Now that I deal with cybersecurity topics in the company I work for, I have realized that many people don't really know the difference between a threat and a vulnerability. Both are related to risk and problems, but conceptually they are very different. Vulnerabilities can be fixed or mitigated; threats, on the other hand, exist outside our control.
In this post, I would like to bring a bit more clarity to what these concepts are and how they relate to each other.
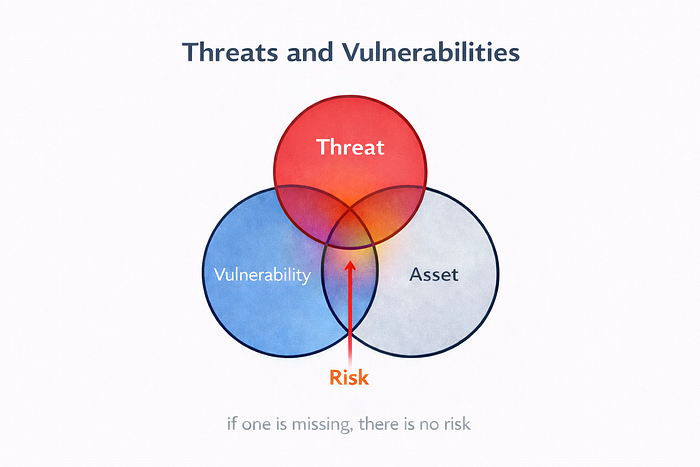
First of all, we need to be clear that for vulnerabilities and threats to exist, there has to be an asset. If there is no asset, there is nothing to protect, nothing to attack, and therefore no risk. If an asset exists but has no vulnerabilities, a threat will have nothing to take advantage of. In that case, there would not be any real risk either. In the same way, a vulnerability is only relevant if there is a threat capable of exploiting it. If no one and nothing can take advantage of it, then in practice it does not create a meaningful risk.
In short, risk appears when these three elements come together: an asset, a vulnerability, and a threat. If one of them is missing, the risk disappears or becomes insignificant.
Threats
A threat is anything capable of negatively affecting an asset. In cybersecurity, people often think directly of hackers, but a threat does not always have to be a person. It can also be a fire, a flood, or even a hurricane, if it affects a company's physical network or IT facilities. These would be external threats, since their origin lies outside the organization. They may come from people outside the company, but also from physical or environmental events that impact its systems and infrastructure.
However, many of the most serious threats are not external, but internal. These originate within the organization itself and, in most cases, they are not intentional but accidental. They are often caused by employees, suppliers, or third parties with access to the working environment. Very often, these kinds of problems appear because established protocols and standards are not followed, or because they do not exist in the first place. This can create vulnerabilities that should not be there and that may later be exploited.
Vulnerabilities
A vulnerability is a weakness in an asset, in its environment, or in the way it is managed that can be exploited and lead to risk.
In cybersecurity, the most common vulnerabilities usually appear in product design, source code, system configuration, or in the implementation of protective measures.
Vulnerabilities can be classified into four main groups:
Environmental vulnerabilities
These are conditions in the surrounding environment that can favor an incident or make its consequences worse. They do not depend directly on the system itself, but they still affect its security.
For example:
- A data center located in an area with flood risk.
- A server room exposed to excessively high temperatures.
In these cases, the problem is not in the software or in the device itself, but in the environment in which it operates.
Physical vulnerabilities
These are related to the material protection of equipment, buildings, and infrastructure.
For example:
- Using a water-based fire suppression system in a room with sensitive electronic equipment.
- Having servers in a room without physical access control.
Here, the weakness directly affects the physical assets that support the system.
Operational vulnerabilities
These appear because of poor execution of company policies, processes, or procedures, or simply because they do not exist.
For example:
- Not applying security updates on time.
- Sharing passwords between several employees.
This type of vulnerability usually originates in the organization and in the way it operates.
Technical vulnerabilities
These are the weaknesses inherent to systems, devices, networks, or applications.
For example:
- Poorly implemented authentication.
- Unencrypted communications.
These are the vulnerabilities most closely associated with the purely technical side of cybersecurity. Many of them discovered in real products and systems end up being registered as CVE (Common Vulnerabilities and Exposures).
Here I have only shown a few examples of each type of vulnerability, but the list could easily be much longer if we spent a few minutes thinking about it.
VE (Common Vulnerabilities and Exposures)
CVEs are a public reference system used to identify and catalogue known cybersecurity vulnerabilities. Their purpose is to allow manufacturers, researchers, and security teams to talk about the same issue using a common identifier. The CVE program focuses on vulnerabilities that have been publicly disclosed.
Each registered vulnerability receives a unique identifier. Its format follows this structure:
CVE-year-number
For example: CVE-2017–0144. The current format allows four or more digits in the last section, not just four.
A CVE does not necessarily include an associated exploit. What it records is the existence of a known vulnerability and a standardized way to refer to it. Whether or not a public exploit exists is a separate matter. In fact, CISA keeps a separate catalogue specifically for vulnerabilities for which there is evidence of active exploitation.
Zero-day vulnerability
When a vulnerability has just been discovered and no fix is yet available, or when its public disclosure is still very recent, it is often considered a zero-day vulnerability. At that point, defenders have little or no room to react, because the issue has not yet been fully resolved or fully communicated.
Over time, if that vulnerability is analyzed, publicly disclosed, and given an official identifier, it may become part of the CVE system. From that moment on, the industry can track it more clearly, share information about its impact, and work on mitigations or patches.

