Responsible Disclosure Notice
The findings described in this article were validated in a controlled lab environment for security research and responsible disclosure. Any associated PoC material was used strictly for authorized testing and is not distributed through this publication. Disclosure to the vendor has been initiated, and the issue is currently under coordinated review, including CVE submission status where applicable.
Supplementary Video Evidence for Responsible Disclosure A controlled lab validation video is available to support independent review and vulnerability verification. The video is provided strictly for responsible disclosure purposes. ( https://www.youtube.com/watch?v=9_tY0gjOz0c&t=2756s )
Overview
- This research highlights a credential exposure risk in Veeam Backup & Replication.
- The PoC shows that sensitive credentials stored by the product may be recovered in plaintext under local compromise conditions.
- The issue is not limited to the backup server itself.
- Because Veeam stores credentials for multiple connected systems, the impact may extend into broader infrastructure compromise.
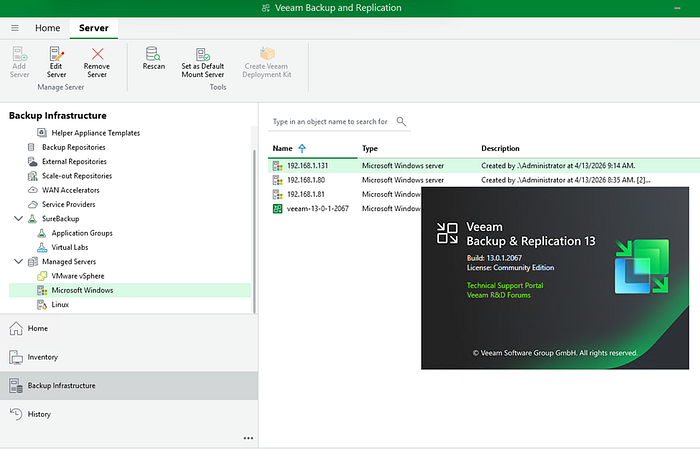
Veeam Backup & Replication 13.0.1.2067 stores managed infrastructure credentials in a recoverable form. Under local compromise of the Veeam server, locally accessible credential data and associated recovery material may allow plaintext recovery of stored credentials, leading to information disclosure and potential compromise of connected systems.
Lab PoC Environment
- The PoC was validated in a controlled lab environment for responsible disclosure.
- The Veeam Backup & Replication server acted as the central backup platform for multiple connected systems.
The lab environment included:
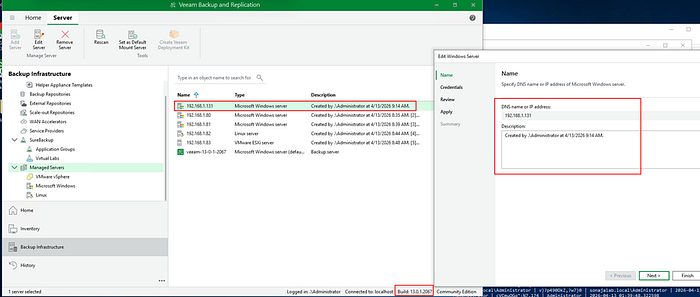
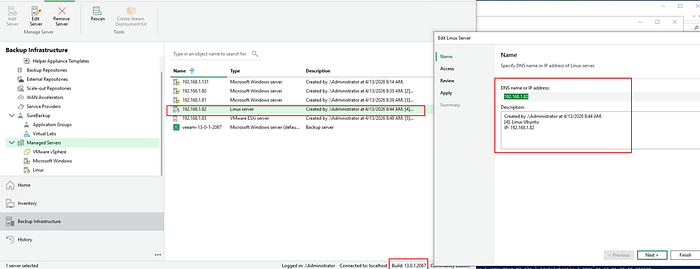
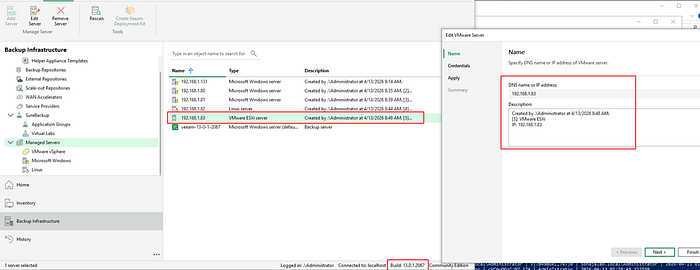
- Veeam Backup & Replication server (Build: 13.0.1.206 Release: March 12,2026 ) ->192.168.1.125 Ref:https://www.veeam.com/products/downloads/latest-version.html
- Domain Controller -> 192.168.1.80 (Generate New Pass: )
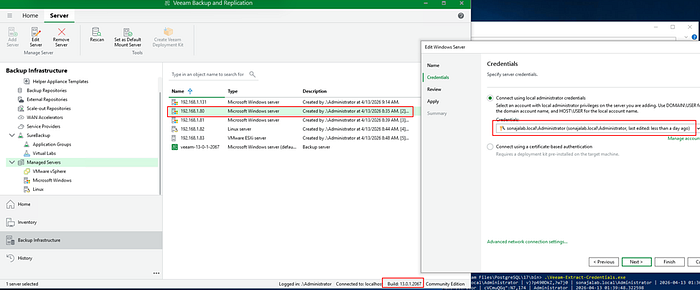
- Windows Workgroup host -> 192.168.1.81 (Generate New Pass: )
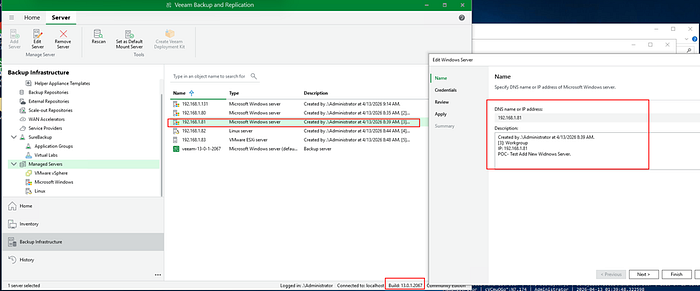
- Windows Workgroup host -> 192.168.1.131 (Generate New Pass: )
- Linux Ubuntu server ->192.168.1.82 (Generate New Pass:)
- VMware ESXi ->192.168.1.83 (Generate New Pass: )
The purpose of the lab was to assess whether compromise of the Veeam server could lead to plaintext credential exposure and broader infrastructure risk.
Risk Description
- The core issue is that protected credential data and the required recovery material are accessible from the same host.
