🧪 Hackviser — Web Application Security
🧩 What is Unrestricted File Upload ?
Unrestricted File Upload vulnerabilities occur from the insecure development of file upload functionalities in web applications. In modern web applications, file uploading is a crucial function that allows users to attach files or change their profile pictures. However, if this functionality is not securely developed, it can lead to serious security risks resulting in Remote Code Execution or Shell Accesses or even more serious vulnerabilities.
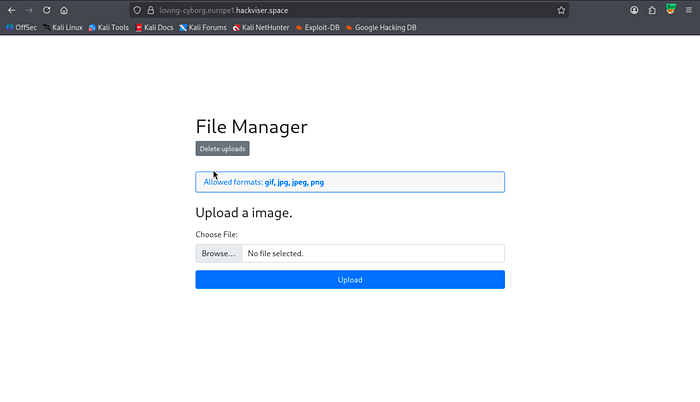
For file upload, the page tells us that it allows only gif, png, jpeg, and png formats. Let's see if it's true or not.
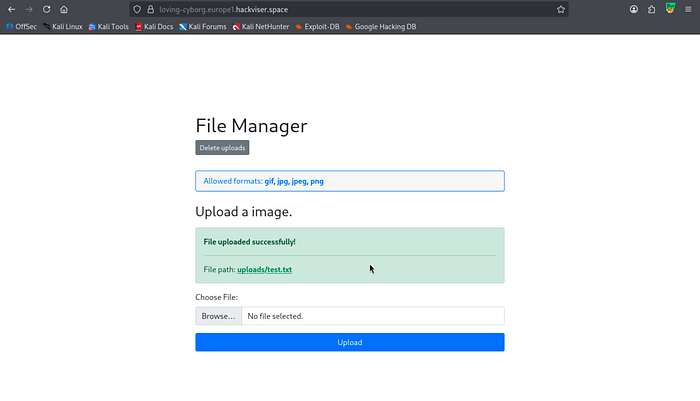
As we can see that there is no filtering for file uploads which lets us to upload and execute whichever file/script we want.
We can upload a basic cmd.php and just execute linux command prompts but instead we are gonna use a shell script which gives us a shell access to the target machine from "https://github.com/flozz/p0wny-shell/blob/master/shell.php".
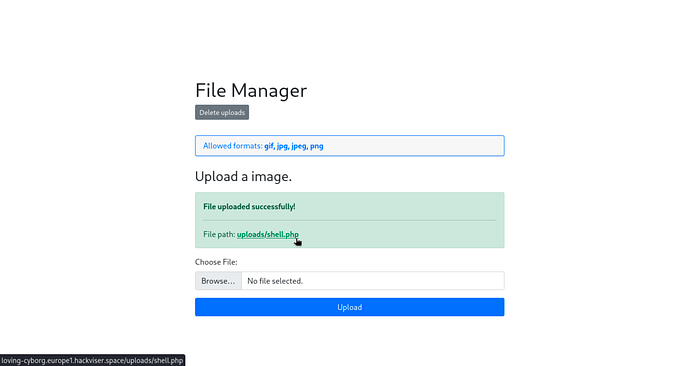
We did upload the shell script and also we have the information of the file's location which is "uploads/shell.php". Let's traverse to that location via. browser.

We are in! Flag is basically the database password which is configured inside the config.php file. We can find it's location by using the command "find / -name "config.php" 2>/dev/null". We use "2>/dev/null" clause to not get the "Permission denied" errors(We send Standard Error (stderr) objects to void) for getting clean and short outputs.
As a result we got the flag with those processes.
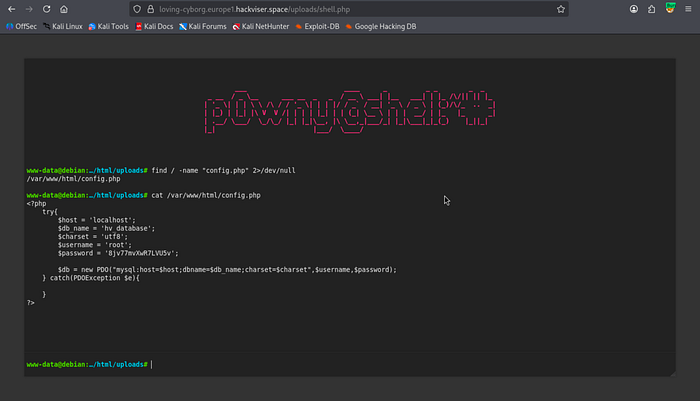
Flag : 8jv77mvXwR7LVU5v