Cybersecurity failures rarely begin with a dramatic breach. Most of the time, they start with something small: an exposed login page, an outdated plugin, a weak API, a misconfigured server, or a forgotten admin panel. Attackers just need one opening .That is exactly why VAPT matters.
What Is VAPT?
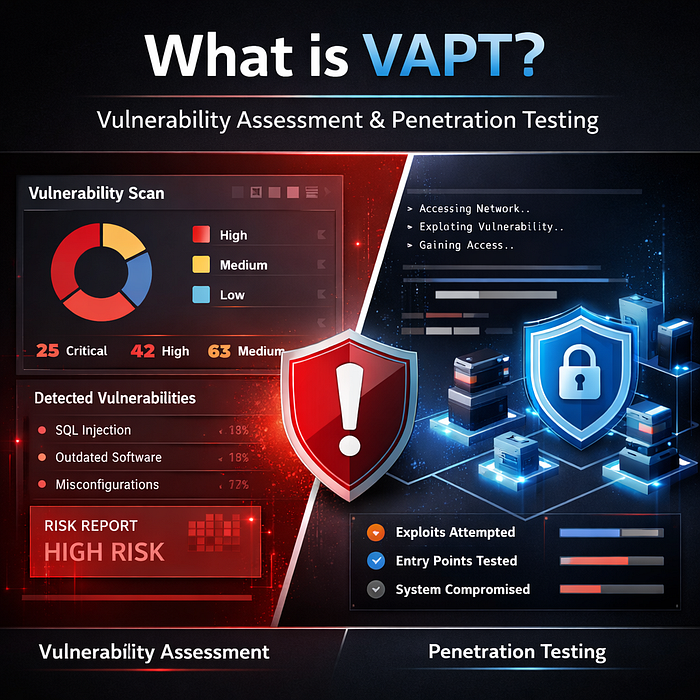
VAPT stands for Vulnerability Assessment and Penetration Testing.
A vulnerability assessment is focused on discovering security weaknesses. It identifies known issues such as outdated software, exposed services, missing patches, insecure configurations, weak encryption, and common coding flaws. Think of it as the process of finding where the cracks are.
A penetration test goes further. It attempts to validate whether those weaknesses can actually be exploited, how far an attacker could go, and what the business impact would be. That is where theory becomes reality. OWASP's testing guidance and CISA's penetration testing material both reflect this more practical, exploitation-oriented approach.
In simple terms, vulnerability assessment tells you what is wrong. Penetration testing tells you what can actually be abused.
Why VAPT Matters More Than Ever
Too many companies still treat security as a checklist. They buy tools, enable alerts, add a firewall, and assume that is enough. It is not.
Modern attacks do not only target large enterprises. Startups, SaaS companies, hospitals, manufacturers, fintech firms, e-commerce businesses, and mid-sized companies are all in scope. Attackers often prefer easier targets with weaker defenses, poor monitoring, or rushed deployments.
The problem is not always a highly sophisticated zero-day. In many cases, breaches happen because of known and preventable issues: insecure authentication, broken access controls, exposed cloud storage, weak passwords, vulnerable third-party components, or poor input validation. Security testing frameworks from OWASP and NIST exist precisely because these weaknesses are common and repeatedly exploited.
What Does VAPT Actually Check?
A serious VAPT exercise typically looks at the following areas, depending on scope:
1. Web Application Security
This includes authentication, session management, authorization flaws, injection vulnerabilities, insecure file uploads, business logic weaknesses, misconfigurations, and exposed sensitive data. OWASP's Web Security Testing Guide is one of the most widely used references for structured web application testing.
2. API Security
APIs are often overlooked, even though they expose direct business logic and data flows. Testing usually covers broken object level authorization, weak token handling, rate limiting issues, excessive data exposure, insecure endpoints, and improper input validation.
3. Network and Infrastructure Security
This covers open ports, exposed services, insecure protocols, weak segmentation, outdated systems, configuration errors, and opportunities for internal or external exploitation.
4. Cloud Security Testing
Many businesses now operate in AWS, Azure, or GCP, but deploy with speed and hope for the best. VAPT in cloud environments can reveal misconfigured storage, over-permissive IAM roles, exposed workloads, poor network restrictions, and weak secrets management.
5. Mobile Application Security
Mobile apps often carry authentication tokens, user data, and API interactions that can be abused if not secured properly. Testing typically examines insecure storage, weak transport protection, reverse engineering exposure, and broken backend trust.
6. Validation of Real-World Impact
This is where penetration testing becomes useful. It shows whether a vulnerability is merely present or whether it can be chained into account takeover, data exposure, privilege escalation, or remote compromise.
That last point is critical. Businesses do not need more raw findings. They need clarity.
Why Your Business Needs VAPT Right Now
VAPT is no longer optional for businesses that rely on digital systems. Companies are launching websites, APIs, cloud workloads, and customer-facing platforms faster than ever, and speed often leads to security gaps. At the same time, the attack surface keeps growing through mobile apps, third-party integrations, admin portals, cloud storage, and remote access systems.
Who Should Get VAPT Done?
In summary: almost every company that uses digital infrastructure. However, VAPT is especially crucial for: • Financial institutions, such as banks, NBFCs, and fintech companies • Healthcare providers, such as hospitals, clinics, and medical technology • E-commerce businesses that store customer or payment data • SaaS companies: cloud-based platforms that handle user data • Governmental organizations and the public sector • As businesses raise money, investors are asking for additional proof of their security posture. • Businesses with dispersed or remote teams
You require VAPT if your company uses a web application or API to provide services, saves any kind of sensitive data, or takes online payments.
Final Thoughts
VAPT is more than just a security option.It is a practical way to identify real weaknesses before they turn into serious business problems. Whether you are running a startup, a growing company, or an established enterprise, regular security testing helps you reduce risk, strengthen trust, and stay prepared for both threats and compliance demands.
CTA
If your business has websites, applications, APIs, cloud systems, or sensitive data, this is the right time to test them properly.
Schedule a VAPT scoping call with digiALERT and get a clear view of your security gaps before attackers find them first — Schedule NOW