All organizations need to protect themselves against cyber threats because those threats develop continuously throughout modern times. Cybercriminals exploit weaknesses in systems, networks, and applications to steal data, disrupt operations, and damage reputations. Organizations implement proactive threat detection methods because they need to identify security weaknesses before attackers can exploit them, and VAPT proves to be an effective method for achieving this goal.
What is VAPT?
VAPT stands for Vulnerability Assessment and Penetration Testing. The term describes a security framework that organizations use to identify and assess their digital security weaknesses before taking steps to secure their systems.
Vulnerability Assessment (VA): A systematic process that scans an IT environment to discover known weaknesses. The system may contain actual security weaknesses, which include outdated software versions and missing patches, misconfigurations, and insecure settings. The security assessment process aims to generate a complete list of all security vulnerabilities that exist in the system.
Penetration Testing (PT): A simulated cyber attack that ethical security professionals, known as ethical hackers or testers, use to test system vulnerabilities under safe testing conditions. This test shows how a real attacker could breach systems, move laterally, or access sensitive data.
The two elements together deliver information about potential risks through VA assessment and provide a realistic demonstration of how those risks could be exploited through PT.
Why VAPT Matters?
Cybersecurity risk is no longer limited to large enterprises — small and medium businesses, government agencies, NGOs, and even individual developers are targeted. Organizations must implement VAPT because it provides essential security benefits, as shown below.
1. Proactive Risk Reduction
VAPT enables organizations to identify security weaknesses in their systems, which they can rectify before attackers launch their breaches.
2. Improved Regulatory Compliance
Organizations that operate in regulated industries must conduct security assessments because their sector requirements include ISO 27001, PCI DSS, HIPAA, and GDPR security testing. VAPT enables organizations to fulfill these testing obligations while showing their compliance efforts.
3. Reduced Costs and Damage
A data breach brings both financial losses and damage to an organization's reputation. The use of VAPT for early threat detection helps organizations cut down their expenses, which result from data loss and system unavailability, legal fines, and loss of client confidence.
4. Enhanced Security Posture
An organization strengthens its defense system through the identification of security flaws which it then mitigates. The organization improves its risk management capabilities through this process.

Key Components of VAPT
VAPT typically follows structured phases. The fundamental processes of the system proceed through essential steps which different providers and frameworks name using various terms.
1. Planning & Scoping
The testing process begins after the testing team establishes its testing parameters. The testing team needs to determine which systems and networks and applications will undergo testing.
The testing team must determine the testing boundaries of their work which includes deciding which testing aspects they will assess. The testing team needs to establish which testing activities need to be conducted at specific times.
The organization needs to establish security testing boundaries which define the areas that require examination. The testing process establishes business objectives and regulatory requirements which parties need to follow.
2. Information Gathering and Reconnaissance
The testers begin their work by gathering details about the target environment. The information they gather includes:
- IP addresses
- Domain information
- Running services
- Open ports
- Publicly exposed data
The attacker develops their organization picture through this stage.
3. Vulnerability Scanning
The automated tools Nessus and OpenVAS perform system scans that identify known security vulnerabilities. The tools assess system fingerprints against their extensive database of vulnerabilities to identify security problems.
4. Penetration Testing
Ethical testers use manual techniques and specialized tools to:
- Exploit identified vulnerabilities
- Attempt to bypass security controls
- Simulate real-world attack scenarios
The assessment shows both security flaws and their potential exploitation by attackers.
5. Analysis & Reporting
The testing process ends when the team creates a complete pentest report, which includes:
- The vulnerabilities that were found during the assessment
- The attacks that were conducted
- The risk assessment, which includes critical, high, medium, and low ratings
- The documentation includes proof and instructions for reproducing the findings
- The proposed solution to fix the problems
The report establishes a plan to resolve the identified problems.
6. Remediation & Re-Testing
The teams use patching, configuration changes, code fixes, and architectural redesigns to eliminate the security vulnerabilities. The team conducts additional testing after implementing fixes to confirm that all problems have been resolved.
Types of VAPT
VAPT shows different testing approaches, which researchers divide into three main categories based on testing scope and methodology. Types of Pen Testing in Cyber Security:
Black Box Testing: Testers have no prior knowledge of the infrastructure. This simulates an external attacker.
The testers in white box testing gain complete access to both the system details and architectural information. This simulates an insider threat or code-level review.
Grey Box Testing: Hackers who obtain partial access to a system pose an actual security threat that organizations face.
Additionally, VAPT can be scoped as:
- Network Testing
- Web Application Testing
- Mobile Application Testing
- Cloud Application Testing
- API Security Testing
- IoT Security Testing
Common Tools Used in VAPT
While a complete list varies based on scope and methodology, some widely used tools include:
- Nmap: network scanning
- Burp Suite: web application testing
- Metasploit: exploitation and payload delivery
- OWASP ZAP: web vulnerability scanner
- Nessus / OpenVAS: vulnerability scanning
- Wireshark: network traffic analysis
These tools help testers automate detection, simulate attacks, and perform deep analysis.
VAPT vs Other Security Assessments
It's useful to distinguish VAPT from other security activities:
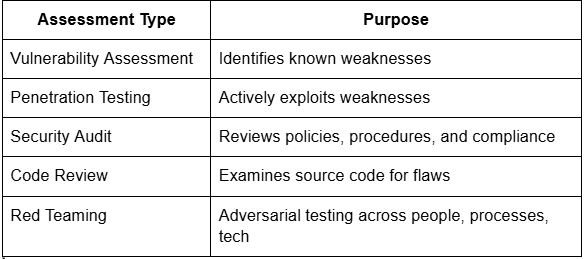
VAPT complements these efforts by focusing specifically on technical weaknesses and real-world exploitation.
Conclusion:
The VAPT method delivers organizations operational security information through its assessment of their digital security systems. The VAPT method uses automated threat detection methods to find system vulnerabilities, which it then tests through controlled exploitation to identify security weaknesses that would lead to major security breaches.
Organizations need to implement VAPT as their security testing method because cyber threats now exist throughout all sectors and geographical areas, which requires them to create transparent, repeatable testing processes.
Source: https://qualysec.com/what-is-vapt-testing-its-methodology-importance-for-business/