Challenge Scenario:
After having a severe attack from the Boogeyman, Quick Logistics LLC improved its security defences. However, the Boogeyman returns with new and improved tactics, techniques and procedures.
In this room, you will be tasked to analyse the new tactics, techniques, and procedures (TTPs) of the threat group named Boogeyman.
Maxine, a Human Resource Specialist working for Quick Logistics LLC, received an application from one of the open positions in the company. Unbeknownst to her, the attached resume was malicious and compromised her workstation.
The security team was able to flag some suspicious commands executed on the workstation of Maxine, which prompted the investigation. Given this, you are tasked to analyse and assess the impact of the compromise.
- What email was used to send the phishing email?
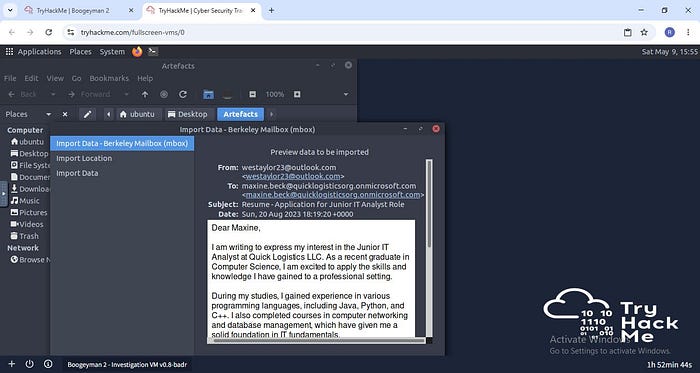
Answer: westaylor23@outlook.com
2. What is the email of the victim employee?
Answer: maxine.beck@quicklogisticsorg.onmicrosoft.com
3. What is the name of the attached malicious document?
Answer: Resume_WesleyTaylor.doc
4. What is the MD5 hash of the malicious attachment?
First we save the attachment file in the artefacts directory, than we use the below command line: md5sum "file name"
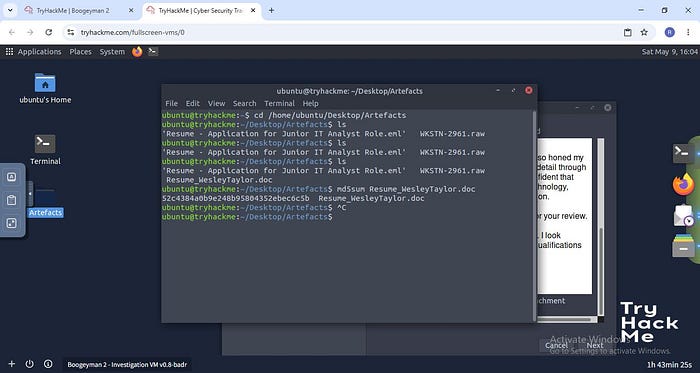
Answer: 52c4384a0b9e248b95804352ebec6c5b
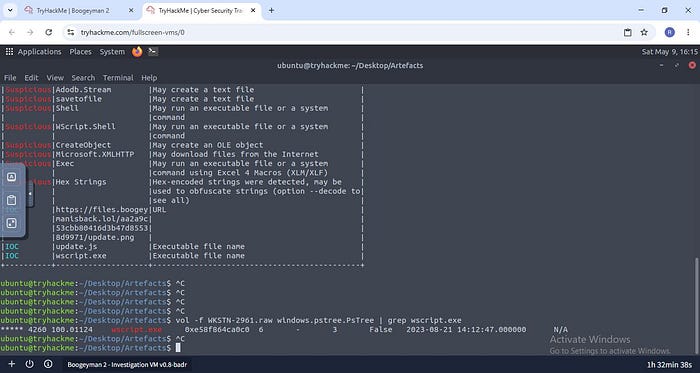
5. What URL is used to download the stage 2 payload based on the document's macro?
For this step we use olebve(this was a first time using this tool so a simple Open source search was the way to go)
Command used:olevbe "file name"
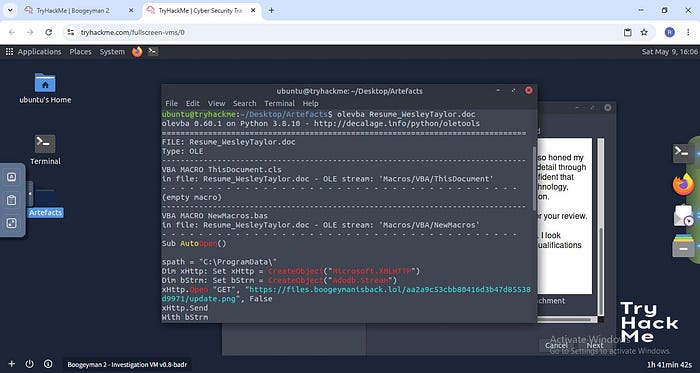
Answer: https://files.boogeymanisback.lol/aa2a9c53cbb80416d3b47d85538d9971/update.png
6. What is the name of the process that executed the newly downloaded stage 2 payload?
Answer: wscript.exe
7. What is the full file path of the malicious stage 2 payload?
Answer: C:\ProgramData\update.js
The 6,7 answers are found on the picture above.
