If you think scams are about suspicious links, you need to read this. The most dangerous emails I've seen don't look dangerous at all.
They don't threaten. They don't rush. They don't ask for your password.
They start with something far more powerful …. a conversation.
The Email That Doesn't Look Like a Scam
Recently, I received the following email.
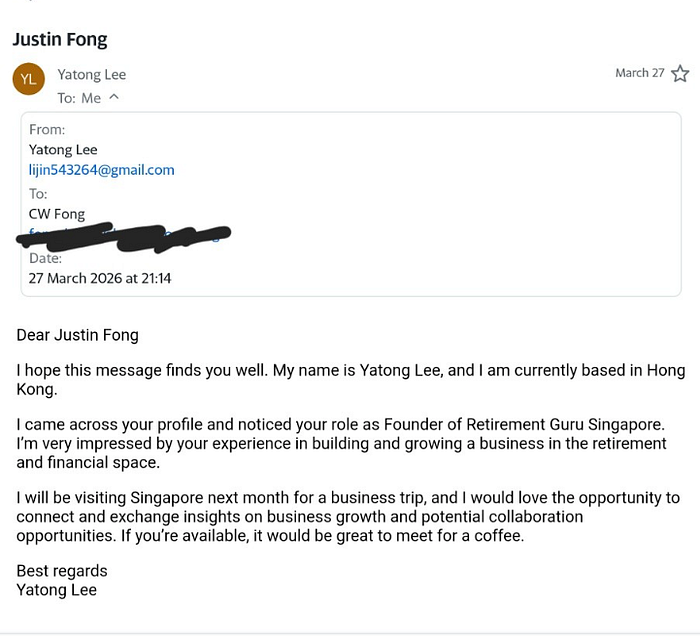
Polite. Professional. Well-written.
Someone reaching out for a coffee meeting while visiting Singapore. Complimenting my work. Suggesting a possible collaboration.
On the surface, nothing was wrong.
And that's exactly why it caught my attention. Because in today's environment, the absence of obvious red flags doesn't mean the absence of risk. So instead of reacting emotionally, I did what I've trained others to do.
I assessed it.
A Practical Phishing Risk Assessment (MoPS Framework)
Over the years, I've developed a methodology to understand why people click, respond, or engage with phishing emails. Based on scientific research, the Model of Phishing Susceptibility explains the behaviour based on the following three dimensions:
Personality + Emotion + Situation → Behaviour
This is important framework is important, as unlike current anti-phishing measures, the framework shifts the focus away from the email and back to the human because this is where the real vulnerability lies.
Overall Verdict
Probability of scam: 70%
Not clearly malicious. But not clean either.
This email sits in what I call the "proceed with extreme caution" zone — the zone that gets most people get into trouble. Not because they are careless. But because they are reasonable.
The Subtle Red Flags People Miss
When people think of scams, they look for broken English, fake logos, or urgent threats. But modern scams don't rely on those anymore. They rely on plausibility. Here's what stood out.
1. Generic but Flattering Outreach
"Very impressed by your experience…"
It sounds good. It feels good.
But there was no specific reference to my work. No mention of my frameworks. No articles cited.
Just a broad compliment.
This is typical of mass outreach scripting. It's designed to trigger a positive emotional response because once that happens, critical thinking steps aside.
2. Weak Identity Signals
The email came from a Gmail account and the name didn't match the handle. Now, this doesn't automatically mean it's a scam, but it does mean something important:
There is no strong accountability trail.
Legitimate professionals leave digital footprints. Company domains. LinkedIn profiles. Consistent naming. When those signals are weak, the burden shifts to you to verify.
3. Vague Intent
"Exchange insights on business growth." "Explore potential collaboration opportunities."
It sounds reasonable, but it is intentionally broad. This is the kind of language that is common in:
- Sales prospecting
- Investment pitches
- Recruitment funnels
- Early-stage scams
Why? Because vagueness allows flexibility. The conversation can evolve depending on how you respond.
