Most Indian startups that get hacked don't get a notification. There's no dramatic ransom screen, no cryptic message from a hacker. The breach happens quietly — usually months before anyone notices — and by the time it surfaces, the damage is already done. Customer data has been sold. Credentials have been reused. A competitor has read your internal roadmap.
This isn't a hypothetical. It's the pattern that plays out repeatedly in breach investigations.
The uncomfortable truth: if you've never actively looked for vulnerabilities in your infrastructure, you almost certainly have them. The question isn't if — it's how deep.
The Entry Points Nobody Audits
1. Exposed APIs with no rate limiting or auth checks
Your mobile app talks to your backend. Your SaaS product has an API. What authentication sits between a random internet request and your user data?
Many startups build APIs fast — as they should — but authentication gets bolted on as an afterthought. The result: endpoints that accept requests from anyone. Sometimes they're accidentally exposed to the public internet. Sometimes internal APIs meant only for your admin panel get indexed by Shodan within days of deployment.
OWASP calls this Broken Object Level Authorization — the top API vulnerability category globally. In India, where SaaS is shipping at startup pace, it's epidemic.
2. Default credentials on cloud infrastructure
Your staging database. Your Kubernetes dashboard. Your Redis instance. Your internal monitoring tool.
A staggering number of breaches trace back to credentials that were never changed from their defaults — admin/admin, root/root, factory passwords on cloud management consoles. The attacker doesn't need to be sophisticated. They scan, they try defaults, they're in.
Staging environments are particularly dangerous. They're treated as non-critical — so they don't get the same hardening — but they often share databases, secrets, or service accounts with production.
3. Unpatched staging and dev environments
Production gets updated. Dev gets forgotten.
Dev and staging environments run old versions of libraries. They have debug endpoints left open. They have verbose error messages that reveal stack traces, database schema information, and internal service paths. They use the same AWS IAM roles as production, sometimes with broader permissions.
An attacker who gets into your staging environment often has a lateral path to production. The "non-critical" label is the vulnerability.
4. Open S3 buckets and misconfigured cloud storage
This one should be dead by now. It isn't.
Open S3 buckets — public-read objects containing customer exports, internal backups, KYC documents, financial records — remain one of the most common findings in any cloud security audit. The misconfiguration is trivially easy to make and trivially easy to find using tools that scan public cloud storage continuously.
If your team provisions S3 buckets regularly, and there's no CSPM tool watching for public access permissions being flipped on, you're flying blind.
5. Third-party integrations with unscoped access
Your product integrates with payment gateways, marketing platforms, analytics SDKs, support tools. Each integration is a potential attack surface. Most teams grant integrations the permissions needed to get it working — not the minimum permissions needed for security.
A compromised third-party vendor is now your problem too. Supply chain attacks aren't just a concept for enterprise — they reach into every startup that installs npm packages without auditing them or grants OAuth scopes without reviewing them.
The Delay That Costs Everything
IBM's Cost of a Data Breach 2024 report places the India average at ₹19.5 crore per breach. But the less-discussed finding is the time to detect: the average organization takes 194 days to identify a breach and another 64 days to contain it.
That's over eight months of an attacker living inside your systems. Reading your emails. Watching your pipeline. Extracting data in trickles too small to trigger alerts.
For a startup, this isn't just a financial loss — it can be fatal. Enterprise customers doing due diligence before signing will find it. Investors in your Series A process will find it. CERT-In expects breach notification within 6 hours of discovery — if you discover it eight months late, you're already non-compliant.
What "Looking" Actually Means
Security isn't a checkbox. It's a practice. But there's a practical starting point: know your attack surface.
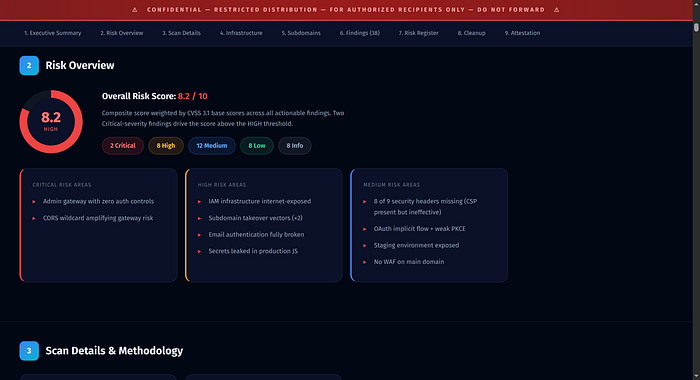
A proper VAPT (Vulnerability Assessment and Penetration Test) using CERT-IN grade methodology will tell you what an attacker sees when they look at your infrastructure. Not just what tools report — what a human expert, given time and context, can actually exploit.
Most startups delay this because they assume it's expensive or disruptive. The reality: catching a critical vulnerability before it's exploited costs a fraction of what remediation, customer notification, and reputational repair costs after.
The startups that find out about a breach last are the ones who never looked.
If you want to know what your infrastructure looks like from the outside, Bachao.AI offers a free security scan. CERT-IN grade methodology, AI-native automated scanning with expert verification. No finding, no charge.
Start at Bachao.AI. The first look costs nothing.
— Shouvik Mukherjee is the Founder & CEO of Bachao.AI (Dhisattva AI Pvt Ltd, DPIIT Recognized). He is an Ex-Principal Engineer and TEDx Speaker with deep roots in cybersecurity.