Autonomous AI with SQLMap: When Automation Starts Thinking for Itself
There was a time when running SQLMap felt powerful.
You'd drop into a terminal, feed it a target, tweak a few flags, and watch it probe an application for SQL injection vulnerabilities. It was technical, methodical, and a little bit thrilling. SQLMap has earned its reputation over the years as one of the most reliable open-source tools in offensive security.
But here's the honest truth: it still depended heavily on the human behind the keyboard.
https://github.com/drcrypterdotru/sqlmap-skynet

You had to interpret results. You had to adjust techniques. You had to decide when to escalate. You had to figure out how to bypass defenses.
That's where the idea of combining SQLMap with autonomous AI becomes interesting — not as hype, but as evolution.
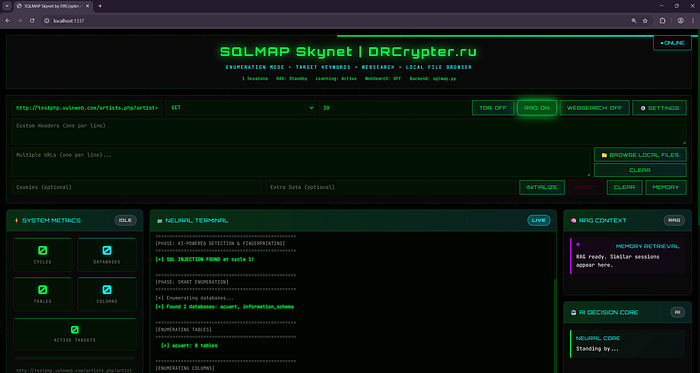
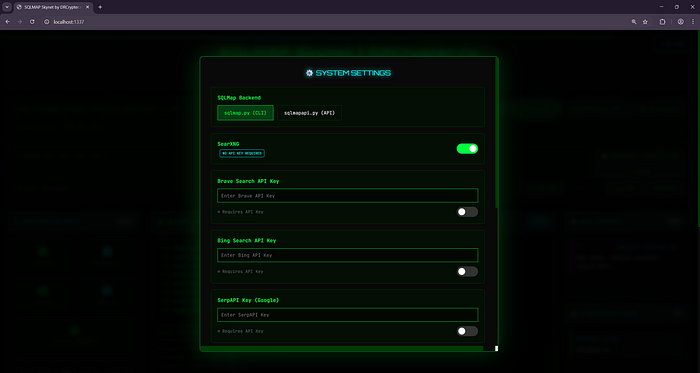
The project sqlmap-skynet explores exactly that direction: taking a trusted, battle-tested tool and wrapping it inside a decision-making layer that behaves more like a penetration tester than a script.
And that changes the conversation entirely.
SQLMap Is Powerful — But It's Linear
At its core, SQLMap is deterministic. You give it input. It tests. It reports.
It doesn't pause and think:
- "Maybe this WAF needs a different approach."
- "The response pattern suggests blind injection."
- "Let me pivot to a different enumeration strategy."
That's the human part.
A skilled tester reads between the lines — subtle timing changes, error structures, behavioral anomalies. Traditional automation doesn't "read," it just executes.
What sqlmap-skynet attempts to do is bridge that gap.
Instead of running SQLMap once and stopping, it orchestrates it in phases. It watches outputs. It adapts parameters. It structures the workflow into something closer to how a real engagement unfolds.
That shift — from execution to orchestration — is the real innovation.
What "Autonomous" Actually Means Here
Autonomous doesn't mean magic. It doesn't mean fully self-aware hacking robots. It means something more practical and more useful.
It means:
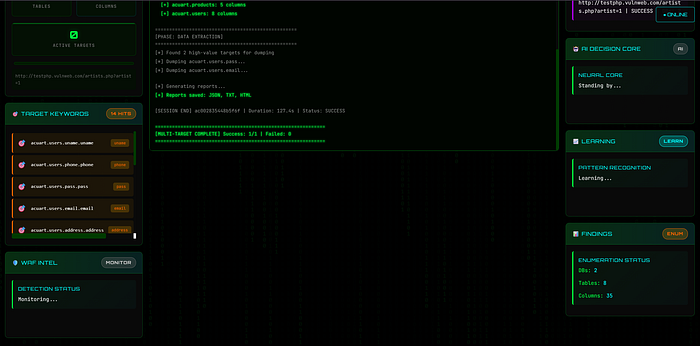
- The system can move through predefined phases (discovery → detection → exploitation → enumeration).
