Information Disclosure is a security vulnerability where a system or application unintentionally exposes sensitive or internal information to users. This means that information is visible that is not intended for normal users to see.
Hey me dear reader…..
This lab from the PortSwigger Web Security Academy demonstrates how sensitive information can be exposed through version control history.Modern applications often use version control systems such as Git to track changes in the source code. While this is essential for development, accidentally exposing version control files on a public server can allow attackers to access the entire project history.
This can reveal sensitive information that was previously removed from the code but still exists in the commit history.
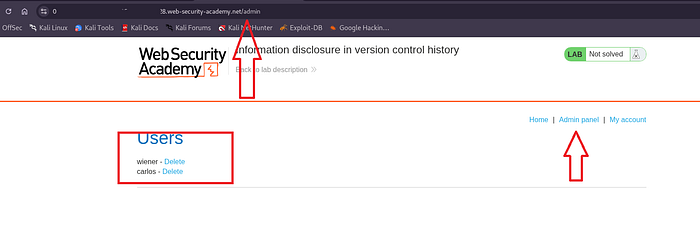
This lab exposes sensitive information through its version control history. To solve the lab, we need to get the password of the admin user, then log in and delete the user Carlos.
Version control systems track every change made to a project. If the version control directory becomes publicly accessible,
attackers may obtain:
- previous versions of the source code
- deleted credentials
- developer comments
- configuration files
- API keys or tokens
Even if sensitive information was removed later, it may still exist in the history.
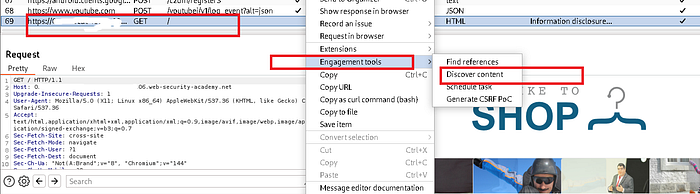
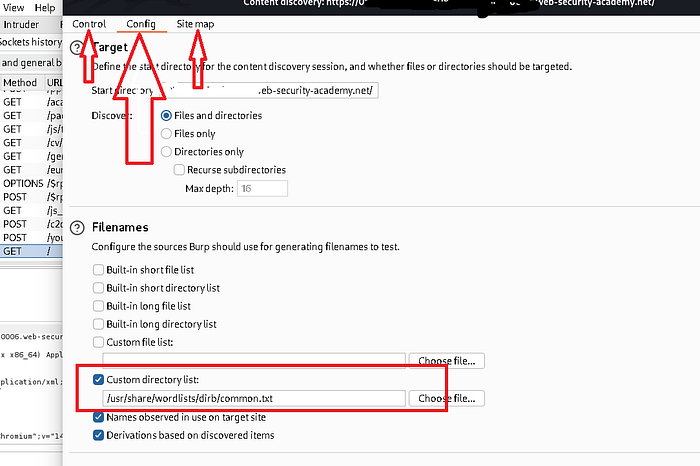
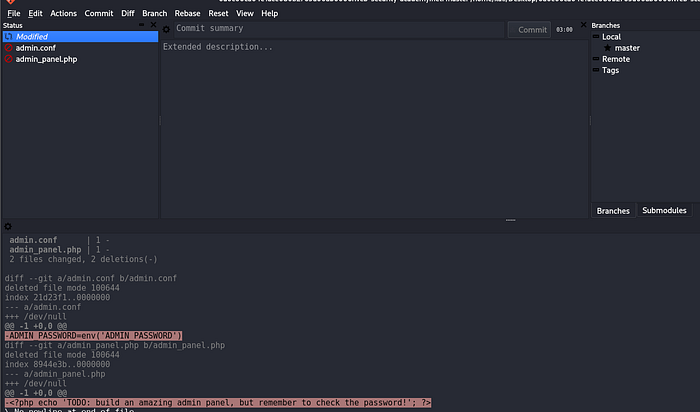
We content discovers here through the burp suite engagement tool. You can use /other tools if you want.
