Bug bounty hunting has a funny way of humbling you. Sometimes you spend hours digging deep and find nothing. Other times, a very simple bug appears… and still ends up marked as duplicate. This is one of those stories.
Quick Context
While testing redacted.com, I noticed something interesting around the profile name field. At first glance it looked like a normal input field — nothing special. But as bug hunters know, user-controlled fields appearing in emails or notifications are always worth testing.
So I tried something simple.
The Idea
The application sends team/organization invitation emails to users.
If any unsanitized input from the application appears inside those emails, it can lead to HTML injection inside the email template.
And that's exactly what happened.
The Test
Inside the Name field, I inserted a simple HTML payload:
<img src="https://pbs.twimg.com/profile_images/2023299574350434304/KPNGQIAC_400x400.jpg">
Nothing fancy. No complex payloads. Just a basic <img> tag.
Saved the profile and continued testing.
Steps to Reproduce
- Login to your account.
- Navigate to Account Settings → Profile.
- Edit the Name field.
- Insert the following payload:
<img src="https://pbs.twimg.com/profile_images/2023299574350434304/KPNGQIAC_400x400.jpg">5. Save the profile.

6.Create or join a Team/Organization.
7.Invite another user to the team.
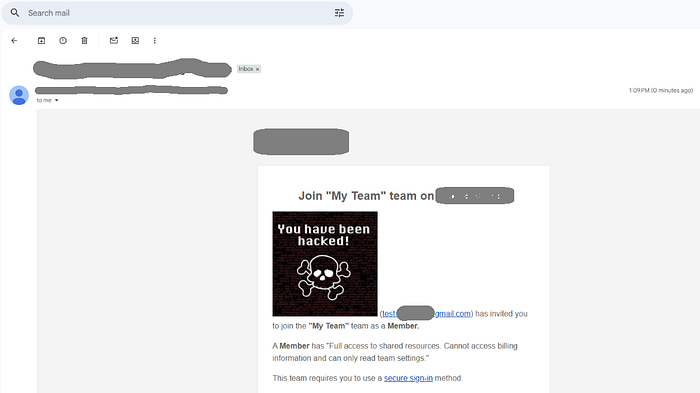
8.When the invited user opens the invitation email, the injected image loads.
What Actually Happens
Instead of escaping the HTML, the application renders the injected content directly inside the email.
Which means the <img> tag is executed when the email is opened.
So when the victim opens the invitation email, their email client loads the image from the attacker-controlled URL.
Basically the email becomes:
"Hey, welcome to the team… also please load this random image from the internet." 😅
Why This Matters
Even though this looks small, it can still cause multiple issues.
Impact includes:
- Stored HTML Injection
- External resource injection in system emails
- Email open tracking using attacker-controlled images
- Victim IP address disclosure
- User-Agent and device fingerprint leakage
- Potential phishing enhancement if abused creatively
- Brand trust issues (because system emails contain attacker content)
So yes… a small bug, but still security-relevant.
The Plot Twist
After submitting the report…
It was marked as Duplicate.
Which means someone else already found it before me.
Classic bug bounty moment.
You find a bug, write a clean report, feel proud… and then the platform says:
"Nice work… but someone already got there first." 🙂

Still, every test like this improves your hunting skills and makes you faster for the next one.
Final Thoughts
Many hunters focus only on complex vulnerabilities, but simple input fields appearing in emails, notifications, or templates can also create interesting bugs.
Sometimes the easiest payloads work.
Sometimes they become duplicates.
But they're always worth testing.
Connect With Me
If you're into bug bounty hunting, security research, or web hacking, feel free to connect.
Connect with me on LinkedIn