- It can adjust SQLMap flags dynamically.
- It can store past scanning patterns and reuse what worked.
- It can generate structured reporting automatically.
In other words, it doesn't just run SQLMap — it manages SQLMap.
And management is where intelligence matters.
Think of it like the difference between owning a powerful engine and building a vehicle around it. SQLMap is the engine. The AI layer is the driver, navigation system, and memory combined.
Memory Changes Everything
One of the most underrated aspects of adding AI into security tooling is memory.
Human testers get better over time because they remember:
- Which payloads bypassed certain filters
- Which response signatures indicated blind injection
- Which targets behaved similarly
If a tool can store and recall successful patterns, it begins to mimic that experience curve.
This is where retrieval-based memory systems (often referred to as RAG architectures) become interesting. Instead of starting from scratch every time, the system can reference previous knowledge and adjust strategies faster than a human manually reviewing logs.
That's not about replacing expertise. It's about compressing it.
The Dashboard Factor
Let's be honest — terminals are powerful but not always efficient.
Security professionals spend too much time parsing raw output. Scrolling. Re-running commands. Tracking logs across sessions.
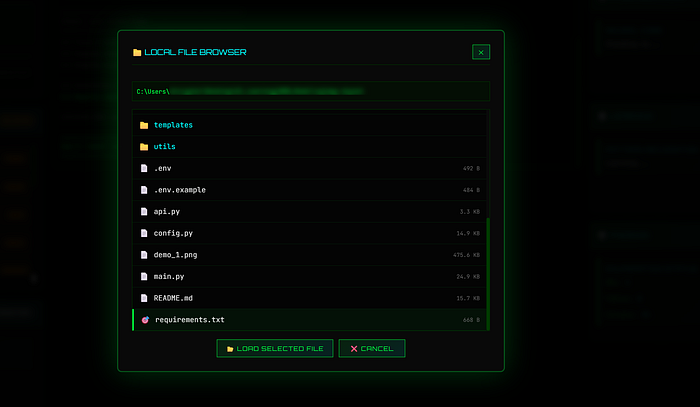
By adding a dashboard layer, the project shifts from "tool" to "platform."
Visualization matters:

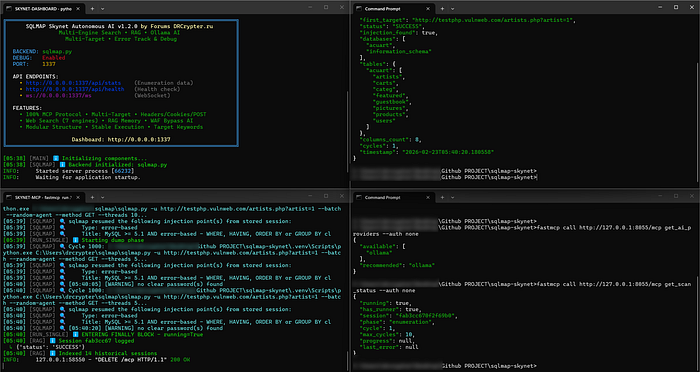
- You see progression stages.
- You understand what phase is active.
- You track decisions being made.
It creates transparency around automation, which is critical when AI is involved. Nobody wants a black box making decisions without visibility.
Why This Matters in 2026
Web applications are more complex than ever. They sit behind CDNs, layered WAFs, rate limiters, behavioral detection systems, and API gateways.
A static scan is rarely enough.
What modern security testing increasingly requires is adaptive probing — adjusting behavior in response to defenses. Humans can do this. Scripts struggle.
The combination of AI logic with established offensive tools represents a new model:
Not replacing tools. Not replacing humans. But amplifying both.
The Ethical Line
This is important.
Automation increases power. AI increases speed. Together, they reduce the skill barrier for exploitation.
That's both exciting and dangerous.
Projects like this must be used responsibly:
- Authorized penetration testing
- Controlled lab environments
- Defensive research
The same technology that helps secure infrastructure can harm it if misused. That's not unique to this project — that's true for every powerful security tool ever released.
With great automation comes great responsibility.
My Honest Take
The real story here isn't "AI hacks websites."
It's that security tooling is evolving from command execution toward intelligent orchestration.
That's a bigger shift than people realize.
The future of offensive and defensive security will likely look like this:
- Tools that reason about their own results
- Systems that remember patterns
- Workflows that feel less like scripts and more like junior analysts
SQLMap has always been a legend in its category. Wrapping it in autonomy doesn't change what it is — it changes how it's used.