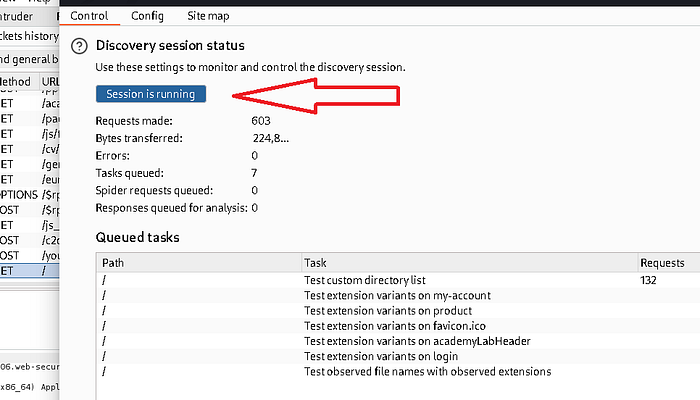
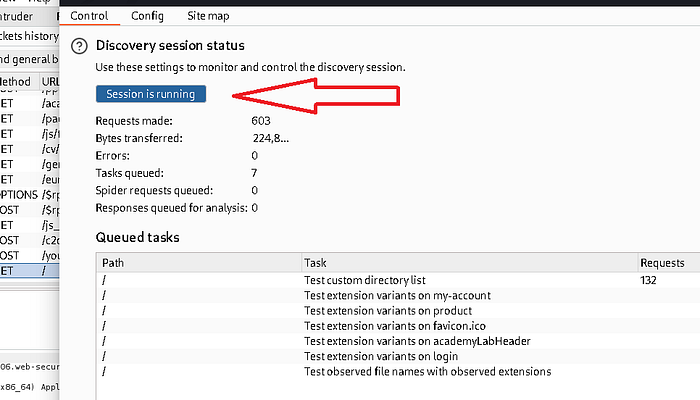
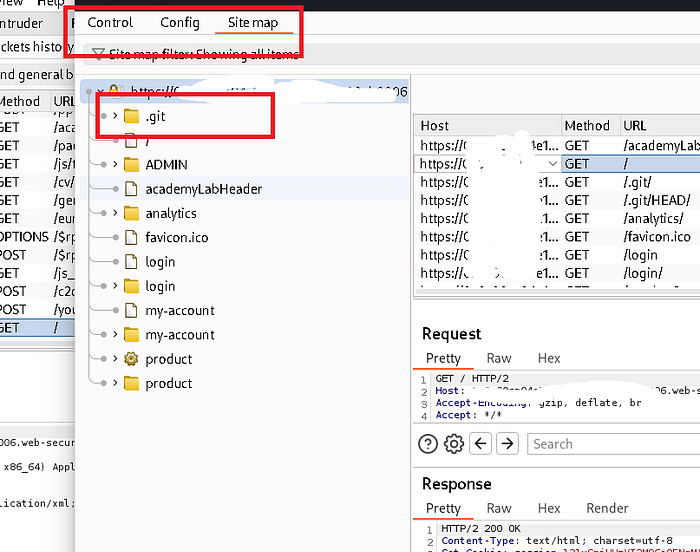
During testing, we identify a publicly accessible Git directory (/.git) where the server allows access to this directory, thus revealing repository metadata.

We will now download this ./git file because we already know that
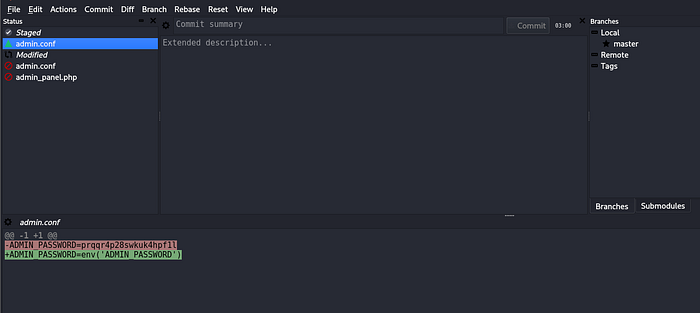
By accessing an open Git directory, it is possible to retrieve repository data and reconstruct the project's source code locally. Attackers can analyze the repository to view the commit history. This allows them to view previous versions of files and identify sensitive information that was moved in subsequent commits.


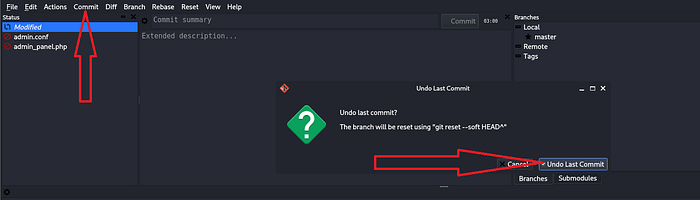
Got password
This lab highlights the security risks of exposing version control systems on production servers. Even if developers remove sensitive information from the current version of the code, it may still exist in the repository history. Proper server configuration and secure development practices are essential to prevent this type of information disclosure vulnerability.