n8n, the popular open-source workflow automation tool, just got hit with another critical security issue. This time, it's CVE-2026–33696 a prototype pollution vulnerability in two specific nodes that can let an authenticated user achieve Remote Code Execution (RCE) on the server.
If you're running self-hosted n8n (or even cloud in some cases), this one deserves your immediate attention.
What Happened?
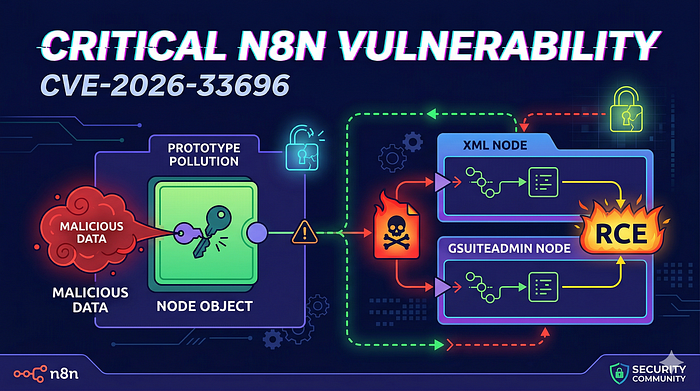
On March 25, 2026, n8n published a security advisory revealing that an authenticated user with permission to create or edit workflows could exploit a flaw in the XML node and the GSuiteAdmin node (Google Workspace Admin).
The core issue is classic prototype pollution (CWE-1321). When these nodes process user-supplied configuration parameters, they merge data without properly protecting against dangerous keys like __proto__ or constructor.prototype.
As a result, an attacker can inject values directly onto Object.prototype the root from which almost every JavaScript object in the Node.js process inherits properties. Once polluted, these changes affect the entire application and can be chained into full remote code execution.
- Severity: Critical
- CVSS 4.0 Score: 9.4
- Attack Requirements: Low just a normal user who can build workflows (no admin rights needed).
How the Attack Works (Mid-Level Technical Breakdown)
Here's the simplified flow:
- Node Configuration — You drag the XML node or GSuiteAdmin node into a workflow and fill in its parameters (e.g., XML parsing options, domain settings, etc.).
- Unsafe Merging — Internally, n8n takes these parameters and merges them into an object using logic that doesn't sanitize prototype keys.
- Pollution — An attacker crafts a payload like this (conceptual example — at the time of writing exact field names aren't publicly detailed yet ):
{
"someParameter": {
"__proto__": {
"pollutedKey": "maliciousValue",
"anotherGadget": "valueThatTriggersRCE"
}
}
}Or using constructor.prototype for similar effect.
4. Impact — Because Object.prototype is now polluted, other parts of n8n (especially expression evaluation, object property checks, or default value handling) behave unexpectedly. Researchers say this pollution can be reliably turned into arbitrary code execution on the n8n server.
The pollution survives until the n8n process is restarted, making it particularly dangerous in long-running instances.
No public Proof of Concept (PoC) has been released yet. The advisory keeps the exact vulnerable parameter names and the final gadget chain under wraps for now which is responsible, but means defenders need to act fast without waiting for exploits to appear on GitHub.
Who Is Affected?
- All n8n versions before the patched releases.
- Specifically:
- Main branch: versions prior to 2.14.1
- 2.13.x branch: prior to 2.13.3
- 1.x branch: prior to 1.123.27
Both self-hosted and n8n cloud instances are impacted if workflows using these nodes are editable by untrusted users.
Official Fix & Workarounds
Best solution: Upgrade immediately to one of these versions:
- 2.14.1
- 2.13.3
- 1.123.27 (or newer)
If you can't upgrade right away, apply these temporary mitigations (note: they are not complete fixes):
- Restrict workflow creation and editing permissions to only fully trusted users.
- Disable the XML node entirely by setting the environment variable:
- text
NODES_EXCLUDE=n8n-nodes-base.xmlThese steps reduce risk significantly but still leave the GSuiteAdmin node potentially exposed. Upgrade as soon as possible.
Why This Matters — Context on n8n Security
This isn't n8n's first rodeo with critical RCE issues in 2026. The platform has seen several high-profile vulnerabilities involving expression sandbox escapes, merge node flaws, and webhook handling problems. As n8n grows in popularity for internal automation, its attack surface expands especially since many deployments run with broad workflow editing rights.
Prototype pollution remains one of the sneakiest JavaScript vulnerabilities because it can silently break assumptions across an entire codebase.
What Should You Do Now?
- Check your version — Run n8n version or check your Docker image/tag.
- Upgrade to the latest patched release.
- Audit permissions — Review who can create/edit workflows in your instance.
- Monitor — Watch for unusual workflow executions or unexpected process behavior.
- Stay updated — Subscribe to n8n's security bulletins and GitHub advisories.
If you're using n8n in a production environment with sensitive integrations (databases, cloud accounts, internal APIs), treat this as urgent.
Final Thoughts
Prototype pollution bugs like CVE-2026–33696 remind us how fragile object merging can be in JavaScript-heavy apps. Even small nodes handling configuration data need strict input validation and safe merge utilities (like lodash.mergeWith with proper guards or structured parsing).
Kudos to the n8n team for quick disclosure and patches. For the community: keep your instances updated and limit blast radius by following the principle of least privilege on workflow editors.4