The Economic Pattern We All Know
You've seen it at the gas pump. Crude oil prices spike → gasoline prices shoot up immediately. Crude prices drop → you wait weeks for relief at the pump. Economists call this "rockets and feathers" (asymmetric price transmission): prices rise like rockets but fall like feathers .
For decades, researchers documented this across 165 producer goods and 77 consumer markets. The data consistently shows that two out of three markets exhibit this asymmetry — not due to conspiracy, but due to market dynamics, consumer search behavior, and strategic firm interactions
The "Rockets and Feathers" economic theory using a relatable example for Security Officers (CISOs) deal with this exact same asymmetry every day, your Security Posture Crashes Faster Than It Recovers

The Rockets and Feathers of Cybersecurity: Why Your Security Posture Crashes Faster Than It Recovers
To understand why cybersecurity mirrors the "Rockets and Feathers" economic model, we have to look at the anatomy of a catastrophic breach. In late 2025, British automotive giant Jaguar Land Rover suffered an attack that cost the UK economy an estimated £1.9 billion.
Here is how their security posture experienced the exact asymmetry of rockets and feathers.

🚀 The Rocket: Why the Crash is Instantaneous
In economics, when costs rise, prices shoot up like a rocket. In cybersecurity, when a vulnerability is exploited, the business impact skyrockets in minutes.
For JLR, the "rocket" launched on August 31, 2025. Threat actors (reportedly a consortium of groups including "ShinyHunters" and "HELLCAT") didn't need to break down a massive digital vault. Reports indicate the breach was traced back to something incredibly simple: stolen Jira credentials harvested via Infostealer malware.
Because JLR operated highly connected "smart factories" where IT (Information Technology) and OT (Operational Technology) were deeply intertwined, the attackers were able to move laterally with terrifying speed.
The Rocket Effect:
- Instant Shutdown: Within hours of detecting the intrusion, JLR was forced to hit the ultimate panic button: shutting down internal IT networks globally to contain the blast radius.
- Immediate Financial Haemorrhage: The moment systems went dark, JLR began losing an estimated £50 million a week.
- The Blast Radius: The risk didn't just spike for JLR; it rocketed across their entire ecosystem. Because supply chains are heavily integrated, the instant JLR went offline, over 100,000 UK supply chain jobs were immediately put at risk.
The rocket phase proves one thing: Destruction operates at the speed of software. One compromised credential, one lateral move, and an entire global empire grounds to a halt.
🪶 The Feather: Why Recovery is a Slow Drift
In economics, when costs drop, prices fall slowly, drifting down like a feather. In cybersecurity, returning to a secure, operational baseline takes from weeks to months of excruciating, manual effort.
If shutting down the factories took hours, turning them back on should be just as fast, right? Absolutely not. This is the "feather" phase, and it is where businesses bleed the most capital.
JLR originally hoped to restart production in days. Instead, factories across the UK, Slovakia, Brazil, and India stood still for nearly four weeks, with full operations not normalizing until mid-November.
Why the Feather Falls So Slowly:
- The Connectivity Trap: JLR's "smart factories" were designed so that "everything is connected" to optimize efficiency. But in a cyberattack, high connectivity means high contamination. You cannot simply flip the power switch back on without knowing exactly where the hackers hid their backdoors.
- Forensic Friction: Every single server, endpoint, and piece of manufacturing equipment had to undergo forensic investigation. IT teams had to manually verify millions of lines of code.
- Physical Logistics: When JLR pulled the plug, there were over a thousand cars sitting on the assembly lines in various stages of build. Restarting meant manually inventorying what parts were needed for every single half-built vehicle before the automated lines could spin up again.
- Data Leakage: The attackers leaked gigabytes of sensitive data — including source code, internal debug logs, and employee details — onto Telegram. Remediating a breach isn't just about deleting malware; it involves managing PR, regulators, and securing exposed internal logic that could be used for future attacks.
