Overview
A Server-Side Request Forgery (SSRF) vulnerability was discovered in Website Link Extractor v1.0 developed by SourceCodester. The application accepts a user-supplied URL and retrieves its content on the server side without proper validation or network restrictions.
This allows an attacker to make the server send requests to internal or restricted resources.
Affected Product
- Vendor: SourceCodester
- Product: Website Link Extractor
- Version: 1.0
- Language: PHP
Vulnerability Details
The application uses the PHP function:
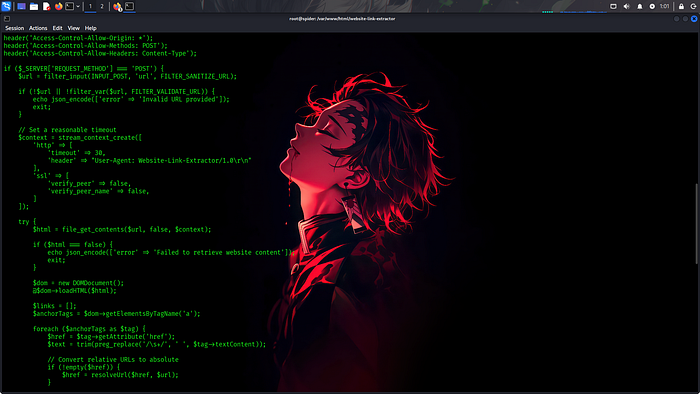
file_get_contents()
to fetch the content of the URL provided by the user.
However, there is:
- No proper input validation
- No filtering of internal IP ranges
- No restriction on localhost or internal network access
Because of this, attackers can force the server to access internal services.
Proof of Concept (PoC)
## Proof of Concept (PoC)
### Screenshot 1 — Internal SSRF Access
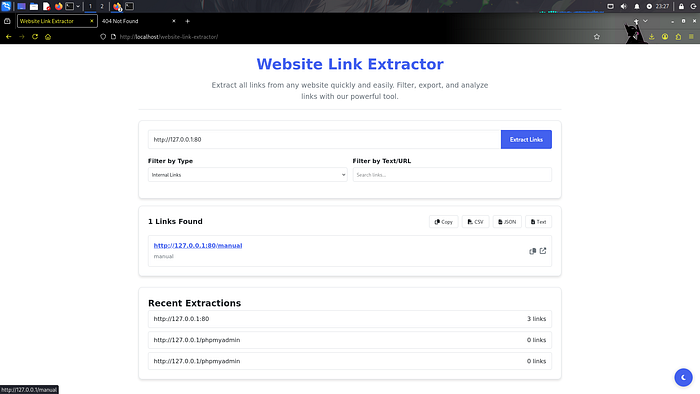
Steps: 1. Open the application: http://localhost/website-link-extractor/ 2. Enter: http://127.0.0.1:80 3. Click Extract Links
Result: The server fetches internal localhost content and extracts internal links.
— -
### Screenshot 2 — SSRF Bypass
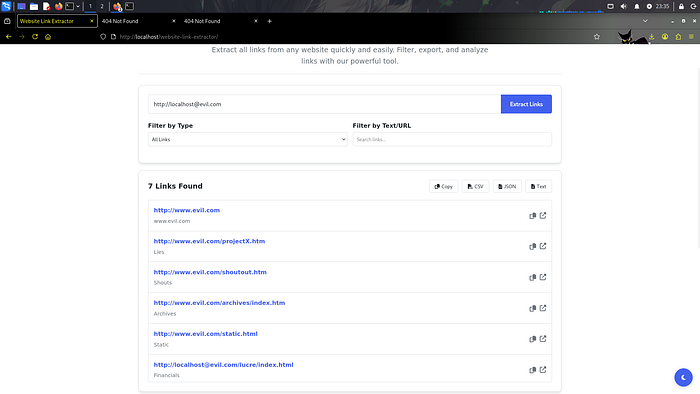
Payload used: http://127.0.0.1@evil.com
Result: The application bypasses URL validation and interacts with internal resources.
Impact
This vulnerability may allow an attacker to:
- Access internal network services
- Interact with localhost applications
- Perform internal port scanning
- Enumerate internal infrastructure
- Access cloud metadata endpoints (e.g., 169.254.169.254)
- Retrieve sensitive internal information
Severity: Medium to High (depending on server environment)
Root Cause
User input is directly passed to:
file_get_contents()
without:
- URL validation
- Internal IP blocking
- Protocol restrictions
- Network access control
Mitigation Recommendations
- Validate and sanitize user-supplied URLs
- Block internal IP ranges (127.0.0.0/8, 10.0.0.0/8, etc.)
- Disable access to localhost and private networks
- Use allowlist-based URL validation
- Restrict outgoing requests from the server
Disclosure Timeline
- Vulnerability discovered during security testing
- Public disclosure via this advisory
Author
Security Researcher: Hemant Raj Bhati Category: Web Application Security Type: Server-Side Request Forgery (SSRF)
