
The event involved a possible Insecure Direct Object Reference (IDOR) attack, where the attacker tried to manipulate the user input and gain unauthorised access to resources.
Collect Data
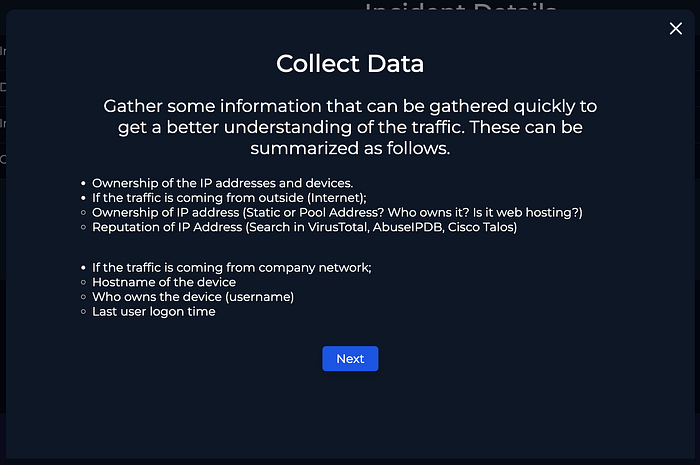
Firstly, we will gather as much as information and then proceed with the playbook. Based on the information given by the SOC system we can find the following details, which will be helpful for further investigation.

We will go through the IP address and check whether the source IP address is legitimate or malicious. Firstly we will check the IP in Virus total.
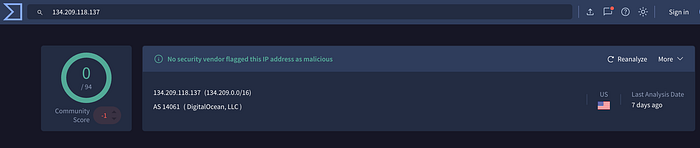
Virustotal shows the source IP : 134.209.118.137 is legitimate but we can't blindly go with this as we have to cross verify the data. Now we will check the same IP in AbuseIPDB .

AbuseIPDB shows the IP is malicious and it has multiple reports of SSH-Attack and also the IP belongs to an company named Digital Ocean in USA. So we are now sure that the source is malicious.

Further we have to verify what is the attack type. We can identify the attack type by inspecting the web traffic between the server and the attacker's IP address from Log Management.
Search using the attacker's IP (134.209.118.137) in the search box and we can see that there are 5 logs between the server (Webserver1005) and the attacker's IP. You can alternatively search with the Server's IP address (172.16.17.15)
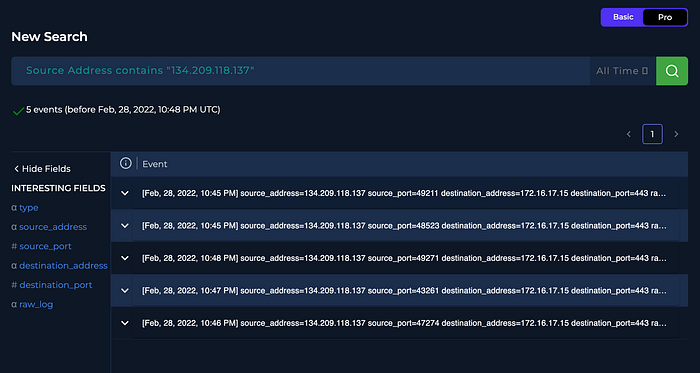
After inspecting the URL from the above logs we can come to conclusion that the attacker tried to modify the user_id parameter in the requested URL. So the attack type is IDOR.

With the different HTTP response size it is evident that data has returned from the server. The attacker tried to obtain different user details and he was successful.
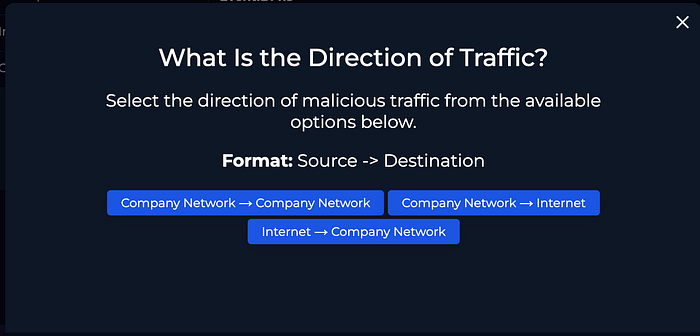
The direction of traffic is Internet → Company Network as its not within the company network.
After investigation it is clear that this was a true positive IDOR attack on the host Webserver1005. The host has been contained and it not an planned test as there is no email regarding this in the email security.
Document the artefacts from your investigation and write an analyst report based on your understanding.
To conclude, the attack was successful and it has been escalated to Tier 2 for further investigation.

