In the world of cybersecurity, sometimes the most impactful discoveries come from the simplest entry points. Recently, while exploring the security posture of various e-commerce platforms, I identified a significant Cross-Site Scripting (XSS) vulnerability on online-moebel-kaufen.de, a prominent German furniture retailer.
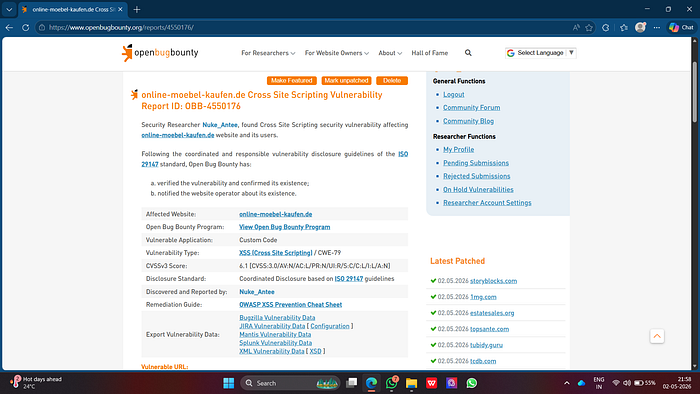
This vulnerability (identified as OBB-4550176) highlights the critical importance of sanitizing user input, even in common features like search bars.
The Discovery: Hunting for XSS
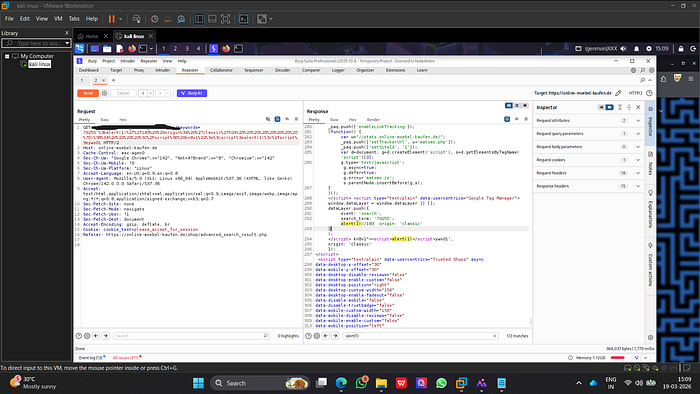
While analyzing the target website, I focused on how it handled user-supplied data in its URL parameters. I discovered that a specific parameter used for search queries was not properly sanitizing input before rendering it back to the page.
Using Burp Suite Professional, I intercepted a request and injected a simple JavaScript payload into the search parameter. The payload was designed to trigger a standard alert box, a classic "Proof of Concept" (PoC) for XSS.
Proof of Concept (PoC)
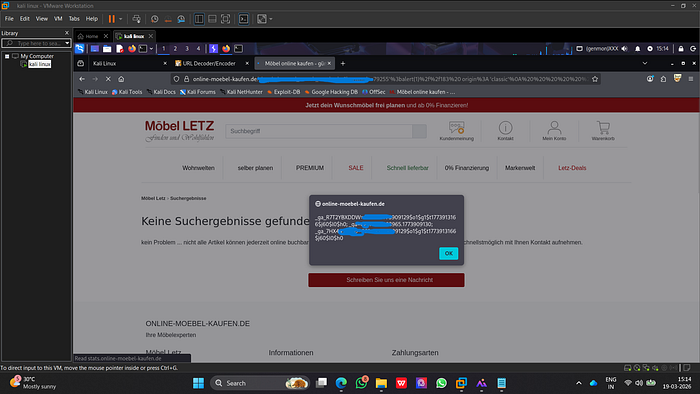
The injection was successful. By crafting a malicious URL, I was able to:
- Trigger a JavaScript Alert: A simple pop-up with the value
1appeared, confirming that the script was executed by the browser. - Access Sensitive Data: To demonstrate the potential impact, I escalated the PoC to show that an attacker could potentially access session information or other sensitive data stored in the browser's context.
The vulnerability was classified as a Reflected XSS (CWE-79) with a CVSSv3 score of 6.1 (Medium). This score reflects that while the attack requires some level of user interaction (clicking a link), the impact on confidentiality and integrity can be significant.
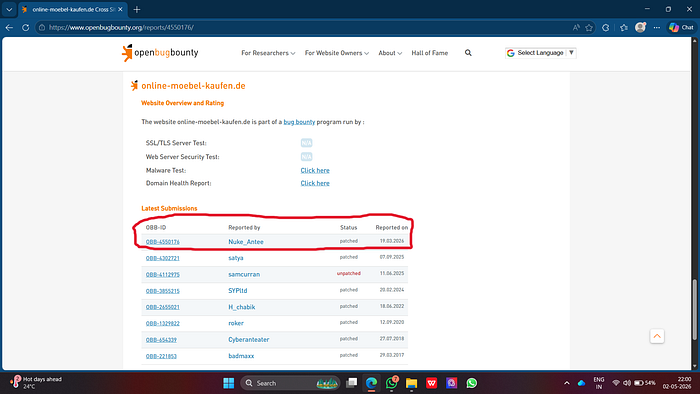
Responsible Disclosure Timeline
Following ethical guidelines and the ISO 29147 standard for coordinated disclosure, I reported the finding through Open Bug Bounty.
- March 19, 2026: Vulnerability discovered and reported.
- March 19, 2026: Open Bug Bounty verified the vulnerability and notified the website operator.
- April 21, 2026: The website operator successfully patched the vulnerability.
Why This Matters
Cross-Site Scripting remains one of the most prevalent web vulnerabilities. If left unpatched, an attacker could use this flaw to:
- Steal session cookies and hijack user accounts.
- Redirect users to malicious phishing websites.
- Deface the website or inject malicious content.
Conclusion and Lessons Learned
The resolution of OBB-4550176 is a success story for coordinated disclosure. The team at online-moebel-kaufen.de acted professionally and resolved the issue within a reasonable timeframe once notified.
For developers, the lesson is clear: Never trust user input. Always use robust sanitization libraries and follow the OWASP XSS Prevention Cheat Sheet to ensure that data rendered in the browser is safe.
Disclaimer: This research was conducted for educational purposes and reported responsibly. I do not encourage or condone unauthorized testing against any systems.