- Under local compromise conditions, stored credentials may be recovered in plaintext.
- This creates a high-risk post-compromise condition.
- Once the Veeam server is compromised locally, it may become a pivot point to other privileged systems.
- From a risk perspective, this is not only a storage weakness. It is a practical credential exposure problem.
Affected Components
- Credential protection within Veeam Backup & Replication.
- Stored credentials used for backup and management operations.
- Connected infrastructure that relies on those credentials.
In the lab PoC, affected systems included:
- Domain Controller and Windows systems
- Linux systems
- VMware ESXi
- Other privileged infrastructure components
Artifacts and Evidence of PoC
- The PoC was validated in a controlled lab environment.
- Credential data and related recovery material were accessible from the local system.
- Stored credentials were successfully recovered in plaintext.
- Recovered credentials were validated against multiple connected systems.
- Authentication was successful across Windows, Linux, and virtualization platforms.
- The recovered credentials included privileged accounts associated with infrastructure administration.
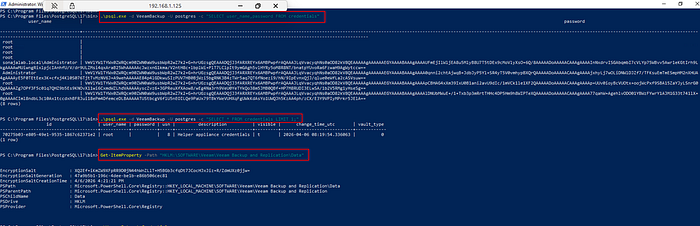
[STEP1]-Access to Veeam Configuration Database
- The Veeam backup server includes psql.exe for the internal PostgreSQL database.
- A local administrator opens PowerShell and executes:
.\psql.exe -d VeeamBackup -U postgres -c "SELECT user_name,password FROM credentials"
- Output reveals:
- Usernames stored in Veeam
- Encrypted password
[STEP2]-Access to Encryption Salt from Registry
- Veeam stores DPAPI salt in registry:
HKLM\SOFTWARE\Veeam\Veeam Backup and Replication\Data
- Verified using PowerShell:
Get-ItemProperty -Path "HKLM:\SOFTWARE\Veeam\Veeam Backup and Replication\Data"
- Obtained:
- EncryptionSalt
- EncryptionSaltGeneration
- EncryptionSaltCreationTime
[STEP3]-Decrypting All Veeam Credentials
- Using salt from registry + encrypted blob from database
- Executed the PoC script:
.\Veeam-Extract-Credentials.ps1
- Windows DPAPI with LocalMachine scope successfully decrypts all stored credentials
- Plaintext passwords extracted include:
- root (Linux)
- Windows Administrator
- ESXi root
- Repository servers
- Helper appliances
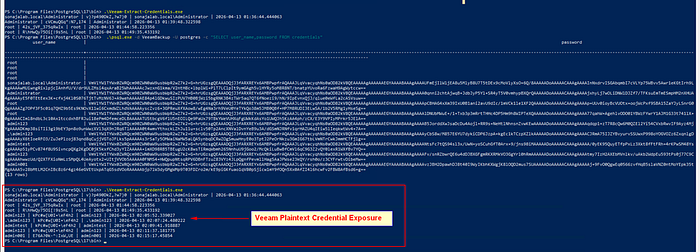
[STEP4]-Validation of Extracted Credentials
- Using recovered plaintext credentials:
- Logged into Linux servers via SSH → success
- Logged into Windows servers via RDP → success
- Logged into ESXi host using root → success

Why This Is Critical
- Backup servers often store highly privileged credentials.