4. The Coincidental Anchor
The sender mentioned being based in Hong Kong but visiting Singapore soon. This is subtle. But it's a classic tactic. It creates a sense of coincidental opportunity: "I'm already in your city anyway." This lowers resistance. It makes the request feel low effort. Natural. Even convenient. And that's precisely the point.
Why This Might Still Be Legitimate
To be fair, not everything about the email was suspicious. This is where nuance matters.
1. No Urgency
There was no pressure. No "act now" language.
This is not typical of traditional phishing (but typical of early stage scams).
2. No Immediate Ask
No links. No attachments. No request for sensitive information.
Just a coffee meeting. This aligns more with business development or networking.
3. Clean Language
The email was structured and well-written. This suggests either a real person or someone using AI tools very effectively. Today, that distinction is increasingly blurred.
What This Email Most Likely Is
If I had to rank the scenarios:
- Potential scam evolving later (70%)
- Sales or business development outreach (20%)
- Opportunistic networking (10%)
- Direct phishing attempt (0%)
And, this is the key point. The risk is not in the first email. The risk is in what comes next.
The Dangerous Shift in How Scams Work
Something I've noticed over the past few years is that scams no longer start with requests.
They start with relationships.
They build familiarity. They build trust. They create a context where the eventual ask feels reasonable.
By the time the request comes, it doesn't feel like a scam anymore. It feels like a continuation of a conversation.
Why Smart People Still Get Phished
This is something I emphasize in my work.
Phishing is not an intelligence problem. It's a human problem.
Let's go back to MoPS.
Personality
Some people are naturally open. Curious. Helpful. Collaborative.
These are strengths. But in the wrong context, they become attack vectors.
Emotion
Flattery. Curiosity. Opportunity.
None of these are negative. But they shift your state to reduce skepticism.
Situation
In retirement, or even mid-career, this becomes more pronounced.
You have more time. More flexibility. Often more capital.
And often times, a desire to stay engaged. This combination makes you a very attractive target.
Behaviour
You reply. You meet. You engage.
Not because you are careless, but because everything felt reasonable.
A Simple Way to Protect Yourself
Over time, I've found that complex advice doesn't work because people don't remember it. So I reduce it into three steps:
Spot — Pause — Verify
Step 1: Spot
Notice the signals.
Not just the obvious ones. But the subtle ones.
- Generic praise
- Weak identity
- Vague intent
You don't need certainty. Just awareness.
Step 2: Pause
This is where most people fail.
They react too quickly. They reply immediately.
But time is your advantage as scammers rely on momentum. You disrupt it by slowing down.
Step 3: Verify
Before engaging further, ask for:
- LinkedIn profile
- Company details
- Specific purpose of outreach
Legitimate people will respond clearly. Scammers prefer ambiguity.
The Bigger Lesson
There is one pattern I keep seeing that worries me — we are still defending against yesterday's scams.
Looking for bad grammar. Suspicious links. Obvious urgency.
But today's threats are quieter. More patient. More human. And that means our defenses must evolve too.
A Thought Worth Holding On To
Retirement is about freedom. But freedom without awareness becomes vulnerability.
You don't need to be paranoid. But you do need to be intentional.
Because the question is no longer:
"Is this email a scam?"
It is:
"What behaviour is this email trying to trigger in me?"
Final Reflection
This email may turn out to be legitimate and lead to a meaningful conversation. Or it may (very likely) not.
But that's not the point. The point is:
You don't wait for certainty to protect yourself. You build habits that make you resilient.
That is the difference between reacting to scams and being prepared for them.
If this resonated with you, I've structured these ideas into a Udemy course titled"Why Smart People Still Get Phished". The course teaches a practical frameworks about how people make decisions under pressure, and why even experienced professionals get phished. Because the goal isn't awareness, it's behaviour.
If you found this useful, follow me on LinkedIn for more insights on phishing resilience.
I am curious. If you ever received an email like this, what will make you trust it or question it?
