I'm a cybersecurity student, and when I first heard about Metasploit, in my college first year, it seemed very fresh and something exciting with the background that keeps the inner kid excited to see something new every day, and the information that was told by my professor who told us that with this tool we could exploit or hack anything, sounds exciting right??
But what actually caught my interest in the tool was when our professor performed a practical, that is, when the magic happens, when you see someone typing some commands and gaining access to another's system, back then I did not know what a shell was; I was only mesmerised by the output we were shown and the process. It was then that I came to know the power and potential of the Metasploit Framework and decided to learn more, and eventually try it firsthand."
Talking a bit about the history of the Metasploit Framework, it was created by H.D Moore in 2003, firstly developed in the Perl programming language as a portable network tool, but was later rewritten in Ruby in 2007, and later acquired by Rapid7 in 2009, a security company that provides unified vulnerability management solutions. Metasploit, after being acquired by Rapid7, introduced a Pro version for enterprises, which was paid. The main difference between the free and the paid version remains that the Pro version offers enterprises a GUI (Graphical User Interface), which provides automation, whereas the free version offers a CLI (Command Line Interface).
The Metasploit Framework is widely used by attackers and defenders; the attackers use it to exploit or basically hack a system and cover their tracks, while the defenders use it to "think like an attacker", which helps them to find the weak points or vulnerabilities in a system and fix them before the attackers exploit them.
From being a portable network tool to being a tool that defined the standard of the industry, used by both attackers and defenders, I think that Metasploit has come a long way, and it follows a very detailed structure and architecture. The architecture is what makes Metasploit very efficient, interesting and trusted by security professionals.
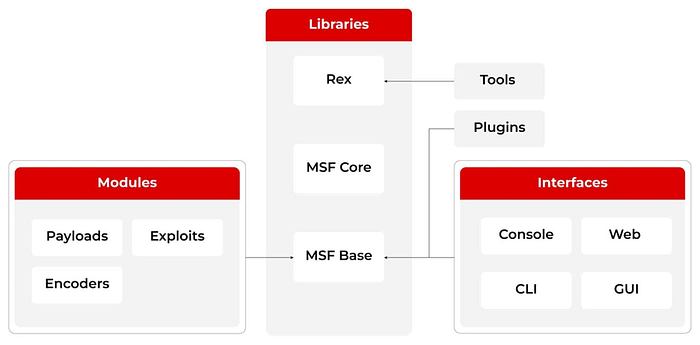
The above diagram explains the architecture of the Metasploit Framework and gives us some understanding of how things work internally and why it is widely used. As the diagram shows, the architecture of Metasploit is divided into 3 main categories, which are:
· Libraries
· Modules
· Interfaces
We'll be discussing about each category in a manner to clearly understand what makes the tool right now, starting with Libraries.
Libraries in the Metasploit Framework define the whole manner of working of the tool. In simple words, it handles how exploits or payloads work from the very starting configuration to gaining access to the target system and also in post-exploitation, the libraries are further divided into 3 parts, with each having its own working and importance. They are:
· REX
· Core
· Base
REX: Ruby Extension Library, or REX, is the lowermost layer and yet one of the most important libraries. Basically, REX handles communication (by handling the protocol like HTTP, SMB, FTP) and data manipulation (by providing encoding and decoding). REX acts as a foundational layer in the Metasploit architecture
Core: Core, also called as MSF-Core, is undoubtedly the heart of the Metasploit Framework as it manages all the internal operations and the interaction between the modules. The module and exploits that we see, or the execution of the modules, which happens so rapidly, are done by the Core library.
Base: Base, also known as MSF-Base, is the layer that we see. It handles the user interface, captures the user input and displays the result back from the Core library.
Now, talking about the part of the Metasploit Framework that makes it so versatile and scalable in the cybersecurity domain, Modules. The modules are some pre-developed scripts made to perform a specific task in Metasploit. Modules can be further differentiated into 5 categories, each used in a specific phase in the attack cycle, they are:
· Exploits
· Payloads
· Encoders/NOPs
· Auxiliary
· Post
Each of these categories has different scripts in them targeting various aspects of the attack lifecycle. Exploits are the scripts that target a particular vulnerability to gain access to a system; these are mainly used for gaining initial access into a system.