Risk is asymmetric. An attacker only has to be right once, exploiting a single stolen credential to launch the rocket and bring a multi-billion dollar enterprise to its knees. But defenders have to be right millions of times during the recovery phase, untangling highly complex, interconnected systems inch by inch.
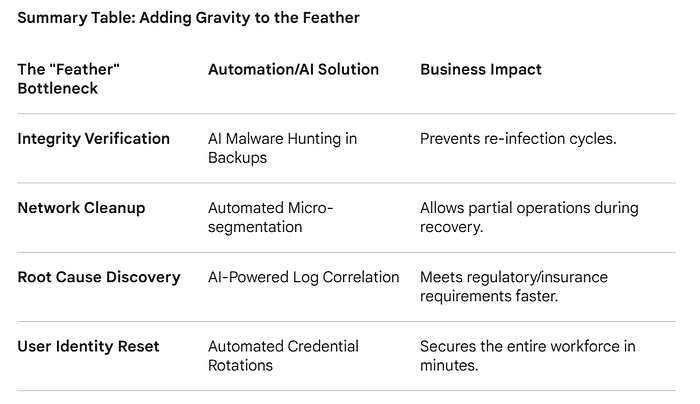
Reducing the "Feather Effect"
To reduce the "Feather Effect"; that agonizingly slow drift back to normalcy; you have to replace manual, human-speed investigation with machine-speed response. In a recovery scenario like the Jaguar Land Rover (JLR) event, the delay isn't usually the lack of backups; it's the lack of trust in the environment.
Automation and AI act as "gravity," pulling that feather down faster by verifying integrity at scale.
1. AI-Driven "Clean Room" Orchestration
The biggest delay in recovery is the fear of "re-infection." If you restore a backup that contains the same dormant malware or "backdoor" used in the initial attack, you launch the Rocket all over again.
- The Manual Way (The Feather): Security teams manually scan backup images one by one using traditional antivirus before pushing them to production.
- The AI Way: Using AI-powered automated recovery orchestration, you spin up backups in an isolated "Clean Room" (a sandboxed cloud environment). An AI model analyzes behavioral patterns within that sandbox ; looking for suspicious "heartbeats," unauthorized encryption attempts, or hidden scripts; at a speed no human could match.
- The Result: You confirm the backup is "clean" in minutes, not days.
2. Automated Micro-Segmentation (Blast Radius Control)
As we saw with JLR, the "Rocket" was fueled by the fact that the factory floor was connected to the office network. The recovery was a "Feather" because they had to manually untangle these connections.
- The Manual Way: Network admins manually write firewall rules and VLAN tags to separate compromised systems from healthy ones.
- The AI Way: AI-based Network Detection and Response (NDR). During a recovery, AI can automatically map every "conversation" between devices. If it sees a manufacturing robot trying to talk to a suspicious external IP, it uses Automated Micro-segmentation to "quarantine" that specific device instantly without killing the whole factory line.
- The Result: You can bring 90% of the plant online while the 10% under investigation remains isolated.
3. Synthetic Forensics & Automated RCA
Root Cause Analysis (RCA) is usually what keeps the "Feather" in the air. Regulators and insurers won't let you resume full operations until you can answer: "How did they get in?"
- The Manual Way: Forensic experts spend weeks pouring over millions of lines of log files from Jira, Active Directory, and VPNs.
- The AI Way: Generative AI for Security Operations (SecOps). You feed the disparate logs into a Large Language Model (LLM) trained on cybersecurity telemetry. The AI can perform "log correlation" instantly, identifying that the stolen Jira credential was the entry point and tracing every lateral move the attacker made.
- The Result: You provide the "Proof of Root Cause" to stakeholders in hours, allowing for a faster green light to resume business.
Conclusion: Don't Let the Feather Decide Your Fate

The Jaguar Land Rover crisis of 2025 serves as a stark reminder: in the digital age, gravity is not symmetrical. We live in a world where a single stolen credential; a tiny spark; can launch a Rocket that incinerates years of reputation and billions in revenue in a matter of hours. But as the smoke clears, most organizations find themselves trapped in the Feather phase — a slow, drifting, and agonizingly expensive descent back to "business as usual."
The JLR story teaches us that the true cost of a breach isn't just the impact of the Rocket; it's the duration of the Feather. Every day spent manually scrubbing servers, every hour lost to forensic uncertainty, and every week the assembly line sits silent is a choice we make by relying on legacy recovery manual processes.
To survive the next "Rocket," we must stop treating recovery as a manual craft and start treating it as an automated science. By integrating AI-driven "Clean Room" orchestration and Automated Micro-segmentation, we can add lead weights to our recovery efforts.
The goal of a modern CISO is simple: You may not be able to stop every rocket from launching, but you can damn sure make sure your feathers fall with the speed of a stone.
