It was 2:00 AM, and my terminal was a blur of scrolling green text. I was deep into a private bug bounty program for a massive corporate real estate company, searching for the things that developers thought they had deleted years ago.
I wasn't actively attacking the server. Instead, I was running gau (GetAllUrls), passively scraping the Wayback Machine and public internet archivers for forgotten endpoints. Most of it was garbage—broken images, dead links, obsolete CSS files.
I blinked, leaning closer to the monitor. Sometime in the past, an operations manager had logged into an internal Chilean compliance portal. Whoever built that portal had made a fatal error: they configured the login mechanism to pass the user's email and password directly into the URL bar as a GET parameter.
When that manager clicked a link to the main application, their browser helpfully sent the URL—password included—as the "referrer." A web crawler had quietly swept by, indexed that referrer, and preserved it in the digital archives for anyone to find.
My heart rate ticked up. There's no way this still works, I thought. This is an ancient log.
The screen flashed white, and a complex dashboard loaded.
"Welcome, Chief of Operations."
I carefully navigated the dashboard, my eyes scanning the modules. I clicked on a tab labeled Gestión Externa (External Management). The page loaded, and a chill went down my spine.
Because this account belonged to the Head of Operations, it had unrestricted access to the company's entire third-party supply chain. Row after row of data flooded the screen: the full names, exact job titles, and — most critically — the Rol Único Tributario (RUT), the highly sensitive Chilean National Identification Numbers, for thousands of external contractors.
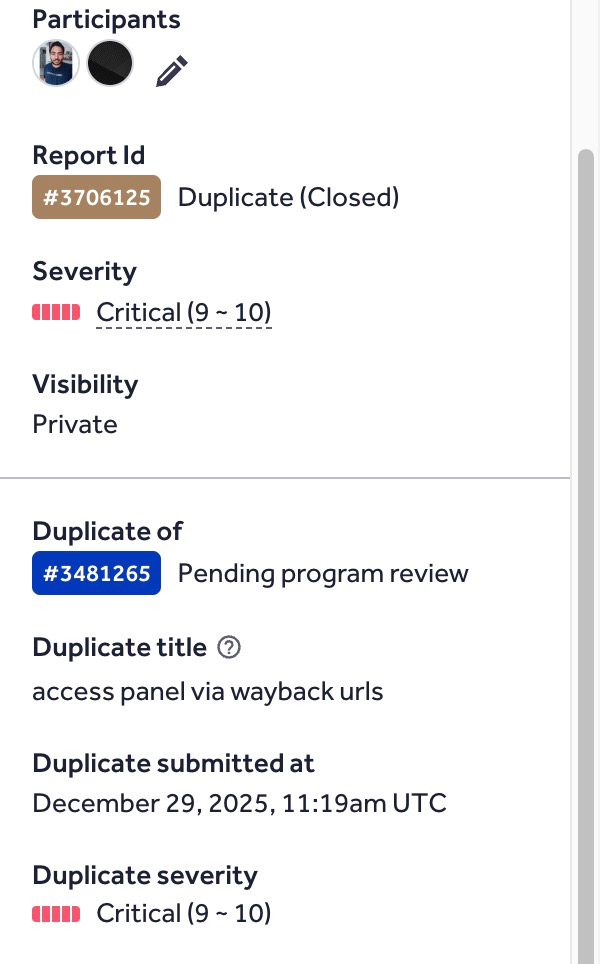
I immediately logged out, documented my findings, redacted the PII, and submitted the report to HackerOne. The adrenaline of finding a Critical bug makes it impossible to sleep, so I sat back and waited for the triage team to respond.
A few hours later, my phone buzzed. An update on my report. I opened the email, expecting the sweet validation of a massive bounty.
Status: Closed - Duplicate.
Another hacker had found the ghost in the machine. I slumped back in my chair, the adrenaline fading into a bittersweet sigh. It's the most painful feeling in bug bounty, but as I closed my laptop for the night, I couldn't help but smile.
I hadn't gotten the bounty, but I had found a Critical vulnerability in a hardened corporate network. The methodology was flawless. The impact was real.