While working on real-world applications and identifying vulnerabilities like XSS, IDOR, and Broken Access Control, I realized something important:
Finding bugs is just one part of security. Preventing them at scale — that's where DevSecOps comes in.
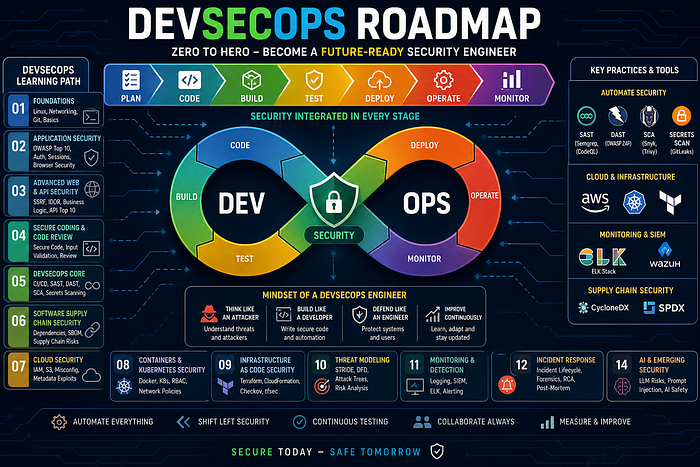
If you want to become a future-ready security engineer, you need to go beyond pentesting and learn how to integrate security into the entire software lifecycle.
This guide is your Zero → Hero DevSecOps roadmap.
🧠 What is DevSecOps (Simple Explanation)
DevSecOps = Development + Security + Operations
👉 Instead of adding security at the end, 👉 We build security into every stage of development
🧭 The Complete DevSecOps Journey

🟢 Phase 1 — Strong Foundations (Don't Skip This)
Before tools, you need core understanding:
- Linux basics (processes, permissions, networking)
- Networking (HTTP, DNS, TLS)
- Git (version control, branches, PRs)
👉 Goal: Understand how applications actually work
🟢 Phase 2 — Application Security Fundamentals
This is your base:
- OWASP Top 10 vulnerabilities
- Authentication & Authorization
- Session management
- Browser security (CORS, CSP, SameSite)
👉 Learn both:
- How to exploit
- How to fix
🟢 Phase 3 — Advanced Web & API Security
Move beyond basics:
- SSRF, Request Smuggling, Cache Poisoning
- Business logic flaws
- Race conditions
- API vulnerabilities (OWASP API Top 10)
👉 This is where real bug bounty skills come in
🟢 Phase 4 — Secure Coding & Code Review
Think like a developer:
- Input validation & output encoding
- Secure file handling
- Error handling
- Manual code review
👉 Start reading real code — this is a game changer
🟢 Phase 5 — DevSecOps Core (Most Important)
Now we shift to automation + pipelines
CI/CD Pipeline Security
Tools:
- Jenkins
- GitHub Actions
- GitLab CI
Security integration:
- SAST → Static code scanning (Semgrep, CodeQL)
- DAST → Runtime testing (OWASP ZAP)
- SCA → Dependency scanning (Snyk, Trivy)
- Secrets scanning → GitLeaks
👉 Goal: Automatically detect vulnerabilities during development
🟢 Phase 6 — Software Supply Chain Security
Modern attacks target dependencies.
Learn:
- Dependency confusion
- Malicious packages
- SBOM (Software Bill of Materials)
Tools:
- CycloneDX
- SPDX
🟢 Phase 7 — Cloud Security
Understand cloud environments:
- IAM misconfigurations
- S3 bucket exposure
- Metadata exploitation (SSRF → cloud creds)
Platforms:
- AWS basics (must know)
🟢 Phase 8 — Containers & Kubernetes Security
Modern apps run in containers.
Learn:
- Docker security
- Image vulnerabilities
- Container escape
- Kubernetes:
- RBAC
- Network policies
- Secrets
🟢 Phase 9 — Infrastructure as Code (IaC) Security
Infrastructure is now code.
Learn:
- Terraform security
- Misconfiguration risks
- Tools:
- Checkov
- tfsec
🟢 Phase 10 — Threat Modeling (Think Like an Architect)
Before building, think about threats:
- STRIDE model
- Attack trees
- Trust boundaries
- Data flow diagrams (DFD)
👉 This is what senior engineers do
🟢 Phase 11 — Security Monitoring & Detection
Security doesn't stop after deployment.
Learn:
- Logging best practices
- SIEM tools
- Detection engineering
Tools:
- ELK Stack
- Splunk
- Wazuh
🟢 Phase 12 — Incident Response
When things go wrong:
- Incident handling lifecycle
- Root cause analysis
- Post-mortem reports
👉 This makes you industry-ready
🟢 Phase 13 — Cryptography Basics
You don't need to be a mathematician, but understand:
- Encryption (AES, RSA)
- Hashing (bcrypt, Argon2)
- Secure password storage
🟢 Phase 14 — AI & Emerging Security
Future-ready engineers must know:
- Prompt injection
- LLM data leakage
- OWASP LLM Top 10
🧩 Real-World Skill You MUST Build
DevSecOps is not just theory.
👉 You must be able to:
- Build a secure CI/CD pipeline
- Automate security testing
- Perform manual pentesting
- Chain vulnerabilities (like XSS → Account Takeover)
- Review code securely
- Secure cloud & Kubernetes environments
⚠️ Biggest Mistake Beginners Make
Learning tools without understanding concepts
Tools change. Concepts don't.
🧠 Final Mindset
To become a top DevSecOps engineer:
- Think like an attacker
- Build like a developer
- Defend like an engineer
🚀 Final Thought
The future of security is not just finding bugs — it's preventing them before they reach production.
If you follow this roadmap consistently, you won't just be a pentester…
👉 You'll become a complete security engineer
If you found this helpful:
🔗 LinkedIn: https://www.linkedin.com/in/kanishka-khandelwal-a49050263/
Drop your thoughts or questions below 👇