8. What is the PID of the process that executed the stage 2 payload?
Now for this step we use volatility framework(also my first time using this tool)
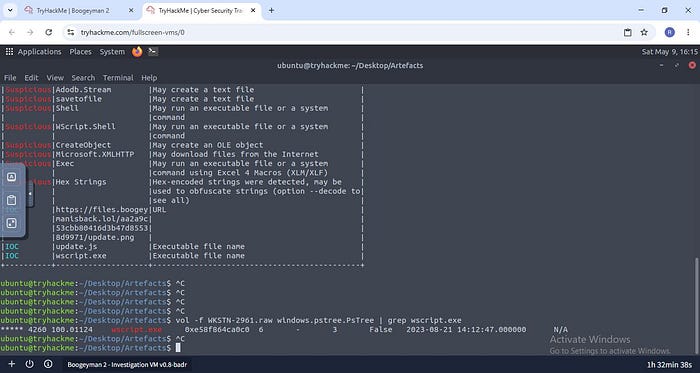
Command: vol -f WKSTN-2961.raw windows.pstree.PsTree | grep wscript.exe
Answer: 4260
9. What is the parent PID of the process that executed the stage 2 payload?
Answer: 1124
10. What URL is used to download the malicious binary executed by the stage 2 payload?
Answer: https://files.boogeymanisback.lol/aa2a9c53cbb80416d3b47d85538d9971/update.exe
11. What is the PID of the malicious process used to establish the C2 connection?
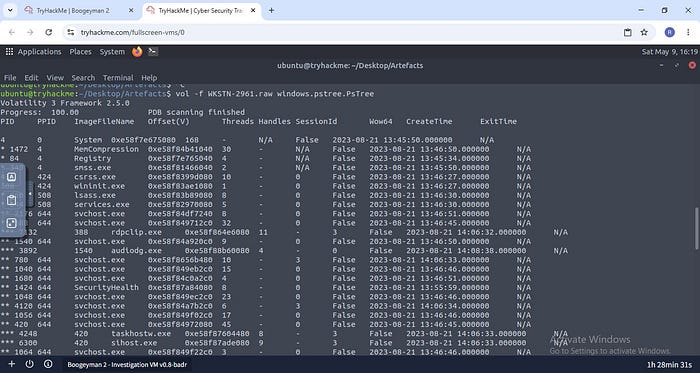
Cmd: vol -f WKSTN-2961.raw windows.pstree.PsTree
Answer: 6216
12. What is the full file path of the malicious process used to establish the C2 connection?
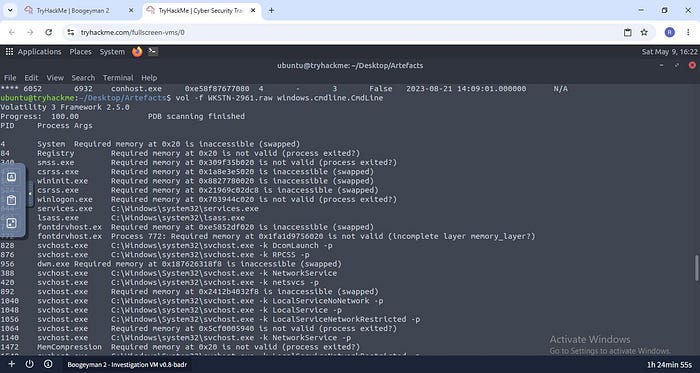
Answer: C:\Windows\Tasks\updater.exe
13. What is the IP address and port of the C2 connection initiated by the malicious binary? (Format: IP address:port)
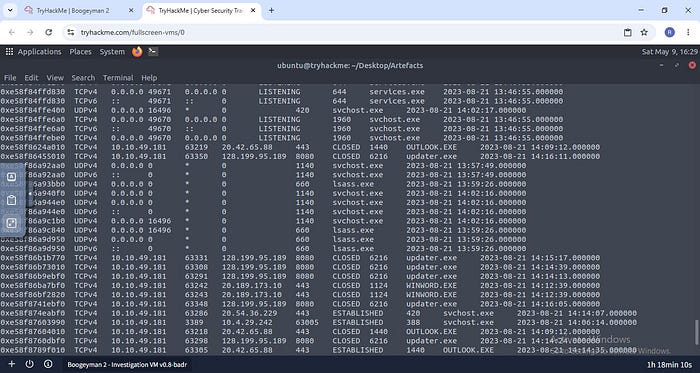
Cmd:vol -f WKSTN-2961.raw windows.netscan
Answer: 128.199.95.189:8080
14.What is the full file path of the malicious email attachment based on the memory dump?
Answer: C:\Users\maxine.beck\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\WQHGZCFI\Resume_WesleyTaylor (002).doc
15. The attacker implanted a scheduled task right after establishing the c2 callback. What is the full command used by the attacker to maintain persistent access?
Cmd: strings WKSTN-2961.raw | grep schtasks
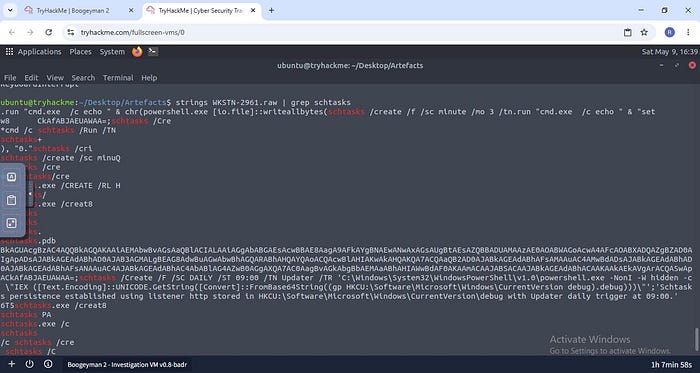
Answer: schtasks /Create /F /SC DAILY /ST 09:00 /TN Updater /TR 'C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NonI -W hidden -c \"IEX ([Text.Encoding]::UNICODE.GetString([Convert]::FromBase64String((gp HKCU:\Software\Microsoft\Windows\CurrentVersion debug).debug)))\"'
That's all for this challenge
Thank you:)
