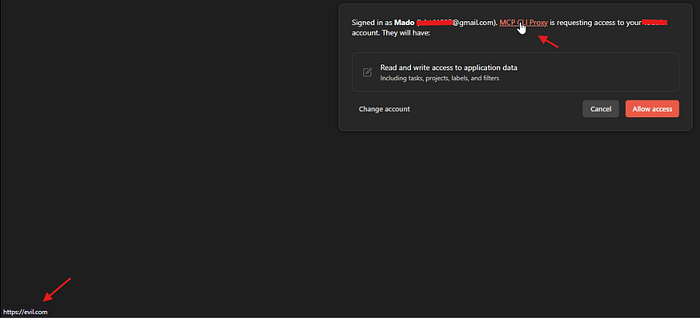
The last payload worked. Now anyone who clicks on MCP CU PROXY gets redirected
to Evil.com.Now if you look at my mouse on the MCP Proxy , check the bottom left side the redirect link to evil.com
The Third Bug ( Upload image = Open Redirect ) Target Overview #3
Target for writing your daily tasks, with roles and the ability to invite people with different roles
When I tried the target as an attacker, I saw the team chat and noticed that anyone can upload images. I attempted XSS, but it didn't work. , I tried Open Redirect, but through image upload
I am try
<?xml version="1.0" encoding="UTF-8"?>
<svg xmlns="http://www.w3.org/2000/svg" width="100" height="100">
<script>
window.location.replace("https://evil.com");
</script>
<circle cx="50" cy="50" r="40" fill="red" />
<text x="50" y="55" text-anchor="middle" fill="white">Click</text>
</svg>Now, when anyone open the chat and see the image, if the victim click on it, they get redirected to evil.com

The Results:
And I want to say that a bug doesn't have to appear immediately if it doesn't work in one place, the same scenario might lead to another bug elsewhere

If You Want To Reach Me All My Contact Info is Here : click_Here
If You Want Read More Blogs Check The Link : 0xMado-Gitbook
……………Thank You For Reading and I hope This Was helpful………………