Payloads are pieces of code or specialised scripts that work only after the exploits gain access to the system. They are dependent on exploits for their successful working; these payloads contain some of the most lethal and severe code, which can take over the entire system.
Encoders, as the name suggests, work by encoding the payload by obfuscating it just to hide it and prevent the antivirus software from detecting it. NOPs (No-Operations Instructions) are instructions to payloads to stop for some time, or simply delay them for efficient execution of the payload.
Auxiliary are the scripts which do not exploit or harm anything; they simply operate by providing the information that can be used further by exploits into targeting the vulnerabilities. They are used in the initial reconnaissance phase, and they act as scouts for the attacker by providing information.
Post, as the name suggest help in post-exploitation activities to be performed. These scripts only come in use after successfully gaining a session on Metasploit and can be more lethal than exploitation if not less. They can be used to capture credentials, sensitive information, and escalate privileges
The last part of the architecture, The Interface layer, is the layer visible to us, and we use it to perform actions. Metasploit provides different types of interfaces for different usage, and to be usable for everyone, it provides 3 interfaces:
· Metasploit-CLI
· Armitage
· Metasploit Pro
Metasploit-CLI is the most widely used interface which is commonly available with Metasploit Framework free version, it is a command-line interface providing all the necessary tools and plugins, the Metasploit-CLI interface is being accessed by typing 'msfconsole', now as the name gives us some idea that it is a console by which we can execute commands and have our desired outputs, this is the interface that we'll be using in the future aspects of the blog to understand the practical concepts of the Metasploit Framework.
Armitage is the GUI (Graphical User Interface) commonly used by beginners to have a feel of Metasploit and help understand hacking in a simplified manner, and realise the potential of Metasploit. It provides all the tasks that could've been done by using msfconsole, which comes with the CLI interface.
Metasploit Pro is the interface used by enterprises and security professionals with the Pro version of Metasploit, which provides automation and more tools for security professionals, including social engineering and reporting capabilities. It requires a valid license to set up the Pro version of Metasploit.
I think we have talked enough theory about Metasploit, but the beauty of Metasploit lies in its practical approach rather than the theory, and I think we all can agree on it, so maybe let's have a feel of what Metasploit is all about, because it is as important as understanding how it works.
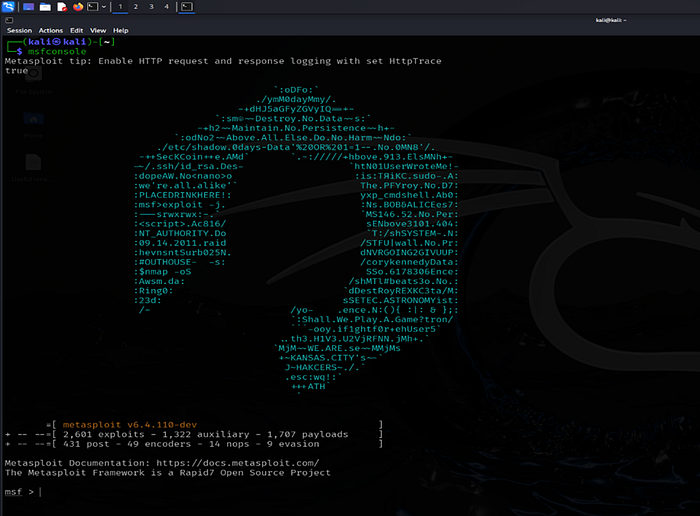
This is what Metasploit-CLI looks like when on the terminal we type 'msfconsole', and the background still excites the kid inside me, msfconsole as explained earlier is the interface by which the user inputs are captured and interpreted by the Base library and further transmits it to the Core library where the inputs get processed and the results are sent back, where they are visible to the user, which is on the screen in the image.
