
Intro
What is Redis?
Redis, originally short for Remote Dictionary Server, is an open-source, in-memory data store commonly used as a cache, database, streaming engine, message broker, and queue. Redis stores data primarily in memory, which makes it extremely fast compared with disk-backed databases. It supports multiple data structures, including strings, hashes, lists, sets, sorted sets, streams, JSON, and geospatial indexes. (Redis)
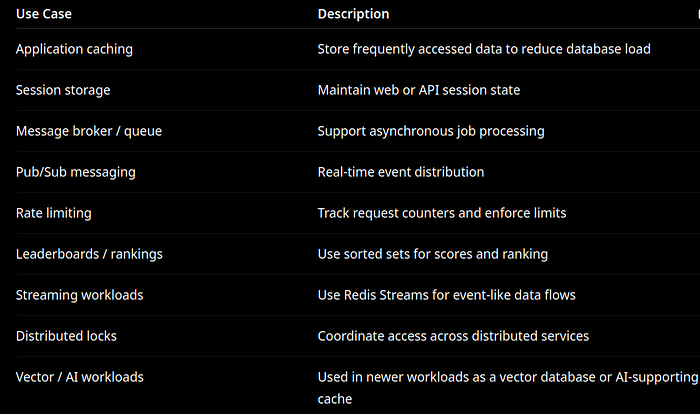
Common Redis Use Cases
Redis is commonly deployed for:
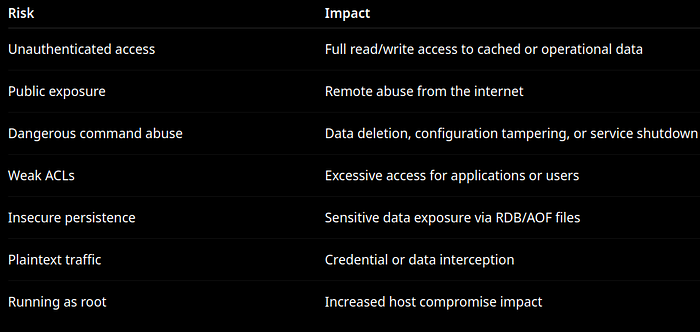
Why Redis Security Matters
Redis is often deployed close to application workloads and may contain sensitive operational data, session tokens, cached database responses, API results, queues, or business logic state. A poorly secured Redis instance can expose an attacker to:
1. Network Exposure (Critical)
Redis was never designed to be internet-facing.
Risks
- Unauthorized access
- Remote command execution via CONFIG / MODULE LOAD
- Data exfiltration
Hardening
bind 127.0.0.1
protected-mode yes
port 6379Or better:
- Bind to private subnet only
- Enforce security groups / firewall rules
SOC Detection
- External connections to port 6379
- Unexpected source IPs
- Use of
INFO,CONFIG,KEYS
2. Authentication & Authorization
Problems
- Default Redis = no authentication
- Single shared password model is weak
Hardening (Preferred: ACLs)
user default off
user appuser on >StrongPassword ~* +@allSOC Use Cases
- Detect:
AUTHfailures- privilege escalation attempts
- access to restricted commands
3. Dangerous Commands
These are frequently abused in attacks:
- FLUSHALL
- CONFIG
- SHUTDOWN
- MODULE LOAD
Hardening
rename-command FLUSHALL ""
rename-command CONFIG ""
rename-command SHUTDOWN ""
Detection
- Any invocation attempt = high severity alert
4. Encryption (TLS)
Redis supports TLS but it's often not enabled.
Hardening
tls-port 6379
port 0
tls-cert-file /etc/redis/cert.pem
tls-key-file /etc/redis/key.pem
tls-ca-cert-file /etc/redis/ca.pemSOC Monitoring
- Detect plaintext Redis traffic internally
- Flag non-TLS connections
5. Persistence Security
Risks
- RDB/AOF files may contain sensitive data
- Attackers can drop malicious payloads via writable dirs
Hardening
chmod 600 /var/lib/redis/*
chown redis:redis /var/lib/redis6. Runtime & OS Hardening
Critical Controls
- Run as non-root:
ps aux | grep redis- Systemd:
User=redis
NoNewPrivileges=yes
PrivateTmp=yes7. Logging & Monitoring
Enable:
loglevel notice
logfile /var/log/redis/redis.logSOC Integration
- Ship logs to SOCFortress SIEM
- Parse: AUTH events, CONFIG changes, connection spikes
8. Detection Use Cases (SOC)
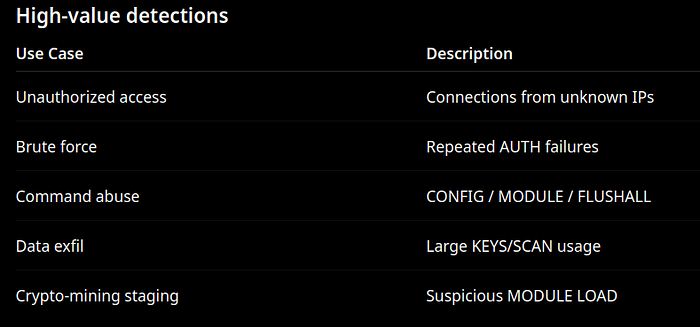
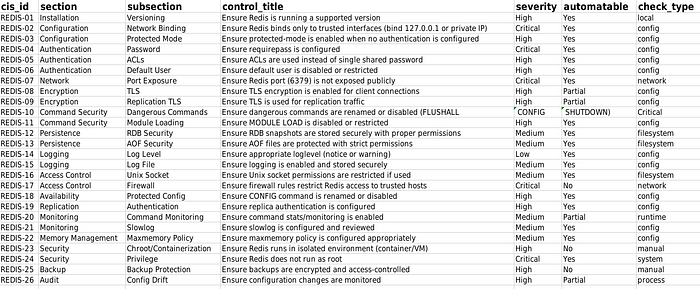
List of Controls
Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Contact Us: https://www.socfortress.co/contact_form.html
