I participated in the FahemSec HackStart CTF, a fun, exciting, and informative competition for beginners. I enjoyed spending a Ramadan evening solving challenges with my colleague Areej. We managed to complete most of the web challenges, along with two crypto and two miscellaneous challenges. Here's a detailed write-up of our approach.
Biscuits→ Web
Checkup→ Web
Knock knock→ Web
Bot→ MISC
Rookie→MISC
Decoder→ Crypto
oneROX→ Crypto

Biscuits — Web
Objective: Access the admin-only section to retrieve the flag.


Only admins can access this, so our target is to become an admin user.
I will open Burp Suite to inspect the request — maybe I can find a vulnerability to exploit and bypass the admin check.
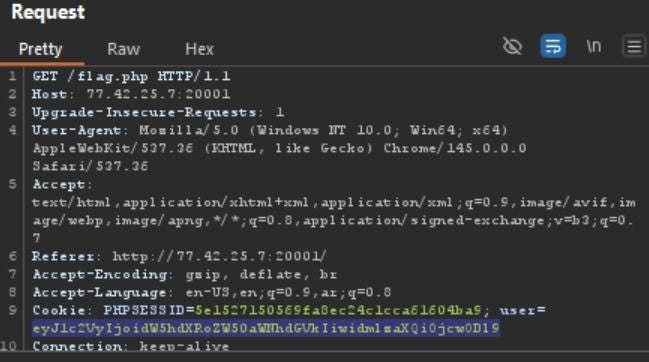
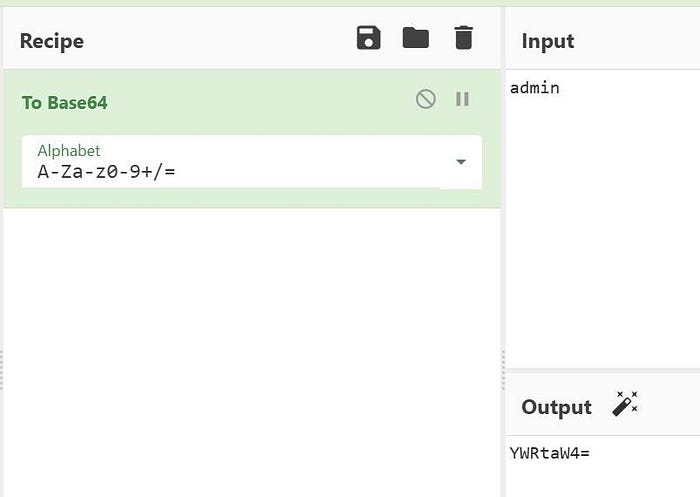
It looks like Base64-encoded data. Let's try decoding it using CyberChef.
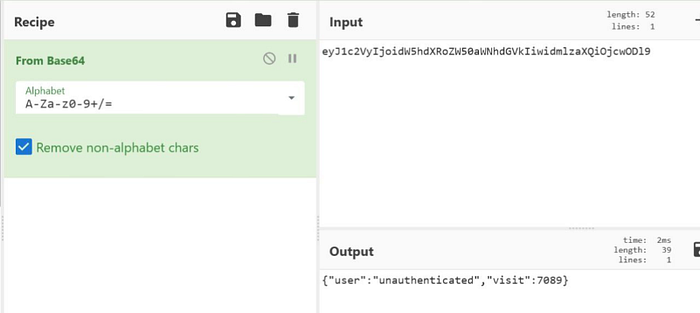
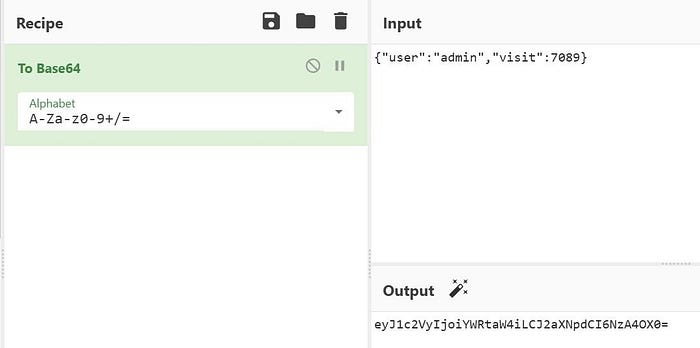
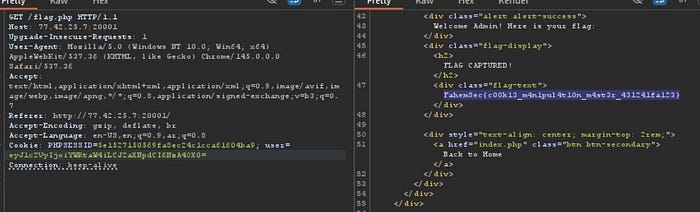
The Base64 value contained the role parameter (unauthenticated). After decoding it, I modified the role to admin, re-encoded the value, and sent the modified request. Since the server did not validate the role properly, I was able to access the admin panel and retrieve the flag.
Now, I can see the flag.
Checkup — Web
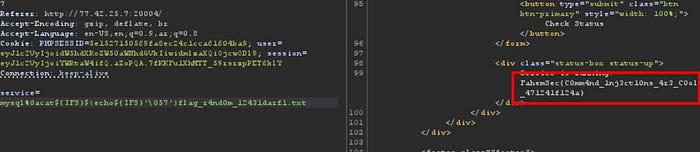
Objective: Exploit a command injection vulnerability.

