Hunters🐺,
I have a new API Hacking write-up to share with you, this one is really crazy because it's just take some hours to find this API bug. You can read about other API Bugs:
I am not consistent with my hunting write-ups because of my recent job but thanks whoever reading my write-ups.
Introduction
Just after submitting API bug to my regular bug bounty program, I have decided to search for one of my faviourite brand bug bounty program and It turns out they have self-hosted bug bounty program.
I picked the global subdomain and ran subfinder for quick subdomains of the global subdomain:
subfinder -d company.com --all --recursive | anew subs.txtI have got so many subdomains but one of them looks intersting let's say it's ghost.company.com, and I quickly opened this subdomain domain in my browser and It turns out this is a very new subdomain of this company.
Fuzzing Patterns
I didn't even touch a single functionlaity of this subdomain. I quickly opened a new terminal and started fuzzing on this subdomain with multiple patterns. You can say, it's nothing but I am hunting on my instinct only 🕷️. These are some patterns for subdomains fuzzing:
ffuf -u https://FUZZghost.company.com/ -w wordlist.txt
ffuf -u https://FUZZ-ghost.company.com/ -w wordlist.com
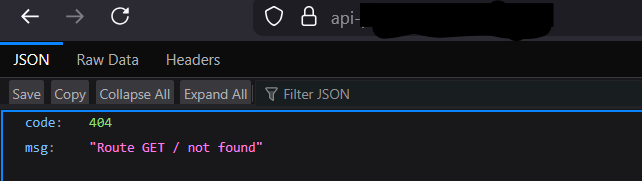
ffuf -u https://ghostFUZZ.company.com/ -w wordlist.com In some time, I got one hit api-ghost.company.com and it's nothing but 404 page saying Not Found.
I love to fuzz on 404 and Blank Pages.
I fired up my dirsearch to find any directory exposure with 200 Status Code.
dirsearch -u https://api-ghost.company.com/ -f -F -x 403,404 -t 3In 15 minutes, I got three directories exposed like /profile & /projects with 401 Status Code and other sensitive directories.

One of the directory is revealing json data like encrypted userId, projected and basic details:
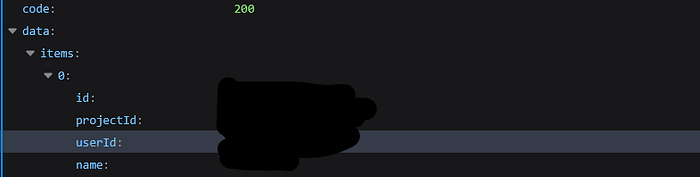
There are almost 700 members with unique userId's so I started fuzzing on id, projectId and userId with 10 unique Id's.
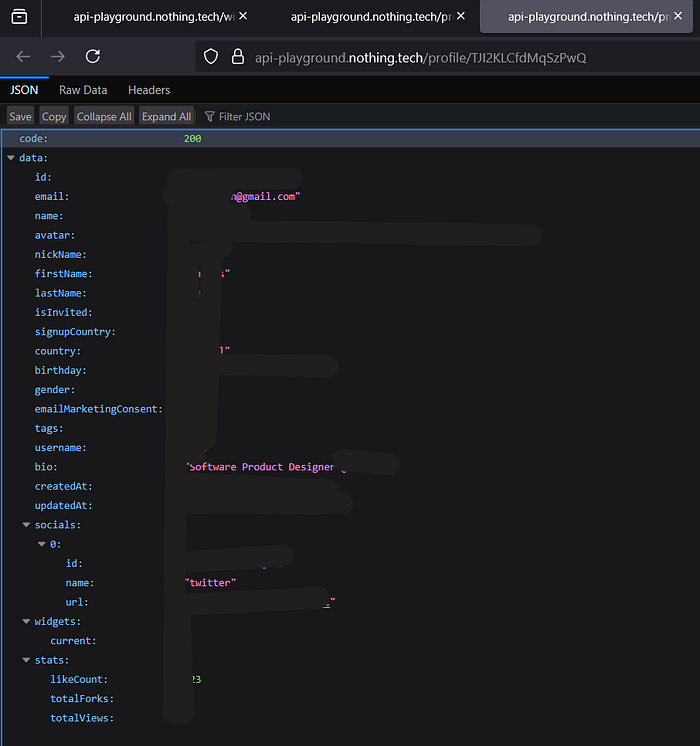
ffuf -u https://api-ghost.company.com/profile/FUZZ -w userids.txt- /projects/projectId → 401
- /profile/userId → 401
One path hits with 200 status code, /profile/id returns personal data of members including some of the company employees like personal email's of employee, date of birth, designation and other sensitive details.
Reporting
I reported this issue to security team, but It end-up being Internal Duplicate.

Enjoyed the read?
If you learn something or this article is helpful for you, as a token of appreciation you can send me:
50 claps, a comment and share everywhere.
Let's connect — I share more insights, bugs, and write-ups on

