In the modern landscape of web development, simple authentication measures like basic API keys or passwords are no longer sufficient to protect sensitive data. As APIs become the backbone of interconnected services, they are increasingly targeted by sophisticated attacks. To build a truly secure system, developers must adopt a multi-layered defense-in-depth strategy.
This guide explores the essential mechanisms for securing your REST API, ranging from request integrity and replay protection to traffic management and transport security.
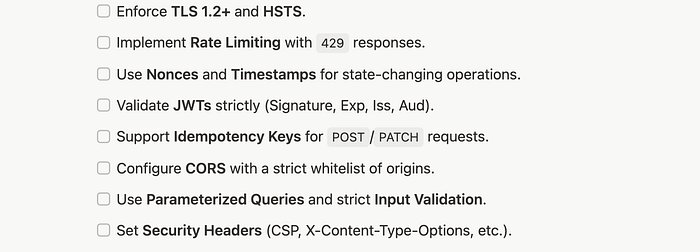
- The Foundation: Transport Layer Security (TLS) All other measures are useless if the data is sent over an unencrypted connection. TLS (the successor to SSL) is the non-negotiable foundation of API security.
Best Practices:
- Enforce HTTPS: Never allow plain HTTP requests.
- Modern Versions: Disable SSLv3, TLS 1.0, and TLS 1.1. Enforce TLS 1.2 or 1.3.
- HSTS: Use HTTP Strict Transport Security to force encrypted connections.
2. Cross-Origin Resource Sharing (CORS) Configuration
If your API is accessed from a browser, CORS is your first line of defense against cross-site request forgery and unauthorized data access.
Secure CORS Practices:
- Whitelisting Origins: Never use Access-Control-Allow-Origin: * in production. Explicitly list the domains allowed to call your API.
- Restricted Methods: Only allow the specific HTTP methods (GET, POST, etc.) your API supports.
- Credential Control: Only set Access-Control-Allow-Credentials: true if absolutely necessary for cookies or HTTP auth.
3. Traffic Management: Rate Limiting and Throttling
To protect your API from abuse, accidental loops, or Denial-of-Service (DoS) attacks, you must implement Rate Limiting.
Key Strategies:
- Token Bucket: Allows for bursts of traffic while maintaining a steady average rate.
- Standard Headers: Inform clients of their status using X-RateLimit-Limit, X-RateLimit-Remaining, and X-RateLimit-Reset.
- Error Code: Return a 429 Too Many Requests status code when limits are exceeded.
4. Input Validation and Sanitization
Many API breaches occur because the server trusts the data sent by the client. Input Validation is the practice of ensuring data matches the expected format, type, and length.
Prevention Techniques:
- Schema Validation: Use tools like JSON Schema or Joi to enforce strict data structures.
- Parameterized Queries: Always use prepared statements for database queries to prevent SQL Injection.
- Sanitization: Strip or escape dangerous characters (like <script> tags) to prevent Cross-Site Scripting (XSS).
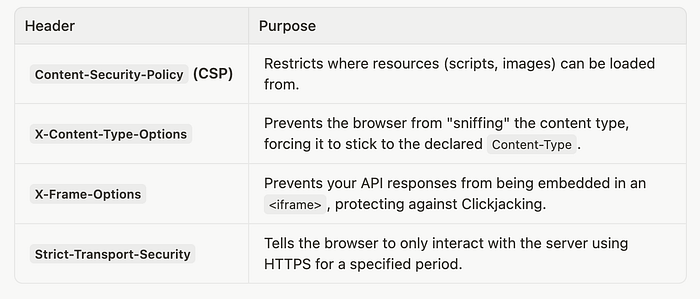
5. Hardening with HTTP Security Headers Beyond CORS and TLS, several specific HTTP headers can harden your API's response and protect the clients consuming it.
6. Preventing Replay Attacks with Nonce A nonce (number used once) is a unique, random string generated for each request. Its primary purpose is to prevent replay attacks, where an attacker intercepts a legitimate request and re-sends it multiple times to achieve a malicious result, such as duplicating a payment or an account creation.
How it Works:
i. Generation: The client generates a unique, one-time-use string and includes it in the request header.
ii. Tracking: The server maintains a temporary record of all nonces received within a specific timeframe.
iii. Validation: If a request arrives with a nonce that has already been used, the server immediately rejects it.
Tip: Use Redis to track nonces with a short TTL (e.g., 5–15 minutes).
When client sends:
X-Request-Nonce: a83hf938hf93
if(redis.exists(nonce))
reject_request()
else
redis.store(nonce, ttl=5min);6. Ensuring Request Freshness (Timestamping) Even with nonces, a captured request could potentially be replayed if the tracking window is too wide. Request freshness involves adding a timestamp to each API call to ensure it was initiated recently.
Why it Matters: By comparing the request's timestamp with the current server time, you can restrict the validity of a request to a very narrow window (e.g., +/- 60 seconds). This significantly limits the window of opportunity for an attacker.
Handling Clock Skew: Always allow a small margin of error (e.g., 30–90 seconds) when validating the timestamp to account for natural drift between client and server clocks.
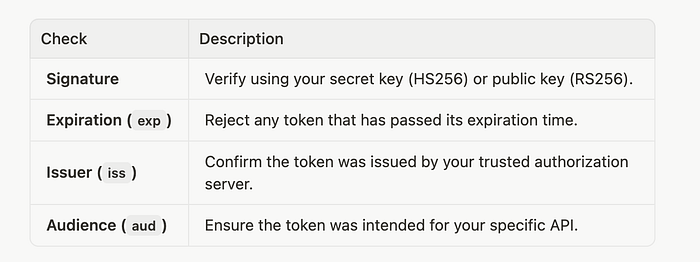
7. JWT Validation JSON Web Tokens (JWTs) are the industry standard for stateless authentication. However, receiving a token is only the first step; you must verify it rigorously on every request.
Essential Validation Steps:
8. Reliability with Idempotency Idempotency ensures that making the same request multiple times has the same effect as making it once. This is critical for handling network retries safely, especially for POST operations.
9. Implementation via Idempotency-Key: i. Client Key: The client sends a unique UUID in the Idempotency-Key header. ii. Server Cache: The server processes the request and stores the result indexed by that key. iii. Deduplication: If the same key is received again, the server returns the cached result instead of re-executing the logic.
Conclusion Securing a REST API is an ongoing process of improvement. By combining these ten layers — from Nonces and HMAC for integrity to CORS and Input Validation for server-side hardening — you create a robust infrastructure that protects both your data and your users.
Summary Checklist: