CVE with just Shodan Dorking ? Are you kidding ? 😈
Previously I never did community page OSINT as my first step and directly I used to search in shodan via titles.
Inspired by hacker_might, I adapted the methodology where first I must do recon of what people are complaining and asking in community, support and forum pages , more priority given where people attach screenshots of their issues.
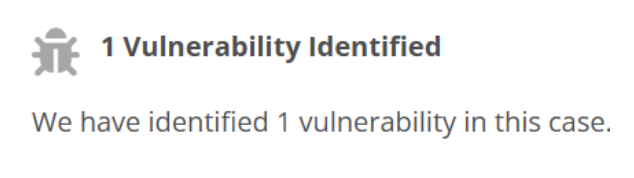
🪲 Google Dorks
site:community.*.* "web interface" "working"
site:support.*.* "dashboard" "port at"
#similarly
"admin panel"
"control panel"
"settings" "not working"
"backup" "not working"
#combine accordingly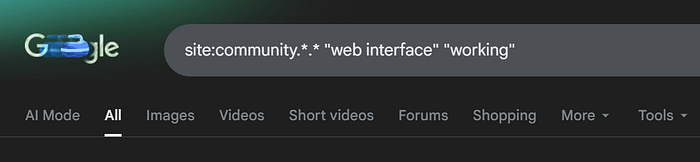
Just for example….

I never heard about this, but dorking led me to this page, and from this I got the keyword to search for in shodan.
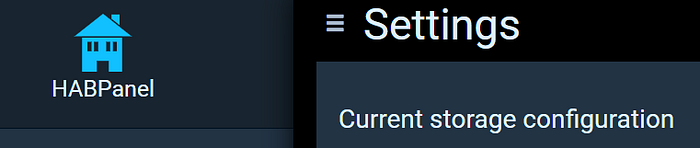
1️⃣ OpenHab
"openhab-ssl"
http.html:"/var/log/openhab/openhab.log"
http.html:"/var/log/openhab/events.log"
http.title:"openHAB" http.html:"home"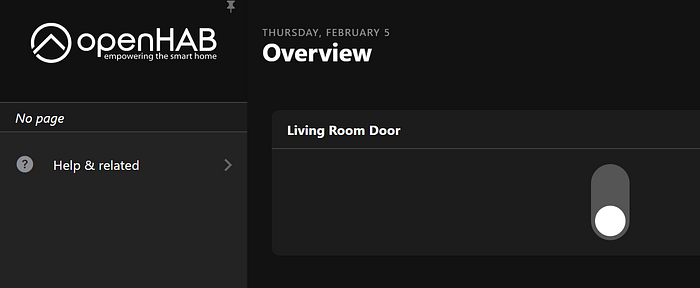
Endpoints
/start/index
/homebuilder/index.html
/cometvisu/?config=oh__default
/basicui/app
/paperui/index.html#/inbox/search
/habpanel/index.html#/settings
/habmin/index.html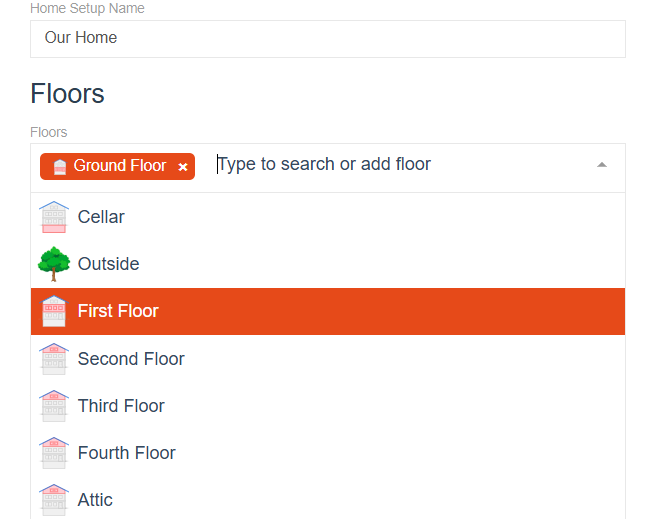
Similarly,
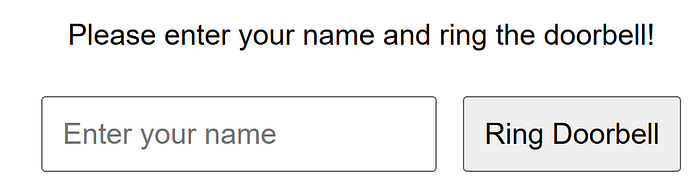
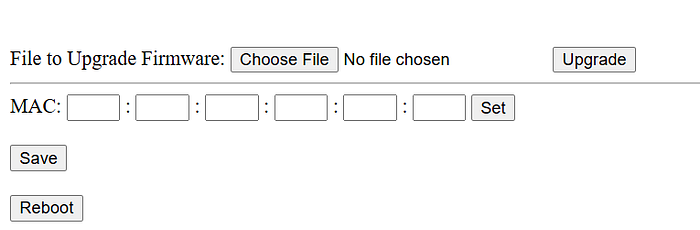
2️⃣ Doorbell
http.title:"doorbell"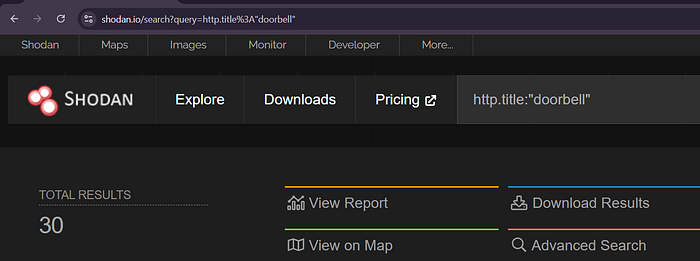
Always report ethically (if eligible!). And some are honeypots. So verify first.
