This write-up is based on a training scenario from LetsDefend and is shared for educational purposes only.
Hello everyone, I'm Fir (find me on LinkedIn). In this article, I'll share my threat hunting investigation based on an IPS/IDS detection scenario involving OS Command Injection attacks. In this lab, I analyzed IPS/IDS logs to identify attacker infrastructure, exploited servers, and commands executed during the attack.
🧠 Hypothesis
Attackers may be attempting to exploit an OS Command Injection vulnerability on a web server to execute system commands and establish a remote connection to external infrastructure.
Step 1 — Identifying Attacker Sources
I started by reviewing IPS/IDS logs to identify how many distinct IP addresses were performing OS Command Injection attacks. Number of attacker IP addresses: 4
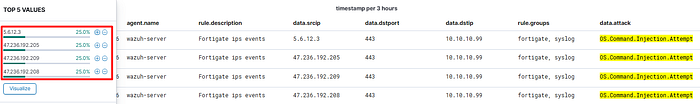
This indicates that multiple sources were attempting to exploit the same vulnerability.
Step 2 — Target Server Analysis
Next, I analyzed which servers were targeted by these attacks. Number of distinct target servers: 1
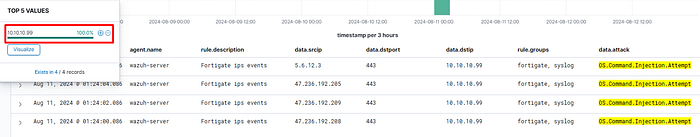
This suggests the attackers were focused on exploiting a specific vulnerable server.
Step 3 — Threat Intelligence Correlation
I checked the attacker IP addresses in the LetsDefend Threat Intelligence platform. Associated APT group:
APT-ZF-41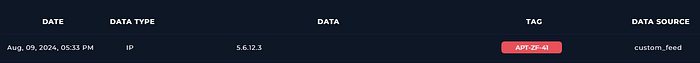
This indicates the attack infrastructure is linked to a known threat actor group.
Step 4 — Successful Attack & Command Execution
Next, I filtered IPS/IDS logs to identify any unblocked OS Command Injection attempts.
- Number of unblocked attacks: 1
- Command executed on the target server:
nc.exe
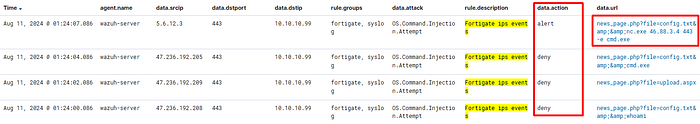
The use of nc.exe (Netcat) suggests the attacker attempted to establish a remote connection from the compromised server.
Step 5 — Process Context Investigation
To understand how the command was executed, I analyzed the process context.
- Parent process:
w3wp.exe - Username:
SYSTEM

This indicates the malicious command was executed through the IIS web server process with SYSTEM-level privileges, giving the attacker high control over the system.
Step 6 — Attack Method Analysis
Next, I reviewed the HTTP method used during the attack attempts. Number of unique IPs using POST method: 1
This suggests the injection payload was delivered through an HTTP POST request.
Step 7 — Outbound Connection Evidence
Finally, I investigated whether the compromised server attempted to connect to external infrastructure. Findings:
- Target IP address: 46.88.3.4
- Log ID confirming the successful connection: 0642134672
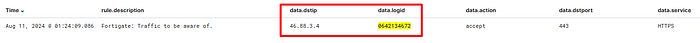
This indicates the command injection attack successfully triggered an outbound connection to attacker-controlled infrastructure.
Conclusion
By correlating IPS/IDS alerts, process execution context, and network logs, threat hunters can detect exploitation attempts and identify attacker infrastructure early. This investigation demonstrates how attackers can exploit web application vulnerabilities to execute system commands and establish remote connections to external infrastructure. By correlating IPS/IDS alerts, process execution context, and network logs, threat hunters can quickly identify exploitation attempts and detect potential command-and-control activity before it escalates further.
Thanks for reading! If you're exploring network-based threat hunting or web attack detection techniques, feel free to share what topic you're investigating next 👋🔥

