When I started to learn cybersecurity concepts, I found the diagram of private and public keys confusing. So I want to break these concepts down in an easy-to-understand way.
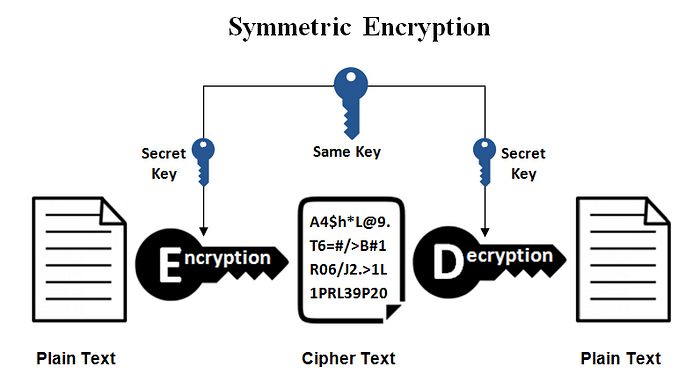
Symmetric encryption is easy: it uses a single key for both encryption and decryption. You use the same key to unlock and lock the door. It is also much faster than Asymmetric encryption.
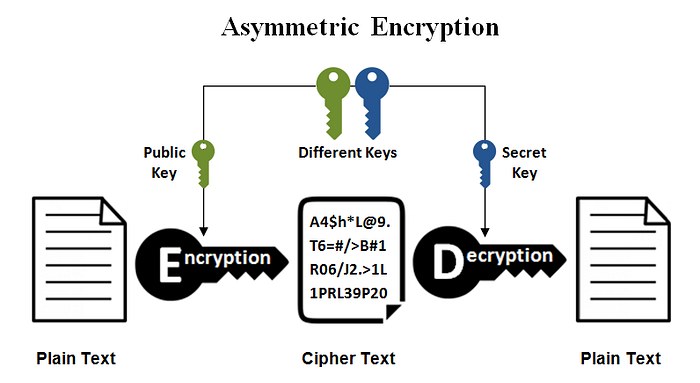
Asymmetric Cryptography: has two keys with different purposes. Everyone has a Public Key (which you share with the world) and a Private Key (which you guard with your life).
The rule is simple: whichever key you use for encryption, you can only decrypt it with the other one.
But how do we actually use them? It all depends on what you want. Confidentiality or Authentication? Let's break it down :
Scenario 1: I Want Confidentiality
Imagine Alice wants to send a personal message to Bob. She doesn't want any "Man in the Middle" to read it.
- Alice encrypts her message using Bob's Public Key.
- Since it was locked with Bob's Public Key, the only thing in the world that can unlock it is Bob's Private Key.
- Conclusion: The message is perfectly hidden (Confidentiality).
In this scenario, we have confidentiality, but Bob can not be sure that this message is from Alice!
Scenario 2: I Want to Prove It's Me (Digital Signatures)
Now, imagine Alice wants to send a message to Bob. The message doesn't need to be a secret, but Bob needs absolute proof that Alice wrote it and that it wasn't tampered with. We need Integrity and Authentication.
This is where Digital Signatures come in.
- Hash it: Alice runs her plaintext document through a hashing algorithm.
Hash is a mathematical function that is the same on every computer. It is like a blender; you give it a text file, video, or whatever, and it gives you an output. The output is a string with random-looking characters. Think of a hash as a unique digital fingerprint of the file. If even a single comma in a very big file is altered, this hash will change completely (the avalanche effect).
- Sign it: Alice encrypts this Hash using her own Private Key. We call this encrypted hash a Digital Signature.
- Send it: She sends the plaintext document + the Digital Signature to Bob.
When Bob receives it, he decrypts the signature using Alice's Public Key to reveal the hash. Then, he hashes the plaintext document himself. If his hash matches Alice's hash, he knows two things:
- Hash matches, so the document hasn't changed (Proof of Integrity).
- Only Alice's Private Key could have locked that hash (Proof of Origin / Authentication).
When you have these two proofs, you achieve a concept called Non-repudiation (the "no take-backs" rule). Because only Alice possesses her private key, she cannot later claim, "I never signed that contract!"
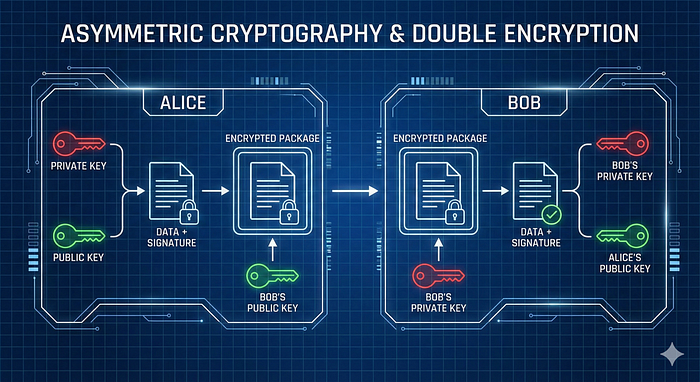
Scenario 3: The Masterpiece (Double Encryption)
Here is the problem with Scenario 2: the message is sent in plaintext. If an attacker intercepts it, they can't change the message, but they can read it.
What if Alice wants the ultimate security? What if she wants the message to be completely secret AND digitally signed? She has to use both previous scenarios. If we combine both, we call it Double Encryption.
- Step 1: Alice does the same thing as scenario 2 (Hashing the message and encrypting the hash with her Private Key). Now she has a package:
[Plaintext Message + Digital Signature]. that we saw in scenario 2. - Step 2: Alice takes that entire package and encrypts the whole thing using Bob's Public Key. If we see hash, encrypting, and decrypting as functions, we have
Bob's_public_key[PlainText + Alice's_private_key(Hash(PlainText))]
Boom. Now, the package is an unreadable mess to anyone observing the network. When Bob receives it, he first uses his Private Key to open the outer layer (Confidentiality). Then, he uses Alice's Public Key to verify the inner signature (Integrity & Non-repudiation).
Cryptography can seem difficult, but once you understand the flow of keys, it becomes much easier.
Which cryptography concept confused you the most when you first learned it?