Information Disclosure is a security vulnerability where a system or application unintentionally exposes sensitive or internal information to users. This means that information is visible that is not intended for normal users to see.
Hey me dear reader…..
In this lab from the PortSwigger Web Security Academy, the goal is to identify and exploit an "information disclosure vulnerability" caused by verbose error messages. This lab's verbose error messages reveal that it is using a vulnerable version of a third-party framework.
Applications sometimes return detailed internal errors when something goes wrong. While these messages help developers during debugging, they can also leak sensitive information , Attackers can use this information to craft further attacks. such as:
* Internal file paths * Technology stack * Database structure * Server configuration
Information disclosure occurs when an application unintentionally reveals sensitive data to users who should not have access to it.Error messages are one of the most common places where this happens.
Common sources include:
* Debug messages * Stack traces * Misconfigured APIs * Source maps * Server headers
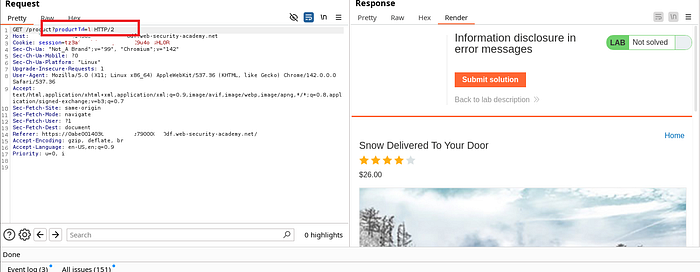
When we look inside a product and capture it with burp suite, the product id is visible. But when this product id is replaced with normal text or something else, it shows us some internal information with Apache version.
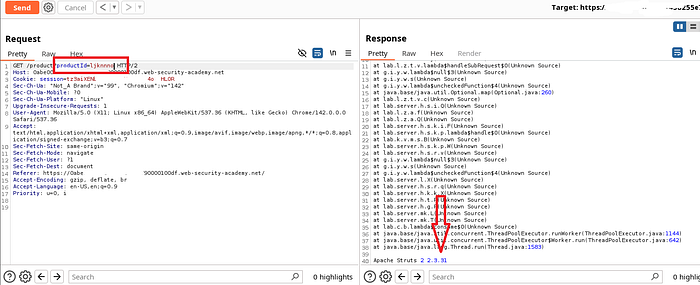
If someone knows the Apache server version, then the system is not directly hacked. But it becomes reconnaissance information for the attackers, meaning they get important information about the target.
Known Vulnerability_CVE (Apache version is vulnerable, attacker can find exploit). Exploit Research (risk increases if outdated). Attack Strategy Planning (it makes attack surface mapping easier). Automated Scanner Targeting (Technology Fingerprinting). Technology Fingerprinting (it makes future attack planning easier).
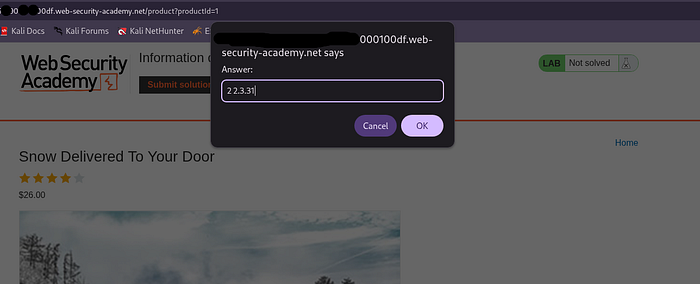
The purpose of this lab is to trigger an error message that reveals internal information about the application. Which we found very easily in this lab and it was resolved.