Hi everyone, It's been a while since my last write-up. Today, we'll go through a very interesting (and quite straightforward) challenge from HTB called ReactOOPs, which highlights a critical vulnerability known as React2Shell.
This vulnerability has a CVSS score of 10.0 (Critical) and was discovered in 2025 (CVE-2025–55182). I remember it popping up over a weekend — always a great time for new exploits to drop 😄
🧩 Initial Analysis
I started by downloading the challenge ZIP file and opening it in VS Code to explore the source code.
The first thing that caught my attention was the package.json file. The project name react2shell immediately hinted at the possible attack vector.
So the first question I asked myself:
Which version of React is vulnerable?
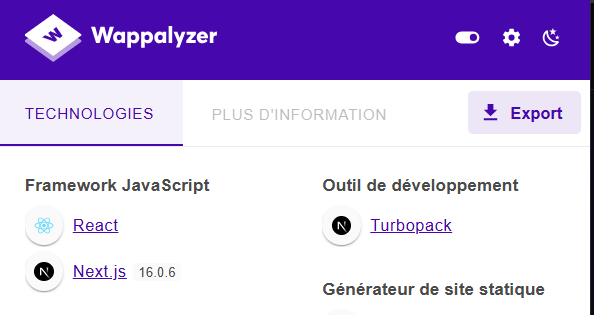
After a bit of research, I found that React 16.x is affected. Using tools like Wappalyzer confirmed that the application was running React 16.0.6.
💣 Exploitation
With that information, I searched for a public exploit and found one on GitHub:
After running the exploit against the target, I successfully gained a shell.
🗂️ Post-Exploitation
Once inside, I went back to the challenge source code to locate the flag. Looking at the Dockerfile, I found that the flag was stored in:
COPY challenge/flag.txt /app/flag.txtNavigating there from the shell revealed the flag, completing the challenge.
🧠 Takeaway
This challenge was quite simple, but it reinforces an important lesson:
Building a pentester mindset is what truly matters.
Always:
- Observe carefully
- Think about possible vulnerabilities
- Then act
Recognizing patterns like "React2Shell" quickly can save a lot of time
That's it for this write-up. See you soon with another challenge or security insight 🚀