The application allowed users to test their typing speed and accuracy. While it looked like a simple performance-based platform, deeper inspection revealed a critical vulnerability: JWT Forging.
Challenge Overview
The application allowed users to:
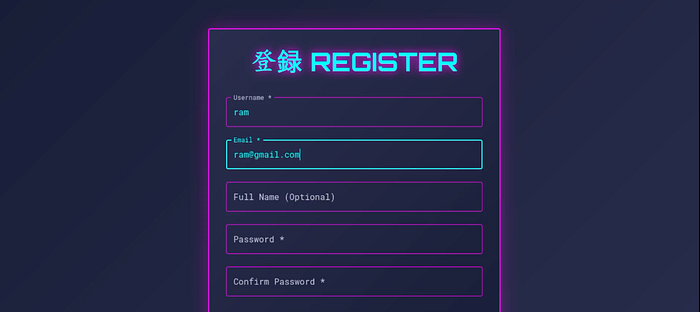
- Register and log in
- Take typing tests
- View typing results
- Track time and accuracy
The objective was to find a vulnerability that could expose the hidden flag.
Initial Testing — Manipulating Typing Results
I began by analyzing the typing result submission request.
Using:
- Caido
I intercepted the request that submitted:
- Typing time
- Accuracy
- Score
I modified the time parameter to a lower value to artificially boost the result.
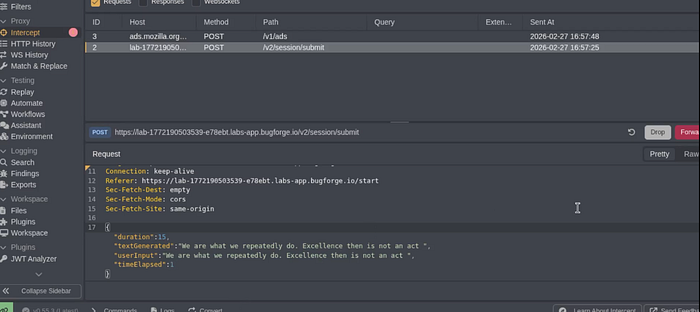
The manipulation worked — the server accepted the modified result.
However, this appeared to be just a minor business logic flaw and did not reveal the flag.
So I continued deeper.
Investigating Authentication — JWT Analysis
While inspecting requests, I noticed the application used JSON Web Tokens (JWT) for authentication.
This immediately opened a new attack surface.
A JWT typically consists of:
- Header
- Payload
- Signature
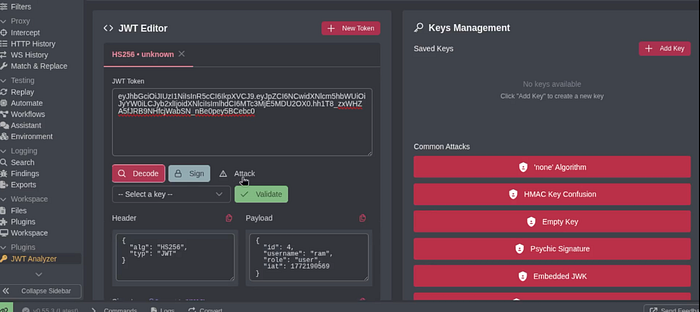
I decoded the token and inspected its contents.
The payload contained fields like:
user_idrole
That was suspicious.
If the server improperly validated the signature, it might allow token tampering.
Exploitation — JWT None Algorithm Attack
I attempted a classic JWT attack:
Step 1: Modify the Token Header
Changed the algorithm in the header to:
"alg": "none"Step 2: Modify the Payload
I then changed:
user_id→ 1role→ admin
Step 3: Remove Signature
Since the algorithm was set to none, the token no longer required a valid signature.
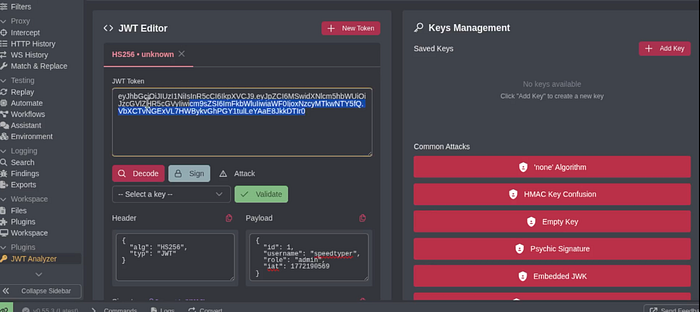
I generated the modified token and replaced the original JWT in the request.
Discovering Hidden Endpoints
To explore further, I used an endpoint extraction technique to enumerate available API routes.
While analyzing endpoints, I discovered:
/v1/admin/flag
This strongly indicated an admin-only endpoint.
Final Exploit
After replacing my JWT with the forged admin token, I accessed:
/v1/admin/flagThe server returned the flag.
This confirmed that:
- The server accepted unsigned tokens
- No proper signature validation was enforced
- Authorization was based solely on token claims
Why This Worked
The vulnerability existed because:
- The server trusted JWT claims without verifying signatures
- The
nonealgorithm was accepted - Role-based access control relied entirely on token payload
- No server-side validation was performed
Proper JWT implementation should:
- Reject
alg: none - Enforce strong signature validation
- Never rely solely on client-controlled claims
Security Lessons Learned
This challenge highlights critical authentication principles:
- Always verify JWT signatures
- Disable the
nonealgorithm - Enforce strict role validation server-side
- Avoid trusting client-side tokens blindly
- Protect admin endpoints with additional authorization checks
JWT misconfiguration can lead to full privilege escalation.
Final Thoughts
This Bugforge challenge reinforced how dangerous authentication flaws can be.
Initially, I found a minor logic issue in typing result manipulation. But deeper inspection of authentication mechanisms revealed a much more critical vulnerability.
JWT vulnerabilities are extremely impactful because they can allow:
- Privilege escalation
- Admin access
- Complete authentication bypass
Another reminder that understanding how authentication tokens work is essential in web security testing.