Venus Protocol, IoTeX, and SOF Token Exploits: $6.65M Lost to Design Flaws, Key Compromise, and Broken Token Logic
Venus was drained through a supply cap bypass combined with price manipulation, turning "donations" into exploitable collateral. IoTeX lost $4.4M after a compromised admin key enabled a malicious upgrade that bypassed all validation. SOF Token's flawed burn logic manipulated pool pricing mid-swap, enabling profitable arbitrage. Different vectors, same pattern: protocol design and control assumptions failed under adversarial conditions.
In Brief
- Venus Protocol lost $2M due to a price manipulation attack.
- IoTeX lost $4.4M after a compromised admin key enabled a malicious contract upgrade.
- SOF Token lost $249K after a flawed burn logic inflated token price during swaps.

Hacks Analysis
Venus Protocol | Amount Lost: $2M
On March 15th, the Venus Protocol exploit on the BSC resulted in a $2M loss. The root cause of the exploit was a supply cap bypass combined with price manipulation of the THE contract. The protocol allowed direct token transfers ("donations") to the vToken contract, which increased collateral value without enforcing the supply cap. The attacker gradually deposited 53.2M THE over 9 months (exceeding the 14.5M cap), and artificially inflated the exchange rate by 3.8x. This allowed the attacker to leave the protocol in $2M bad debt.


Exploited Contract (on BNB): 0xF4C8E32EaDEC4BFe97E0F595AdD0f4450a863a11
Transaction: 0x4f477e941c12bbf32a58dc12db7bb0cb4d31d41ff25b2457e6af3c15d7f5663f
IoTeX | Amount Lost: $4.4M
On February 21st, the IoTeX ioTube bridge exploit in the Ethereum mainnet resulted in a $4.4M loss. The root cause was a compromised validator admin key. The attacker gained ownership of the Validator contract and upgraded it to a malicious implementation. This new logic bypassed all signature verification and validation checks. The attacker then minted 410M CIOTX and gained control over bridge reserves. Using this access, they withdrew multiple assets from the TokenSafe contract.

Transaction: 0x1b5772b2a0e1f71327e227ed4ff3ef9fbdc63a47cc8a7fb8995aab41dc7d7c3d
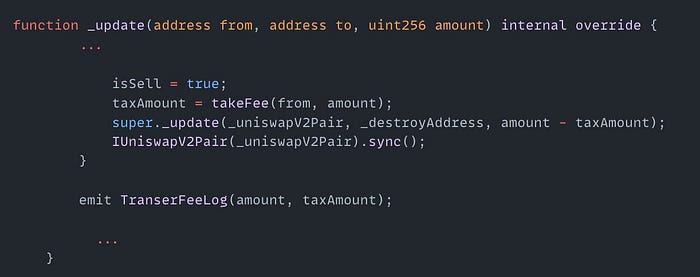
SOF Token | Amount Lost: $249K
On February 14th, the SOF Token exploit on the BSC resulted in a $249K loss. The root cause of the exploit was a flawed burn mechanism in the private _update() function. This function burned SOF tokens and called sync() before calculating the swap output. Because the pool synced before pricing, the SOF token price got artificially inflated. The attacker swapped SOF tokens, repaid the flash loads and made a profit.
Exploited Contract (on BNB): 0xaeb414d0a64dfca14fd41b28efc78f437008df42
Transaction: 0xcb5b22d86819b84ef176aee2d6b89f687e74d829560de1bcc63d53fcb2ac68f8
Olympix: Your Partner in Secure Smart Contracts
Olympix provides advanced Solidity analysis tools to help developers identify and fix vulnerabilities before they become critical exploits.
Get started today to fortify your smart contracts and proactively shield them from exploits in the evolving Web3 security landscape.
Connect with us on:
Twitter | LinkedIn | Discord | Medium | Instagram | Telegram | Newsletter
