Stop looking for id=1. Start hunting the authorization mistakes developers don't see.
If you've been hunting for bugs for more than a few months, you've felt it.
The easy IDORs are disappearing.
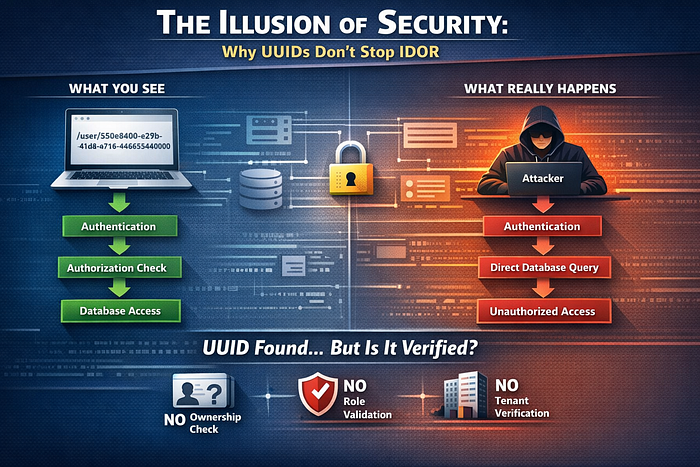
You don't see:
/user/101Now you see:
/user/550e8400-e29b-41d4-a716-446655440000Long. Random. Complex.
Developers often feel confident when they see identifiers like this:
"Nobody can guess this."
But here is the reality:
UUID is not access control.
Modern applications are still exposing sensitive data — not because IDs are predictable, but because authorization is incorrectly implemented or missing.
This is no longer about guessing numbers.
This is about understanding how systems are designed and where they fail.
The Real Problem: Authorization Is an Afterthought
To understand modern IDOR, you must clearly separate two concepts:
Authentication answers:
Who are you?
Authorization answers:
What are you allowed to access?
Most modern applications implement authentication properly:
- Login systems work
- Tokens are validated
- Sessions are managed
However, authorization is often inconsistent or incomplete.
In many systems, once a user is authenticated, the backend trusts the input provided by the user — especially identifiers such as user IDs, order IDs, or invoice IDs.
This trust is where vulnerabilities begin.
If the system does not verify whether the authenticated user is actually allowed to access the requested resource, it becomes vulnerable to IDOR.
The Anatomy of Modern IDOR
Consider the following request:
GET /api/orders/550e8400-e29b-41d4-a716-446655440000At first glance, this appears secure due to the complexity of the identifier.
However, the security depends entirely on backend validation.
Secure Flow
[ Client ]
↓
[ Authentication Check ]
↓
[ Authorization Check (Ownership / Role / Tenant) ]
↓
[ Fetch Object From Database ]
↓
[ Return Response ]In a secure implementation, the system verifies:
- Whether the user owns the resource
- Whether the user has the required permissions
- Whether the resource belongs to the same tenant or organization
Only after these checks pass is the data returned.
Vulnerable Flow
[ Client ]
↓
[ Authentication Check ]
↓
[ Fetch Object From Database ]
↓
[ Return Response ]In this case:
- No ownership validation is performed
- No role or permission checks are applied
- No tenant isolation is enforced
The backend simply accepts the identifier and retrieves the object.
This single missing step results in a critical vulnerability.
The UUID Illusion: Security Through Obscurity
To prevent traditional IDOR attacks, developers replaced sequential numeric IDs with UUIDs.
From:
/invoice/1001
/invoice/1002
/invoice/1003To:
/invoice/771e8400-e29b-41d4-a716-446655440000This change reduces simple enumeration.
However, it introduces a false assumption:
If the identifier cannot be guessed, the system is secure.
This is incorrect.
Security should never rely on the secrecy of identifiers.
The Key Insight
Attackers do not rely on guessing UUIDs.
They obtain them through other means.
Once a valid UUID is available, the focus shifts entirely to testing authorization.
If the backend does not validate access properly, the system is vulnerable regardless of how complex the identifier is.
How Attackers Collect UUIDs
Modern IDOR exploitation depends on collecting valid identifiers.
Below are common real-world methods.
1. Username Enumeration Leading to UUID Disclosure
Some applications reveal internal identifiers during error handling.
Example:
{
"error":"User exists",
"user_id":"771e8400-e29b-41d4-a716-446655440000"
}This can occur in:
- Registration endpoints
- Login responses
- Password reset flows
A single request can expose a valid UUID.