- Those credentials may provide access to servers, hypervisors, management systems, and backup-related infrastructure.
- If these credentials are exposed, the attacker may gain access far beyond the Veeam host itself.
- The PoC demonstrates that this is not only theoretical; the exposed credentials were validated successfully across multiple connected systems.
- In ransomware scenarios, this becomes especially serious because backup infrastructure is often a primary target.
Attack Chain
Attack Chain: From Local Compromise to Privileged Infrastructure Compromise
High-level attack chain showing how local compromise of a Veeam Backup & Replication server may lead to plaintext credential exposure, privileged access expansion, lateral movement, and broader infrastructure impact.
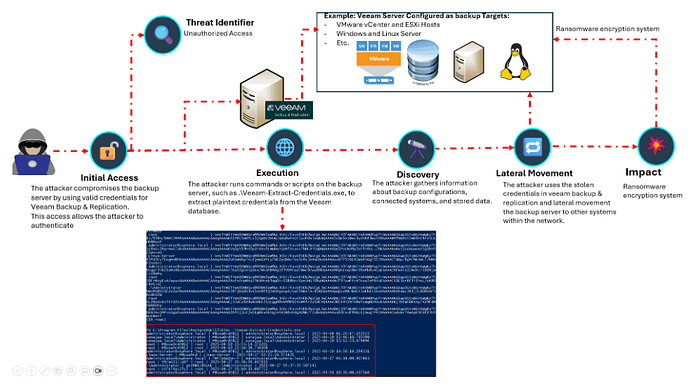
- This attack chain illustrates how compromise of a Veeam Backup & Replication server may evolve into broader infrastructure compromise.
- The key risk is not limited to credential disclosure alone.
- Once the backup server is compromised locally, exposed credentials may provide access to other privileged systems managed through the platform.
- This makes the Veeam server a high-value post-compromise pivot point in enterprise environments.
Attack Flow
Initial Access
- The attacker gains unauthorized or abused access to the Veeam server.
- At this stage, the Veeam host becomes the starting point for further compromise.
Credential Exposure
- Sensitive credential material stored on the Veeam server becomes accessible under local access conditions.
- This may lead to plaintext credential exposure involving accounts used for backup and management operations.
Discovery
- The attacker identifies connected systems, backup targets, privileged accounts, and infrastructure dependencies.
- These may include Windows systems, Linux systems, VMware ESXi hosts, vCenter, repositories, and other administrative assets.
Privileged Access Expansion
- Exposed credentials may allow access to connected systems beyond the Veeam host itself.
- This significantly increases the attacker's ability to reach critical infrastructure.
Lateral Movement
- The attacker uses the exposed credentials to move across the environment.
- What begins as a local compromise of the backup server may expand into multi-system compromise.
Impact
- The final impact may include privileged infrastructure compromise, backup disruption, loss of recovery assurance, and increased ransomware impact.
- In enterprise environments, this may significantly increase the blast radius of a single host compromise.
Why This Attack Chain Matters
- It shows that the backup server is not just another application host.
- It may hold privileged trust relationships across multiple systems.
- A compromise of the Veeam server may therefore lead to:
- plaintext credential exposure
- privileged access to connected infrastructure
- lateral movement opportunities
- increased operational and recovery risk
- wider environment compromise
DFIR Relevance and Operational Impact
- A compromised Veeam server should not be treated as only a single-host incident.
- It may also represent a credential exposure event affecting multiple connected systems.
- DFIR teams should consider backup infrastructure a high-priority asset during:
- incident scoping
- containment
- privilege review
- lateral movement analysis
- ransomware investigation
- This issue is highly relevant to post-compromise investigations where backup systems may serve as a high-value pivot point.
Potential Impact
- Exposure of privileged credentials across connected systems
- Increased risk of lateral movement and privilege escalation
- Increased risk to backup integrity, recovery assurance, and virtualization infrastructure
- In ransomware scenarios, this may significantly increase enterprise-wide operational impact
Conclusion
- This proof of concept demonstrates that local compromise of a Veeam Backup & Replication server may lead to plaintext credential exposure.
- Because those credentials may provide privileged access to multiple connected systems, the security impact can extend far beyond the backup server itself.
- This issue should not be viewed as a standalone credential storage weakness.
- From a risk perspective, it represents a high-impact exposure that may affect enterprise-wide trust, operational resilience, and recovery assurance.
Reference: https://www.youtube.com/watch?v=9_tY0gjOz0c&t=2756s
Reference: https://www.veeam.com/products/downloads/latest-version.html
#Cybersecurity #DFIR #Veeam #Backup #CredentialExposure #PrivilegeEscalation #Ransomware #SecurityResearch