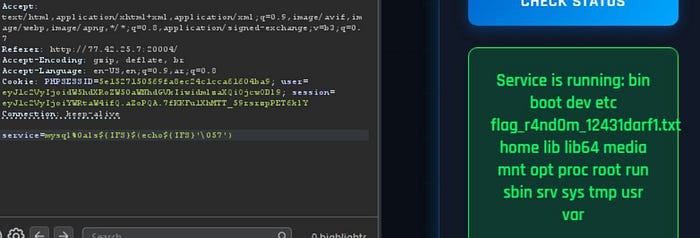
This is a basic command injection vulnerability with a filter on /, so we need to find a way to bypass it.
Knock Knock — Web
Objective: Exploit an IDOR vulnerability in password update.
The main target is to get the flag, so now I will create an account to see what I can do after logging in.
When I update the password, I can see my username in the request, but it is encrypted. This suggests a possible IDOR vulnerability in the change password functionality — so I will try changing the username to admin.
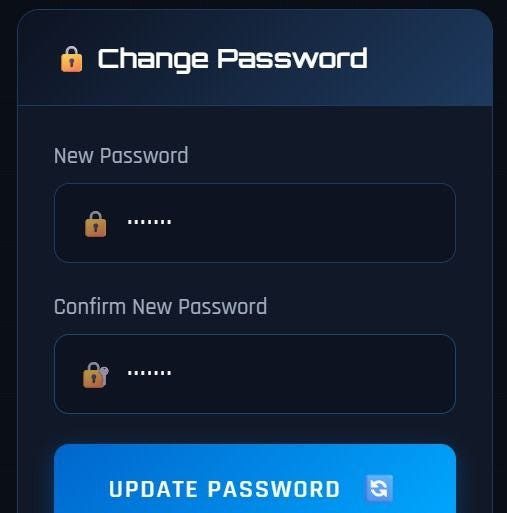


change it to admin and encrypt
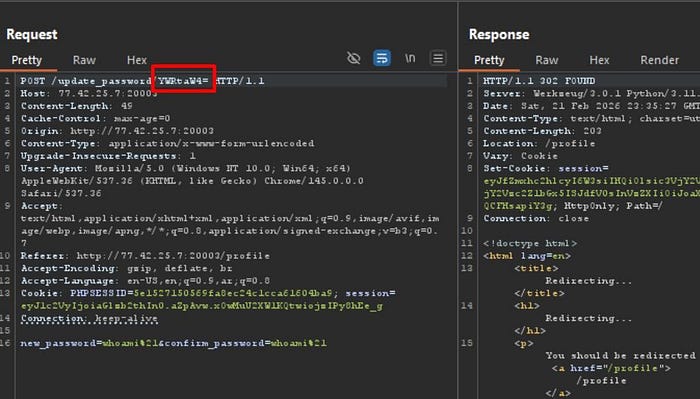
Log in using these credentials.

Rookie — Misc
Objective: Subdomain enumeration for FahemSec.
Using crt.sh :


oneROX — Crypto
Objective: Decrypt a hexadecimal cipher.
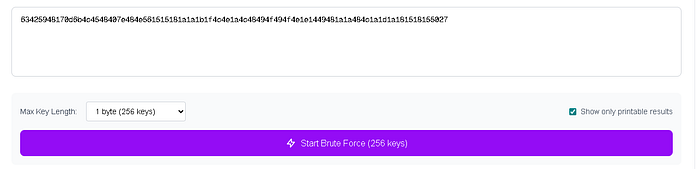
Want to decrypt this Cipher Hex = 63425948170d6b4c4548407e484e561515181a1a1b1f4c4e1a4c48494f494f4e1e1449481a1a484c1a1d1a181518155027
Convert Hex → ASCII

It does not look like normal readable text. There is likely another layer (XOR, Caesar, repeating key)
Run brute-force single-byte XOR :https://inventivehq.com/tools/security/xor-cipher

Decoder — Crypto
Objective: Decode a text message using a simple substitution.
- Text appeared easy to read but used a themed alphabet (Pokémon).

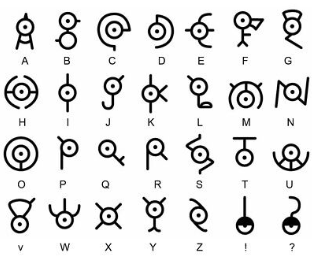
so the clear text is :
EASY FLAG LEET

Overall, it was a great opportunity to practice real-world hacking skills in a beginner-friendly environment.