I have a lot to demonstrate, but for current moment this was it for this article!
If you think you found a valid vulnerability, where the vendor need to fix it, you may report via kb[.]cert[.]org/vuls/vulcoordrequest/
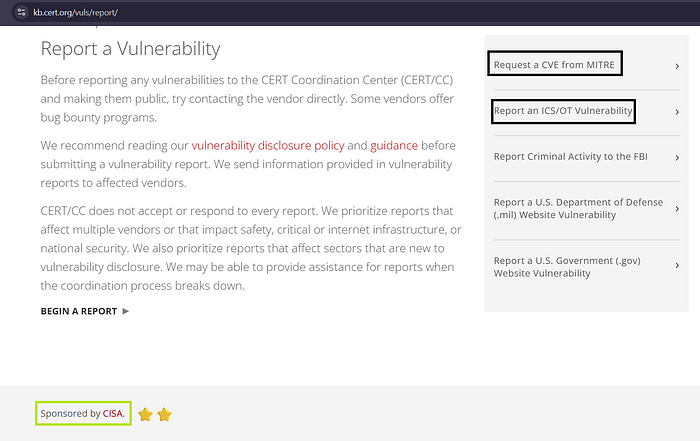

However, if it's a misconfiguration by the customer of the vendor. Then it's not accepted as a valid risk.
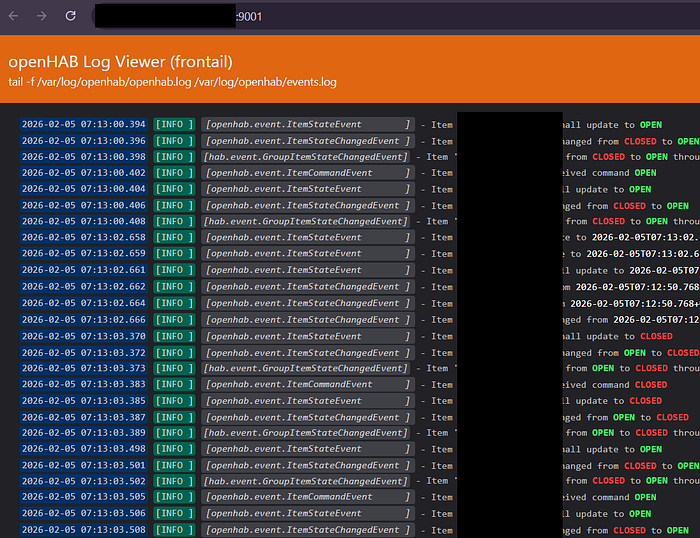
This part below is completely different from above. I reported two vulnerabilities. One got rejected with this saying
REJECTED: Response if you report misconfiguration bug associated with only individual customer 🥲
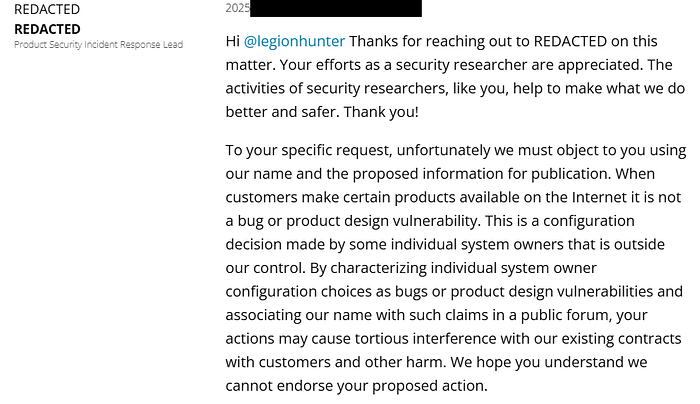
CVE : Response if you find a valid vulnerability in the product of the vendor
My first CVE coming soon. But i have permission to only disclose it only after 4–5 months :) So that all it's customers update their version first and then the attack surface will be minimal or almost zero till then.
Hope you learned the process, methodology & mindset behind how I do Deep OSINT based RECON that leads to interesting opportunities.
Detailed blog coming soon for my first CVE.