2. API Overexposure
Frontend interfaces often hide internal identifiers, but APIs still return them.
Example:
Frontend display:
Team Members:
- Rahul
- AmanAPI response:
{
"members": [
{"name":"Rahul", "uuid":"uuid-1"},
{"name":"Aman", "uuid":"uuid-2"}
]
}Although the UI hides the UUIDs, they remain visible in network responses.
Tools such as browser developer tools or proxy tools can easily reveal this data.
3. Logs and Debug Information Leakage
Improper error handling can expose sensitive information.
Example:
{
"trace":"User object ID: 550e8400-e29b..."
}This occurs when:
- Debug mode is enabled in production
- Stack traces are returned to the client
- Logging data is exposed via APIs
These leaks provide attackers with valid identifiers.
4. Export Features
Export functionality is frequently overlooked during security testing.
Files such as CSV, Excel, or PDF often contain:
- Internal identifiers
- Hidden metadata
- Foreign key relationships
A single export operation can reveal multiple UUIDs, making it a highly effective data source.
Advanced Section: Understanding UUID Versions
Different UUID versions have different characteristics.
Understanding them can provide additional insight during testing.
UUID v1 — Timestamp-Based
Structure:
| 60-bit timestamp | 14-bit clock seq | 48-bit MAC |Characteristics:
- Contains creation time
- Includes device identifier (MAC address)
Security implications:
- Reveals when the object was created
- May expose infrastructure-related information
- Allows grouping of related objects
In high-frequency systems, it may be possible to approximate nearby values.
UUID v4 — Random-Based
Total possible combinations:
2^122 ≈ 5.3 x 10^36This makes brute-force attacks impractical.
However, brute-force is not relevant in IDOR scenarios.
If authorization is missing, a single valid UUID is sufficient to exploit the system.
UUID v7 — Time-Ordered UUID
Structure:
48-bit timestamp + random bitsCharacteristics:
- Sortable by time
- More efficient for databases
Security considerations:
- Not fully random
- Predictable ordering based on timestamps
While still difficult to exploit directly, it reduces randomness compared to v4.
Method-Based Authorization Failures
A common mistake during testing is checking only one HTTP method.
Example:
POST /api/user/uuid → 403 ForbiddenMany testers stop here.
However, different methods may have different security implementations.
Always test:
GET /api/user/uuid
PATCH /api/user/uuid
PUT /api/user/uuid
DELETE /api/user/uuidExample of flawed implementation:
app.post("/api/user/:id", secureUpdate);
app.delete("/api/user/:id", deleteUser); // Missing authorizationIn this case:
- POST is protected
- DELETE is not
This inconsistency is a frequent source of vulnerabilities.
Cross-Tenant IDOR in SaaS Applications
In multi-tenant systems:
Tenant A
Tenant B
Tenant CEach tenant's data must remain isolated.
Vulnerable Query
SELECT * FROM invoices WHERE id = ?Secure Query
SELECT * FROM invoices WHERE id = ? AND tenant_id = ?Without tenant validation:
- Users from one tenant can access data from another
- Data isolation is broken
This type of vulnerability often leads to severe data breaches.
Blind IDOR: No Visible Output
In some cases, the response does not reveal any data.
Example:
DELETE /api/user/VICTIM_UUIDResponse:
200 OK
{}Although the response appears harmless, the action may still succeed.
Possible impacts:
- Account deletion
- Data modification
- Triggered background processes
Verification steps:
- Attempt to log in as the affected user
- Check for email notifications
- Observe system behavior changes
Lack of visible output does not mean lack of impact.
Secure vs Vulnerable Flow Summary
Vulnerable
Request → Authentication → Fetch Object → ResponseSecure
Request → Authentication → Authorization → Fetch Object → ResponseThe absence of authorization is the core issue.
The Required Mindset Shift
Traditional approach:
Can the identifier be guessed?
Modern approach:
Does the system validate ownership and permissions for this request?
This shift is essential for identifying real vulnerabilities.
Final Truth: UUID Is Not a Security Boundary
A UUID is only an identifier.
It does not provide security.
Proper authorization must include:
- Ownership validation
- Role-based access control
- Tenant isolation
- Permission enforcement
If these checks are not implemented, the system is vulnerable.
The complexity of the identifier does not matter.