✅ 1) What it is (very simple definition)
Access control vulnerability happens when
A user can access something they should NOT be allowed to access.
Examples include accessing:
- another user's data
- admin-only pages
- restricted APIs
- hidden features
Even when the app "looks secure" on UI — Theare access control vulnerabilities? backend fails to enforce permissions properly.
This is also called:
- Authorization flaw
- Broken access control
- IDOR (Insecure Direct Object Reference)
🎯 2) Why it exists (what problem access control was meant to solve)
Web apps need to:
- Show each user only their own data
- Restrict admin features
- Separate normal users vs premium vs staff
- Protect internal systems
So apps implement access control toThe
Ensure privacy => User should only see their account privacy Enforce roles => account Only admins can delete users. Prevent abuse => users Only staff can download reports Protect revenue => reports Premium features behind a subscription.
The problem? Many developers trust the frontend UI
⚙️ 3) How it works (step-by-step — browser → request → server)
Let's take a simple case:
A user opens theinstead
/user/profile?id=101🧭 Step-by-step flow
1️⃣ Browser sends request
GET /user/profile?id=101
Cookie: session=user12️⃣ Server extracts two values
- session user →
user1 - requested user →
id=101
3️⃣ Correct behavior (secure) Serveropens the checks:
does user1 own profile 101?
If NO → deny access
4️⃣ Vulnerable behavior The serverServer only checks:
Is the user logged in?
Then returns data anyway.
Result → user can modify ID manually:
/user/profile?id=102Now they can view another user's profile.
That is broken access control.
🧩 4) Simple Examples (easy to imagine)
🟢 Example 1 — Change User ID in URL
GET /orders?id=1001 → your order
Change to:
GET /orders?id=1002 → someone else's orderIf data loads → That's the server and an IDOR vulnerability (exploitable).
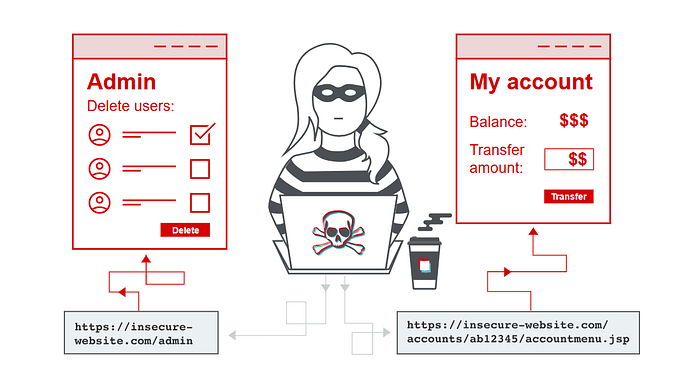
🟢 Example 2 — Hidden Admin Button in UI
The UI hides the "Delete User" button for normal users. But the request The UI hides the still valid:
POST /admin/deleteUser?id=55If user can send request via Burp…
and server allows it…
The vulnerability is privilege escalation.the request
🌍 5) Real-world example (modern web app/API)privilege escalation.
Imagine a mobile banking API:
GET /api/v1/accounts/92391/transactions
Authorization: Bearer token_user_AUser changes account number in proxy:
/api/v1/accounts/92392/transactionsIf transactions return:
- privacy violation
- financial exposure
- regulatory breach
This is high-severity broken access control.
This is extremely common in the following:/API)
- fintech
- healthcare
- SaaS CRMs
- e-commerce order APIs
⚠️ 6) What can go wrong (misconfigurations)
Here are real root causes seen in production:
❌ Trusting frontend controls
UI hides admin features Butin the following: the APIBut API has no role validation.
❌ Only validating login — not ownership
Developer checks:
- Is user authenticated? ✅
But does NOT check:
- Does this user own this object? ❌
❌ Relying on client-side values
Such as:
- role stored in cookies
- role stored in JWT without verification
- user ID passed from UI
❌ Reusing APIs across roles
Same API called by:
- admin panel
- normal user dashboard
Backend assumes:
"Only admins will call this API"
Attackers do.
🧨 7) How attackers abuse it (basic → advanced)
Let's move from beginner → professional exploitation logic.
🟡 Basic Attacks
- Modify ID parameter
- Change username in the request. the request.
- Replace account number
- Remove UI restrictions
Example:
/user/profile?id=101 → 102 → 103🟠 Intermediate Attacks
- modify JSON body
{ "user_id": 55 }- change object references
- bypass missing server-side validation
🔴 Advanced Real-World Exploitation
1) Replace your JWT user ID.
The original JWT contains
"uid": 101Modify to:
"uid": 102If backend does not validate signature properly → Account Takeover
2) Role escalation via header tampering
Add:
X-User-Role: adminor
X-Organization-Id: 1If backend trusts header → Privilege Escalation
3) Accessing internal admin APIs
Normal user accesses:
/internal/api/exportUsers
/internal/api/generateReportsIf no authorization checks → full database exposure.
🧪 8) Where & how to test manually in VAPT
Here's how professionals approach this.
🔎 Where to look
Target endpoints like the following:
/user/*/account/*/orders/*/profile/*/api/v1/*/admin/*
🧰 Manual Testing Workflow (Burp / Proxy)
- Capture request
- Identify sensitive identifiers:
- id
- account_id
- user_id
- org_id
3. Change values manually
4. Replay request
Observe:
Result & Interpretation Access denied => Secure. Redirect to login => auth enforced Error 403 => secure Data returned => valid exploitable finding
🎯 Validation checklist (avoid false positives)
A finding is valid & exploitable only if
- Another user's data is exposed. or
- unauthorized operation succeeds
Just changing the ID and getting
- error
- null
- empty response
is NOT a vulnerability.
🧱 9) Common beginner misunderstandings & false positives
❌ "App returns 404 after ID change—it's vulnerable."
No. That means the record doesn't exist.
❌ "UI blocks the action—so it's secure."
Test API anyway.
UI ≠ Security control.
❌ "I changed ID but got same data."
Many apps ignore unknown IDs.
Not exploitable → not a valid issue.
❌ "Any 200 OK response = vulnerability."
Not always.
You must confirm:
- cross-user data exposure OR
- privilege escalation
Otherwise, it's noise.
Useful Links:
Learn more = https://owasp.org/Top10/2021/A01_2021-Broken_Access_Control/
lab = https://portswigger.net/web-security/access-control
tools = https://github.com/encodedguy/bugbounty-cheatsheet/blob/master/AccessControl/WebSecurity.md