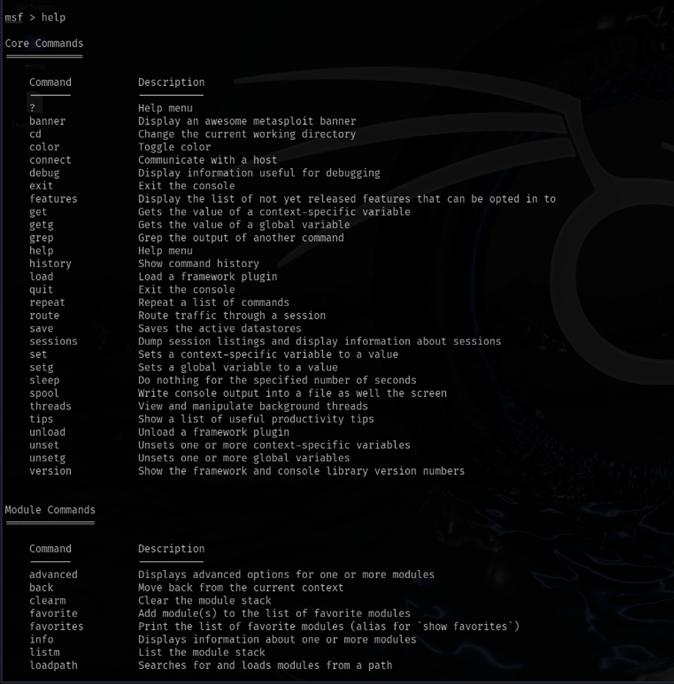
The 'help' command shows all the processes and commands that we can execute through the Metasploit Framework, making it efficient for beginners. This command works like it is the manual or guide of the tool, and it is good for beginners who want or like to perform practical tasks, but can't decide how or have the fear of breaking their own system or others.
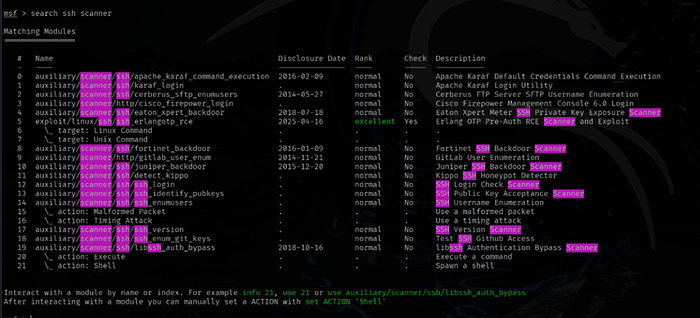
The 'search' command searches the Metasploit database for the user-inputted modules and displays the modules that perform the desired result. The search command uses the database of the Metasploit Framework to display the modules stored, which works when we don't know the exact name of the module, but we can search it out to choose the best among the list as it also provides us with the rank of the module, giving us an idea that would the module be best suited for our purpose.
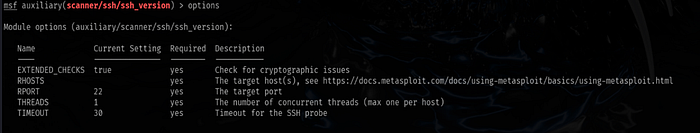
The 'options' command shows the options by which the attacker can configure the module and insert the required details to make the attack successful. In simple terms, it is more of a configuration command used mainly after selecting an exploit. It is used to configure the module selected to tune it into our specific needs, if any, and give the module the required data that it needs to reach the destination system and exploit the vulnerability, such as any module would ask for an IP address of the target system.
Note: The above practicals were conducted on Kali Linux in a safe sandbox environment (VirtualBox), which was isolated from the actual system. The practicals were performed on a vulnerable machine (Metasploitable 2). The setup of the whole lab will be available on a later blog.
To summarize, in this article we came to know about what was Metasploit Framework tool and its working and its architecture, I hope I was able to make It clear and understanding enough for everyone who read this, and I want to assure that this wasn't the only blog on Metasploit because what is it without the practical knowledge, so in the next part of the blog we'll be trying to demonstrate the practical application of Metasploit by scanning a real target. So, stay tuned!
Feel free to comment for your feedback, and if you're also learning security, drop a comment or connect with me on LinkedIn